481:, and their solutions must be agreed upon by all nodes and reach consensus. The solutions are then used to validate transactions, add blocks and generate new bitcoins. Miners are rewarded for solving these puzzles and successfully adding new blocks. However, the Bitcoin-style mining process is very energy intensive because the proof of work shaped like a lottery mechanism. The underlying computational work has no other use but to provide security to the network that provides open access and has to work in adversarial conditions. Miners have to use a lot of energy to add a new block containing a transaction to the blockchain. The energy used in this competition is what fundamentally gives bitcoin its level of security and resistance to attacks. Also, miners have to invest computer hardwares that need large spaces as fixed cost.
4587:
4611:
230:
4599:
210:
406:
4557:
3458:
2385:
3482:
3470:
2395:
204:
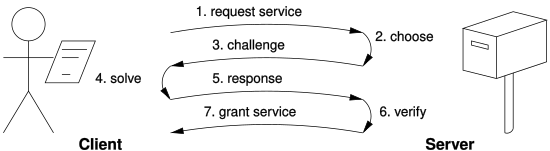
protocols assume a direct interactive link between the requester (client) and the provider (server). The provider chooses a challenge, say an item in a set with a property, the requester finds the relevant response in the set, which is sent back and checked by the provider. As the challenge is chosen
434:
Each block that is added to the blockchain, starting with the block containing a given transaction, is called a confirmation of that transaction. Ideally, merchants and services that receive payment in the cryptocurrency should wait for at least one confirmation to be distributed over the network,
140:
in 1997. It was designed as an anti-spam mechanism that required email senders to perform a small computational task, effectively proving that they expended resources (in the form of CPU time) before sending an email. This task was trivial for legitimate users but would impose a significant cost on
184:
Whether PoW systems can actually solve a particular denial-of-service issue such as the spam problem is subject to debate; the system must make sending spam emails obtrusively unproductive for the spammer, but should also not prevent legitimate users from sending their messages. In other words, a
458:
Some PoWs claim to be ASIC-resistant, i.e. to limit the efficiency gain that an ASIC can have over commodity hardware, like a GPU, to be well under an order of magnitude. ASIC resistance has the advantage of keeping mining economically feasible on commodity hardware, but also contributes to the
392:
PoW. But in
Bitcoin, double-spend protection is provided by a decentralized P2P protocol for tracking transfers of coins, rather than the hardware trusted computing function used by RPoW. Bitcoin has better trustworthiness because it is protected by computation. Bitcoins are "mined" using the
435:
before assuming that the payment was done. The more confirmations that the merchant waits for, the more difficult it is for an attacker to successfully reverse the transaction in a blockchain—unless the attacker controls more than half the total network power, in which case it is called a
282:
computations that allow participants who know a secret, typically a private key, to generate cheap PoWs. The rationale is that mailing-list holders may generate stamps for every recipient without incurring a high cost. Whether such a feature is desirable depends on the usage scenario.
220:
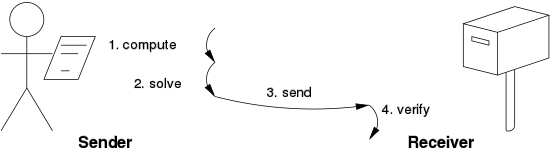
protocols do not assume such a link: as a result, the problem must be self-imposed before a solution is sought by the requester, and the provider must check both the problem choice and the found solution. Most such schemes are unbounded probabilistic iterative procedures such as
185:
genuine user should not encounter any difficulties when sending an email, but an email spammer would have to expend a considerable amount of computing power to send out many emails at once. Proof-of-work systems are being used by other, more complex cryptographic systems such as
273:
if the client must perform few computations, but must collect some tokens from remote servers before querying the final service provider. In this sense, the work is not actually performed by the requester, but it incurs delays anyway because of the latency to get the required
123:
was carried out or that a computational puzzle was "solved", but deterring manipulation of data by establishing large energy and hardware-control requirements to be able to do so. Proof-of-work systems have been criticized by environmentalists for their energy consumption.
144:
Hashcash's system was based on the concept of finding a hash value that met certain criteria, a task that required computational effort and thus served as a "proof of work." The idea was that by making it computationally expensive to send large volumes of email,
205:
on the spot by the provider, its difficulty can be adapted to its current load. The work on the requester side may be bounded if the challenge-response protocol has a known solution (chosen by the provider), or is known to exist within a bounded search space.
455:(ASICs) for PoW. This trend toward mining pools and specialized ASICs has made mining some cryptocurrencies economically infeasible for most players without access to the latest ASICs, nearby sources of inexpensive energy, or other special advantages.
507:
in to continue mining without the use of renewable energy but they will not be allowed to expand or renew permits with the state, no new mining companies that do not completely use renewable energy will not also not be allowed to begin mining.
417:
cryptocurrency. Studies have estimated the total energy consumption of cryptocurrency mining. The PoW mechanism requires a vast amount of computing resources, which consume a significant amount of electricity. 2018 estimates from the
367:
based on "proof of useful work" (PoUW). Rather than miners consuming energy in solving complex, but essentially useless, puzzles to validate transactions, Ofelimos achieves consensus while simultaneously providing a decentralized
924:
80:
in a permissionless decentralized network, in which miners compete to append blocks and mine new currency, each miner experiencing a success probability proportional to the computational effort expended. PoW and PoS
1816:
41:) that a certain amount of a specific computational effort has been expended. Verifiers can subsequently confirm this expenditure with minimal effort on their part. The concept was first implemented in
100:– the computation – must be moderately hard (yet feasible) on the prover or requester side but easy to check for the verifier or service provider. This idea is also known as a CPU cost function,
1887:
Describes a complete money system (including generation, storage, assay, and transfer) based on proof of work functions and the machine architecture problem raised by the use of these functions.
372:. The protocol is built around Doubly Parallel Local Search (DPLS), a local search algorithm that is used as the PoUW component. The paper gives an example that implements a variant of
61:
on a network by requiring some work from a service requester, usually meaning processing time by a computer. The term "proof of work" was first coined and formalized in a 1999 paper by
910:
820:
244:(with the same mean). A generic technique for reducing variance is to use multiple independent sub-challenges, as the average of multiple samples will have a lower variance.
1846:
132:
The concept of Proof of Work (PoW) has its roots in early research on combating spam and preventing denial-of-service attacks. One of the earliest implementations of PoW was
393:
Hashcash proof-of-work function by individual miners and verified by the decentralized nodes in the P2P bitcoin network. The difficulty is periodically adjusted to keep the
1592:
267:
where the computation speed is bound by main memory accesses (either latency or bandwidth), the performance of which is expected to be less sensitive to hardware evolution.
1007:
312:
1808:
4537:
4367:
1437:
360:
1503:
1657:
1259:
859:
178:
including the colon and any amount of whitespace following it up to the digit '1') begins with 52 binary zeros, that is 13 hexadecimal zeros:
4220:
1635:
807:
4140:
3528:
1949:
3557:
2431:
2147:
888:
459:
corresponding risk that an attacker can briefly rent access to a large amount of unspecialized commodity processing power to launch a
152:
One popular system, used in
Hashcash, uses partial hash inversions to prove that computation was done, as a goodwill token to send an
485:
3418:
1838:
987:
754:
725:
2106:
1584:
1301:
783:
452:
1727:
236:
Known-solution protocols tend to have slightly lower variance than unbounded probabilistic protocols because the variance of a
4156:
3398:
1389:
1235:
1175:
1099:
719:
4591:
1320:
581:
165:
158:
3917:
3073:
4084:
3214:
4213:
3408:
2474:
1919:
237:
1954:
1406:
Juels, Ari; Brainard, John (1999). "Client puzzles: A cryptographic defense against connection depletion attacks".
1181:
3521:
3474:
2814:
2000:
1891:
472:
324:
311:
Partial hash inversion This paper formalizes the idea of a proof of work and introduces "the dependent idea of a
66:
1839:"New York governor signs first-of-its-kind law cracking down on bitcoin mining — here's everything that's in it"
1681:
388:
network went online. Bitcoin is a proof-of-work digital currency that, like Finney's RPoW, is also based on the
4416:
4125:
3610:
3562:
2909:
2424:
2258:
1127:
3912:
3388:
2819:
2101:
1470:
1426:
4206:
4130:
2865:
2524:
2275:
1616:
1492:
562:
364:
77:
4641:
4532:
4487:
4300:
3899:
3541:
3537:
2469:
2238:
348:
2977:
1653:
69:
in 2004 through the idea of "reusable proof of work" using the 160-bit secure hash algorithm 1 (SHA-1).
