134:
546:
351:
Smith S, Lederman R, Monagle P, Alzougool BM, Naish L, Dreyfus S. Individually tailored client-focused reports for ubiquitous devices: An experimental analysis. 23rd
Australasian Conference on Information Systems. Australasian Conference on Information Systems ACIS.
111:
Dreyfus has written on the importance of protecting
Freedom of Information access (FOI), the problems of information asymmetry and "tool asymmetry" between the individual citizen and the state, and the trend of "security clearance creep". She was a member of the
277:
Miceli MP, Dreyfus S, Near JP. Outsider 'whistleblowers': Conceptualizing and distinguishing 'bell-ringing' behavior. International
Handbook on Whistleblowing Research. Edward Elgar Publishing Ltd. 2014. Editors: Brown AJ, Lewis D, Moberly RE, Vandekerckhove
287:
Bosua R, Milton S, Dreyfus S, Lederman R. Going public: Researching external whistleblowing in a new media age. International
Handbook on Whistleblowing Research. Edward Elgar Publishing Ltd. 2014. Editors: Brown AJ, Lewis D, Moberly RE, Vandekerckhove
332:
Kee, K., Knott, J.C., Dreyfus, S., Lederman, R., Milton, S, Joe, K. 2012. "One hundred tasks an hour: An observational study of emergency department consultant activities". Emergency
Medicine Australasia, Vol 24 (3) pp 294–302. Retrieved 11 June
123:, discussing the importance of protecting public access to strong encryption, the need for legal protections for whistleblowers, and the security paradox of legislation enforcing retention of metadata for two years for everyone in Australia.
267:
Peng F, Kurnia S, Lederman RM, Dreyfus S. Information
Systems and Hospital Work: A structuralist investigation. Proceedings of the 16th PACIFIC ASIA CONFERENCE ON INFORMATION SYSTEMS. Association for Information Systems.
361:
Lederman RM, Dreyfus S, Matchan J E, Knott JC, Milton S. Electronic error-reporting systems: A case study into the impact on nurse reporting of medical errors. Nursing
Outlook. Mosby. 2013, Vol. 61, Issue 6, pp. 417 -
228:
Lederman RM, Dreyfus S, Matchan J E, Knott JC, Milton S. Electronic error-reporting systems: A case study into the impact on nurse reporting of medical errors. Nursing
Outlook. Mosby. 2013, Vol. 61, Issue 6, pp. 417 -
342:
Lederman R, Dreyfus S. Managing Health
Information Delivery Processes for Better Medical Decision Making. DSS 2.0 - Supporting Decision Making with New Technologies. IOS Press. 2014, Vol. 261.
101:
reports with the aim of allowing doctors to improve communication with patients and families regarding the status of their diseases in progressive and chronic illnesses such as diabetes.
219:
Brown, AJ, Vanderkerckhov, W, Dreyfus, S (2014). ‘The relationship between transparency, whistleblowing and public trust’. Research
Handbook on Transparency, Edward Elgar, Cheltenham UK
298:
Lederman R, Kurnia S, Peng F, Dreyfus S (2015). "Tick a box, any box: A case study on the unintended consequences of system misuse in a hospital emergency department".
93:
has focused on the patient information experience in the health system and the role of technology in error incident reporting in hospital settings. She has co-invented
380:
Dreyfus, S., Lederman, R., Smith P., Monagle, P. (2011) "Customising pathology report design for patient use". Electronic Journal of Health Informatics. Vol 6, No. 2.
239:
Pang, F. R Sharma, R Lederman, S Dreyfus (2011). "Organisational Culture and Organisational Impacts of Information Systems: A Review of the Empirical Literature".
570:
575:
389:
Slaughter, Y, Hajek, J, Smith, W, Chang, S, Dreyfus, S. (2015). ‘The online delivery of language programs: Bridging the divide in languages education.’
