2299:
2071:
2638:
2892:(SAN) is a dedicated network that provides access to consolidated, block-level data storage. SANs are primarily used to make storage devices, such as disk arrays, tape libraries, and optical jukeboxes, accessible to servers so that the storage appears as locally attached devices to the operating system. A SAN typically has its own network of storage devices that are generally not accessible through the local area network by other devices. The cost and complexity of SANs dropped in the early 2000s to levels allowing wider adoption across both enterprise and small to medium-sized business environments.
824:
1860:
5188:"Many of the theoretical studies of the performance and design of the ARPA Network were developments of earlier work by Kleinrock ... Although these works concerned message switching networks, they were the basis for a lot of the ARPA network investigations ... The intention of the work of Kleinrock was to analyse the performance of store and forward networks, using as the primary performance measure the average message delay. ... Kleinrock extended the theoretical approaches of to the early ARPA network."
2291:
1627:
176:
8399:
1790:
1904:
1514:
8409:
3076:
52:
2205:
8419:
2806:(PAN) is a computer network used for communication among computers and different information technological devices close to one person. Some examples of devices that are used in a PAN are personal computers, printers, fax machines, telephones, PDAs, scanners, and video game consoles. A PAN may include wired and wireless devices. The reach of a PAN typically extends to 10 meters. A wired PAN is usually constructed with
1435:
2570:
6778:
2329:, often constructed per the OSI model, communications functions are divided up into protocol layers, where each layer leverages the services of the layer below it until the lowest layer controls the hardware that sends information across the media. The use of protocol layering is ubiquitous across the field of computer networking. An important example of a protocol stack is
5045:
Distributed
Communications" in the early 1960's. Also of note was work done by Donald Davies and others at the National Physical Laboratory in England in the mid-1960's. ... Another early major network development which affected development of the ARPANET was undertaken at the National Physical Laboratory in Middlesex, England, under the leadership of D. W. Davies.
1618:, the network topology is a ring, but the physical topology is often a star, because all neighboring connections can be routed via a central physical location. Physical layout is not completely irrelevant, however, as common ducting and equipment locations can represent single points of failure due to issues like fires, power failures and flooding.
2371:, also called TCP/IP, is the foundation of all modern networking. It offers connection-less and connection-oriented services over an inherently unreliable network traversed by datagram transmission using Internet protocol (IP). At its core, the protocol suite defines the addressing, identification, and routing specifications for
1488:. When one user is not sending packets, the link can be filled with packets from other users, and so the cost can be shared, with relatively little interference, provided the link is not overused. Often the route a packet needs to take through a network is not immediately available. In that case, the packet is
3819:. Netscape created a standard called secure socket layer (SSL). SSL requires a server with a certificate. When a client requests access to an SSL-secured server, the server sends a copy of the certificate to the client. The SSL client checks this certificate (all web browsers come with an exhaustive list of
2972:(WAN) is a computer network that covers a large geographic area such as a city, country, or spans even intercontinental distances. A WAN uses a communications channel that combines many types of media such as telephone lines, cables, and airwaves. A WAN often makes use of transmission facilities provided by
2872:(HAN) is a residential LAN used for communication between digital devices typically deployed in the home, usually a small number of personal computers and accessories, such as printers and mobile computing devices. An important function is the sharing of Internet access, often a broadband service through a
3028:(GAN) is a network used for supporting mobile users across an arbitrary number of wireless LANs, satellite coverage areas, etc. The key challenge in mobile communications is handing off communications from one local coverage area to the next. In IEEE Project 802, this involves a succession of terrestrial
5144:
Although there was considerable technical interchange between the NPL group and those who designed and implemented the ARPANET, the NPL Data
Network effort appears to have had little fundamental impact on the design of ARPANET. Such major aspects of the NPL Data Network design as the standard network
2128:
at a higher power level, or to the other side of obstruction so that the signal can cover longer distances without degradation. In most twisted-pair
Ethernet configurations, repeaters are required for cable that runs longer than 100 meters. With fiber optics, repeaters can be tens or even hundreds of
5529:
The authors wish to thank a number of colleagues for helpful comments during early discussions of international network protocols, especially R. Metcalfe, R. Scantlebury, D. Walden, and H. Zimmerman; D. Davies and L. Pouzin who constructively commented on the fragmentation and accounting issues; and
3066:
is a network that is under the administrative control of a single organization but supports a limited connection to a specific external network. For example, an organization may provide access to some aspects of its intranet to share data with its business partners or customers. These other entities
3053:
is a set of networks that are under the control of a single administrative entity. An intranet typically uses the
Internet Protocol and IP-based tools such as web browsers and file transfer applications. The administrative entity limits the use of the intranet to its authorized users. Most commonly,
1421:
Computer networks enhance how users communicate with each other by using various electronic methods like email, instant messaging, online chat, voice and video calls, and video conferencing. Networks also enable the sharing of computing resources. For example, a user can print a document on a shared
5298:
The hierarchical approach is further motivated by theoretical results (e.g., ) which show that, by optimally placing separators, i.e., elements that connect levels in the hierarchy, tremendous gain can be achieved in terms of both routing table size and update message churn. ... KLEINROCK, L., AND
4690:
As Kahn recalls: ... Paul Baran's contributions ... I also think Paul was motivated almost entirely by voice considerations. If you look at what he wrote, he was talking about switches that were low-cost electronics. The idea of putting powerful computers in these locations hadn't quite occurred to
2185:
based on the destination MAC address in each frame. They learn the association of physical ports to MAC addresses by examining the source addresses of received frames and only forward the frame when necessary. If an unknown destination MAC is targeted, the device broadcasts the request to all ports
1638:
is a virtual network that is built on top of another network. Nodes in the overlay network are connected by virtual or logical links. Each link corresponds to a path, perhaps through many physical links, in the underlying network. The topology of the overlay network may (and often does) differ from
1521:
The physical or geographic locations of network nodes and links generally have relatively little effect on a network, but the topology of interconnections of a network can significantly affect its throughput and reliability. With many technologies, such as bus or star networks, a single failure can
5216:
In mathematical modelling use is made of the theories of queueing processes and of flows in networks, describing the performance of the network in a set of equations. ... The analytic method has been used with success by
Kleinrock and others, but only if important simplifying assumptions are made.
3512:
priority schemes allowing selected traffic to bypass congestion. Priority schemes do not solve network congestion by themselves, but they help to alleviate the effects of congestion for critical services. A third method to avoid network congestion is the explicit allocation of network resources to
5044:
Aside from the technical problems of interconnecting computers with communications circuits, the notion of computer networks had been considered in a number of places from a theoretical point of view. Of particular note was work done by Paul Baran and others at the Rand
Corporation in a study "On
3463:
that use aggressive retransmissions to compensate for packet loss tend to keep systems in a state of network congestion even after the initial load is reduced to a level that would not normally induce network congestion. Thus, networks using these protocols can exhibit two stable states under the
3012:
in which some of the links between nodes are carried by open connections or virtual circuits in some larger network (e.g., the
Internet) instead of by physical wires. The data link layer protocols of the virtual network are said to be tunneled through the larger network. One common application is
2793:
has key components implemented at the nanoscale, including message carriers, and leverages physical principles that differ from macroscale communication mechanisms. Nanoscale communication extends communication to very small sensors and actuators such as those found in biological systems and also
3605:
is the monitoring of data being transferred over computer networks such as the
Internet. The monitoring is often done surreptitiously and may be done by or at the behest of governments, by corporations, criminal organizations, or individuals. It may or may not be legal and may or may not require
4667:
Paul Baran ... focused on the routing procedures and on the survivability of distributed communication systems in a hostile environment, but did not concentrate on the need for resource sharing in its form as we now understand it; indeed, the concept of a software switch was not present in his
2277:
A firewall is a network device or software for controlling network security and access rules. Firewalls are inserted in connections between secure internal networks and potentially insecure external networks such as the
Internet. Firewalls are typically configured to reject access requests from
2165:
Network bridges and network switches are distinct from a hub in that they only forward frames to the ports involved in the communication whereas a hub forwards to all ports. Bridges only have two ports but a switch can be thought of as a multi-port bridge. Switches normally have numerous ports,
1411:
In 1995, the transmission speed capacity for
Ethernet increased from 10 Mbit/s to 100 Mbit/s. By 1998, Ethernet supported transmission speeds of 1 Gbit/s. Subsequently, higher speeds of up to 400 Gbit/s were added (as of 2018). The scaling of Ethernet has been a contributing
2614:
are structured and that similar addresses imply proximity within the network. Structured addresses allow a single routing table entry to represent the route to a group of devices. In large networks, the structured addressing used by routers outperforms unstructured addressing used by bridging.
4826:
the first occurrence in print of the term protocol in a data communications context ... the next hardware tasks were the detailed design of the interface between the terminal devices and the switching computer, and the arrangements to secure reliable transmission of packets of data over the
3013:
secure communications through the public Internet, but a VPN need not have explicit security features, such as authentication or content encryption. VPNs, for example, can be used to separate the traffic of different user communities over an underlying network with strong security features.
2923:
is part of a computer network infrastructure that provides a path for the exchange of information between different LANs or subnetworks. A backbone can tie together diverse networks within the same building, across different buildings, or over a wide area. When designing a network backbone,
1882:, optical fibers can simultaneously carry multiple streams of data on different wavelengths of light, which greatly increases the rate that data can be sent to up to trillions of bits per second. Optic fibers can be used for long runs of cable carrying very high data rates, and are used for
3593:
access, misuse, modification, or denial of the computer network and its network-accessible resources. Network security is used on a variety of computer networks, both public and private, to secure daily transactions and communications among businesses, government agencies, and individuals.
1927: – Terrestrial microwave communication uses Earth-based transmitters and receivers resembling satellite dishes. Terrestrial microwaves are in the low gigahertz range, which limits all communications to line-of-sight. Relay stations are spaced approximately 40 miles (64 km) apart.
1138:
proposed to the Central Committee of the Communist Party of the Soviet Union a detailed plan for the re-organization of the control of the Soviet armed forces and of the Soviet economy on the basis of a network of computing centers. Kitov's proposal was rejected, as later was the 1962
2390:
is a family of IEEE standards dealing with local area networks and metropolitan area networks. The complete IEEE 802 protocol suite provides a diverse set of networking capabilities. The protocols have a flat addressing scheme. They operate mostly at layers 1 and 2 of the OSI model.
1894:(MMF). Single-mode fiber has the advantage of being able to sustain a coherent signal for dozens or even a hundred kilometers. Multimode fiber is cheaper to terminate but is limited to a few hundred or even only a few dozens of meters, depending on the data rate and cable grade.
3040:
Networks are typically managed by the organizations that own them. Private enterprise networks may use a combination of intranets and extranets. They may also provide network access to the Internet, which has no single owner and permits virtually unlimited global connectivity.
5145:
interface, the routing algorithm, and the software structure of the switching node were largely ignored by the ARPANET designers. There is no doubt, however, that in many less fundamental ways the NPL Data Network had and effect on the design and evolution of the ARPANET.
1935: – Satellites also communicate via microwave. The satellites are stationed in space, typically in geosynchronous orbit 35,400 km (22,000 mi) above the equator. These Earth-orbiting systems are capable of receiving and relaying voice, data, and TV signals.
2834:(LAN) is a network that connects computers and devices in a limited geographical area such as a home, school, office building, or closely positioned group of buildings. Wired LANs are most commonly based on Ethernet technology. Other networking technologies such as
3874:
Unofficially, the Internet is the set of users, enterprises, and content providers that are interconnected by Internet Service Providers (ISP). From an engineering viewpoint, the Internet is the set of subnets, and aggregates of subnets, that share the registered
3329:
to another. Delay may differ slightly, depending on the location of the specific pair of communicating endpoints. Engineers usually report both the maximum and average delay, and they divide the delay into several components, the sum of which is the total delay:
2935:
For example, a large company might implement a backbone network to connect departments that are located around the world. The equipment that ties together the departmental networks constitutes the network backbone. Another example of a backbone network is the
6047:"IEEE Standard for Information Technology--Telecommunications and Information Exchange between Systems - Local and Metropolitan Area Networks--Specific Requirements - Part 11: Wireless LAN Medium Access Control (MAC) and Physical Layer (PHY) Specifications"
3428:
occurs when a link or node is subjected to a greater data load than it is rated for, resulting in a deterioration of its quality of service. When networks are congested and queues become too full, packets have to be discarded, and participants must rely on
3098:
is the largest example of internetwork. It is a global system of interconnected governmental, academic, corporate, public, and private computer networks. It is based on the networking technologies of the Internet protocol suite. It is the successor of the
2189:
Bridges and switches divide the network's collision domain but maintain a single broadcast domain. Network segmentation through bridging and switching helps break down a large, congested network into an aggregation of smaller, more efficient networks.
2780:
Networks may be characterized by many properties or features, such as physical capacity, organizational purpose, user authorization, access rights, and others. Another distinct classification method is that of the physical extent or geographic scale.
4155:
Shortly after the first paper on time-shared computers by C. Strachey at the June 1959 UNESCO Information Processing conference, H. M. Teager and J. McCarthy at MIT delivered an unpublished paper "Time-shared Program Testing" at the August 1959 ACM
1191:
between computers over a network. Baran's work addressed adaptive routing of message blocks across a distributed network, but did not include routers with software switches, nor the idea that users, rather than the network itself, would provide the
3866:
is a community of interest under private administration usually by an enterprise, and is only accessible by authorized users (e.g. employees). Intranets do not have to be connected to the Internet, but generally have a limited connection. An
1707:. The overlay network has no control over how packets are routed in the underlying network between two overlay nodes, but it can control, for example, the sequence of overlay nodes that a message traverses before it reaches its destination.
5113:
Significant aspects of the network's internal operation, such as routing, flow control, software design, and network control were developed by a BBN team consisting of Frank Heart, Robert Kahn, Severo Omstein, William Crowther, and David
2147:. In addition to reconditioning and distributing network signals, a repeater hub assists with collision detection and fault isolation for the network. Hubs and repeaters in LANs have been largely obsoleted by modern network switches.
5621:
Council, National Research; Sciences, Division on Engineering and Physical; Board, Computer Science and Telecommunications; Applications, Commission on Physical Sciences, Mathematics, and; Committee, NII 2000 Steering (1998-02-05).
2465:
protocols that transfer multiple digital bit streams over optical fiber using lasers. They were originally designed to transport circuit mode communications from a variety of different sources, primarily to support circuit-switched
2106:. The three most significant octets are reserved to identify NIC manufacturers. These manufacturers, using only their assigned prefixes, uniquely assign the three least-significant octets of every Ethernet interface they produce.
1227:
were connected using 50 kbit/s circuits between the University of California at Los Angeles, the Stanford Research Institute, the University of California at Santa Barbara, and the University of Utah. Designed principally by
2220:
A router is an internetworking device that forwards packets between networks by processing the addressing or routing information included in the packet. The routing information is often processed in conjunction with the
3151:
is an overlay network, typically running on the Internet, that is only accessible through specialized software. It is an anonymizing network where connections are made only between trusted peers — sometimes called
3126:
Participants on the Internet use a diverse array of methods of several hundred documented, and often standardized, protocols compatible with the Internet protocol suite and the IP addressing system administered by the
4691:
him as being cost effective. So the idea of computer switches was missing. The whole notion of protocols didn't exist at that time. And the idea of computer-to-computer communications was really a secondary concern.
3416:
are often used to model queuing performance in a circuit-switched network. The network planner uses these diagrams to analyze how the network performs in each state, ensuring that the network is optimally designed.