4577:
4411:
3514:
3302:
2939:
363:
conference Crypto 2022 researchers presented a paper describing
Ofelimos, a blockchain protocol with a
1278:
1208:
Abliz, Mehmud; Znati, Taieb (December 2009). "A Guided Tour Puzzle for Denial of
Service Prevention".
4636:
4527:
3795:
3462:
3428:
3403:
3383:
3058:
3048:
2860:
2417:
2253:
2091:
369:
302:
3600:
1536:
1218:
1052:
1010:, a specific comparison that shows how different classes of devices have different processing power.
851:
4517:
4507:
4362:
4135:
3971:
3670:
3665:
3486:
3433:
3353:
2398:
54:
4512:
4502:
4305:
4265:
4258:
4248:
4243:
4058:
3878:
3111:
2987:
2972:
2726:
2587:
1632:
419:
1561:
1463:"An (almost) constant-effort solution-verification proof-of-work protocol based on Merkle trees"
1373:
1364:
4253:
4166:
3552:
3368:
3101:
2944:
2929:
2914:
2840:
2781:
2740:
2459:
2352:
1213:
156:. For instance, the following header represents about 2 hash computations to send a message to
101:
1869:
4631:
4560:
4406:
4352:
4181:
3831:
3785:
3675:
3633:
3618:
3423:
3378:
3038:
3008:
2949:
2761:
2735:
2479:
2464:
2248:
2182:
2137:
2096:
1980:
1912:
1039:
557:
423:
120:
880:
4522:
4446:
3851:
3755:
3705:
3680:
3043:
2967:
2934:
2919:
2845:
1975:
1944:
241:
1882:
1697:
8:
4285:
4176:
4053:
4002:
3941:
3841:
3760:
3720:
3700:
3224:
2060:
1355:
915:
815:
542:
983:
4615:
4391:
4375:
4322:
4110:
4094:
4043:
3628:
3028:
2982:
2533:
2504:
2484:
2305:
2243:
2050:
1939:
1789:
1719:
1253:
1241:
1073:
746:
697:
632:
532:
775:
229:
4451:
4441:
4312:
3987:
3285:
2766:
2494:
2489:
2197:
2152:
1793:
1781:
1723:
1385:
1231:
1171:
1095:
1027:
715:
636:
624:
295:
109:
58:
4598:
1699:
1245:
499:
enacted a two-year moratorium on cryptocurrency mining that does not completely use
104:, computational puzzle, or CPU pricing function. Another common feature is built-in
4386:
4074:
4028:
3790:
3443:
3393:
3373:
3229:
3209:
3179:
2904:
2899:
2880:
2637:
2388:
2311:
2055:
2015:
1905:
1771:
1761:
1711:
1377:
1223:
1163:
1085:
836:
the two best-known – and in the context of cryptocurrencies also most commonly used
705:
662:
614:
500:
496:
209:
62:
2010:
1766:
1749:
984:"Proof of Work can work - Fifth Workshop on the Economics of Information Security"
405:
394:
4603:
4089:
4038:
4033:
3821:
3536:
3413:
3363:
3174:
2327:
2283:
2122:
2030:
1873:
1685:
1639:
1620:
1090:
1084:. Lecture Notes in Computer Science. Vol. 2729. Springer. pp. 426–444.
667:
654:
601:
Lachtar, Nada; Elkhail, Abdulrahman Abu; Bacha, Anys; Malik, Hafiz (2020-07-01).
1167:
1023:
704:. Lecture Notes in Computer Science. Vol. 740. Springer. pp. 139–147.
413:
Since the creation of
Bitcoin, proof-of-work has been the predominant design of
4461:
4381:
4342:
4290:
4275:
4079:
3807:
3239:
3169:
3119:
3023:
2800:
2771:
2543:
2538:
2509:
2440:
2365:
2342:
2132:
1990:
1970:
1331:
1162:. Lecture Notes in Computer Science. Vol. 8976. Springer. pp. 49–62.
920:
552:
547:
527:
489:
258:
90:
82:
967:
Laurie, Ben; Clayton, Richard (May 2004). "Proof-of-work proves not to work".
947:
108:-structures that reward allocating computational capacity to the network with
4625:
4542:
4497:
4456:
4436:
4332:
4295:
4270:
4048:
3292:
2075:
2035:
2020:
1785:
1422:
1381:
1359:
1069:
710:
689:
628:
619:
602:
537:
488:
Erik Thedéen called on the EU to ban the proof of work model in favor of the
50:
30:
3750:
4492:
4337:
4327:
4317:
4280:
4229:
2695:
2582:
2370:
2218:
2213:
2157:
2065:
1715:
414:
86:
27:
1227:
4471:
4161:
4007:
3936:
3932:
3438:
3327:
3199:
3063:
2360:
2142:
2045:
1698:
Savva
Shanaev; Arina Shuraeva; Mikhail Vasenin; Maksim Kuznetsov (2019).
504:
460:
448:
436:
342:
1776:
1300:
Gabber, Eran; Jakobsson, Markus; Matias, Yossi; Mayer, Alain J. (1998).
4431:
4401:
4396:
4357:
3358:
3249:
3194:
3081:
3033:
2959:
2661:
2656:
2454:
2127:
2025:
1995:
1679:
tevador/RandomX: Proof of work algorithm based on random code execution
1152:
522:
4421:
3836:
3715:
3189:
3091:
3018:
2924:
2776:
2040:
1985:
1678:
1077:
693:
137:
116:
105:
46:
3623:
4466:
4426:
4115:
4012:
3997:
3992:
3982:
3946:
3866:
3780:
3660:
3184:
3164:
3144:
3134:
3129:
3053:
3013:
2992:
2855:
2835:
2829:
2809:
2786:
2756:
2686:
2676:
2671:
2631:
2622:
2607:
2602:
2597:
2499:
2409:
2337:
2332:
2070:
1879:
1809:"Ban proof of work crypto mining to save energy, EU regulator says"
1748:
Ciaian, Pavel; Kancs, d’Artis; Rajcaniova, Miroslava (2021-10-21).
1700:"Cryptocurrency Value and 51% Attacks: Evidence from Event Studies"
659:
Secure
Information Networks: Communications and Multimedia Security
503:
as a power source for two years. Existing mining companies will be
389:
222:
146:
133:
42:
1462:
1321:"Defending against denial-of-service attacks with puzzle auctions"
1119:
447:
Within the
Bitcoin community there are groups working together in
247:
There are also fixed-cost functions such as the time-lock puzzle.
3951:
3907:
3685:
3332:
3297:
3254:
3149:
3124:
3096:
2870:
2612:
2577:
2322:
2005:
1928:
911:"Analysis | Bye-Bye, Miners! How Ethereum's Big Change Will Work"
517:
478:
385:
373:
250:
Moreover, the underlying functions used by these schemes may be:
186:
73:
1613:
1120:"Exponential memory-bound functions for proof of work protocols"
603:"A Cross-Stack Approach Towards Defending Against Cryptojacking"
4347:
4120:
3861:
3856:
3826:
3816:
3775:
3770:
3765:
3745:
3740:
3710:
3695:
3655:
3307:
3234:
3154:
3139:
3086:
2890:
2824:
2716:
2666:
2647:
2167:
153:
96:
A key feature of proof-of-work schemes is their asymmetry: the
1372:. Lecture Notes in Computer Science. Vol. 1318. pp.
852:"Proof of Work Explained in Simple Terms - The Chain Bulletin"
261:, as well as from high-end server to low-end portable devices.
170:
It is verified with a single computation by checking that the
3846:
3735:
3690:
3638:
3595:
3590:
3584:
3337:
3275:
3259:
3219:
3204:
3159:
2875:
2700:
2568:
2317:
2172:
1427:"New client puzzle outsourcing techniques for DoS resistance"
171:
16:
System that regulates the formation of blocks on a blockchain
1153:"Cuckoo Cycle: A Memory Bound Graph-Theoretic Proof-of-Work"
65:
and Ari Juels. The concept was adapted to digital tokens by
3961:
3956:
3927:
3922:
3886:
2592:
2514:
1434:
11th ACM Conference on
Computer and Communications Security
1897:
1582:
1420:
1299:
257:
where the computation runs at the speed of the processor,
3730:
3725:
3578:
3280:
3244:
2850:
1557:
1529:"Cambridge Bitcoin Electricity Consumption Index (CBECI)"
1528:
1022:
600:
1274:
1080:(2003). "On Memory-Bound Functions for Fighting Spam".
4368:
Cryptographically secure pseudorandom number generator
969:
Workshop on the
Economics of Information Security 2004
376:, a local search algorithm to solve Boolean problems.