254:
65:
is an Australian technology researcher, journalist, and academic. She is a lecturer in the Department of Computing and Information Systems at the
371:
Lederman, R and Dreyfus, S. (2014). ‘Tailoring Patient Information To Encourage Patient Engagement’. ECIS e-Health Workshop Tel Aviv University
536:
489:
640:
610:
605:
108:-speaking primary school students, particularly for difficult languages that require more hours of practice such as Asian languages.
635:
600:
580:
461:
Dreyfus, S and Chang, S (2016). ‘FBI vs Apple: giving up security and privacy could hurt us all’. The Conversation. 24 Feb.
625:
190:
595:
590:
403:
479:
Dreyfus, S (2015). ‘The security paradox: individual privacy versus digital driftnets’. The Conversation. 30 March.
630:
470:
Dreyfus, S (2016). ‘Governments undermining encryption will do more harm than good’. The Conversation. 13 Jan.
615:
69:, as well as the principal researcher on the impact of digital technologies on whistleblowing as a form of
620:
165:
153:
147:
53:
90:
160:
who is credited as a researcher for the book. Dreyfus released it in e-version in 2001 for free.
66:
565:
532:
248:
429:
191:"Suelette Dreyfus: School of Computing and Information Systems, The University of Melbourne"
585:
8:
104:
Her research in education has focused on using social media to teach foreign language to
315:
241:
Proceedings of 21st Australasian Conference on Information Systems, Brisbane, Australia
133:
437:
319:
70:
113:
550:
307:
105:
74:
540:
152:
The book describes the exploits of a group of Australian, American, and British
157:
78:
559:
441:
198:
163:
Dreyfus was an Associate Producer and interview subject for the documentary
311:
238:
515:
533:
Underground: Hacking, Madness and Obsession on the Electronic Frontier
148:
Underground: Hacking, Madness and Obsession on the Electronic Frontier
98:
94:
404:"Resurrect FOI & end security clearance creep to restore trust"
390:
297:
490:"Suelette Dreyfus speaks on Julian Assange e Wikileaks"
156:during the late 1980s and early 1990s, among them
557:
300:Journal of Information Technology Teaching Cases
571:Academic staff of the University of Melbourne
393:20th National Languages Conference. Melbourne
73:. Her research includes information systems,
422:
253:: CS1 maint: multiple names: authors list (
77:, privacy, and the impact of technology on
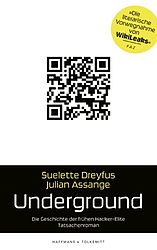
576:Australian people of French-Jewish descent
132:
81:, health informatics and e-education.
558:
16:Australian researcher and journalist
145:She is the author of the 1997 book
13:
547:Works by or about Suelette Dreyfus
14:
652:
526:
119:Her essays have also appeared in
641:People associated with WikiLeaks
611:Australian political journalists
606:Australian freelance journalists
636:Information systems researchers
601:Australian computer specialists
581:Writers about computer security
508:
482:
473:
464:
455:
396:
383:
374:
365:
355:
345:
336:
326:
291:
281:
271:
261:
232:
222:
213:
183:
126:
42:Researcher, journalist, writer
1:
430:"Exposed: Wikileaks' secrets"
176:
7:
166:In the Realm of the Hackers
10:
657:
626:Journalists from Melbourne
97:in information design for
84:
46:
38:
30:
23:
596:Australian women writers
591:Activists from Melbourne
114:WikiLeaks advisory board
67:University of Melbourne
631:Open content activists