2090:
and has the ability to process low-level network information. For example, the NIC may have a connector for plugging in a cable, or an aerial for wireless transmission and reception, and the associated circuitry.
1522:
cause the network to fail entirely. In general, the more interconnections there are, the more robust the network is; but the more expensive it is to install. Therefore, most network diagrams are arranged by their
3850:
Network administrators can see networks from both physical and logical perspectives. The physical perspective involves geographic locations, physical cabling, and the network elements (e.g., routers, bridges and
2573:
Routing calculates good paths through a network for information to take. For example, from node 1 to node 6 the best routes are likely to be 1-8-7-6, 1-8-10-6 or 1-9-10-6, as these are the shortest routes.
2302:
Message flows between two devices (A-B) at the four layers of the TCP/IP model in the presence of a router (R). Red flows are effective communication paths, black paths are across the actual network links.
986:. Hostnames serve as memorable labels for the nodes and are rarely changed after initial assignment. Network addresses serve for locating and identifying the nodes by communication protocols such as the
1957: – Wireless LANs use a high-frequency radio technology similar to digital cellular. Wireless LANs use spread spectrum technology to enable communication between multiple devices in a limited area.
1809:
is widely used for cable television systems, office buildings, and other work-sites for local area networks. Transmission speed ranges from 200 million bits per second to more than 500 million bits per
1220:, pioneered the implementation of the concept in 1968-69 using 768 kbit/s links. Both Baran's and Davies' inventions were seminal contributions that influenced the development of computer networks.
2422:
protocol, which forms the basis for the authentication mechanisms used in VLANs (but it is also found in WLANs) – it is what the home user sees when the user has to enter a "wireless access key".
1851:. The transmission speed ranges from 2 Mbit/s to 10 Gbit/s. Twisted pair cabling comes in two forms: unshielded twisted pair (UTP) and shielded twisted-pair (STP). Each form comes in several
1457:
Packets consist of two types of data: control information and user data (payload). The control information provides data the network needs to deliver the user data, for example, source and destination
1068:, since it relies on the theoretical and practical application of the related disciplines. Computer networking was influenced by a wide array of technological developments and historical milestones.
6782:
2498:. ATM has similarities with both circuit and packet switched networking. This makes it a good choice for a network that must handle both traditional high-throughput data traffic, and real-time,
5327:
The Spanish, dark horses, were the first people to have a public network. They'd got a bank network which they craftily turned into a public network overnight, and beat everybody to the post.
3859:, map onto one or more transmission media. For example, a common practice in a campus of buildings is to make a set of LAN cables in each building appear to be a common subnet, using VLANs.
3485:
techniques where endpoints typically slow down or sometimes even stop transmission entirely when the network is congested to try to avoid congestive collapse. Specific techniques include:
3402:. The number of rejected calls is a measure of how well the network is performing under heavy traffic loads. Other types of performance measures can include the level of noise and echo.
1843:
and other standards. It typically consists of 4 pairs of copper cabling that can be utilized for both voice and data transmission. The use of two wires twisted together helps to reduce
2996:
is a network that a single organization builds to interconnect its office locations (e.g., production sites, head offices, remote offices, shops) so they can share computer resources.
2580:
is the process of selecting network paths to carry network traffic. Routing is performed for many kinds of networks, including circuit switching networks and packet switched networks.
5247:
Hierarchical addressing systems for network routing have been proposed by Fultz and, in greater detail, by McQuillan. A recent very full analysis may be found in Kleinrock and Kamoun.
3409:(ATM) network, performance can be measured by line rate, quality of service (QoS), data throughput, connect time, stability, technology, modulation technique, and modem enhancements.
6679:
3091:
is the connection of multiple different types of computer networks to form a single computer network using higher-layer network protocols and connecting them together using routers.
1584:: each node is connected to its left and right neighbor node, such that all nodes are connected and that each node can reach each other node by traversing nodes left- or rightwards.
6862:
2595:
can also forward packets and perform routing, though because they lack specialized hardware, may offer limited performance. The routing process directs forwarding on the basis of
1650:
Overlay networks have been used since the early days of networking, back when computers were connected via telephone lines using modems, even before data networks were developed.
3839:, which usually means they are in the same geographic location and are on the same LAN, whereas a network administrator is responsible for keeping that network up and running. A
3412:
There are many ways to measure the performance of a network, as each network is different in nature and design. Performance can also be modeled instead of measured. For example,
3910:
mechanism. Intranets and extranets can be securely superimposed onto the Internet, without any access by general Internet users and administrators, using secure VPN technology.
2911:
For example, a university campus network is likely to link a variety of campus buildings to connect academic colleges or departments, the library, and student residence halls.
1422:
printer or use shared storage devices. Additionally, networks allow for the sharing of files and information, giving authorized users access to data stored on other computers.
4234:
3843:
has less of a connection of being in a local area and should be thought of as a set of arbitrarily located users who share a set of servers, and possibly also communicate via
3696:
data so only the intended recipient can decrypt it, with no dependency on third parties. End-to-end encryption prevents intermediaries, such as Internet service providers or
4849:
2136:
that affects network performance and may affect proper function. As a result, many network architectures limit the number of repeaters used in a network, e.g., the Ethernet
4910:
2904:(CAN) is made up of an interconnection of LANs within a limited geographical area. The networking equipment (switches, routers) and transmission media (optical fiber,
2239:
Modems (modulator-demodulator) are used to connect network nodes via wire not originally designed for digital network traffic, or for wireless. To do this one or more
1761:(LAN) technology are collectively known as Ethernet. The media and protocol standards that enable communication between networked devices over Ethernet are defined by
1657:. Even today, each Internet node can communicate with virtually any other through an underlying mesh of sub-networks of wildly different topologies and technologies.
3609:
Computer and network surveillance programs are widespread today, and almost all Internet traffic is or could potentially be monitored for clues to illegal activity.
5039:
2278:
unrecognized sources while allowing actions from recognized ones. The vital role firewalls play in network security grows in parallel with the constant increase in
3811:
The introduction and rapid growth of e-commerce on the World Wide Web in the mid-1990s made it obvious that some form of authentication and encryption was needed.
2591:
through intermediate nodes. Intermediate nodes are typically network hardware devices such as routers, bridges, gateways, firewalls, or switches. General-purpose
6198:
2379:, the next generation of the protocol with a much enlarged addressing capability. The Internet protocol suite is the defining set of protocols for the Internet.
1703:
in the network. On the other hand, an overlay network can be incrementally deployed on end-hosts running the overlay protocol software, without cooperation from
1116:
4967:
6177:
3494:
3175:
is anonymous (that is, IP addresses are not publicly shared), and therefore users can communicate with little fear of governmental or corporate interference.
2225:. A router uses its routing table to determine where to forward packets and does not require broadcasting packets which is inefficient for very big networks.
1244:
carried out mathematical work to model the performance of packet-switched networks, which underpinned the development of the ARPANET. His theoretical work on
3054:
an intranet is the internal LAN of an organization. A large intranet typically has at least one web server to provide users with organizational information.
6721:
4934:
4383:
Essentially all the work was defined by 1961, and fleshed out and put into formal written form in 1962. The idea of hot potato routing dates from late 1960.
3862:
Users and administrators are aware, to varying extents, of a network's trust and scope characteristics. Again using TCP/IP architectural terminology, an
1370:
published their paper "Ethernet: Distributed Packet Switching for Local Computer Networks" and collaborated on several patents received in 1977 and 1978.
6654:
4751:
Davies's invention of packet switching and design of computer communication networks ... were a cornerstone of the development which led to the Internet
3067:
are not necessarily trusted from a security standpoint. The network connection to an extranet is often, but not always, implemented via WAN technology.
1943:
use several radio communications technologies. The systems divide the region covered into multiple geographic areas. Each area is served by a low-power
1499:(MTU). A longer message may be fragmented before it is transferred and once the packets arrive, they are reassembled to construct the original message.
692:
2932:
are critical factors to take into account. Normally, the backbone network's capacity is greater than that of the individual networks connected to it.
3633:
2099:
1610:: nodes are arranged hierarchically. This is the natural topology for a larger Ethernet network with multiple switches and without redundant meshing.
5926:
6961:
5660:
4521:
5718:
1270:
was the first to make the hosts responsible for the reliable delivery of data, rather than this being a centralized service of the network itself.
6495:
5664:
5217:... It is heartening in Kleinrock's work to see the good correspondence achieved between the results of analytic methods and those of simulation.
1672:, which maps keys to nodes in the network. In this case, the underlying network is an IP network, and the overlay network is a table (actually a
3016:
VPN may have best-effort performance or may have a defined service level agreement (SLA) between the VPN customer and the VPN service provider.
2615:
Structured IP addresses are used on the Internet. Unstructured MAC addresses are used for bridging on Ethernet and similar local area networks.
4021:
4056:
3750:-based communications systems do not include end-to-end encryption. These systems can only guarantee the protection of communications between
4140:
1217:
6687:
2550:
1598:: each node is connected to an arbitrary number of neighbors in such a way that there is at least one traversal from any node to any other.
1147:
4297:
2132:
Repeaters work on the physical layer of the OSI model but still require a small amount of time to regenerate the signal. This can cause a
6908:
6469:
5639:
5158:
4465:
1878:. Some advantages of optical fibers over metal wires are very low transmission loss and immunity to electrical interference. Using dense
6625:
4197:
7435:
5058:
3871:
is an extension of an intranet that allows secure communications to users outside of the intranet (e.g. business partners, customers).
2976:, such as telephone companies. WAN technologies generally function at the lower three layers of the OSI model: the physical layer, the
2546:
2599:, which maintain a record of the routes to various network destinations. Most routing algorithms use only one network path at a time.
3104:
2856:
to provide connectivity. Current Ethernet or other IEEE 802.3 LAN technologies operate at data transfer rates up to and in excess of
1653:
The most striking example of an overlay network is the Internet itself. The Internet itself was initially built as an overlay on the
799:
6094:
5373:
5230:
3835:
Users and network administrators typically have different views of their networks. Users can share printers and some servers from a
4840:
3903:
3272:, i.e., the average rate of successful data transfer through a communication path. The throughput is affected by processes such as
5129:
The Froehlich/Kent Encyclopedia of Telecommunications: Volume 1 - Access Charges in the U.S.A. to Basics of Digital Communications
4577:
2470:. However, due to its protocol neutrality and transport-oriented features, SONET/SDH also was the obvious choice for transporting
1404:
In 1980, Ethernet was upgraded from the original 2.94 Mbit/s protocol to the 10 Mbit/s protocol, which was developed by
4176:
3777:
The end-to-end encryption paradigm does not directly address risks at the endpoints of the communication themselves, such as the
2767:
2522:
6556:
5199:
4994:
In nearly all respects, Davies' original proposal, developed in late 1965, was similar to the actual networks being built today.
8152:
8124:
4894:
4681:
4375:
3939:
2310:
is a set of rules for exchanging information over a network. Communication protocols have various characteristics. They may be
116:
17:
6787:
829:
8177:
7237:
7208:
6594:
6452:
6152:
6127:
6066:
6019:
5782:
5633:
5283:
5240:
5209:
5015:
4744:
4714:
4272:
4134:
4101:
4035:
3906:
communications. When money or sensitive information is exchanged, the communications are apt to be protected by some form of
2542:
2352:
88:
6527:
5868:
3692:
paradigm of uninterrupted protection of data traveling between two communicating parties. It involves the originating party
2056:. Any particular piece of equipment will frequently contain multiple building blocks and so may perform multiple functions.
8028:
5475:
2956:(MAN) is a large computer network that interconnects users with computer resources in a geographic region of the size of a
6817:
Kurose James F and Keith W. Ross: Computer Networking: A Top-Down Approach Featuring the Internet, Pearson Education 2005.
6349:
6072:
6025:
4436:
Almost immediately after the 1965 meeting, Davies conceived of the details of a store-and-forward packet switching system.
3797:, which relates to things such as the identities of the endpoints and the times and quantities of messages that are sent.
3135:. Service providers and large enterprises exchange information about the reachability of their address spaces through the
2841:
also provide a way to create a wired LAN using existing wiring, such as coaxial cables, telephone lines, and power lines.
8182:
7454:
5956:
5778:
5010:. Johns Hopkins studies in the history of technology New series. Baltimore: Johns Hopkins Univ. Press. pp. 153–196.
4552:
4087:
3234:
3128:
3108:
2558:
1557:
5178:
3827:
for use in the session. The session is now in a very secure encrypted tunnel between the SSL server and the SSL client.
95:
7687:
6004:
IEEE STD 802.1X-2020 (Revision of IEEE STD 802.1X-2010 Incorporating IEEE STD 802.1Xbx-2014 and IEEE STD 802.1Xck-2018)
4327:
4070:
1286:
1108:
828:
682:
411:
6210:
6169:
5299:
KAMOUN, F. Hierarchical routing for large networks: Performance evaluation and optimization. Computer Networks (1977).
2908:
cabling, etc.) are almost entirely owned by the campus tenant or owner (an enterprise, university, government, etc.).
8334:
8162:
7692:
5843:
5694:
5343:
5186:(PhD thesis). Department of Electrical Engineering, Imperial College of Science and Technology, University of London.
4978:
4777:
4459:
2311:
2028:
Apart from any physical transmission media, networks are built from additional basic system building blocks, such as
1193:
1073:
135:
69:
2940:, which is a massive, global system of fiber-optic cable and optical networking that carry the bulk of data between
1718:). Academic research includes end system multicast, resilient routing and quality of service studies, among others.
1614:
The physical layout of the nodes in a network may not necessarily reflect the network topology. As an example, with
8422:
7516:
7012:
6956:
1969:
1879:
1589:
1336:
1229:
756:
339:
102:
7810:
6931:
6901:
6793:
6713:
5549:
4942:
3836:
1119:
in Paris that year. McCarthy was instrumental in the creation of three of the earliest time-sharing systems (the
1111:
initiated the first project to implement time-sharing of user programs at MIT. Strachey passed the concept on to
652:
4797:
8101:
8063:
7720:
7428:
7124:
7022:
5900:
5497:
5137:
3656:
3652:
3543:
3430:
3187:
2925:
2510:
2482:
Asynchronous Transfer Mode (ATM) is a switching technique for telecommunication networks. It uses asynchronous
2458:
2430:
Ethernet is a family of technologies used in wired LANs. It is described by a set of standards together called
2125:
1917:
Network connections can be established wirelessly using radio or other electromagnetic means of communication.
1883:
1643:
networks are overlay networks. They are organized as nodes of a virtual system of links that run on top of the
1158:
1120:
846:
830:
642:
73:
6647:
3513:
specific flows. One example of this is the use of Contention-Free Transmission Opportunities (CFTXOPs) in the
2098:—usually stored in the controller's permanent memory. To avoid address conflicts between network devices, the
1750:, the software to handle the media is defined at layers 1 and 2 — the physical layer and the data link layer.
637:
8243:
8220:
7950:
7940:
7402:
6951:
6936:
5038:(Report). Bolt, Beranek & Newman Inc. 1 April 1981. pp. 13, 53 of 183 (III-11 on the printed copy).