4575:
1747:
1493:"Combinatorial Optimization via Proof-of-Useful-Work"
1210:
2009 Annual Computer Security Applications Conference
3498:
1290:
A popular PoW system. First announced in March 1997.
1026:; Burrows, Mike; Manasse, Mark; Wobber, Ted (2005).
1363:
286:
197:There are two classes of proof-of-work protocols.
1558:"Cambridge Bitcoin Electricity Consumption Index"
1068:
477:Miners compete to solve crypto challenges on the
291:Here is a list of known proof-of-work functions:
4623:
948:"Hashcash - A Denial of Service Counter-Measure"
881:"The Only Crypto Story You Need, by Matt Levine"
698:"Pricing via Processing or Combatting Junk Mail"
1421:Waters, Brent; Juels, Ari; Halderman, John A.;
1302:"Curbing junk e-mail via secure classification"
1064:
1062:
802:
800:
578:On most Unix systems this can be verified with
422:equate Bitcoin's energy consumption to that of
1365:"Auditable metering with lightweight security"
1354:
1018:
1016:
962:
960:
652:
354:
308:Ong–Schnorr–Shamir signature broken by Pollard
4214:
3522:
2425:
1913:
1750:"The economic dependency of bitcoin security"
1583:Michael J. Casey; Paul Vigna (16 June 2014).
1414:
1405:
1319:Wang, Xiao-Feng; Reiter, Michael (May 2003).
966:
379:
315:", a "re-usable proof-of-work" (RPoW) system.
1560:. Cambridge Center For Alternative Finance.
1293:
1059:
797:
776:"What Is Proof of Work (PoW) in Blockchain?"
684:
682:
680:
678:
655:"Proofs of Work and Bread Pudding Protocols"
1399:
1013:
957:
648:
646:
189:, which uses a system similar to Hashcash.
141:spammers attempting to send bulk messages.
4221:
4207:
3529:
3515:
3481:
2432:
2418:
1920:
1906:
1894:for Simplified Payment Verification (SPV).
1328:IEEE Symposium on Security and Privacy '03
1318:
1258:: CS1 maint: location missing publisher (
1207:
1203:
1201:
1146:
1144:
1113:
1111:
409:Bitcoin electricity consumption as of 2021
1775:
1765:
1348:
1312:
1217:
1089:
1028:"Moderately hard, memory-bound functions"
975:
709:
688:
675:
666:
618:
486:European Securities and Markets Authority
466:
442:
181:0000000000000756af69e2ffbdb930261873cd71
1585:"Short-Term Fixes To Avert "51% Attack""
1160:Financial Cryptography and Data Security
1008:How powerful was the Apollo 11 computer?
643:
453:application-specific integrated circuits
404:
174:hash of the stamp (omit the header name
2107:List of people in blockchain technology
1837:Sigalos, MacKenzie (23 November 2022).
1836:
1806:
1454:
1198:
1141:
1108:
982:Liu, Debin; Camp, L. Jean (June 2006).
981:
661:. Kluwer Academic Publishers: 258–272.
429:
72:Proof of work was later popularized by
4624:
3268:
1704:The Journal of Alternative Investments
1651:
1564:from the original on 29 September 2020
1460:
1266:
1117:
908:
653:Jakobsson, Markus; Juels, Ari (1999).
492:model due its lower energy emissions.
4202:
3510:
3399:Decentralized autonomous organization
2413:
1901:
1521:
1509:from the original on 9 September 2022
1150:
400:
93:they are the most common mechanisms.
3469:
2439:
2394:
1654:"The State of Cryptocurrency Mining"
1614:Overview of the Bitcoin mining pools
1082:Advances in Cryptology - CRYPTO 2003
945:
927:from the original on 2 December 2021
846:
844:
1595:from the original on 15 August 2020
1576:
702:Advances in Cryptology — CRYPTO' 92
136:, created by British cryptographer
13:
1660:from the original on 10 March 2020
1212:. Honolulu, HI. pp. 279–288.
909:Kharif, Olga (November 30, 2021).
607:IEEE Computer Architecture Letters
583::::9B760005E92F0DAE | openssl sha1
484:In January 2022 Vice-Chair of the
228:
208:
14:
4653:
3409:Distributed ledger technology law
1876: (archived December 22, 2007)
1863:
1490:
1467:Cryptology ePrint Archive, Report
1124:Cryptology ePrint Archive, Report
841:
826:from the original on 27 June 2023
808:"Cryptocurrencies and blockchain"
57:and other service abuses such as
4609:
4597:
4585:
4556:
4555:
4228:
3480:
3468:
3457:
3456:
2393:
2384:
2383:
1892:Merkle Proof Standardised Format
1272:
747:"RPOW - Reusable Proofs of Work"
278:Finally, some PoW systems offer
240:is lower than the variance of a
1849:from the original on 2022-12-03
1830:
1819:from the original on 2022-04-19
1800:
1741:
1730:from the original on 2021-02-06
1691:
1672:
1645:
1626:
1607:
1550:
1539:from the original on 2020-03-02
1484:
1473:from the original on 2016-08-26
1443:from the original on 2021-04-21
1281:from the original on 2017-09-29
1187:from the original on 2017-07-05
1130:from the original on 2018-04-09
1001:
990:from the original on 2017-08-20
939:
891:from the original on 2023-04-07
862:from the original on 2023-04-01
786:from the original on 2024-01-17
757:from the original on 2023-06-19
728:from the original on 2017-11-26
473:Environmental impact of bitcoin
287:List of proof-of-work functions
112:in the form of cryptocurrency.
4417:Information-theoretic security
4126:NIST hash function competition
2259:2020 Twitter account hijacking
902:
873:
768:
739:
594:
574:
495:In November 2022 the state of
1:
4592:Free and open-source software
2102:List of bitcoin organizations
1767:10.1080/00036846.2021.1931003
1652:Vorick, David (13 May 2018).
588:
127:
115:The purpose of proof-of-work
4131:Password Hashing Competition
3542:message authentication codes
3538:Cryptographic hash functions
2276:The Rise and Rise of Bitcoin
1396:Updated version May 4, 1998.
1091:10.1007/978-3-540-45146-4_25
668:10.1007/978-0-387-35568-9_18
563:Consensus (computer science)
259:which greatly varies in time
119:is not proving that certain
85:) remain the two best known
7:
4533:Message authentication code
4488:Cryptographic hash function
4301:Cryptographic hash function
4085:Merkle–Damgård construction
2470:Cryptographic hash function
2239:Bitcoin scalability problem
1927:
1807:Bateman, Tom (2022-01-19).
1500:IACR conference Crypto 2022
1168:10.1007/978-3-662-48051-9_4
511:
370:optimization problem solver
355:Proof of useful work (PoUW)
349:Guided tour puzzle protocol
192:
87:Sybil deterrence mechanisms
10:
4658:
4412:Harvest now, decrypt later
946:Back, Adam (August 2002).
470:
463:against a cryptocurrency.
380:Bitcoin-type proof of work
296:Integer square root modulo
53:in 1993 as a way to deter
4551:
4528:Post-quantum cryptography
4480:
4236:
4198:
4149:
4103:
4067:
4021:
3970:
3898:
3875:
3804:
3648:
3609:
3571:
3548:
3506:
3502:
3452:
3429:Initial exchange offering
3404:Decentralized application
3384:Cryptocurrency in Nigeria
3346:
3320:
3110:
3072:
3001:
2958:
2889:
2799:
2749:
2725:
2709:
2685:
2646:
2621:
2567:
2557:
2523:
2447:
2379:
2351:
2294:
2267:
2254:2018 Bitcoin bomb threats
2249:2018 cryptocurrency crash
2231:
2206:
2190:
2181:
2115:
2092:List of bitcoin companies
2084:
1963:
1935:
55:denial-of-service attacks
4518:Quantum key distribution
4508:Authenticated encryption
4363:Random number generation
3879:key derivation functions
3434:List of cryptocurrencies
3321:Crypto service companies
3112:Cryptocurrency exchanges
1382:10.1007/3-540-63594-7_75
711:10.1007/3-540-48071-4_10
620:10.1109/LCA.2020.3017457
568:
238:rectangular distribution
164:X-Hashcash: 1:52:380119:
37:) proves to others (the
33:in which one party (the
4513:Public-key cryptography
4503:Symmetric-key algorithm
4306:Key derivation function
4266:Cryptographic primitive
4259:Authentication protocol
4249:Outline of cryptography
4244:History of cryptography
4157:Hash-based cryptography
4059:Length extension attack
1591:. Wall Street Journal.
1461:Coelho, Fabien (2007).