539:21 August 2012 at the
142:
312:10.1057/jittc.2015.13
136:
71:freedom of expression
616:Australian producers
201:on 13 November 2019
621:Internet activists
516:"Suelette Dreyfus"
494:Cyber Security 360
195:cis.unimelb.edu.au
143:
137:German cover from
89:Dreyfus' work in
60:
59:
648:
551:Internet Archive
520:
519:
512:
506:
505:
503:
501:
486:
480:
477:
471:
468:
462:
459:
453:
452:
450:
448:
426:
420:
419:
417:
415:
410:. 21 August 2015
400:
394:
387:
381:
378:
372:
369:
363:
359:
353:
349:
343:
340:
334:
330:
324:
323:
295:
289:
285:
279:
275:
269:
265:
259:
258:
252:
244:
236:
230:
226:
220:
217:
211:
210:
208:
206:
197:. Archived from
187:
121:The Conversation
75:digital security
63:Suelette Dreyfus
49:
25:Suelette Dreyfus
21:
20:
656:
655:
651:
650:
649:
647:
646:
645:
556:
555:
541:Wayback Machine
529:
524:
523:
514:
513:
509:
499:
497:
488:
487:
483:
478:
474:
469:
465:
460:
456:
446:
444:
428:
427:
423:
413:
411:
402:
401:
397:
388:
384:
379:
375:
370:
366:
360:
356:
350:
346:
341:
337:
331:
327:
296:
292:
286:
282:
276:
272:
266:
262:
246:
245:
237:
233:
227:
223:
218:
214:
204:
202:
189:
188:
184:
179:
131:
87:
47:
26:
17:
12:
11:
5:
654:
644:
643:
638:
633:
628:
623:
618:
613:
608:
603:
598:
593:
588:
583:
578:
573:
568:
554:
553:
544:
528:
527:External links
525:
522:
521:
507:
496:. 19 June 2018
481:
472:
463:
454:
421:
395:
382:
373:
364:
354:
344:
335:
325:
290:
280:
270:
260:
231:
221:
212:
181:
180:
178:
175:
169:, inspired by
158:Julian Assange
130:
125:
86:
83:
79:whistleblowing
58:
57:
50:
44:
43:
40:
36:
35:
32:
28:
27:
24:
15:
9:
6:
4:
3:
2:
653:
642:
639:
637:
634:
632:
629:
627:
624:
622:
619:
617:
614:
612:
609:
607:
604:
602:
599:
597:
594:
592:
589:
587:
584:
582:
579:
577:
574:
572:
569:
567:
566:Living people
564:
563:
561:
552:
548:
545:
542:
538:
534:
531:
530:
517:
511:
495:
491:
485:
476:
467:
458:
443:
439:
435:
431:
425:
409:
405:
399:
392:
386:
377:
368:
358:
348:
339:
329:
321:
317:
313:
309:
305:
301:
294:
284:
274:
264:
256:
250:
242:
235:
225:
216:
200:
196:
192:
186:
182:
174:
172:
168:
167:
161:
159:
155:
151:
149:
140:
135:
129:
124:
122:
117:
115:
109:
107:
102:
100:
96:
92:
82:
80:
76:
72:
68:
64:
56:
55:
51:
45:
41:
39:Occupation(s)
37:
33:
29:
22:
19:
510:
498:. Retrieved
493:
484:
475:
466:
457:
445:. Retrieved
433:
424:
412:. Retrieved
408:The Mandarin
407:
398:
385:
376:
367:
357:
347:
338:
328:
306:(2): 74–83.
303:
299:
293:
283:
273:
263:
249:cite journal
240:
234:
224:
215:
203:. Retrieved
199:the original
194:
185:
170:
164:
162:
146:
144:
138:
127:
120:
118:
110:
103:
88:
62:
61:
52:
48:Notable work
18:
586:Cypherpunks
500:13 November
414:13 November
205:13 November
173:, in 2003.
171:Underground
139:Underground
128:Underground
54:Underground
31:Nationality
560:Categories
177:References
95:prototypes
34:Australian
442:1357-0978
320:110123206
99:pathology
537:Archived
447:13 March
434:Wired UK
91:e-health
549:at the
518:. IMDb.
154:hackers
106:English
440:
391:AFMLTA
318:
141:(2011)
85:Career
352:2012.
316:S2CID
268:2012.
502:2019
449:2022
438:ISSN
416:2019
362:426.
333:2012
255:link
229:426.
207:2019
308:doi
562::
492:.
436:.
432:.
406:.
314:.
302:.
288:W.
278:W.
251:}}
247:{{
193:.
116:.
543:)
535:(
504:.
451:.
418:.
322:.
310::
304:5
257:)
243:.
209:.
150:.
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.