3840:
3293:
2334:
1348:
1128:
792:
751:
268:
84:
8324:
7912:
7820:
7725:
7501:
7486:
6997:
6982:
6941:
3887:
names of servers are translated to IP addresses, transparently to users, via the directory function of the
3697:
3297:
2526:
2315:
2065:
2029:
907:
597:
441:
388:
203:
6239:
632:
8412:
8147:
7645:
7163:
7110:
6814:
Wendell Odom, Rus Healy, Denise Donohue. (2010) CCIE Routing and Switching. Indianapolis, IN: Cisco Press
6509:
5934:
4767:
3985:
3778:
3625:
2760:
2121:
1658:
1536:: all nodes are connected to a common medium along this medium. This was the layout used in the original
1233:
6284:
4490:
3244:
that defines the format and sequencing of messages between clients and servers of that network service.
8443:
8384:
8033:
7178:
7017:
6894:
5740:
5710:
5081:
4954:
Historians credit seminal insights to Welsh scientist Donald W. Davies and American engineer Paul Baran
4396:
3823:
preloaded), and if the certificate checks out, the server is authenticated and the client negotiates a
3663:
society, with limited political and personal freedoms. Fears such as this have led to lawsuits such as
3406:
3318:
3161:
3132:
3079:
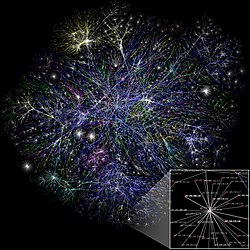
Partial map of the Internet based on 2005 data. Each line is drawn between two nodes, representing two
2993:
2719:
2483:
2471:
2255:
sent over a standard voice telephone line. Modems are still commonly used for telephone lines, using a
2075:
1096:
to be transmitted over regular unconditioned telephone lines at a speed of 110 bits per second (bit/s).
761:
667:
662:
627:
426:
324:
263:
3855:) that interconnect via the transmission media. Logical networks, called, in the TCP/IP architecture,
8402:
8329:
8304:
8167:
7815:
7421:
7213:
7032:
6992:
6987:
6946:
5802:
4734:
3852:
3740:
3648:
3172:
2953:
2714:
1974:
1887:
1848:
1704:
1496:
1282:
944:
349:
2102:(IEEE) maintains and administers MAC address uniqueness. The size of an Ethernet MAC address is six
1665:
are the means that allow mapping of a fully connected IP overlay network to its underlying network.
8253:
8086:
7672:
7541:
7256:
7143:
7007:
4922:
This was the first digital local network in the world to use packet switching and high-speed links.
3925:
3806:
3724:
3571:
2652:
2538:
2182:
1931:
1891:
1828:
1774:
1495:
The physical link technologies of packet networks typically limit the size of packets to a certain
1237:
827:
785:
687:
647:
154:
40:
33:
4121:
3570:
on devices connected to the network, or to prevent these devices from accessing the network via a
2848:(WAN) using a router. The defining characteristics of a LAN, in contrast to a WAN, include higher
1157:
In 1963, J. C. R. Licklider sent a memorandum to office colleagues discussing the concept of the "
545:
8314:
8248:
8139:
7955:
7615:
7002:
6709:
3990:
3949:
3907:
3880:
3786:
3482:
3434:
3206:
3136:
3005:
2877:
2741:
2368:
2256:
1981:
1844:
1601:
1566:: all nodes are connected to a special central node. This is the typical layout found in a small
1451:
1232:, the network's routing, flow control, software design and network control were developed by the
1124:
1010:
1002:
768:
587:
354:
288:
243:
62:
6120:
The evolution of mobile communications in the US and Europe: Regulation, technology, and markets
5404:
Kirstein, P.T. (1999). "Early experiences with the Arpanet and Internet in the United Kingdom".
2637:
8379:
8210:
8091:
7858:
7848:
7843:
7390:
7329:
7218:
7198:
7147:
7105:
5374:"Designed for Change: End-to-End Arguments, Internet Innovation, and the Net Neutrality Debate"
4289:
3970:
3959:
3700:, from reading or tampering with communications. End-to-end encryption generally protects both
3689:
3326:
2819:
2753:
2419:
2403:
2307:
1987:
1679:
Overlay networks have also been proposed as a way to improve Internet routing, such as through
1669:
1426:
leverages resources from multiple computers across a network to perform tasks collaboratively.
1201:
933:
672:
657:
572:
6442:
5623:
5127:
4704:
4449:
4205:
4117:
3677:
has hacked into government websites in protest of what it considers "draconian surveillance".
2450:
protocol family for home users today. IEEE 802.11 shares many properties with wired Ethernet.
2251:
that can be tailored to give the required properties for transmission. Early modems modulated
109:
8349:
8319:
8309:
8205:
8119:
7995:
7935:
7902:
7892:
7775:
7740:
7730:
7667:
7536:
7511:
7506:
7471:
7173:
7139:
7041:
6977:
6621:
6577:
Simmonds, A; Sandilands, P; van Ekert, L (2004). "An Ontology for Network Security Attacks".
4264:
3685:
3586:
3257:
2873:
2803:
2794:
tends to operate in environments that would be too harsh for other communication techniques.
2731:
2699:
2662:
2607:
2395:
2078:
network interface in the form of an accessory card. A lot of network interfaces are built-in.
2011:
2007:
1575:
1481:
1423:
1398:
In 1977, the first long-distance fiber network was deployed by GTE in Long Beach, California.
1388:
1325:
998:
773:
592:
562:
451:
406:
5066:
4721:
Baran had put more emphasis on digital voice communications than on computer communications.
4255:
Gillies, James M.; Gillies, James; Gillies, James and Cailliau Robert; Cailliau, R. (2000).
2446:
standards, also widely known as WLAN or WiFi, is probably the most well-known member of the
2070:
8109:
8081:
8053:
8048:
7877:
7853:
7805:
7788:
7783:
7765:
7755:
7750:
7712:
7662:
7657:
7574:
7520:
7370:
7344:
6762:
6478:
6424:
6390:
6000:"IEEE Standard for Local and Metropolitan Area Networks--Port-Based Network Access Control"
5768:
5563:
4536:
Both Paul Baran and Donald Davies in their original papers anticipated the use of T1 trunks
3899:
3895:
3824:
3812:
3602:
3478:
3446:
3289:
3281:
3277:
3241:
2889:
2857:
2677:
2667:
2294:
The TCP/IP model and its relation to common protocols used at different layers of the model
2272:
2053:
2014:
but does not prevent sending large amounts of information (they can have high throughput).
1991:
1980:
Extending the Internet to interplanetary dimensions via radio waves and optical means, the
1405:
1245:
1205:
1100:
1061:
1017:
540:
421:
5745:
Entrepreneurial Capitalism and Innovation: A History of Computer Communications, 1968-1988
5380:
4451:
The Innovators: How a Group of Hackers, Geniuses, and Geeks Created the Digital Revolution
3636:, governments now possess an unprecedented ability to monitor the activities of citizens.
8:
8374:
8299:
8215:
8200:
7965:
7745:
7702:
7697:
7594:
7584:
7556:
7339:
7291:
7168:
6830:
Network Communication Architecture and Protocols: OSI Network Architecture 7 Layers Model
6101:
5977:
5259:
Feldmann, Anja; Cittadini, Luca; Mühlbauer, Wolfgang; Bush, Randy; Maennel, Olaf (2009).
4686:
Entrepreneurial Capitalism and Innovation: A History of Computer Communications 1968–1988
3716:
3486:
3466:
3025:
2901:
1734:
1714:
manages an overlay network that provides reliable, efficient content delivery (a kind of
1711:
1474:
1470:
1373:
1256:
1089:
1041:
994:
971:
577:
446:
436:
431:
283:
228:
218:
5059:"Internet Began 35 Years Ago at UCLA with First Message Ever Sent Between Two Computers"
8339:
8238:
8114:
8071:
7980:
7922:
7907:
7897:
7682:
7481:
7276:
7183:
6600:
6489:
5683:
5654:
5603:
5456:
5421:
5289:
5104:
4842:
A Digital Communication Network for Computers Giving Rapid Response at remote Terminals
4817:
4573:
4513:
4427:
3980:
3888:
3816:
3782:
3755:
3751:
3747:
3665:
3547:
3539:
3509:
3474:
3449:
of new connections. A consequence of these latter two is that incremental increases in
3425:
3368:
3359:
A certain minimum level of delay is experienced by signals due to the time it takes to
3346:
3210:
3120:
3112:
2929:
2849:
2831:
2672:
2199:
2178:
2049:
1824:
1758:
1700:
1680:
1466:
1213:
1197:
1188:
1151:
1112:
1065:
967:
416:
369:
344:
233:
223:
6319:
5270:. ReArch '09. New York, NY, USA: Association for Computing Machinery. pp. 43–48.
4839:
Davies, Donald; Bartlett, Keith; Scantlebury, Roger; Wilkinson, Peter (October 1967).
4168:
3879:
space and exchange information about the reachability of those IP addresses using the
8359:
8289:
8268:
8230:
8038:
8005:
7985:
7677:
7589:
7463:
7385:
7334:
7266:
7223:
7064:
6833:
6820:
6590:
6552:
6448:
6148:
6123:
6062:
6015:
5876:, Third Annual International Symposium on Advanced Radio Technologies, archived from
5849:
5839:
5690:
5629:
5520:
5339:
5279:
5236:
5205:
5133:
5011:
4902:
4773:
4740:
4736:
Turing's Legacy: A History of Computing at the National Physical Laboratory 1945-1995
4710:
4658:
4619:
4455:
4419:
4367:
4344:
4323:
4268:
4257:
4130:
4097:
4066:
4031:
4000:
3771:
3758:, not between the communicating parties themselves. Examples of non-E2EE systems are
3728:
3674:
3660:
3629:
3360:
3352:
3273:
2969:
2957:
2941:
2937:
2869:
2845:
2790:
2726:
2657:
2600:
2588:
2467:
2133:
2103:
2083:
2023:
1875:
1793:
1727:
1673:
1654:
1567:
1485:
1484:
of the transmission medium can be better shared among users than if the network were
1384:. This underlying infrastructure was used for expanding TCP/IP networks in the 1980s.
1274:
1241:
987:
963:
929:
876:
856:
713:
379:
329:
238:
213:
6867:
5460:
5108:
5008:
Transforming computer technology: information processing for the Pentagon, 1962-1986
4517:
4431:
1161:", a computer network intended to allow general communications among computer users.
8192:
8076:
8043:
7838:
7760:
7649:
7635:
7630:
7579:
7491:
7444:
6917:
6797:
6752:
6604:
6582:
6414:
6380:
6315:
6054:
6007:
5593:
5553:
5512:
5448:
5425:
5413:
5344:"RCP, the Experimental Packet-Switched Data Transmission Service of the French PTT"
5293:
5271:
5096:
4875:
4821:
4809:
4650:
4611:
4505:
4411:
4359:
3820:
3794:
3582:
3524:
3508:
Another method to avoid the negative effects of network congestion is implementing
3460:
3399:
3334:
3157:
2920:
2905:
2709:
2584:
1995:
1939:
1912:
1739:
1523:
1508:
1352:
1184:
1169:
1165:
1057:
956:
900:
815:
472:
461:
359:
303:
5772:
5607:
4864:"all users of the network will provide themselves with some kind of error control"
2513:, which is the connection between an Internet service provider and the home user.
2506:
must be established between two endpoints before the actual data exchange begins.
2322:
or packet switching, and they may use hierarchical addressing or flat addressing.
1961:
defines a common flavor of open-standards wireless radio-wave technology known as
1863:
2007 map showing submarine optical fiber telecommunication cables around the world
8263:
8157:
8129:
8023:
7975:
7960:
7945:
7800:
7795:
7735:
7625:
7599:
7551:
7496:
7309:
7271:
7242:
6857:
6837:
6586:
6531:
6058:
6011:
5877:
4226:
4052:
3995:
3975:
3954:
3815:
took the first shot at a new standard. At the time, the dominant web browser was
3763:
3701:
3613:
3559:
3322:
3183:
3009:
2977:
2611:
2503:
2502:
content such as voice and video. ATM uses a connection-oriented model in which a
2499:
2342:
2174:
2170:
2166:
facilitating a star topology for devices, and for cascading additional switches.
1952:
1684:
1635:
1549:
1462:
1458:
1442:
Most modern computer networks use protocols based on packet-mode transmission. A
1309:
1293:
1278:
1021:
1006:
979:
952:
940:
708:
489:
364:
273:
208:
162:
6881:
6765:
6746:
6427:
6408:
6393:
6374:
6334:
5260:
3528:
1999:
1874:
is a glass fiber. It carries pulses of light that represent data via lasers and
1859:
1570:
LAN, where each client connects to a central network switch, and logically in a
27:
Network that allows computers to share resources and communicate with each other
8369:
8273:
8172:
8018:
7990:
7395:
7319:
7281:
7153:
6648:"Bigger Monster, Weaker Chains: The Growth of an American Surveillance Society"
6046:
5999:
5948:
5566:
5543:
5032:
4638:
4599:
3884:
3705:
3659:—have expressed concern that increasing surveillance of citizens may lead to a
3617:
3563:
3498:
3438:
3392:
3375:
delays can range from less than a microsecond to several hundred milliseconds.
3194:
3190:
for members or users of the network, or to help the network itself to operate.
3116:
2973:
2704:
2495:
2326:
2240:
2160:
2156:
2045:
2041:
1852:
1699:
have not seen wide acceptance largely because they require modification of all
1553:
1443:
1356:
1321:
1081:
1025:
975:
937:
718:
524:
499:
494:
468:
457:
334:
298:
293:
253:
191:
5766:
5516:
5452:
5439:
Kirstein, Peter T. (2009). "The early history of packet switching in the UK".
5379:. Information Technology and Innovation Foundation. p. 11. Archived from
5312:
4615:
4548:
4363:
1465:
codes, and sequencing information. Typically, control information is found in
8437:
8258:
7546:
7304:
7261:
7100:
7054:
6876:
6852:
5985:
5853:
5524:
4906:
4763:
4662:
4623:
4423:
4371:
3964:
3567:
3502:
3413:
3340:
3309:
3285:
2981:
2596:
2248:
2222:
2087:
1870:
1805:
1800:
The following classes of wired technologies are used in computer networking.
1778:
1743:
1489:
1249:
1180:
1135:
1033:
1029:
948:
866:
677:
582:
567:
509:
258:
248:
5275:
5100:
4813:
4654:
4509:
4415:
2348:
There are many communication protocols, a few of which are described below.
2298:
8354:
8013:
7188:
3844:
3640:
3590:
3450:
3237:(DHCP) to ensure that the equipment on the network has a valid IP address.
3168:
3088:
3029:
2692:
2682:
2554:
2490:. This differs from other protocols such as the Internet protocol suite or
2462:
2319:
2252:
2144:
2037:
1835:
1696:
1640:
1607:
1595:
1581:
1571:
1563:
1267:
1104:
1093:
881:
622:
519:
374:
6260:
5598:
5581:
5351:
1072:
In the late 1950s, a network of computers was built for the U.S. military
8344:
7970:
7882:
7314:
7296:
7079:
7069:
7059:
5530:
S. Crocker who commented on the creation and destruction of associations.
3759:
3442:
3398:
In circuit-switched networks, network performance is synonymous with the
3218:
2853:
2647:
2443:
2415:
2407:
2399:
2338:
2279:
2095:
1958:
1944:
1820:
1766:
1626:
1533:
1367:
1344:
1317:
1209:
1037:
893:
861:
3920:
3349: – time it takes to push the packet's bits onto the link
2345:
and the home user's personal computer when the user is surfing the web.
1977:
is used, which limits the physical positioning of communicating devices.
8364:
8294:
7887:
7620:
7476:
6581:. Lecture Notes in Computer Science. Vol. 3285. pp. 317–323.
5157:
Heart, F.; McKenzie, A.; McQuillian, J.; Walden, D. (January 4, 1978).