1118:Coelho, Fabien (2005).
420:University of Cambridge
4254:Cryptographic protocol
4167:Message authentication
3369:Complementary currency
2475:Decentralized exchange
2460:Cryptocurrency tumbler
2353:Bitcoin in El Salvador
1716:10.3905/jai.2019.1.081
1370:Financial Cryptography
1306:Financial Cryptography
1047:Cite journal requires
467:Environmental concerns
443:ASICs and mining pools
410:
397:around a target time.
313:bread pudding protocol
233:
213:
4407:End-to-end encryption
4353:Cryptojacking malware
3424:Initial coin offering
3379:Cryptocurrency bubble
2910:Basic Attention Token
2480:Decentralized finance
2465:Cryptocurrency wallet
2138:Cryptocurrency wallet
2097:List of bitcoin forks
1955:Environmental effects
1633:What is an ASIC miner
1228:10.1109/ACSAC.2009.33
751:nakamotoinstitute.org
558:Proof of elapsed time
408:
232:
218:Solution–verification
212:
161:on January 19, 2038:
4523:Quantum cryptography
4447:Trusted timestamping
3419:Environmental impact
3389:Cryptocurrency scams
1976:Andreas Antonopoulos
1642:on digitaltrends.com
1356:Franklin, Matthew K.
1151:Tromp, John (2015).
580:echo -n 1:52:380119:
430:History modification
242:Poisson distribution
167::::9B760005E92F0DAE
89:. In the context of
76:as a foundation for
4286:Cryptographic nonce
4054:Side-channel attack
3074:Inactive currencies
916:The Washington Post
816:European Parliament
543:Proof of personhood
365:consensus mechanism
149:would be reduced.
4642:Energy consumption
4392:Subliminal channel
4376:Pseudorandom noise
4323:Key (cryptography)
4111:CAESAR Competition
4095:HAIFA construction
4044:Brute-force attack
2534:Proof of authority
2505:Non-fungible token
2485:Distributed ledger
2306:Bitcoin Foundation
2244:History of bitcoin
2051:Cameron Winklevoss
1684:2021-09-01 at the
1638:2018-05-22 at the
1623:on blockchain.info
1619:2020-04-21 at the
533:Proof of authority
479:Bitcoin blockchain
451:. Some miners use
411:
401:Energy consumption
234:
214:
202:Challenge–response
4573:
4572:
4569:
4568:
4452:Key-based routing
4442:Trapdoor function
4313:Digital signature
4194:
4193:
4190:
4189:
3988:ChaCha20-Poly1305
3805:Password hashing/
3496:
3495:
3316:
3315:
2795:
2794:
2495:Lightning Network
2407:
2406:
2299:
2227:
2226:
2198:Bitcoin Unlimited
2153:Lightning Network
1760:(49): 5738–5755.
1754:Applied Economics
1491:Fitzi, Matthias.
1423:Felten, Edward W.
1391:978-3-540-63594-9
1237:978-1-4244-5327-6
1177:978-3-662-48050-2
1101:978-3-540-40674-7
856:chainbulletin.com
721:978-3-540-57340-1
4649:
4637:Cryptocurrencies
4614:
4613:
4612:
4602:
4601:
4590:
4589:
4588:
4581:
4559:
4558:
4387:Insecure channel
4223:
4216:
4209:
4200:
4199:
4075:Avalanche effect
4029:Collision attack
3572:Common functions
3531:
3524:
3517:
3508:
3507:
3504:
3503:
3500:
3499:
3484:
3483:
3472:
3471:
3460:
3459:
3444:Virtual currency
3394:Digital currency
3374:Crypto-anarchism
3266:
3265:
3019:HBAR (Hashgraph)
3002:Other currencies
2638:Ethereum Classic
2565:
2564:
2441:Cryptocurrencies
2434:
2427:
2420:
2411:
2410:
2397:
2396:
2387:
2386:
2312:Bitcoin Magazine
2297:
2188:
2187:
2056:Tyler Winklevoss
2016:Satoshi Nakamoto
1922:
1915:
1908:
1899:
1898:
1858:
1857:
1855:
1854:
1834:
1828:
1827:
1825:
1824:
1804:
1798:
1797:
1779:
1769:
1745:
1739:
1738:
1736:
1735:
1695:
1689:
1676:
1670:
1669:
1667:
1665:
1649:
1643:
1630:
1624:
1611:
1605:
1604:
1602:
1600:
1580:
1574:
1573:
1571:
1569:
1554:
1548:
1547:
1545:
1544:
1525:
1519:
1518:
1516:
1514:
1508:
1497:
1488:
1482:
1481:
1479:
1478:
1458:
1452:
1451:
1449:
1448:
1442:
1431:
1418:
1412:
1411:
1403:
1397:
1395:
1367:
1352:
1346:
1345:
1343:
1342:
1336:
1330:. Archived from
1325:
1316:
1310:
1309:
1297:
1291:
1289:
1287:
1286:
1270:
1264:
1263:
1257:
1249:
1221:
1205:
1196:
1195:
1193:
1192:
1186:
1157:
1148:
1139:
1138:
1136:
1135:
1115:
1106:
1105:
1093:
1074:Goldberg, Andrew
1066:
1057:
1056:
1050:
1045:
1043:
1035:
1020:
1011:
1005:
999:
998:
996:
995:
979:
973:
972:
964:
955:
954:
952:
943:
937:
936:
934:
932:
906:
900:
899:
897:
896:
877:
871:
870:
868:
867:
848:
839:
838:
833:
831:
825:
812:
804:
795:
794:
792:
791:
772:
766:
765:
763:
762:
743:
737:
736:
734:
733:
713:
686:
673:
672:
670:
650:
641:
640:
622:
598:
584:
577:
501:renewable energy
177:
160:
91:cryptocurrencies
63:Markus Jakobsson
4657:
4656:
4652:
4651:
4650:
4648:
4647:
4646:
4622:
4621:
4620:
4610:
4608:
4596:
4586:
4584:
4576:
4574:
4565:
4547:
4476:
4232:
4227:
4186:
4145:
4104:Standardization
4099:
4090:Sponge function
4063:
4039:Birthday attack
4034:Preimage attack
4017:
3973:
3966:
3894:
3877:
3876:General purpose
3871:
3806:
3800:
3649:Other functions
3644:
3611:SHA-3 finalists
3605:
3567:
3544:
3535:
3497:
3492:
3448:
3414:Double-spending
3364:Blockchain game
3342:
3312:
3264:
3106:
3068:
2997:
2954:
2885:
2791:
2745:
2721:
2705:
2681:
2642:
2617:
2553:
2519:
2443:
2438:
2408:
2403:
2375:
2347:
2328:Canaan Creative
2298:(not exchanges)
2296:
2290:
2263:
2223:
2202:
2177:
2123:Bitcoin network
2111:
2080:
2031:Vitalik Buterin
1981:Brian Armstrong
1959:
1931:
1926:
1874:Wayback Machine
1870:Finney's system
1866:
1861:
1852:
1850:
1835:
1831:
1822:
1820:
1805:
1801:
1746:
1742:
1733:
1731:
1696:
1692:
1686:Wayback Machine
1677:
1673:
1663:
1661:
1650:
1646:
1640:Wayback Machine
1631:
1627:
1621:Wayback Machine
1612:
1608:
1598:
1596:
1581:
1577:
1567:
1565:
1556:
1555:
1551:
1542:
1540:
1527:
1526:
1522:
1512:
1510:
1506:
1495:
1489:
1485:
1476:
1474:
1459:
1455:
1446:
1444:
1440:
1429:
1419:
1415:
1404:
1400:
1392:
1353:
1349:
1340:
1338:
1334:
1323:
1317:
1313:
1298:
1294:
1284:
1282:
1271:
1267:
1251:
1250:
1238:
1219:10.1.1.597.6304
1206:
1199:
1190:
1188:
1184:
1178:
1155:
1149:
1142:
1133:
1131:
1116:
1109:
1102:
1067:
1060:
1048:
1046:
1037:
1036:
1021:
1014:
1006:
1002:
993:
991:
980:
976:
965:
958:
950:
944:
940:
930:
928:
907:
903:
894:
892:
879:
878:
874:
865:
863:
850:
849:
842:
829:
827:
823:
810:
806:
805:
798:
789:
787:
774:
773:
769:
760:
758:
745:
744:
740:
731:
729:
722:
687:
676:
651:
644:
599:
595:
591:
579:
571:
514:
475:
469:
445:
432:
403:
382:
357:
289:
195:
182:
175:
168:
157:
130:
26:) is a form of
17:
12:
11:
5:
4655:
4645:
4644:
4639:
4634:
4619:
4618:
4606:
4594:
4571:
4570:
4567:
4566:
4564:
4563:
4552:
4549:
4548:
4546:
4545:
4540:
4538:Random numbers
4535:
4530:
4525:
4520:
4515:
4510:
4505:
4500:
4495:
4490:
4484:
4482:
4478:
4477:
4475:
4474:
4469:
4464:
4462:Garlic routing
4459:
4454:
4449:
4444:
4439:
4434:
4429:
4424:
4419:
4414:
4409:
4404:
4399:
4394:
4389:
4384:
4382:Secure channel
4379:
4373:
4372:
4371:
4360:
4355:
4350:
4345:
4343:Key stretching
4340:
4335:
4330:
4325:
4320:
4315:
4310:
4309:
4308:
4303:
4293:
4291:Cryptovirology
4288:
4283:
4278:
4276:Cryptocurrency
4273:
4268:
4263:
4262:
4261:
4251:
4246:
4240:
4238:
4234:
4233:
4226:
4225:
4218:
4211:
4203:
4196:
4195:
4192:
4191:
4188:
4187:
4185:
4184:
4179:
4174:
4169:
4164:
4159:
4153:
4151:
4147:
4146:
4144:
4143:
4138:
4133:
4128:
4123:
4118:
4113:
4107:
4105:
4101:
4100:
4098:
4097:
4092:
4087:
4082:
4080:Hash collision
4077:
4071:
4069:
4065:
4064:
4062:
4061:
4056:
4051:
4046:
4041:
4036:
4031:
4025:
4023:
4019:
4018:
4016:
4015:
4010:
4005:
4000:
3995:
3990:
3985:
3979:
3977:
3968:
3967:
3965:
3964:
3959:
3954:
3949:
3944:
3939:
3930:
3925:
3920:
3915:
3910:
3904:
3902:
3896:
3895:
3893:
3892:
3889:
3883:
3881:
3873:
3872:
3870:
3869:
3864:
3859:
3854:
3849:
3844:
3839:
3834:
3829:
3824:
3819:
3813:
3811:
3808:key stretching
3802:
3801:
3799:
3798:
3793:
3788:
3783:
3778:
3773:
3768:
3763:
3758:
3753:
3748:
3743:
3738:
3733:
3728:
3723:
3718:
3713:
3708:
3703:
3698:
3693:
3688:
3683:
3678:
3673:
3668:
3663:
3658:
3652:
3650:
3646:
3645:
3643:
3642:
3636:
3631:
3626:
3621:
3615:
3613:
3607:
3606:
3604:
3603:
3598:
3593:
3588:
3582:
3575:
3573:
3569:
3568:
3566:
3565:
3560:
3555:
3549:
3546:
3545:
3534:
3533:
3526:
3519:
3511:
3494:
3493:
3491:
3490:
3478:
3466:
3453:
3450:
3449:
3447:
3446:
3441:
3436:
3431:
3426:
3421:
3416:
3411:
3406:
3401:
3396:
3391:
3386:
3381:
3376:
3371:
3366:
3361:
3356:
3350:
3348:
3347:Related topics
3344:
3343:
3341:
3340:
3335:
3330:
3324:
3322:
3318:
3317:
3314:
3313:
3311:
3310:
3305:
3300:
3295:
3290:
3289:
3288:
3278:
3272:
3270:
3263:
3262:
3257:
3252:
3247:
3242:
3237:
3232:
3227:
3222:
3217:
3212:
3207:
3202:
3197:
3192:
3187:
3182:
3177:
3172:
3167:
3162:
3157:
3152:
3147:
3142:
3137:
3132:
3127:
3122:
3116:
3114:
3108:
3107:
3105:
3104:
3099:
3094:
3089:
3084:
3078:
3076:
3070:
3069:
3067:
3066:
3061:
3056:
3051:
3046:
3041:
3036:
3031:
3026:
3021:
3016:
3011:
3005:
3003:
2999:
2998:
2996:
2995:
2990:
2985:
2980:
2975:
2970:
2964:
2962:
2956:
2955:
2953:
2952:
2947:
2942:
2937:
2932:
2927:
2922:
2917:
2912:
2907:
2902:
2896:
2894:
2887:
2886:
2884:
2883:
2878:
2873:
2868:
2863:
2858:
2853:
2848:
2843:
2838:
2833:
2827:
2822:
2817:
2812:
2806:
2804:
2801:Proof of stake
2797:
2796:
2793:
2792:
2790:
2789:
2784:
2779:
2774:
2772:Nervos Network
2769:
2764:
2759:
2753:
2751:
2747:
2746:
2744:
2743:
2738:
2732:
2730:
2723:
2722:
2720:
2719:
2713:
2711:
2707:
2706:
2704:
2703:
2698:
2692:
2690:
2683:
2682:
2680:
2679:
2674:
2669:
2664:
2659:
2653:
2651:
2644:
2643:
2641:
2640:
2635:
2628:
2626:
2619:
2618:
2616:
2615:
2610:
2605:
2600:
2595:
2590:
2585:
2580:
2574:
2572:
2562:
2555:
2554:
2552:
2551:
2546:
2544:Proof of stake
2541:
2539:Proof of space
2536:
2530:
2528:
2521:
2520:
2518:
2517:
2512:
2510:Smart contract
2507:
2502:
2497:
2492:
2487:
2482:
2477:
2472:
2467:
2462:
2457:
2451:
2449:
2445:
2444:
2437:
2436:
2429:
2422:
2414:
2405:
2404:
2402:
2401:
2391:
2380:
2377:
2376:
2374:
2373:
2368:
2363:
2357:
2355:
2349:
2348:
2346:
2345:
2340:
2335:
2330:
2325:
2320:
2315:
2308:
2302:
2300:
2295:Legal entities
2292:
2291:
2289:
2288:
2280:
2271:
2269:
2265:
2264:
2262:
2261:
2256:
2251:
2246:
2241:
2235:
2233:
2229:
2228:
2225:
2224:
2222:
2221:
2216:
2210:
2208:
2204:
2203:
2201:
2200:
2194:
2192:
2185:
2179:
2178:
2176:
2175:
2170:
2165:
2160:
2155:
2150:
2145:
2140:
2135:
2133:Cryptocurrency
2130:
2125:
2119:
2117:
2113:
2112:
2110:
2109:
2104:
2099:
2094:
2088:
2086:
2082:
2081:
2079:
2078:
2073:
2068:
2063:
2058:
2053:
2048:
2043:
2038:
2033:
2028:
2023:
2018:
2013:
2008:
2003:
1998:
1993:
1991:Wences Casares
1988:
1983:
1978:
1973:
1971:Gavin Andresen
1967:
1965:
1961:
1960:
1958:
1957:
1952:
1947:
1942:
1936:
1933:
1932:
1925:
1924:
1917:
1910:
1902:
1896:
1895:
1889:
1877:
1865:
1864:External links
1862:
1860:
1859:
1829:
1799:
1740:
1690:
1671:
1644:
1625:
1606:
1575:
1549:
1520:
1483:
1453:
1413:
1398:
1390:
1360:Malkhi, Dahlia
1347:
1311:
1292:
1265:
1236:
1197:
1176:
1140:
1107:
1100:
1070:Dwork, Cynthia
1058:
1049:|journal=
1012:
1000:
974:
956:
938:
921:Bloomberg News
901:
872:
840:
796:
767:
738:
720:
690:Dwork, Cynthia
674:
642:
613:(2): 126–129.