4093:
3944:
3876:
3790:
3693:
3670:
3454:
3384:
3372:
3265:
3214:
3080:
2569:
2521:
There are a number of different digital cellular standards, including:
2487:
2431:
2244:
2137:
1886:
to interconnect continents. There are two basic types of fiber optics,
1762:
1585:
1313:
1297:
1176:
557:
514:
504:
5417:
5204:. Internet Archive. Wiley. pp. See page refs highlighted at url.
4320:
How Not to Network a Nation: The Uneasy History of the Soviet Internet
3337: – time it takes a router to process the packet header
3209:
are examples of well-known network services. Network services such as
3083:. The length of the lines indicates the delay between those two nodes.
943:
to communicate with each other. These interconnections are made up of
7869:
7830:
7251:
7158:
7084:
7049:
6757:
6419:
6385:
5558:
4798:"Data Communications at the National Physical Laboratory (1965-1975)"
4062:
3736:
3464:
same level of load. The stable state with low throughput is known as
3364:
2815:
1923:
1796:
are used to transmit light from one computer/network node to another.
1747:
1715:
1332:
851:
722:
278:
6886:
5904:
5582:"Ethernet: Distributed Packet Switching for Local Computer Networks"
3628:
program, technologies such as high-speed surveillance computers and
3075:
2434:
published by the Institute of Electrical and Electronics Engineers.
2290:
1907:
Computers are very often connected to networks using wireless links.
1513:
993:
Computer networks may be classified by many criteria, including the
175:
51:
7930:
7413:
7380:
6680:"Anonymous hacks UK government sites over 'draconian surveillance'"
6513:
4027:
3868:
3863:
3767:
3621:
3355: – time for a signal to propagate through the media
3202:
3095:
3063:
3050:
2811:
2736:
2592:
2534:
2491:
2447:
2387:
2213:
2204:
2124:, cleans it of unnecessary noise and regenerates it. The signal is
2115:
2033:
1973:
uses visible or invisible light for communications. In most cases,
1903:
1840:
1732:
The transmission media (often referred to in the literature as the
1692:
1644:
1537:
1305:
1301:
1263:
983:
925:
5397:
4838:
2173:(layer 2) of the OSI model and bridge traffic between two or more
1401:
In 1979, Robert Metcalfe pursued making Ethernet an open standard.
7375:
7074:
6576:
3644:
3367:. This delay is extended by more variable levels of delay due to
3269:
3148:
3139:(BGP), forming a redundant worldwide mesh of transmission paths.
3100:
2577:
2530:
2461:(SONET) and Synchronous Digital Hierarchy (SDH) are standardized
1688:
1662:
1545:
1541:
1434:
1255:
In 1972, commercial services were first deployed on experimental
1224:
6231:
6006:. 7.1.3 Connectivity to unauthenticated systems. February 2020.
5620:
5579:
5268:
Proceedings of the 2009 workshop on Re-architecting the internet
3967: – International standard for electrical and optical cables
6871:
6053:. 4.2.5 Interaction with other IEEE 802 layers. February 2021.
4023:
Military Communications: From Ancient Times to the 21st Century
3856:
3542:
is "the ability to provide and maintain an acceptable level of
3490:
3388:
3198:
2260:
1526:
which is the map of logical interconnections of network hosts.
1392:
5258:
4876:"The National Physical Laboratory Data Communications Network"
4345:"The beginnings of packet switching: some underlying concepts"
2186:
except the source, and discovers the location from the reply.
2177:
to form a single local network. Both are devices that forward
1395:, a token-passing network first used to share storage devices.
7324:
6292:
5166:(Technical report). Burlington, MA: Bolt, Beranek and Newman.
5156:
5022:
Prominently cites Baran and Davies as sources of inspiration.
4254:
3720:
3712:
3514:
3383:
The parameters that affect performance typically can include
3261:
3186:
are applications hosted by servers on a computer network, to
3123:, video transfer, and a broad range of information services.
2944:(WANs), metro, regional, national and transoceanic networks.
2835:
2234:
1962:
1813:
1789:
1085:
1077:
5542:
Cerf, Vinton; dalal, Yogen; Sunshine, Carl (December 1974).
4574:"NIHF Inductee Donald Davies, Who Invented Packet Switching"
4123:
The Compatible Time-Sharing System A Programmer's Guide]
3620:, recognize and monitor threats, and prevent or investigate
1604:: each node is connected to every other node in the network.
6645:
5062:
4739:. National Museum of Science and Industry. pp. 132–4.
4290:"Kitov Anatoliy Ivanovich. Russian Virtual Computer Museum"
3732:
3517:
3343: – time the packet spends in routing queues
3264:
may refer to consumed bandwidth, corresponding to achieved
2838:
2687:
2411:
2376:
2372:
2330:
2209:
2120:
A repeater is an electronic device that receives a network
1816:
1770:
1615:
1447:
1381:
1377:
1312:
and colleagues at the University of Hawaii. Metcalfe, with
1140:
6825:
Computer Networking with Internet Protocols and Technology
6811:
Shelly, Gary, et al. "Discovering Computers" 2003 Edition.
5810:
4873:
1738:) used to link devices to form a computer network include
1196:. Davies' hierarchical network design included high-speed
1172:
that implemented computer control in the switching fabric.
7360:
6206:
4935:"The real story of how the Internet became so vulnerable"
4549:"NIHF Inductee Paul Baran, Who Invented Packet Switching"
2807:
2603:
techniques enable the use of multiple alternative paths.
1574:, where each wireless client associates with the central
1289:, the first international heterogeneous computer network.
1045:
5119:
3606:
authorization from a court or other independent agency.
3325:
for a bit of data to travel across the network from one
2143:
An Ethernet repeater with multiple ports is known as an
1252:
remains critical to the operation of the Internet today.
6051:
IEEE STD 802.11-2020 (Revision of IEEE STD 802.11-2016)
5545:
Specification of Internet Transmission Control Protocol
5125:
3531:
addresses the subject of congestion control in detail.
1339:
published their seminal 1974 paper on internetworking,
1048:, and use of email and instant messaging applications.
6714:"Hacktivists in the frontline battle for the internet"
6616:
6614:
6232:"IEEE P802.3ba 40Gb/s and 100Gb/s Ethernet Task Force"
5261:"HAIR: Hierarchical architecture for internet routing"
6306:
Mansfield-Devine, Steve (December 2009). "Darknets".
6265:
IEEE 802.20 — Mobile Broadband Wireless Access (MBWA)
4259:
How the Web was Born: The Story of the World Wide Web
3111:. The Internet utilizes copper communications and an
2402:) deals with the routing of Ethernet packets using a
2341:(the Wi-Fi protocol). This stack is used between the
3453:
lead either to only a small increase in the network
2852:, limited geographic range, and lack of reliance on
6611:
6467:
3585:consists of provisions and policies adopted by the
3457:or to a potential reduction in network throughput.
1146:In 1960, the commercial airline reservation system
76:. Unsourced material may be challenged and removed.
6622:"Is the U.S. Turning Into a Surveillance Society?"
6095:"Design Principles for DSL-Based Access Solutions"
5682:
5498:"A Protocol for Packet Network Intercommunication"
5005:
4256:
3624:activity. With the advent of programs such as the
2208:A typical home or small office router showing the
1056:Computer networking may be considered a branch of
5836:CompTIA Network+ exam guide : (Exam N10-005)
5541:
4848:. ACM Symposium on Operating Systems Principles.
4639:"Principles and lessons in packet communications"
3634:Communications Assistance For Law Enforcement Act
2100:Institute of Electrical and Electronics Engineers
1341:A Protocol for Packet Network Intercommunication.
8435:
6677:
6305:
5676:
5674:
5580:Robert M. Metcalfe; David R. Boggs (July 1976).
3317:is a design and performance characteristic of a
6410:Domain names – Implementation and Specification
5901:"Bergen Linux User Group's CPIP Implementation"
4089:AN/FSQ-7: the computer that shaped the Cold War
3612:Surveillance is very useful to governments and
1376:in Europe, North America and Japan began using
826:
6646:Jay Stanley; Barry Steinhardt (January 2003).
6639:
6199:"New global standard for fully networked home"
5918:
4892:
4795:
2259:technology and cable television systems using
1639:that of the underlying one. For example, many
32:"Datacom" redirects here. For other uses, see
7453:Note: This template roughly follows the 2012
7429:
6902:
6440:
6335:"The Darknet: A Digital Copyright Revolution"
5829:
5827:
5671:
5235:. Internet Archive. Wiley. pp. 110–111.
5006:Norberg, Arthur L.; O'Neill, Judy E. (1996).
4198:"Reminiscences on the Theory of Time-Sharing"
3167:Darknets are distinct from other distributed
2987:
2761:
2477:
1218:National Physical Laboratory (United Kingdom)
955:methods that may be arranged in a variety of
901:
793:
6744:
5924:
5809:. Carnegie Mellon University. Archived from
5732:
5659:: CS1 maint: multiple names: authors list (
4874:Scantlebury, R. A.; Wilkinson, P.T. (1974).
4050:
2947:
2551:Digital Enhanced Cordless Telecommunications
2094:In Ethernet networks, each NIC has a unique
1831:) to create a high-speed local area network.
1304:, a networking system that was based on the
1148:semi-automatic business research environment
962:The nodes of a computer network can include
928:sharing resources located on or provided by
6735:
6494:: CS1 maint: numeric names: authors list (
6406:
5767:D. Andersen; H. Balakrishnan; M. Kaashoek;
4895:"Internet pioneers airbrushed from history"
4227:"Computer - Time-sharing and minicomputers"
3913:
2333:(the World Wide Web protocol) running over
1668:Another example of an overlay network is a
7436:
7422:
6909:
6895:
6740:
6738:
6708:
6167:
5824:
5663:) CS1 maint: numeric names: authors list (
5033:A History of the ARPANET: The First Decade
4673:
4169:"Computer Pioneers - Christopher Strachey"
3711:Examples of end-to-end encryption include
3160:) — using non-standard protocols and
2999:
2768:
2754:
2547:Universal Mobile Telecommunications System
2362:
2285:
2002:. It was implemented in real life in 2001.
1380:in the late 1970s and interconnected with
974:, or other specialized or general-purpose
908:
894:
800:
786:
6756:
6418:
6384:
5976:
5970:
5625:The Unpredictable Certainty: White Papers
5597:
5557:
5180:Packet and circuit-switched data networks
4682:"6.1 The Communications Subnet: BBN 1969"
4636:
3101:Advanced Research Projects Agency Network
2486:and encodes data into small, fixed-sized
1548:. This is still a common topology on the
136:Learn how and when to remove this message
6861:) is being considered for deletion. See
5866:
5680:
5495:
5476:"Oral History of Robert (Bob) W. Taylor"
5438:
5403:
5310:
5056:
4762:
4600:"On Distributed Communications Networks"
4454:. Simon and Schuster. pp. 237–246.
4447:
4019:
3680:
3437:. Typical effects of congestion include
3074:
2797:
2568:
2297:
2289:
2203:
2082:A network interface controller (NIC) is
2069:
1902:
1858:
1855:, designed for use in various scenarios.
1788:
1625:
1560:links instead, forming a star or a tree.
1512:
1433:
1408:, Bob Garner, Roy Ogus, and Yogen Dalal.
1117:UNESCO Information Processing Conference
947:technologies based on physically wired,
6840:, "Data Networks," Prentice Hall, 1992.
6447:(5th ed.). Elsevier. p. 372.
6400:
6372:
6261:"IEEE 802.20 Mission and Project Scope"
6117:
5838:(5th ed.). New York: McGraw-Hill.
5762:
5760:
5711:"Introduction to Ethernet Technologies"
5406:IEEE Annals of the History of Computing
5371:
5338:
5079:
4965:
4702:
4488:
4484:
4482:
4394:
4116:
3597:
3035:
2883:
2814:connections while technologies such as
2523:Global System for Mobile Communications
2150:
1150:(SABRE) went online with two connected
1013:mechanisms, and organizational intent.
14:
8436:
8153:Knowledge representation and reasoning
6877:IEEE Ethernet manufacturer information
6342:Richmond Journal of Law and Technology
5833:
5738:
5485:, CHM Reference number: X5059.2009: 28
5473:
5228:
5197:
5176:
5080:Roberts, Lawrence G. (November 1978).
5042:from the original on 1 December 2012.
4966:Roberts, Lawrence G. (November 1978).
4489:Roberts, Lawrence G. (November 1978).
4395:Roberts, Lawrence G. (November 1978).
4317:
4110:
4085:
4020:Sterling, Christopher H., ed. (2008).
3940:Comparison of network diagram software
3378:
3247:
3019:
2895:
2337:over IP (the Internet protocols) over
1183:independently invented the concept of
8178:Philosophy of artificial intelligence
7417:
6916:
6890:
6745:Rosen, E.; Rekhter, Y. (March 1999).
6444:Computer Networks: A Systems Approach
5232:Computer networks and their protocols
5201:Computer networks and their protocols
5073:
4791:
4789:
4732:
4597:
4342:
3550:and challenges to normal operation."
3534:
3420:
2825:
2543:Enhanced Data Rates for GSM Evolution
2516:
2353:Rate Based Satellite Control Protocol
2109:
2059:
1223:In 1969, the first four nodes of the
7497:Energy consumption (Green computing)
7443:
6510:"Telecommunications Magazine Online"
6441:Peterson, L.L.; Davie, B.S. (2011).
6332:
6326:
6142:
5757:
4479:
4263:. Oxford University Press. pp.
3830:
2963:
2863:
2784:
2247:by the digital signal to produce an
2169:Bridges and switches operate at the
1757:that uses copper and fiber media in
1592:(FDDI), made use of such a topology.
1347:, and Carl Sunshine wrote the first
74:adding citations to reliable sources
45:
8183:Distributed artificial intelligence
7455:ACM Computing Classification System
6882:A computer networking acronym guide
5779:Association for Computing Machinery
5505:IEEE Transactions on Communications
5372:Bennett, Richard (September 2009).
5222:
5082:"The evolution of packet switching"
4999:
4968:"The Evolution of Packet Switching"
4959:
4927:
4696:
4604:IEEE Transactions on Communications
4576:. National Inventors Hall of Fame.
4551:. National Inventors Hall of Fame.
4491:"The evolution of packet switching"
4397:"The evolution of packet switching"
4388:
4336:
4296:. Translated by Alexander Nitusov.
3577:
3558:Computer networks are also used by
3235:Dynamic Host Configuration Protocol
3129:Internet Assigned Numbers Authority
3109:United States Department of Defense
2914:
2618:
2559:Integrated Digital Enhanced Network
2494:that use variable-sized packets or
2357:
1502:
1363:as a shorthand for internetworking.
1143:economy management network project.
24:
7688:Integrated development environment
6805:
6653:. American Civil Liberties Union.
6624:. American Civil Liberties Union.
6555:. ResiliNets Research Initiative.
6092:
5489:
5467:
5350:. pp. 171–185. Archived from
5191:
5170:
4832:
4802:Annals of the History of Computing
4786:
4726:
4679:
4318:Peters, Benjamin (25 March 2016).
4287:
3178:
2096:Media Access Control (MAC) address
2086:that connects the computer to the
1773:signals as a transmission medium.
1683:guarantees achieve higher-quality
1621:
1366:In July 1976, Robert Metcalfe and
1009:, the network size, the topology,
822:
25:
8455:
8163:Automated planning and scheduling
7693:Software configuration management
6865:to help reach a consensus. ›
6844:
6468:ITU-D Study Group 2 (June 2006).
6407:Mockapetris, P. (November 1987).
6236:IEEE 802.3 ETHERNET WORKING GROUP
5313:"The Origins of Packet Switching"
4381:from the original on 2022-10-10.
4086:Ulmann, Bernd (August 19, 2014).
4058:A New History of Modern Computing
1429:
1285:(UCL), connecting the ARPANET to
1168:introduced the first widely used
1074:Semi-Automatic Ground Environment
8417:
8407:
8398:
8397:
7013:Object-oriented operating system
6781: This article incorporates
6776:
6471:Teletraffic Engineering Handbook
6145:Nanoscale Communication Networks
6122:. Boston, London: Artech House.
5474:Taylor, Bob (October 11, 2008),
5126:F.E. Froehlich, A. Kent (1990).
3894:Over the Internet, there can be
3303:
3240:Services are usually based on a
2860:, standardized by IEEE in 2010.
2636:
2017:
2006:The last two cases have a large
1970:Free-space optical communication
1721:
1590:Fiber Distributed Data Interface
1492:and waits until a link is free.
174:
50:
8408:
7811:Computational complexity theory
6794:General Services Administration
6724:from the original on 2018-03-14
6702:
6678:Emil Protalinski (2012-04-07).
6671:
6660:from the original on 2022-10-09
6628:from the original on 2017-03-14
6570:
6559:from the original on 2020-11-06
6545:
6520:
6502:
6461:
6434:
6366:
6355:from the original on 2012-04-15
6299:
6277:
6253:
6242:from the original on 2011-11-20
6224:
6191:
6180:from the original on 2023-02-04
6161:
6136:
6111:
6086:
6075:from the original on 2022-05-17
6039:
6028:from the original on 2023-02-04
5992:
5959:from the original on 2008-04-08
5941:
5903:. Blug.linux.no. Archived from
5893:
5860:
5795:
5785:from the original on 2011-11-24
5721:from the original on 2018-04-10
5703:
5642:from the original on 2023-02-04
5614:
5573:
5535:
5483:Computer History Museum Archive
5432:
5365:
5332:
5304:
5252:
5150:
5050:
5025:
4913:from the original on 2020-01-01
4886:
4867:
4855:from the original on 2022-10-10
4796:Campbell-Kelly, Martin (1987).
4756:
4630:
4591:
4580:from the original on 2022-02-12
4566:
4555:from the original on 2022-02-12
4541:
4527:from the original on 2023-02-04
4468:from the original on 2023-02-04
4441:
4311:
4300:from the original on 2023-02-04
4237:from the original on 2015-01-02
4179:from the original on 2019-05-15
4146:from the original on 2012-05-27
3632:software, and laws such as the
2822:typically form a wireless PAN.
2606:Routing can be contrasted with
2437:
1248:in the late 1970s with student
1103:filed a patent application for
1038:application and storage servers
1016:Computer networks support many
61:needs additional citations for
7595:Network performance evaluation
7023:Supercomputer operating system
6512:. January 2003. Archived from
4880:Proceedings of the 2nd ICCC 74
4281:
4248:
4219:
4190:
4161:
4079:
4044:
4013:
3657:American Civil Liberties Union
3653:Electronic Frontier Foundation
2509:ATM still plays a role in the
2459:Synchronous optical networking
1884:undersea communications cables
1159:Intergalactic Computer Network
1121:Compatible Time-Sharing System
1084:. It was the first commercial
13:
1:
7966:Multimedia information system
7951:Geographic information system
7941:Enterprise information system
7530:Computer systems organization
6850:
6376:Simple Mail Transfer Protocol
6320:10.1016/S1361-3723(09)70150-2
6308:Computer Fraud & Security
6170:"personal area network (PAN)"
5689:. O'Reilly & Associates.
5685:Ethernet The Definitive Guide
5681:Spurgeon, Charles E. (2000).
5317:Computer Resurrection Issue 5
5229:Davies, Donald Watts (1979).
5198:Davies, Donald Watts (1979).
4893:Guardian Staff (2013-06-25).
4769:A Brief History of the Future
4709:. Stripe Press. p. 286.
4703:Waldrop, M. Mitchell (2018).
4007:
3793:. E2EE also does not address
3698:application service providers
3294:bandwidth allocation protocol
2583:In packet-switched networks,
2030:network interface controllers
1765:. Wireless LAN standards use
1687:. Previous proposals such as
1349:Transmission Control Protocol
1129:Dartmouth Time Sharing System
8325:Computational social science
7913:Theoretical computer science
7726:Software development process
7502:Electronic design automation
7487:Very Large Scale Integration
6998:Just enough operating system
6983:Distributed operating system
6587:10.1007/978-3-540-30176-9_41
6373:Klensin, J. (October 2008).
6209:. 2008-12-12. Archived from
6059:10.1109/IEEESTD.2021.9363693
6012:10.1109/IEEESTD.2020.9018454
5628:. National Academies Press.
5441:IEEE Communications Magazine
4352:IEEE Communications Magazine
3505:in devices such as routers.
3363:a packet serially through a
3298:dynamic bandwidth allocation
3252:
3221:(people remember names like
2844:A LAN can be connected to a
2527:General Packet Radio Service
2453:
2266:
2066:Network interface controller
1990:was a humorous April fool's
1412:factor to its continued use.
1308:, developed in the 1960s by
7:
8148:Natural language processing
7936:Information storage systems
7111:User space and kernel space
6528:"State Transition Diagrams"
5867:A. Hooke (September 2000),
5496:Cerf, V.; Kahn, R. (1974).
3986:Network planning and design
3932:
3626:Total Information Awareness
3553:
3497:and the original Ethernet,
3070:
3057:
3044:
2425:
2382:
2373:Internet Protocol Version 4
1898:
1092:in 1958. The modem allowed
1088:for computers, released by
10:
8460:
8064:Human–computer interaction
8034:Intrusion detection system
7946:Social information systems
7931:Database management system
7018:Real-time operating system
5927:"bridge – network bridges"
5774:Resilient Overlay Networks
5132:. CRC Press. p. 344.
3853:application-layer gateways
3804:
3800:
3520:home networking standard.
3407:Asynchronous Transfer Mode
3319:telecommunications network
3307:
3188:provide some functionality
3142:
2994:enterprise private network
2988:Enterprise private network
2564:
2484:time-division multiplexing
2478:Asynchronous Transfer Mode
2472:Asynchronous Transfer Mode
2442:Wireless LAN based on the
2350:
2270:
2232:
2197:
2193:
2154:
2113:
2063:
2021:
1910:
1880:wave division multiplexing
1839:cabling is used for wired
1725:
1705:Internet service providers
1506:
1107:in the United Kingdom and
1051:
38:
31:
8393:
8330:Computational engineering
8305:Computational mathematics
8282:
8229:
8191:
8138:
8100:
8062:
8004:
7921:
7867:
7829:
7774:
7711:
7644:
7608:
7565:
7529:
7462:
7451:
7353:
7290:
7236:
7214:Multilevel feedback queue
7209:Fixed-priority preemptive
7197:
7132:
7123:
7093:
7040:
7031:
6993:Hobbyist operating system
6988:Embedded operating system
6970:
6924:
6827:, Pearson Education 2004.
6553:"Definitions: Resilience"
6118:Paetsch, Michael (1993).
5739:Pelkey, James L. (2007).
5586:Communications of the ACM
5517:10.1109/TCOM.1974.1092259
5453:10.1109/MCOM.2009.4785372
5160:Arpanet Completion Report
4616:10.1109/TCOM.1964.1088883
4448:Isaacson, Walter (2014).
4364:10.1109/MCOM.2002.1018006
3649:Reporters Without Borders
3414:state transition diagrams
3225:better than numbers like
2954:metropolitan area network
2948:Metropolitan area network
2228:
2216:network cable connections
1975:line-of-sight propagation
1932:Communications satellites
1888:single-mode optical fiber
1849:electromagnetic induction
1819:technology uses existing
1746:, and free space. In the
1517:Common network topologies
1497:maximum transmission unit
1287:British academic networks
1283:University College London
1238:Bolt Beranek & Newman
978:. They are identified by
945:telecommunication network
653:Exponential random (ERGM)
320:Informational (computing)
8340:Computational healthcare
8335:Differentiable computing
8254:Graphics processing unit
7673:Domain-specific language
7542:Computational complexity
7257:General protection fault
7008:Network operating system
6962:User features comparison
6863:templates for discussion
4772:. Phoenix. p. 292.
4733:Yates, David M. (1997).
3914:Journals and newsletters
3807:Transport Layer Security
3787:random number generators
3572:denial-of-service attack
2720:Municipal wireless (MWN)
2539:Evolution-Data Optimized
1892:multi-mode optical fiber
1784:
1775:Power line communication
1630:A sample overlay network
1387:In 1976, John Murphy of
1024:, such as access to the
1003:communications protocols
340:Scientific collaboration
34:Datacom (disambiguation)
8315:Computational chemistry
8249:Photograph manipulation
8140:Artificial intelligence
7956:Decision support system
7003:Mobile operating system
5870:Interplanetary Internet
5276:10.1145/1658978.1658990
5101:10.1109/PROC.1978.11141
5089:Proceedings of the IEEE
4814:10.1109/MAHC.1987.10023
4655:10.1109/PROC.1978.11143
4643:Proceedings of the IEEE
4510:10.1109/PROC.1978.11141
4498:Proceedings of the IEEE
4416:10.1109/PROC.1978.11141
4404:Proceedings of the IEEE
4231:Encyclopedia Britannica
3991:Network traffic control
3950:History of the Internet
3908:communications security
3881:Border Gateway Protocol
3589:to prevent and monitor
3435:reliable communications
3137:Border Gateway Protocol
3115:backbone to enable the
3103:(ARPANET) developed by
3006:virtual private network
3000:Virtual private network
2878:digital subscriber line
2742:Interplanetary Internet
2610:in its assumption that
2369:Internet protocol suite
2363:Internet protocol suite
2286:Communication protocols
2257:digital subscriber line
1982:Interplanetary Internet
1602:Fully connected network
1529:Common topologies are:
1452:packet-switched network
1446:is a formatted unit of
1343:Later that year, Cerf,
1296:wrote a formal memo at
1204:and the essence of the
1202:communication protocols
1125:BBN Time-Sharing System
997:used to carry signals,
934:communication protocols
932:. Computers use common
769:Category:Network theory
289:Preferential attachment
8380:Educational technology
8211:Reinforcement learning
7961:Process control system
7859:Computational geometry
7849:Algorithmic efficiency
7844:Analysis of algorithms
7492:Systems on Chip (SoCs)
7106:Loadable kernel module
6789:Federal Standard 1037C
6783:public domain material
6333:Wood, Jessica (2010).
5803:"End System Multicast"
5348:Proceedings of ICCC 74
5177:Clarke, Peter (1982).
4637:Kleinrock, L. (1978).
4120:; et al. (1963).
3971:Minimum-Pairs Protocol
3960:Information revolution
3779:technical exploitation
3690:digital communications
3501:reduction in TCP, and
3327:communication endpoint
3084:
2820:infrared communication
2574:
2420:Network Access Control
2404:Spanning Tree Protocol
2308:communication protocol
2303:
2295:
2217:
2079:
1988:IP over Avian Carriers
1908:
1864:
1797:
1670:distributed hash table
1631:
1518:
1439:
1416:
1240:. In the early 1970s,
1175:Throughout the 1960s,
833:
658:Random geometric (RGG)
18:Network infrastructure
8350:Electronic publishing
8320:Computational biology
8310:Computational physics
8206:Unsupervised learning
8120:Distributed computing
7996:Information retrieval
7903:Mathematical analysis
7893:Mathematical software
7776:Theory of computation
7741:Software construction
7731:Requirements analysis
7609:Software organization
7537:Computer architecture
7507:Hardware acceleration
7472:Printed circuit board
7174:Process control block
7140:Computer multitasking
6978:Disk operating system
5834:Meyers, Mike (2012).
5717:. WideBand Products.
5599:10.1145/360248.360253
4055:(14 September 2021).
3921:Open Computer Science
3841:community of interest
3686:End-to-end encryption
3681:End to end encryption
3587:network administrator
3489:in protocols such as
3292:(using, for example,
3213:(DNS) give names for
3078:
2874:cable Internet access
2804:personal area network
2798:Personal area network
2572:
2418:defines a port-based
2351:Further information:
2301:
2293:
2207:
2073:
2012:two-way communication
2008:round-trip delay time
1906:
1862:
1792:
1726:Further information:
1629:
1576:wireless access point
1516:
1507:Further information:
1437:
1424:Distributed computing
1389:Datapoint Corporation
1351:(TCP) specification,
1326:PARC Universal Packet
1266:network, directed by
832:
774:Category:Graph theory
8110:Concurrent computing
8082:Ubiquitous computing
8054:Application security
8049:Information security
7878:Discrete mathematics
7854:Randomized algorithm
7806:Computability theory
7784:Model of computation
7756:Software maintenance
7751:Software engineering
7713:Software development
7663:Programming language
7658:Programming paradigm
7575:Network architecture
7345:Virtual tape library
6937:Forensic engineering
6143:Bush, S. F. (2010).
5978:Tanenbaum, Andrew S.
4343:Baran, Paul (2002).
4173:history.computer.org
3904:consumer-to-consumer
3900:business-to-consumer
3896:business-to-business
3825:symmetric-key cipher
3603:Network surveillance
3598:Network surveillance
3479:congestion avoidance
3473:Modern networks use
3290:bandwidth allocation
3282:bandwidth throttling
3278:bandwidth management
3207:network file sharing
3036:Organizational scope
2890:storage area network
2884:Storage area network
2273:Firewall (computing)
2151:Bridges and switches
1992:Request for Comments
1374:Public data networks
1328:for internetworking.
1262:In 1973, the French
1257:public data networks
1246:hierarchical routing
1206:end-to-end principle
1101:Christopher Strachey
1090:AT&T Corporation
1062:computer engineering
70:improve this article
39:For other uses, see
8385:Document management
8375:Operations research
8300:Enterprise software
8216:Multi-task learning
8201:Supervised learning
7923:Information systems
7746:Software deployment
7703:Software repository
7557:Real-time computing
7354:Supporting concepts
7340:Virtual file system
4984:on 31 December 2018
4882:. pp. 223–228.
3666:Hepting v. AT&T
3487:exponential backoff
3467:congestive collapse
3379:Performance metrics
3321:. It specifies the
3248:Network performance
3026:global area network
3020:Global area network
2926:network performance
2902:campus area network
2896:Campus area network
2850:data transfer rates
2557:(IS-136/TDMA), and
2312:connection-oriented
2212:telephone line and
2010:, which gives slow
1712:Akamai Technologies
1676:) indexed by keys.
1359:, coining the term
1324:also developed the
995:transmission medium
972:networking hardware
578:Degree distribution
229:Community structure
8168:Search methodology
8115:Parallel computing
8072:Interaction design
7981:Computing platform
7908:Numerical analysis
7898:Information theory
7683:Software framework
7646:Software notations
7585:Network components
7482:Integrated circuit
7277:Segmentation fault
7125:Process management
5955:. September 1996.
5925:Bradley Mitchell.
4975:IEEE Invited Paper
4598:Baran, P. (1964).
4294:computer-museum.ru
4065:. pp. 87–89.