592:
590:
587:
586:
585:
570:
567:
566:
565:
560:
555:
553:Proof of stake
550:
548:Proof of space
545:
540:
535:
530:
528:Cryptocurrency
525:
520:
513:
510:
490:proof of stake
468:
465:
444:
441:
431:
428:
402:
399:
381:
378:
356:
353:
352:
351:
346:
340:
337:
334:
331:
328:
325:Diffie-Hellman
322:
319:
318:Hash sequences
316:
309:
306:
299:
288:
285:
276:
275:
268:
262:
227:
226:
207:
206:
194:
191:
180:
163:
129:
126:
83:proof of stake
15:
9:
6:
4:
3:
2:
4654:
4643:
4640:
4638:
4635:
4633:
4630:
4629:
4627:
4617:
4607:
4605:
4600:
4595:
4593:
4583:
4582:
4579:
4562:
4554:
4553:
4550:
4544:
4543:Steganography
4541:
4539:
4536:
4534:
4531:
4529:
4526:
4524:
4521:
4519:
4516:
4514:
4511:
4509:
4506:
4504:
4501:
4499:
4498:Stream cipher
4496:
4494:
4491:
4489:
4486:
4485:
4483:
4479:
4473:
4470:
4468:
4465:
4463:
4460:
4458:
4457:Onion routing
4455:
4453:
4450:
4448:
4445:
4443:
4440:
4438:
4437:Shared secret
4435:
4433:
4430:
4428:
4425:
4423:
4420:
4418:
4415:
4413:
4410:
4408:
4405:
4403:
4400:
4398:
4395:
4393:
4390:
4388:
4385:
4383:
4380:
4377:
4374:
4369:
4366:
4365:
4364:
4361:
4359:
4356:
4354:
4351:
4349:
4346:
4344:
4341:
4339:
4336:
4334:
4333:Key generator
4331:
4329:
4326:
4324:
4321:
4319:
4316:
4314:
4311:
4307:
4304:
4302:
4299:
4298:
4297:
4296:Hash function
4294:
4292:
4289:
4287:
4284:
4282:
4279:
4277:
4274:
4272:
4271:Cryptanalysis
4269:
4267:
4264:
4260:
4257:
4256:
4255:
4252:
4250:
4247:
4245:
4242:
4241:
4239:
4235:
4231:
4224:
4219:
4217:
4212:
4210:
4205:
4204:
4201:
4197:
4183:
4180:
4178:
4175:
4173:
4172:Proof of work
4170:
4168:
4165:
4163:
4160:
4158:
4155:
4154:
4152:
4148:
4142:
4139:
4137:
4134:
4132:
4129:
4127:
4124:
4122:
4119:
4117:
4114:
4112:
4109:
4108:
4106:
4102:
4096:
4093:
4091:
4088:
4086:
4083:
4081:
4078:
4076:
4073:
4072:
4070:
4066:
4060:
4057:
4055:
4052:
4050:
4049:Rainbow table
4047:
4045:
4042:
4040:
4037:
4035:
4032:
4030:
4027:
4026:
4024:
4020:
4014:
4011:
4009:
4006:
4004:
4001:
3999:
3996:
3994:
3991:
3989:
3986:
3984:
3981:
3980:
3978:
3975:
3972:Authenticated
3969:
3963:
3960:
3958:
3955:
3953:
3950:
3948:
3945:
3943:
3940:
3938:
3934:
3931:
3929:
3926:
3924:
3921:
3919:
3916:
3914:
3911:
3909:
3906:
3905:
3903:
3901:
3900:MAC functions
3897:
3890:
3888:
3885:
3884:
3882:
3880:
3874:
3868:
3865:
3863:
3860:
3858:
3855:
3853:
3850:
3848:
3845:
3843:
3840:
3838:
3835:
3833:
3830:
3828:
3825:
3823:
3820:
3818:
3815:
3814:
3812:
3809:
3803:
3797:
3794:
3792:
3789:
3787:
3784:
3782:
3779:
3777:
3774:
3772:
3769:
3767:
3764:
3762:
3759:
3757:
3754:
3752:
3749:
3747:
3744:
3742:
3739:
3737:
3734:
3732:
3729:
3727:
3724:
3722:
3719:
3717:
3714:
3712:
3709:
3707:
3704:
3702:
3699:
3697:
3694:
3692:
3689:
3687:
3684:
3682:
3679:
3677:
3674:
3672:
3669:
3667:
3664:
3662:
3659:
3657:
3654:
3653:
3651:
3647:
3640:
3637:
3635:
3632:
3630:
3627:
3625:
3622:
3620:
3617:
3616:
3614:
3612:
3608:
3602:
3599:
3597:
3594:
3592:
3589:
3587:(compromised)
3586:
3583:
3581:(compromised)
3580:
3577:
3576:
3574:
3570:
3564:
3563:Known attacks
3561:
3559:
3556:
3554:
3551:
3550:
3547:
3543:
3539:
3532:
3527:
3525:
3520:
3518:
3513:
3512:
3509:
3505:
3501:
3489:
3488:
3479:
3477:
3476:
3467:
3465:
3464:
3455:
3454:
3451:
3445:
3442:
3440:
3437:
3435:
3432:
3430:
3427:
3425:
3422:
3420:
3417:
3415:
3412:
3410:
3407:
3405:
3402:
3400:
3397:
3395:
3392:
3390:
3387:
3385:
3382:
3380:
3377:
3375:
3372:
3370:
3367:
3365:
3362:
3360:
3357:
3355:
3352:
3351:
3349:
3345:
3339:
3336:
3334:
3331:
3329:
3326:
3325:
3323:
3319:
3309:
3306:
3304:
3301:
3299:
3296:
3294:
3293:LocalBitcoins
3291:
3287:
3284:
3283:
3282:
3279:
3277:
3274:
3273:
3271:
3267:
3261:
3258:
3256:
3253:
3251:
3248:
3246:
3243:
3241:
3238:
3236:
3233:
3231:
3228:
3226:
3225:ItBit (Paxos)
3223:
3221:
3218:
3216:
3213:
3211:
3208:
3206:
3203:
3201:
3198:
3196:
3193:
3191:
3188:
3186:
3183:
3181:
3178:
3176:
3173:
3171:
3168:
3166:
3163:
3161:
3158:
3156:
3153:
3151:
3148:
3146:
3143:
3141:
3138:
3136:
3133:
3131:
3128:
3126:
3123:
3121:
3118:
3117:
3115:
3113:
3109:
3103:
3100:
3098:
3095:
3093:
3090:
3088:
3085:
3083:
3080:
3079:
3077:
3075:
3071:
3065:
3062:
3060:
3057:
3055:
3052:
3050:
3047:
3045:
3042:
3040:
3037:
3035:
3032:
3030:
3027:
3025:
3022:
3020:
3017:
3015:
3012:
3010:
3007:
3006:
3004:
3000:
2994:
2991:
2989:
2986:
2984:
2981:
2979:
2976:
2974:
2971:
2969:
2966:
2965:
2963:
2961:
2957:
2951:
2948:
2946:
2943:
2941:
2938:
2936:
2933:
2931:
2928:
2926:
2923:
2921:
2918:
2916:
2913:
2911:
2908:
2906:
2903:
2901:
2898:
2897:
2895:
2892:
2888:
2882:
2879:
2877:
2874:
2872:
2869:
2867:
2864:
2862:
2859:
2857:
2854:
2852:
2849:
2847:
2844:
2842:
2839:
2837:
2834:
2831:
2828:
2826:
2823:
2821:
2818:
2816:
2813:
2811:
2808:
2807:
2805:
2802:
2798:
2788:
2785:
2783:
2780:
2778:
2775:
2773:
2770:
2768:
2765:
2763:
2760:
2758:
2755:
2754:
2752:
2748:
2742:
2739:
2737:
2734:
2733:
2731:
2728:
2724:
2718:
2715:
2714:
2712:
2710:RandomX-based
2708:
2702:
2699:
2697:
2694:
2693:
2691:
2688:
2684:
2678:
2675:
2673:
2670:
2668:
2665:
2663:
2660:
2658:
2655:
2654:
2652:
2649:
2645:
2639:
2636:
2633:
2630:
2629:
2627:
2624:
2620:
2614:
2611:
2609:
2606:
2604:
2601:
2599:
2596:
2594:
2591:
2589:
2586:
2584:
2581:
2579:
2576:
2575:
2573:
2570:
2566:
2563:
2560:
2559:Proof of work
2556:
2550:
2549:Proof of work
2547:
2545:
2542:
2540:
2537:
2535:
2532:
2531:
2529:
2526:
2522:
2516:
2513:
2511:
2508:
2506:
2503:
2501:
2498:
2496:
2493:
2491:
2488:
2486:
2483:
2481:
2478:
2476:
2473:
2471:
2468:
2466:
2463:
2461:
2458:
2456:
2453:
2452:
2450:
2446:
2442:
2435:
2430:
2428:
2423:
2421:
2416:
2415:
2412:
2400:
2392:
2390:
2382:
2381:
2378:
2372:
2369:
2367:
2366:Bitcoin Beach
2364:
2362:
2359:
2358:
2356:
2354:
2350:
2344:
2341:
2339:
2336:
2334:
2331:
2329:
2326:
2324:
2321:
2319:
2316:
2314:
2313:
2309:
2307:
2304:
2303:
2301:
2293:
2286:
2285:
2281:
2278:
2277:
2273:
2272:
2270:
2266:
2260:
2257:
2255:
2252:
2250:
2247:
2245:
2242:
2240:
2237:
2236:
2234:
2230:
2220:
2217:
2215:
2212:
2211:
2209:
2205:
2199:
2196:
2195:
2193:
2189:
2186:
2184:
2180:
2174:
2171:
2169:
2166:
2164:
2163:Proof of work
2161:
2159:
2156:
2154:
2151:
2149:
2146:
2144:
2141:
2139:
2136:
2134:
2131:
2129:
2126:
2124:
2121:
2120:
2118:
2114:
2108:
2105:
2103:
2100:
2098:
2095:
2093:
2090:
2089:
2087:
2083:
2077:
2076:Erik Voorhees
2074:
2072:
2069:
2067:
2064:
2062:
2059:
2057:
2054:
2052:
2049:
2047:
2044:
2042:
2039:
2037:
2036:Ross Ulbricht
2034:
2032:
2029:
2027:
2024:
2022:
2021:Charlie Shrem
2019:
2017:
2014:
2012:
2011:Mark Karpelès
2009:
2007:
2004:
2002:
1999:
1997:
1994:
1992:
1989:
1987:
1984:
1982:
1979:
1977:
1974:
1972:
1969:
1968:
1966:
1962:
1956:
1953:
1951:
1948:
1946:
1943:
1941:
1938:
1937:
1934:
1930:
1923:
1918:
1916:
1911:
1909:
1904:
1903:
1900:
1893:
1890:
1888:
1884:
1881:
1878:
1875:
1871:
1868:
1867:
1848:
1844:
1840:
1833:
1818:
1814:
1810:
1803:
1795:
1791:
1787:
1783:
1778:
1773:
1768:
1763:
1759:
1755:
1751:
1744:
1729:
1725:
1721:
1717:
1713:
1709:
1705:
1701:
1694:
1687:
1683:
1680:
1675:
1659:
1655:
1648:
1641:
1637:
1634:
1629:
1622:
1618:
1615:
1610:
1594:
1590:
1586:
1579:
1563:
1559:
1553:
1538:
1534:
1533:www.cbeci.org
1530:
1524:
1505:
1501:
1494:
1487:
1472:
1468:
1464:
1457:
1439:
1435:
1428:
1424:
1417:
1409:
1402:
1393:
1387:
1383:
1379:
1375:
1371:
1366:
1361:
1357:
1351:
1337:on 2016-03-03
1333:
1329:
1322:
1315:
1307:
1303:
1296:
1280:
1276:
1269:
1261:
1255:
1247:
1243:
1239:
1233:
1229:
1225:
1220:
1215:
1211:
1204:
1202:
1183:
1179:
1173:
1169:
1165:
1161:
1154:
1147:
1145:
1129:
1125:
1121:
1114:
1112:
1103:
1097:
1092:
1087:
1083:
1079:
1075:
1071:
1065:
1063:
1054:
1041:
1034:(2): 299–327.
1033:
1029:
1025:
1024:Abadi, Martín
1019:
1017:
1009:
1004:
989:
985:
978:
970:
963:
961:
949:
942:
926:
922:
918:
917:
912:
905:
890:
886:
885:Bloomberg.com
882:
876:
861:
857:
853:
847:
845:
837:
822:
819:. July 2018.
818:
817:
809:
803:
801:
785:
781:
777:
771:
756:
752:
748:
742:
727:
723:
717:
712:
707:
703:
699:
695:
691:
685:
683:
681:
679:
669:
664:
660:
656:
649:
647:
638:
634:
630:
626:
621:
616:
612:
608:
604:
597:
593:
582:
576:
573:
572:
564:
561:
559:
556:
554:
551:
549:
546:
544:
541:
539:
538:Proof of burn
536:
534:
531:
529:
526:
524:
521:
519:
516:
515:
509:
506:
505:grandfathered
502:
498:
493:
491:
487:
482:
480:
474:
464:
462:
456:
454:
450:
440:
438:
427:
425:
421:
416:
407:
398:
396:
391:
387:
384:In 2009, the
377:
375:
371:
366:
362:
350:
347:
344:
341:
338:
335:
332:
329:
327:–based puzzle
326:
323:
320:
317:
314:
310:
307:
304:
300:
298:a large prime
297:
294:
293:
292:
284:
281:
272:
271:Network-bound
269:
266:
263:
260:
256:
253:
252:
251:
248:
245:
243:
239:
231:
224:
219:
216:
215:
211:
203:
200:
199:
198:
190:
188:
179:
173:
166:
162:
159:
155:
150:
148:
142:
139:
135:
125:
122:
118:
113:
111:
107:
103:
102:client puzzle
99:
94:
92:
88:
84:
79:
75:
70:
68:
64:
60:
56:
52:
51:Cynthia Dwork
48:
44:
40:
36:
32:
29:
28:cryptographic
25:
21:
20:Proof of work
4632:Cryptography
4493:Block cipher
4338:Key schedule
4328:Key exchange
4318:Kleptography
4281:Cryptosystem
4230:Cryptography
4171:
3485:
3473:
3461:
3338:Initiative Q
2696:Bitcoin Gold
2588:Counterparty
2583:Bitcoin Cash
2558:
2548:
2371:Bitcoin City
2310:
2282:
2274:
2219:Bitcoin Gold
2214:Bitcoin Cash
2162:
2116:Technologies
2066:Dave Kleiman
2061:Craig Wright
1950:Legal status
1886:
1851:. Retrieved
1842:
1832:
1821:. Retrieved
1812:
1802:
1777:10419/251105
1757:
1753:
1743:
1732:. Retrieved
1710:(3): 65–77.
1707:
1703:
1693:
1674:
1662:. Retrieved
1647:
1628:
1609:
1597:. Retrieved
1588:
1578:
1568:30 September
1566:. Retrieved
1552:
1541:. Retrieved
1532:
1523:
1511:. Retrieved
1499:
1486:
1475:. Retrieved
1466:
1456:
1445:. Retrieved
1433:
1416:
1407:
1401:
1369:
1350:
1339:. Retrieved
1332:the original
1327:
1314:
1305:
1295:
1283:. Retrieved
1273:Back, Adam.
1268:
1209:
1189:. Retrieved
1159:
1132:. Retrieved
1123:
1081:
1040:cite journal
1031:
1003:
992:. Retrieved
977:
968:
941:
929:. Retrieved
914:
904:
893:. Retrieved
884:
875:
864:. Retrieved
855:
835:
828:. Retrieved
814:
788:. Retrieved
780:Investopedia
779:
770:
759:. Retrieved
750:
741:
730:. Retrieved
701:
658:
610:
606:
596:
575:
494:
483:
476:
457:
449:mining pools
446:
433:
415:Peer-to-peer
412:
383:
358:
339:Cuckoo Cycle
290:
279:
277:
270:
265:Memory-bound
264:
254:
249:
246:
235:
217:
201:
196:
183:
169:
151:
143:
131:
114:
97:
95:
71:
38:
34:
23:
19:
18:
4616:Numismatics
4481:Mathematics
4472:Mix network
4162:Merkle tree
4150:Utilization
4136:NSA Suite B
3439:Token money
3328:Hyperledger
3200:EDX Markets
3064:WhopperCoin
2960:Stablecoins
2361:Bitcoin Law
2287:(2015 film)
2279:(2014 film)
2143:Bitcoin ATM
2046:Cody Wilson
1513:9 September
424:Switzerland
343:Merkle tree
303:Fiat–Shamir
176:X-Hashcash:
4626:Categories
4432:Ciphertext
4402:Decryption
4397:Encryption
4358:Ransomware
3974:encryption
3751:RadioGatún
3558:Comparison
3359:BitLicense
3303:QuadrigaCX
3286:bankruptcy
3250:ShapeShift
3195:Crypto.com
3082:BitConnect
3034:MobileCoin
2803:currencies
2662:Bitconnect
2657:Auroracoin
2561:currencies
2527:mechanisms
2455:Blockchain
2448:Technology
2128:Blockchain
2026:Nick Szabo
2001:Hal Finney
1996:Tim Draper
1853:2022-12-04
1823:2022-01-22
1734:2020-10-28
1664:28 October
1589:Money Beat
1543:2020-02-20
1477:2007-11-25
1447:2019-08-06
1341:2013-04-15
1285:2005-03-02
1275:"HashCash"
1191:2015-09-30
1134:2007-11-04
1078:Naor, Moni
994:2015-12-29
931:13 January
895:2023-04-01
866:2023-04-01
830:29 October
790:2024-01-17
761:2024-01-17
732:2012-09-10
694:Naor, Moni
589:References
523:Bitmessage
471:See also:
461:51% attack
437:51% attack
395:block time
305:signatures
128:Background
117:algorithms
67:Hal Finney
4422:Plaintext
3891:KDF1/KDF2
3810:functions
3796:Whirlpool
3190:Coincheck
3092:KodakCoin
2940:Shiba Inu
2925:KodakCoin
2915:Chainlink
2841:Injective
2815:Avalanche
2777:Primecoin
2525:Consensus
2041:Roger Ver
1986:Adam Back
1945:Economics
1794:231942439
1786:0003-6846
1724:211422987
1688:on Github
1254:cite book
1214:CiteSeerX
637:222070383
629:1556-6056
255:CPU-bound
138:Adam Back
106:incentive
78:consensus
47:Moni Naor
39:verifiers
4604:Internet
4561:Category
4467:Kademlia
4427:Codetext
4370:(CSPRNG)
4116:CRYPTREC
3947:Poly1305
3867:yescrypt
3781:Streebog
3661:CubeHash
3641:(winner)
3463:Category
3185:Coinbase
3165:Bitstamp
3145:Bitpanda
3135:bitFlyer
3130:Bitfinex
3054:SafeMoon
3014:Filecoin
2993:USD Coin
2861:Polkadot
2856:Peercoin
2836:Gridcoin
2830:Ethereum
2810:Algorand
2787:Vertcoin
2757:AmbaCoin
2687:Equihash
2677:Litecoin
2672:Dogecoin
2632:Ethereum
2608:Peercoin
2603:Namecoin
2598:MazaCoin
2500:MetaMask
2389:Category
2338:GHash.io
2333:CoinDesk
2284:Deep Web
2207:Currency
2071:Jihan Wu
1883:Bit gold
1880:bit gold
1847:Archived
1817:Archived
1813:euronews
1728:Archived
1682:Archived
1658:Archived
1636:Archived
1617:Archived
1593:Archived
1562:Archived
1537:Archived
1504:Archived
1471:Archived
1438:Archived
1425:(2004).