3981:Network simulation
3889:Domain Name System
3817:Netscape Navigator
3540:Network resilience
3535:Network resilience
3523:For the Internet,
3510:quality of service
3475:congestion control
3426:Network congestion
3421:Network congestion
3369:network congestion
3347:Transmission delay
3211:Domain Name System
3133:address registries
3121:Internet of things
3113:optical networking
3085:
2942:wide area networks
2930:network congestion
2832:local area network
2826:Local area network
2715:Metropolitan (MAN)
2575:
2517:Cellular standards
2304:
2296:
2218:
2200:Router (computing)
2129:kilometers apart.
2110:Repeaters and hubs
2080:
2060:Network interfaces
1909:
1876:optical amplifiers
1865:
1827:, phone lines and
1798:
1794:Fiber-optic cables
1781:to transmit data.
1777:uses a building's
1759:local area network
1681:quality of service
1659:Address resolution
1632:
1588:networks, and the
1552:, although modern
1519:
1480:With packets, the
1440:
1214:local area network
1189:data communication
1113:J. C. R. Licklider
1066:telecommunications
964:personal computers
957:network topologies
847:Process management
834:
762:Network scientists
688:Soft configuration
85:"Computer network"
8444:Computer networks
8431:
8430:
8360:Electronic voting
8290:Quantum Computing
8283:Applied computing
8269:Image compression
8039:Hardware security
8029:Security services
7986:Digital marketing
7766:Open-source model
7678:Modeling language
7590:Network scheduler
7411:
7410:
7267:Memory protection
7238:Memory management
7232:
7231:
7224:Shortest job next
7119:
7118:
6918:Operating systems
6834:Dimitri Bertsekas
6821:William Stallings
6596:978-3-540-23659-7
6579:Applied Computing
6454:978-0-1238-5060-7
6154:978-1-60807-003-9
6129:978-0-8900-6688-1
6068:978-1-5044-7283-8
6021:978-1-5044-6440-6
5982:Computer Networks
5635:978-0-309-17414-5
5418:10.1109/85.759368
5285:978-1-60558-749-3
5242:978-0-471-99750-4
5211:978-0-471-99750-4
5017:978-0-8018-5152-0
4746:978-0-901805-94-2
4716:978-1-953953-36-0
4706:The Dream Machine
4680:Pelkey, James L.
4649:(11): 1320–1329.
4274:978-0-19-286207-5
4136:978-0-262-03008-3
4103:978-3-486-85670-5
4037:978-1-85109-737-1
4001:Network on a chip
3883:. Typically, the
3831:Views of networks
3821:root certificates
3729:instant messaging
3715:for web traffic,
3661:mass surveillance
3461:Network protocols
3353:Propagation delay
3274:bandwidth shaping
2970:wide area network
2964:Wide area network
2958:metropolitan area
2938:Internet backbone
2870:home area network
2864:Home area network
2846:wide area network
2791:nanoscale network
2785:Nanoscale network
2778:
2777:
2612:network addresses
2601:Multipath routing
2589:packet forwarding
2585:routing protocols
2468:digital telephony
2134:propagation delay
2084:computer hardware
2024:Node (networking)
1940:Cellular networks
1753:A widely adopted
1728:Data transmission
1655:telephone network
1568:switched Ethernet
1459:network addresses
1281:into practice at
1242:Leonard Kleinrock
1236:team working for
1127:in 1962, and the
1115:at the inaugural
1080:system using the
988:Internet Protocol
980:network addresses
918:
917:
857:Memory management
816:Operating systems
810:
809:
730:
729:
638:Bianconi–Barabási
532:
531:
350:Artificial neural
325:Telecommunication
146:
145:
138:
120:
16:(Redirected from
8451:
8421:
8420:
8411:
8410:
8401:
8400:
8221:Cross-validation
8193:Machine learning
8077:Social computing
8044:Network security
7839:Algorithm design
7761:Programming team
7721:Control variable
7698:Software library
7636:Software quality
7631:Operating system
7580:Network protocol
7445:Computer science
7438:
7431:
7424:
7415:
7414:
7366:Computer network
7130:
7129:
7038:
7037:
6911:
6904:
6897:
6888:
6887:
6802:
6801:
6796:. Archived from
6780:
6779:
6770:
6769:
6760:
6758:10.17487/RFC2547
6742:
6733:
6732:
6730:
6729:
6706:
6700:
6699:
6697:
6695:
6686:. Archived from
6675:
6669:
6668:
6666:
6665:
6659:
6652:
6643:
6637:
6636:
6634:
6633:
6618:
6609:
6608:
6574:
6568:
6567:
6565:
6564:
6549:
6543:
6542:
6540:
6539:
6530:. Archived from
6524:
6518:
6517:
6506:
6500:
6499:
6493:
6485:
6483:
6477:. Archived from
6476:
6465:
6459:
6458:
6438:
6432:
6431:
6422:
6420:10.17487/RFC1035
6404:
6398:
6397:
6388:
6386:10.17487/RFC5321
6370:
6364:
6363:
6361:
6360:
6354:
6339:
6330:
6324:
6323:
6303:
6297:
6296:
6291:. Archived from
6289:The Opto Project
6281:
6275:
6274:
6272:
6271:
6257:
6251:
6250:
6248:
6247:
6228:
6222:
6221:
6219:
6218:
6195:
6189:
6188:
6186:
6185:
6168:Margaret Rouse.
6165:
6159:
6158:
6147:. Artech House.
6140:
6134:
6133:
6115:
6109:
6108:
6106:
6100:. Archived from
6099:
6093:Martin, Thomas.
6090:
6084:
6083:
6081:
6080:
6043:
6037:
6036:
6034:
6033:
5996:
5990:
5989:
5984:(4th ed.).
5974:
5968:
5967:
5965:
5964:
5945:
5939:
5938:
5933:. Archived from
5922:
5916:
5915:
5913:
5912:
5897:
5891:
5890:
5889:
5888:
5882:
5875:
5864:
5858:
5857:
5831:
5822:
5821:
5819:
5818:
5807:project web site
5799:
5793:
5792:
5791:
5790:
5771:(October 2001),
5764:
5755:
5754:
5752:
5751:
5736:
5730:
5729:
5727:
5726:
5707:
5701:
5700:
5688:
5678:
5669:
5668:
5658:
5650:
5648:
5647:
5618:
5612:
5611:
5601:
5577:
5571:
5570:
5561:
5559:10.17487/RFC0675
5539:
5533:
5532:
5502:
5493:
5487:
5486:
5480:
5471:
5465:
5464:
5436:
5430:
5429:
5401:
5395:
5394:
5392:
5391:
5385:
5378:
5369:
5363:
5362:
5360:
5359:
5336:
5330:
5329:
5324:
5323:
5308:
5302:
5301:
5265:
5256:
5250:
5249:
5226:
5220:
5219:
5195:
5189:
5187:
5185:
5174:
5168:
5167:
5165:
5154:
5148:
5147:
5123:
5117:
5116:
5086:
5077:
5071:
5070:
5065:. Archived from
5054:
5048:
5047:
5037:
5029:
5023:
5021:
5003:
4997:
4996:
4991:
4989:
4983:
4977:. Archived from
4972:
4963:
4957:
4956:
4951:
4950:
4941:. Archived from
4931:
4925:
4924:
4919:
4918:
4890:
4884:
4883:
4871:
4865:
4863:
4861:
4860:
4854:
4847:
4836:
4830:
4829:
4827:high-speed lines
4808:(3/4): 221–247.
4793:
4784:
4783:
4760:
4754:
4753:
4730:
4724:
4723:
4700:
4694:
4693:
4677:
4671:
4670:
4634:
4628:
4627:
4595:
4589:
4588:
4586:
4585:
4570:
4564:
4563:
4561:
4560:
4545:
4539:
4538:
4533:
4532:
4526:
4495:
4486:
4477:
4476:
4474:
4473:
4445:
4439:
4438:
4401:
4392:
4386:
4385:
4380:
4349:
4340:
4334:
4333:
4315:
4309:
4308:
4306:
4305:
4285:
4279:
4278:
4262:
4252:
4246:
4245:
4243:
4242:
4223:
4217:
4216:
4214:
4213:
4204:. Archived from
4202:jmc.stanford.edu
4194:
4188:
4187:
4185:
4184:
4165:
4159:
4158:
4152:
4151:
4145:
4128:
4114:
4108:
4107:
4083:
4077:
4076:
4053:Ceruzzi, Paul E.
4048:
4042:
4041:
4017:
3795:traffic analysis
3583:Network Security
3578:Network security
3564:computer viruses
3560:security hackers
3400:grade of service
3335:Processing delay
3242:service protocol
3231:
3230:
3184:Network services
2921:backbone network
2915:Backbone network
2880:(DSL) provider.
2770:
2763:
2756:
2653:Near-field (NFC)
2640:
2627:Computer network
2623:
2622:
2619:Geographic scale
2358:Common protocols
2181:of data between
2175:network segments
1913:Wireless network
1853:category ratings
1740:electrical cable
1524:network topology
1509:Network topology
1503:Network topology
1486:circuit switched
1185:packet switching
1170:telephone switch
1166:Western Electric
1058:computer science
1036:, shared use of
941:interconnections
922:computer network
910:
903:
896:
825:
812:
811:
802:
795:
788:
673:Stochastic block
663:Hyperbolic (HGN)
612:
611:
475:
464:
396:
395:
304:Social influence
178:
150:
149:
141:
134:
130:
127:
121:
119:
78:
54:
46:
21:
8459:
8458:
8454:
8453:
8452:
8450:
8449:
8448:
8434:
8433:
8432:
8427:
8418:
8389:
8370:Word processing
8278:
8264:Virtual reality
8225:
8187:
8158:Computer vision
8134:
8130:Multiprocessing
8096:
8058:
8024:Security hacker
8000:
7976:Digital library
7917:
7868:Mathematics of
7863:
7825:
7801:Automata theory
7796:Formal language
7770:
7736:Software design
7707:
7640:
7626:Virtual machine
7604:
7600:Network service
7561:
7552:Embedded system
7525:
7458:
7447:
7442:
7412:
7407:
7349:
7310:Defragmentation
7295:
7286:
7272:Protection ring
7241:
7228:
7200:
7193:
7115:
7089:
7027:
6966:
6920:
6915:
6866:
6847:
6838:Robert Gallager
6808:
6806:Further reading
6786:
6777:
6775:
6773:
6743:
6736:
6727:
6725:
6707:
6703:
6693:
6691:
6676:
6672:
6663:
6661:
6657:
6650:
6644:
6640:
6631:
6629:
6620:
6619:
6612:
6597:
6575:
6571:
6562:
6560:
6551:
6550:
6546:
6537:
6535:
6526:
6525:
6521:
6508:
6507:
6503:
6487:
6486:
6481:
6474:
6466:
6462:
6455:
6439:
6435:
6405:
6401:
6371:
6367:
6358:
6356:
6352:
6337:
6331:
6327:
6304:
6300:
6283:
6282:
6278:
6269:
6267:
6259:
6258:
6254:
6245:
6243:
6230:
6229:
6225:
6216:
6214:
6197:
6196:
6192:
6183:
6181:
6166:
6162:
6155:
6141:
6137:
6130:
6116:
6112:
6104:
6097:
6091:
6087:
6078:
6076:
6069:
6045:
6044:
6040:
6031:
6029:
6022:
5998:
5997:
5993:
5975:
5971:
5962:
5960:
5949:"Define switch"
5947:
5946:
5942:
5923:
5919:
5910:
5908:
5899:
5898:
5894:
5886:
5884:
5880:
5873:
5865:
5861:
5846:
5832:
5825:
5816:
5814:
5801:
5800:
5796:
5788:
5786:
5765:
5758:
5749:
5747:
5737:
5733:
5724:
5722:
5709:
5708:
5704:
5697:
5679:
5672:
5652:
5651:
5645:
5643:
5636:
5619:
5615:
5578:
5574:
5540:
5536:
5500:
5494:
5490:
5478:
5472:
5468:
5437:
5433:
5402:
5398:
5389:
5387:
5383:
5376:
5370:
5366:
5357:
5355:
5337:
5333:
5321:
5319:
5309:
5305:
5286:
5263:
5257:
5253:
5243:
5227:
5223:
5212:
5196:
5192:
5183:
5175:
5171:
5163:
5155:
5151:
5140:
5124:
5120:
5095:(11): 1307–13.
5084:
5078:
5074:
5055:
5051:
5035:
5031:
5030:
5026:
5018:
5004:
5000:
4987:
4985:
4981:
4970:
4964:
4960:
4948:
4946:
4939:Washington Post
4933:
4932:
4928:
4916:
4914:
4891:
4887:
4872:
4868:
4858:
4856:
4852:
4845:
4837:
4833:
4794:
4787:
4780:
4761:
4757:
4747:
4731:
4727:
4717:
4701:
4697:
4678:
4674:
4635:
4631:
4596:
4592:
4583:
4581:
4572:
4571:
4567:
4558:
4556:
4547:
4546:
4542:
4530:
4528:
4524:
4504:(11): 1307–13.
4493:
4487:
4480:
4471:
4469:
4462:
4446:
4442:
4410:(11): 1307–13.
4399:
4393:
4389:
4378:
4347:
4341:
4337:
4330:
4316:
4312:
4303:
4301:
4286:
4282:
4275:
4253:
4249:
4240:
4238:
4225:
4224:
4220:
4211:
4209:
4196:
4195:
4191:
4182:
4180:
4167:
4166:
4162:
4149:
4147:
4143:
4137:
4126:
4115:
4111:
4104:
4084:
4080:
4073:
4051:Haigh, Thomas;
4049:
4045:
4038:
4030:. p. 399.