1362:(1997).
1279:Archived
1246:14434713
1182:Archived
1128:Archived
988:Archived
925:Archived
889:Archived
860:Archived
821:Archived
784:Archived
755:Archived
726:Archived
696:(1993).
512:See also
497:New York
390:Hashcash
336:Hokkaido
330:Moderate
280:shortcut
223:Hashcash
193:Variants
147:spamming
134:Hashcash
43:Hashcash
4578:Portals
4237:General
4022:Attacks
3952:SipHash
3908:CBC-MAC
3842:LM hash
3822:Balloon
3686:HAS-160
3475:Commons
3354:Airdrop
3333:IQ.Wiki
3298:Mt. Gox
3269:Defunct
3255:Uniswap
3215:Genesis
3150:Bithumb
3125:Binance
3097:OneCoin
3059:Stellar
2945:The DAO
2935:Polygon
2905:Aventus
2820:Cardano
2613:Titcoin
2578:Bitcoin
2569:SHA-256
2399:Commons
2323:Bitmain
2232:History
2006:Wei Dai
1940:History
1929:Bitcoin
1872:at the
1599:30 June
1408:NDSS 99
1374:151–160
518:Bitcoin
386:Bitcoin
374:WalkSAT
359:At the
321:Puzzles
301:Weaken
274:tokens.
187:bitcoin
74:Bitcoin
4348:Keygen
4182:Pepper
4121:NESSIE
4068:Design
3862:scrypt
3857:PBKDF2
3832:Catena
3827:bcrypt
3817:Argon2
3776:Snefru
3771:Shabal
3766:SWIFFT
3746:RIPEMD
3741:N-hash
3716:MASH-2
3711:MASH-1
3696:Kupyna
3656:BLAKE3
3639:Keccak
3624:Grøstl
3601:BLAKE2
3308:Thodex
3235:Kucoin
3230:Kraken
3210:Gemini
3180:Circle
3155:BitMEX
3140:Bitkub
3087:Coinye
3049:Ripple
3024:Helium
2988:Tether
2893:tokens
2891:ERC-20
2866:Solana
2825:EOS.IO
2729:-based
2717:Monero
2689:-based
2667:Coinye
2650:-based
2648:Scrypt
2625:-based
2623:Ethash
2571:-based
2268:Movies
2191:Client
2168:SegWit
1964:People
1792:
1784:
1722:
1388:
1244:
1234:
1216:
1174:
1098:
718:
635:
627:
345:–based
333:Mbound
154:e-mail
35:prover
4378:(PRN)
3976:modes
3852:Makwa
3847:Lyra2
3837:crypt
3786:Tiger
3736:MDC-2
3691:HAVAL
3676:Fugue
3634:Skein
3619:BLAKE
3596:SHA-3
3591:SHA-2
3585:SHA-1
3276:BTC-e
3260:Upbit
3220:Huobi
3205:eToro
3160:Bitso
3102:Petro
2983:Terra
2930:Minds
2900:Augur
2876:Tezos
2871:Steem
2832:(2.0)
2782:Verge
2750:Other
2741:Petro
2701:Zcash
2634:(1.0)
2318:BitGo
2183:Forks
2173:SHA-2
2148:ECDSA
2085:Lists
1790:S2CID
1720:S2CID
1507:(PDF)
1496:(PDF)
1441:(PDF)
1430:(PDF)
1335:(PDF)
1324:(PDF)
1242:S2CID
1185:(PDF)
1156:(PDF)
951:(PDF)
824:(PDF)
811:(PDF)
633:S2CID
569:Notes
172:SHA-1
110:value
31:proof
4177:Salt
4141:CNSA
4008:IAPM
3962:VMAC
3957:UMAC
3942:PMAC
3937:CMAC
3933:OMAC
3928:NMAC
3923:HMAC
3918:GMAC
3887:HKDF
3756:SIMD
3706:Lane
3681:GOST
3666:ECOH
3553:List
3540:and
3487:List
3240:Kuna
3170:BTCC
3120:Abra
3039:Nano
3029:Luna
3009:Chia
2973:Diem
2950:TRON
2767:IOTA
2762:Firo
2736:Dash
2593:LBRY
2515:Web3
2490:Fork
2343:Nuri
1843:CNBC
1782:ISSN
1666:2020
1601:2014
1570:2020
1515:2022
1386:ISBN
1260:link
1232:ISBN
1172:ISBN
1096:ISBN
1053:help
933:2022
832:2020
716:ISBN
625:ISSN
361:IACR
121:work
98:work
59:spam
49:and
4013:OCB
4003:GCM
3998:EAX
3993:CWC
3983:CCM
3913:DAA
3791:VSH
3761:SM3
3731:MD6
3726:MD4
3721:MD2
3701:LSH
3671:FSB
3579:MD5
3281:FTX
3245:OKX
3175:BUX
3044:NEO
2978:Pax
2968:Dai
2920:Kin
2881:TON
2851:Nxt
2846:Kin
2727:X11
2158:P2P
1772:hdl
1762:doi
1712:doi
1378:doi
1224:doi
1164:doi
1086:doi
706:doi
663:doi
615:doi
45:by
24:PoW
4628::
3629:JH
1885:.
1845:.
1841:.
1815:.
1811:.
1788:.
1780:.
1770:.
1758:53
1756:.
1752:.
1726:.
1718:.
1708:22
1706:.
1702:.
1656:.
1587:.
1535:.
1531:.
1502:.
1498:.
1469:.
1465:.
1436:.
1432:.
1384:.
1376:.
1368:.
1358:;
1326:.
1304:.
1277:.
1256:}}
1252:{{
1240:.
1230:.
1222:.
1200:^
1180:.
1170:.
1158:.
1143:^
1126:.
1122:.
1110:^
1094:.
1076:;
1072:;
1061:^
1044::
1042:}}
1038:{{
1030:.
1015:^
986:.
959:^
923:.
919:.
913:.
887:.
883:.
858:.
854:.
843:^
834:.
813:.
799:^
782:.
778:.
753:.
749:.
724:.
714:.
700:.
692:;
677:^
657:.
645:^
631:.
623:.
611:19
609:.
605:.
439:.
426:.
4580::
4222:e
4215:t
4208:v
3935:/
3530:e
3523:t
3516:v
2433:e
2426:t
2419:v
1921:e
1914:t
1907:v
1856:.
1826:.
1796:.
1774::
1764::
1737:.
1714::
1668:.
1603:.
1572:.
1546:.
1517:.
1480:.
1450:.
1410:.
1394:.
1380::
1344:.
1308:.
1288:.
1262:)
1248:.
1226::
1194:.
1166::
1137:.
1104:.
1088::
1055:)
1051:(
1032:5
997:.
971:.
953:.
935:.
898:.
869:.
793:.
764:.
735:.
708::
671:.
665::
639:.
617::
225:.
81:(
22:(
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.