4018:
4014:
4010:
4005:
3976:Network mapping
3955:Information Age
3935:
3916:
3833:
3809:
3803:
3785:, poor quality
3764:Yahoo Messenger
3702:confidentiality
3683:
3647:groups—such as
3614:law enforcement
3600:
3580:
3556:
3546:in the face of
3537:
3483:traffic control
3423:
3381:
3312:
3306:
3255:
3250:
3228:
3227:
3181:
3179:Network service
3145:
3073:
3060:
3047:
3038:
3022:
3010:overlay network
3002:
2990:
2978:data link layer
2974:common carriers
2966:
2950:
2917:
2898:
2886:
2866:
2858:100 Gbit/s
2828:
2800:
2787:
2774:
2683:Wireless (WLAN)
2630:
2621:
2567:
2519:
2504:virtual circuit
2480:
2456:
2440:
2428:
2385:
2375:(IPv4) and for
2365:
2360:
2355:
2343:wireless router
2318:, they may use
2288:
2275:
2269:
2241:carrier signals
2237:
2231:
2202:
2196:
2171:data link layer
2163:
2155:Main articles:
2153:
2118:
2112:
2068:
2062:
2026:
2020:
1953:spread spectrum
1915:
1901:
1787:
1735:physical medium
1730:
1724:
1685:streaming media
1636:overlay network
1624:
1622:Overlay network
1550:data link layer
1511:
1505:
1463:error detection
1432:
1419:
1320:, Ed Taft, and
1310:Norman Abramson
1294:Robert Metcalfe
1279:internetworking
1054:
1011:traffic control
1007:network traffic
953:radio-frequency
951:, and wireless
914:
839:Common features
831:
823:
806:
744:
709:Boolean network
683:Maximum entropy
633:Barabási–Albert
550:
467:
456:
244:Controllability
209:Complex network
196:
183:
182:
181:
180:
179:
163:Network science
142:
131:
125:
122:
79:
77:
67:
55:
44:
37:
28:
23:
22:
15:
12:
11:
5:
8457:
8447:
8446:
8429:
8428:
8426:
8425:
8415:
8405:
8394:
8391:
8390:
8388:
8387:
8382:
8377:
8372:
8367:
8362:
8357:
8352:
8347:
8342:
8337:
8332:
8327:
8322:
8317:
8312:
8307:
8302:
8297:
8292:
8286:
8284:
8280:
8279:
8277:
8276:
8274:Solid modeling
8271:
8266:
8261:
8256:
8251:
8246:
8241:
8235:
8233:
8227:
8226:
8224:
8223:
8218:
8213:
8208:
8203:
8197:
8195:
8189:
8188:
8186:
8185:
8180:
8175:
8173:Control method
8170:
8165:
8160:
8155:
8150:
8144:
8142:
8136:
8135:
8133:
8132:
8127:
8125:Multithreading
8122:
8117:
8112:
8106:
8104:
8098:
8097:
8095:
8094:
8089:
8084:
8079:
8074:
8068:
8066:
8060:
8059:
8057:
8056:
8051:
8046:
8041:
8036:
8031:
8026:
8021:
8019:Formal methods
8016:
8010:
8008:
8002:
8001:
7999:
7998:
7993:
7991:World Wide Web
7988:
7983:
7978:
7973:
7968:
7963:
7958:
7953:
7948:
7943:
7938:
7933:
7927:
7925:
7919:
7918:
7916:
7915:
7910:
7905:
7900:
7895:
7890:
7885:
7880:
7874:
7872:
7865:
7864:
7862:
7861:
7856:
7851:
7846:
7841:
7835:
7833:
7827:
7826:
7824:
7823:
7818:
7813:
7808:
7803:
7798:
7793:
7792:
7791:
7780:
7778:
7772:
7771:
7769:
7768:
7763:
7758:
7753:
7748:
7743:
7738:
7733:
7728:
7723:
7717:
7715:
7709:
7708:
7706:
7705:
7700:
7695:
7690:
7685:
7680:
7675:
7670:
7665:
7660:
7654:
7652:
7642:
7641:
7639:
7638:
7633:
7628:
7623:
7618:
7612:
7610:
7606:
7605:
7603:
7602:
7597:
7592:
7587:
7582:
7577:
7571:
7569:
7563:
7562:
7560:
7559:
7554:
7549:
7544:
7539:
7533:
7531:
7527:
7526:
7524:
7523:
7514:
7509:
7504:
7499:
7494:
7489:
7484:
7479:
7474:
7468:
7466:
7460:
7459:
7452:
7449:
7448:
7441:
7440:
7433:
7426:
7418:
7409:
7408:
7406:
7405:
7400:
7399:
7398:
7396:User interface
7393:
7383:
7378:
7373:
7368:
7363:
7357:
7355:
7351:
7350:
7348:
7347:
7342:
7337:
7332:
7327:
7322:
7320:File attribute
7317:
7312:
7307:
7301:
7299:
7288:
7287:
7285:
7284:
7282:Virtual memory
7279:
7274:
7269:
7264:
7259:
7254:
7248:
7246:
7234:
7233:
7230:
7229:
7227:
7226:
7221:
7216:
7211:
7205:
7203:
7195:
7194:
7192:
7191:
7186:
7181:
7176:
7171:
7166:
7161:
7156:
7154:Context switch
7151:
7136:
7134:
7127:
7121:
7120:
7117:
7116:
7114:
7113:
7108:
7103:
7097:
7095:
7091:
7090:
7088:
7087:
7082:
7077:
7072:
7067:
7062:
7057:
7052:
7046:
7044:
7035:
7029:
7028:
7026:
7025:
7020:
7015:
7010:
7005:
7000:
6995:
6990:
6985:
6980:
6974:
6972:
6968:
6967:
6965:
6964:
6959:
6954:
6949:
6944:
6939:
6934:
6928:
6926:
6922:
6921:
6914:
6913:
6906:
6899:
6891:
6885:
6884:
6879:
6874:
6846:
6845:External links
6843:
6842:
6841:
6831:
6828:
6818:
6815:
6812:
6807:
6804:
6800:on 2022-01-22.
6772:
6771:
6734:
6712:(2012-04-20).
6701:
6670:
6638:
6610:
6595:
6569:
6544:
6519:
6516:on 2011-02-08.
6501:
6484:on 2007-01-11.
6460:
6453:
6433:
6399:
6365:
6325:
6298:
6295:on 2005-01-15.
6276:
6252:
6223:
6190:
6160:
6153:
6135:
6128:
6110:
6107:on 2011-07-22.
6085:
6067:
6038:
6020:
5991:
5969:
5940:
5937:on 2008-03-28.
5917:
5892:
5859:
5844:
5823:
5794:
5756:
5731:
5702:
5695:
5670:
5634:
5613:
5592:(5): 395–404.
5572:
5534:
5511:(5): 637–648.
5488:
5466:
5431:
5396:
5364:
5331:
5311:Derek Barber.
5303:
5284:
5251:
5241:
5221:
5210:
5190:
5169:
5149:
5138:
5118:
5072:
5069:on 2008-03-08.
5057:Chris Sutton.
5049:
5024:
5016:
4998:
4958:
4926:
4885:
4866:
4831:
4785:
4778:
4764:Naughton, John
4755:
4745:
4725:
4715:
4695:
4672:
4629:
4590:
4565:
4540:
4478:
4460:
4440:
4387:
4335:
4329:978-0262034180
4328:
4310:
4280:
4273:
4247:
4218:
4189:
4160:
4135:
4118:Corbató, F. J.
4109:
4102:
4078:
4072:978-0262542906
4071:
4043:
4036:
4011:
4009:
4006:
4004:
4003:
3998:
3993:
3988:
3983:
3978:
3973:
3968:
3962:
3957:
3952:
3947:
3942:
3936:
3934:
3931:
3930:
3929:
3915:
3912:
3885:human-readable
3847:technologies.
3832:
3829:
3805:Main article:
3802:
3799:
3682:
3679:
3639:However, many
3618:social control
3599:
3596:
3579:
3576:
3568:computer worms
3555:
3552:
3536:
3533:
3439:queueing delay
3431:retransmission
3422:
3419:
3393:bit error rate
3380:
3377:
3357:
3356:
3350:
3344:
3338:
3308:Main article:
3305:
3302:
3254:
3251:
3249:
3246:
3195:World Wide Web
3180:
3177:
3144:
3141:
3117:World Wide Web
3072:
3069:
3059:
3056:
3046:
3043:
3037:
3034:
3021:
3018:
3001:
2998:
2989:
2986:
2965:
2962:
2949:
2946:
2916:
2913:
2897:
2894:
2885:
2882:
2865:
2862:
2827:
2824:
2799:
2796:
2786:
2783:
2776:
2775:
2773:
2772:
2765:
2758:
2750:
2747:
2746:
2745:
2744:
2739:
2734:
2729:
2724:
2723:
2722:
2712:
2707:
2702:
2697:
2696:
2695:
2690:
2688:Virtual (VLAN)
2685:
2680:
2670:
2665:
2663:Personal (PAN)
2660:
2655:
2650:
2642:
2641:
2633:
2632:
2620:
2617:
2597:routing tables
2566:
2563:
2518:
2515:
2479:
2476:
2474:(ATM) frames.
2455:
2452:
2439:
2436:
2427:
2424:
2384:
2381:
2364:
2361:
2359:
2356:
2327:protocol stack
2316:connectionless
2287:
2284:
2271:Main article:
2268:
2265:
2233:Main article:
2230:
2227:
2198:Main article:
2195:
2192:
2161:Network switch
2157:Network bridge
2152:
2149:
2114:Main article:
2111:
2108:
2064:Main article:
2061:
2058:
2052:, modems, and
2022:Main article:
2019:
2016:
2004:
2003:
1985:
1978:
1966:
1948:
1936:
1928:
1911:Main article:
1900:
1897:
1896:
1895:
1857:
1856:
1832:
1811:
1786:
1783:
1723:
1720:
1623:
1620:
1612:
1611:
1605:
1599:
1593:
1579:
1561:
1558:point-to-point
1554:physical layer
1504:
1501:
1467:packet headers
1444:network packet
1438:Network Packet
1431:
1430:Network packet
1428:
1418:
1415:
1414:
1413:
1409:
1402:
1399:
1396:
1385:
1371:
1364:
1329:
1322:Butler Lampson
1290:
1275:Peter Kirstein
1271:
1260:
1253:
1221:
1173:
1162:
1155:
1144:
1132:
1097:
1082:Bell 101 modem
1053:
1050:
1026:World Wide Web
916:
915:
913:
912:
905:
898:
890:
887:
886:
885:
884:
879:
874:
869:
867:Device drivers
864:
859:
854:
849:
841:
840:
836:
835:
819:
818:
808:
807:
805:
804:
797:
790:
782:
779:
778:
777:
776:
771:
765:
764:
759:
754:
746:
745:
743:
742:
739:
735:
732:
731:
728:
727:
726:
725:
716:
711:
703:
702:
698:
697:
696:
695:
690:
685:
680:
675:
670:
665:
660:
655:
650:
648:Watts–Strogatz
645:
640:
635:
630:
625:
617:
616:
608:
607:
603:
602:
601:
600:
595:
590:
585:
580:
575:
570:
565:
560:
552:
551:
549:
548:
543:
537:
534:
533:
530:
529:
528:
527:
522:
517:
512:
507:
502:
497:
492:
484:
483:
479:
478:
477:
476:
469:Incidence list
465:
458:Adjacency list
454:
449:
444:
439:
434:
429:
427:Data structure
424:
419:
414:
409:
401:
400:
392:
391:
385:
384:
383:
382:
377:
372:
367:
362:
357:
355:Interdependent
352:
347:
342:
337:
332:
327:
322:
314:
313:
309:
308:
307:
306:
301:
299:Network effect
296:
294:Balance theory
291:
286:
281:
276:
271:
266:
261:
256:
254:Social capital
251:
246:
241:
236:
231:
226:
221:
216:
211:
206:
198:
197:
195:
194:
188:
185:
184:
173:
172:
171:
170:
169:
166:
165:
159:
158:
144:
143:
58:
56:
49:
26:
9:
6:
4:
3:
2:
8456:
8445:
8442:
8441:
8439:
8424:
8416:
8414:
8406:
8404:
8396:
8395:
8392:
8386:
8383:
8381:
8378:
8376:
8373:
8371:
8368:
8366:
8363:
8361:
8358:
8356:
8353:
8351:
8348:
8346:
8343:
8341:
8338:
8336:
8333:
8331:
8328:
8326:
8323:
8321:
8318:
8316:
8313:
8311:
8308:
8306:
8303:
8301:
8298:
8296:
8293:
8291:
8288:
8287:
8285:
8281:
8275:
8272:
8270:
8267:
8265:
8262:
8260:
8259:Mixed reality
8257:
8255:
8252:
8250:
8247:
8245:
8242:
8240:
8237:
8236:
8234:
8232:
8228:
8222:
8219:
8217:
8214:
8212:
8209:
8207:
8204:
8202:
8199:
8198:
8196:
8194:
8190:
8184:
8181:
8179:
8176:
8174:
8171:
8169:
8166:
8164:
8161:
8159:
8156:
8154:
8151:
8149:
8146:
8145:
8143:
8141:
8137:
8131:
8128:
8126:
8123:
8121:
8118:
8116:
8113:
8111:
8108:
8107:
8105:
8103:
8099:
8093:
8092:Accessibility
8090:
8088:
8087:Visualization
8085:
8083:
8080:
8078:
8075:
8073:
8070:
8069:
8067:
8065:
8061:
8055:
8052:
8050:
8047:
8045:
8042:
8040:
8037:
8035:
8032:
8030:
8027:
8025:
8022:
8020:
8017:
8015:
8012:
8011:
8009:
8007:
8003:
7997:
7994:
7992:
7989:
7987:
7984:
7982:
7979:
7977:
7974:
7972:
7969:
7967:
7964:
7962:
7959:
7957:
7954:
7952:
7949:
7947:
7944:
7942:
7939:
7937:
7934:
7932:
7929:
7928:
7926:
7924:
7920:
7914:
7911:
7909:
7906:
7904:
7901:
7899:
7896:
7894:
7891:
7889:
7886:
7884:
7881:
7879:
7876:
7875:
7873:
7871:
7866:
7860:
7857:
7855:
7852:
7850:
7847:
7845:
7842:
7840:
7837:
7836:
7834:
7832:
7828:
7822:
7819:
7817:
7814:
7812:
7809:
7807:
7804:
7802:
7799:
7797:
7794:
7790:
7787:
7786:
7785:
7782:
7781:
7779:
7777:
7773:
7767:
7764:
7762:
7759:
7757:
7754:
7752:
7749:
7747:
7744:
7742:
7739:
7737:
7734:
7732:
7729:
7727:
7724:
7722:
7719:
7718:
7716:
7714:
7710:
7704:
7701:
7699:
7696:
7694:
7691:
7689:
7686:
7684:
7681:
7679:
7676:
7674:
7671:
7669:
7666:
7664:
7661:
7659:
7656:
7655:
7653:
7651:
7647:
7643:
7637:
7634:
7632:
7629:
7627:
7624:
7622:
7619:
7617:
7614:
7613:
7611:
7607:
7601:
7598:
7596:
7593:
7591:
7588:
7586:
7583:
7581:
7578:
7576:
7573:
7572:
7570:
7568:
7564:
7558:
7555:
7553:
7550:
7548:
7547:Dependability
7545:
7543:
7540:
7538:
7535:
7534:
7532:
7528:
7522:
7518:
7515:
7513:
7510:
7508:
7505:
7503:
7500:
7498:
7495:
7493:
7490:
7488:
7485:
7483:
7480:
7478:
7475:
7473:
7470:
7469:
7467:
7465:
7461:
7456:
7450:
7446:
7439:
7434:
7432:
7427:
7425:
7420:
7419:
7416:
7404:
7401:
7397:
7394:
7392:
7389:
7388:
7387:
7384:
7382:
7379:
7377:
7374:
7372:
7369:
7367:
7364:
7362:
7359:
7358:
7356:
7352:
7346:
7343:
7341:
7338:
7336:
7333:
7331:
7328:
7326:
7323:
7321:
7318:
7316:
7313:
7311:
7308:
7306:
7303:
7302:
7300:
7298:
7293:
7289:
7283:
7280:
7278:
7275:
7273:
7270:
7268:
7265:
7263:
7262:Memory paging
7260:
7258:
7255:
7253:
7250:
7249:
7247:
7244:
7239:
7235:
7225:
7222:
7220:
7217:
7215:
7212:
7210:
7207:
7206:
7204:
7202:
7196:
7190:
7187:
7185:
7182:
7180:
7177:
7175:
7172:
7170:
7167:
7165:
7162:
7160:
7157:
7155:
7152:
7149:
7145:
7141:
7138:
7137:
7135:
7131:
7128:
7126:
7122:
7112:
7109:
7107:
7104:
7102:
7101:Device driver
7099:
7098:
7096:
7092:
7086:
7083:
7081:
7078:
7076:
7073:
7071:
7068:
7066:
7063:
7061:
7058:
7056:
7053:
7051:
7048:
7047:
7045:
7043:
7042:Architectures
7039:
7036:
7034:
7030:
7024:
7021:
7019:
7016:
7014:
7011:
7009:
7006:
7004:
7001:
6999:
6996:
6994:
6991:
6989:
6986:
6984:
6981:
6979:
6976:
6975:
6973:
6969:
6963:
6960:
6958:
6955:
6953:
6950:
6948:
6945:
6943:
6940:
6938:
6935:
6933:
6930:
6929:
6927:
6923:
6919:
6912:
6907:
6905:
6900:
6898:
6893:
6892:
6889:
6883:
6880:
6878:
6875:
6873:
6869:
6864:
6860:
6859:
6854:
6849:
6848:
6839:
6835:
6832:
6829:
6826:
6822:
6819:
6816:
6813:
6810:
6809:
6803:
6799:
6795:
6791:
6790:
6784:
6767:
6764:
6759:
6754:
6750:
6749:
6748:BGP/MPLS VPNs
6741:
6739:
6723:
6719:
6715:
6711:
6705:
6690:on 2013-04-03
6689:
6685:
6681:
6674:
6656:
6649:
6642:
6627:
6623:
6617:
6615:
6606:
6602:
6598:
6592:
6588:
6584:
6580:
6573:
6558:
6554:
6548:
6534:on 2003-10-15
6533:
6529:
6523:
6515:
6511:
6505:
6497:
6491:
6480:
6473:
6472:
6464:
6456:
6450:
6446:
6445:
6437:
6429:
6426:
6421:
6416:
6412:
6411:
6403:
6395:
6392:
6387:
6382:
6378:
6377:
6369:
6351:
6347:
6343:
6336:
6329:
6321:
6317:
6313:
6309:
6302:
6294:
6290:
6286:
6280:
6266:
6262:
6256:
6241:
6237:
6233:
6227:
6213:on 2009-02-21
6212:
6208:
6204:
6203:ITU-T Newslog
6200:
6194:
6179:
6175:
6171:
6164:
6156:
6150:
6146:
6139:
6131:
6125:
6121:
6114:
6103:
6096:
6089:
6074:
6070:
6064:
6060:
6056:
6052:
6048:
6042:
6027:
6023:
6017:
6013:
6009:
6005:
6001:
5995:
5987:
5986:Prentice Hall
5983:
5979:
5973:
5958:
5954:
5950:
5944:
5936:
5932:
5928:
5921:
5907:on 2014-02-15
5906:
5902:
5896:
5883:on 2012-01-13
5879:
5872:
5871:
5863:
5855:
5851:
5847:
5845:9780071789226
5841:
5837:
5830:
5828:
5813:on 2005-02-21
5812:
5808:
5804:
5798:
5784:
5780:
5776:
5775:
5770:
5763:
5761:
5746:
5742:
5741:"Yogen Dalal"
5735:
5720:
5716:
5715:www.wband.com
5712:
5706:
5698:
5696:1-56592-660-9
5692:
5687:
5686:
5677:
5675:
5666:
5662:
5656:
5641:
5637:
5631:
5627:
5626:
5617:
5609:
5605:
5600:
5595:
5591:
5587:
5583:
5576:
5568:
5565:
5560:
5555:
5551:
5547:
5546:
5538:
5531:
5526:
5522:
5518:
5514:
5510:
5506:
5499:
5492:
5484:
5477:
5470:
5462:
5458:
5454:
5450:
5446:
5442:
5435:
5427:
5423:
5419:
5415:
5411:
5407:
5400:
5386:on 2019-08-29
5382:
5375:
5368:
5354:on 2013-10-20
5353:
5349:
5345:
5341:
5335:
5328:
5318:
5314:
5307:
5300:
5295:
5291:
5287:
5281:
5277:
5273:
5269:
5262:
5255:
5248:
5244:
5238:
5234:
5233:
5225:
5218:
5213:
5207:
5203:
5202:
5194:
5182:
5181:
5173:
5162:
5161:
5153:
5146:
5141:
5135:
5131:
5130:
5122:
5115:
5110:
5106:
5102:
5098:
5094:
5090:
5083:
5076:
5068:
5064:
5060:
5053:
5046:
5041:
5034:
5028:
5019:
5013:
5009:
5002:
4995:
4988:September 10,
4980:
4976:
4969:
4962:
4955:
4945:on 2015-05-30
4944:
4940:
4936:
4930:
4923:
4912:
4908:
4904:
4900:
4896:
4889:
4881:
4877:
4870:
4851:
4844:
4843:
4835:
4828:
4823:
4819:
4815:
4811:
4807:
4803:
4799:
4792:
4790:
4781:
4779:9780753810934
4775:
4771:
4770:
4765:
4759:
4752:
4748:
4742:
4738:
4737:
4729:
4722:
4718:
4712:
4708:
4707:
4699:
4692:
4687:
4683:
4676:
4669:
4664:
4660:
4656:
4652:
4648:
4644:
4640:
4633:
4625:
4621:
4617:
4613:
4609:
4605:
4601:
4594:
4579:
4575:
4569:
4554:
4550:
4544:
4537:
4523:
4519:
4515:
4511:
4507:
4503:
4499:
4492:
4485:
4483:
4467:
4463:
4461:9781476708690
4457:
4453:
4452:
4444:
4437:
4433:
4429:
4425:
4421:
4417:
4413:
4409:
4405:
4398:
4391:
4384:
4377:
4373:
4369:
4365:
4361:
4357:
4353:
4346:
4339:
4331:
4325:
4322:. MIT Press.
4321:
4314:
4299:
4295:
4291:
4284:
4276:
4270:
4266:
4261:
4260:
4251:
4236:
4232:
4228:
4222:
4208:on 2020-04-28
4207:
4203:
4199:
4193:
4178:
4174:
4170:
4164:
4157:
4142:
4138:
4132:
4129:. MIT Press.
4125:
4124:
4119:
4113:
4105:
4099:
4095:
4091:
4090:
4082:
4074:
4068:
4064:
4060:
4059:
4054:
4047:
4039:
4033:
4029:
4025:
4024:
4016:
4012:
4002:
3999:
3997:
3994:
3992:
3989:
3987:
3984:
3982:
3979:
3977:
3974:
3972:
3969:
3966:
3965:ISO/IEC 11801
3963:
3961:
3958:
3956:
3953:
3951:
3948:
3946:
3943:
3941:
3938:
3937:
3927:
3923:
3922:
3918:
3917:
3911:
3909:
3905:
3901:
3897:
3892:
3890:
3886:
3882:
3878:
3872:
3870:
3865:
3860:
3858:
3854:
3848:
3846:
3842:
3838:
3828:
3826:
3822:
3818:
3814:
3808:
3798:
3796:
3792:
3788:
3784:
3780:
3775:
3773:
3769:
3765:
3761:
3757:
3753:
3749:
3744:
3742:
3738:
3734:
3730:
3726:
3722:
3718:
3714:
3709:
3707:
3703:
3699:
3695:
3691:
3687:
3678:
3676:
3672:
3668:
3667:
3662:
3658:
3654:
3650:
3646:
3642:
3637:
3635:
3631:
3627:
3623:
3619:
3615:
3610:
3607:
3604:
3595:
3592:
3588:
3584:
3575:
3573:
3569:
3565:
3561:
3551:
3549:
3545:
3541:
3532:
3530:
3526:
3521:
3519:
3516:
3511:
3506:
3504:
3503:fair queueing
3500:
3496:
3492:
3488:
3484:
3480:
3476:
3471:
3469:
3468:
3462:
3458:
3456:
3452:
3448:
3444:
3440:
3436:
3432:
3427:
3418:
3415:
3410:
3408:
3403:
3401:
3396:
3395:and latency.
3394:
3390:
3386:
3376:
3374:
3370:
3366:
3362:
3354:
3351:
3348:
3345:
3342:
3341:Queuing delay
3339:
3336:
3333:
3332:
3331:
3328:
3324:
3320:
3316:
3315:Network delay
3311:
3310:Network delay
3304:Network delay
3301:
3299:
3295:
3291:
3287:
3286:bandwidth cap
3283:
3279:
3275:
3271:
3267:
3263:
3259:
3245:
3243:
3238:
3236:
3232:
3229:210.121.67.18
3224:
3220:
3219:MAC addresses
3216:
3212:
3208:
3204:
3200:
3196:
3191:
3189:
3185:
3176:
3174:
3170:
3165:
3163:
3159:
3155:
3150:
3140:
3138:
3134:
3130:
3124:
3122:
3118:
3114:
3110:
3106:
3102:
3097:
3092:
3090:
3082:
3077:
3068:
3065:
3055:
3052:
3042:
3033:
3031:
3030:wireless LANs
3027:
3017:
3014:
3011:
3007:
2997:
2995:
2985:
2983:
2982:network layer
2979:
2975:
2971:
2961:
2959:
2955:
2945:
2943:
2939:
2933:
2931:
2927:
2922:
2912:
2909:
2907:
2903:
2893:
2891:
2881:
2879:
2875:
2871:
2861:
2859:
2855:
2851:
2847:
2842:
2840:
2837:
2833:
2823:
2821:
2817:
2813:
2809:
2805:
2795:
2792:
2782:
2771:
2766:
2764:
2759:
2757:
2752:
2751:
2749:
2748:
2743:
2740:
2738:
2735:
2733:
2730:
2728:
2725:
2721:
2718:
2717:
2716:
2713:
2711:
2708:
2706:
2703:
2701:
2698:
2694:
2691:
2689:
2686:
2684:
2681:
2679:
2678:Storage (SAN)
2676:
2675:
2674:
2671:
2669:
2666:
2664:
2661:
2659:
2656:
2654:
2651:
2649:
2646:
2645:
2644:
2643:
2639:
2635:
2634:
2628:
2625:
2624:
2616:
2613:
2609:
2604:
2602:
2598:
2594:
2590:
2586:
2581:
2579:
2571:
2562:
2560:
2556:
2552:
2548:
2544:
2540:
2536:
2532:
2528:
2524:
2514:
2512:
2507:
2505:
2501:
2497:
2493:
2489:
2485:
2475:
2473:
2469:
2464:
2460:
2451:
2449:
2445:
2435:
2433:
2423:
2421:
2417:
2413:
2409:
2405:
2401:
2397:
2394:For example,
2392:
2389:
2380:
2378:
2374:
2370:
2354:
2349:
2346:
2344:
2340:
2336:
2332:
2328:
2323:
2321:
2317:
2313:
2309:
2300:
2292:
2283:
2281:
2280:cyber attacks
2274:
2264:
2262:
2258:
2254:
2253:audio signals
2250:
2249:analog signal
2246:
2242:
2236:
2226:
2224:
2223:routing table
2215:
2211:
2206:
2201:
2191:
2187:
2184:
2180:
2176:
2172:
2167:
2162:
2158:
2148:
2146:
2141:
2139:
2135:
2130:
2127:
2126:retransmitted
2123:
2117:
2107:
2105:
2101:
2097:
2092:
2089:
2088:network media
2085:
2077:
2072:
2067:
2057:
2055:
2051:
2047:
2043:
2039:
2035:
2031:
2025:
2018:Network nodes
2015:
2013:
2009:
2001:
1997:
1993:
1989:
1986:
1983:
1979:
1976:
1972:
1971:
1967:
1964:
1960:
1956:
1954:
1949:
1946:
1942:
1941:
1937:
1934:
1933:
1929:
1926:
1925:
1920:
1919:
1918:
1914:
1905:
1893:
1889:
1885:
1881:
1877:
1873:
1872:
1871:optical fiber
1867:
1866:
1861:
1854:
1850:
1846:
1842:
1838:
1837:
1833:
1830:
1826:
1825:coaxial cable
1822:
1818:
1815:
1812:
1808:
1807:
1806:Coaxial cable
1803:
1802:
1801:
1795:
1791:
1782:
1780:
1779:power cabling
1776:
1772:
1769:, others use
1768:
1764:
1760:
1756:
1751:
1749:
1745:
1744:optical fiber
1741:
1737:
1736:
1729:
1722:Network links
1719:
1717:
1713:
1710:For example,
1708:
1706:
1702:
1698:
1694:
1690:
1686:
1682:
1677:
1675:
1671:
1666:
1664:
1660:
1656:
1651:
1648:
1646:
1642:
1637:
1628:
1619:
1617:
1609:
1606:
1603:
1600:
1597:
1594:
1591:
1587:
1583:
1580:
1577:
1573:
1569:
1565:
1562:
1559:
1556:variants use
1555:
1551:
1547:
1543:
1539:
1535:
1532:
1531:
1530:
1527:
1525:
1515:
1510:
1500:
1498:
1493:
1491:
1487:
1483:
1478:
1476:
1472:
1468:
1464:
1460:
1455:
1453:
1450:carried by a
1449:
1445:
1436:
1427:
1425:
1410:
1407:
1403:
1400:
1397:
1394:
1390:
1386:
1383:
1379:
1375:
1372:
1369:
1365:
1362:
1358:
1354:
1350:
1346:
1342:
1338:
1334:
1330:
1327:
1323:
1319:
1315:
1311:
1307:
1306:Aloha network
1303:
1299:
1295:
1291:
1288:
1284:
1280:
1276:
1272:
1269:
1265:
1261:
1258:
1254:
1251:
1250:Farouk Kamoun
1247:
1243:
1239:
1235:
1231:
1226:
1222:
1219:
1215:
1211:
1207:
1203:
1199:
1195:
1190:
1186:
1182:
1181:Donald Davies
1178:
1174:
1171:
1167:
1163:
1160:
1156:
1153:
1149:
1145:
1142:
1137:
1136:Anatoly Kitov
1133:
1130:
1126:
1123:in 1961, the
1122:
1118:
1114:
1110:
1109:John McCarthy
1106:
1102:
1098:
1095:
1091:
1087:
1083:
1079:
1075:
1071:
1070:
1069:
1067:
1063:
1059:
1049:
1047:
1043:
1039:
1035:
1031:
1030:digital video
1027:
1023:
1019:
1014:
1012:
1008:
1004:
1000:
996:
991:
989:
985:
982:and may have
981:
977:
973:
969:
965:
960:
958:
954:
950:
946:
942:
939:
935:
931:
930:network nodes
927:
923:
911:
906:
904:
899:
897:
892:
891:
889:
888:
883:
880:
878:
875:
873:
870:
868:
865:
863:
860:
858:
855:
853:
850:
848:
845:
844:
843:
842:
838:
837:
821:
820:
817:
814:
813:
803:
798:
796:
791:
789:
784:
783:
781:
780:
775:
772:
770:
767:
766:
763:
760:
758:
755:
753:
750:
749:
748:
747:
740:
737:
736:
734:
733:
724:
720:
717:
715:
712:
710:
707:
706:
705:
704:
700:
699:
694:
693:LFR Benchmark
691:
689:
686:
684:
681:
679:
678:Blockmodeling
676:
674:
671:
669:
666:
664:
661:
659:
656:
654:
651:
649:
646:
644:
643:Fitness model
641:
639:
636:
634:
631:
629:
626:
624:
621:
620:
619:
618:
614:
613:
610:
609:
605:
604:
599:
596:
594:
591:
589:
586:
584:
583:Assortativity
581:
579:
576:
574:
571:
569:
566:
564:
561:
559:
556:
555:
554:
553:
547:
544:
542:
539:
538:
536:
535:
526:
523:
521:
518:
516:
513:
511:
508:
506:
503:
501:
498:
496:
493:
491:
488:
487:
486:
485:
481:
480:
474:
470:
466:
463:
459:
455:
453:
450:
448:
445:
443:
440:
438:
435:
433:
430:
428:
425:
423:
420:
418:
415:
413:
410:
408:
405:
404:
403:
402:
398:
397:
394:
393:
390:
387:
386:
381:
378:
376:
373:
371:
368:
366:
363:
361:
358:
356:
353:
351:
348:
346:
343:
341:
338:
336:
333:
331:
328:
326:
323:
321:
318:
317:
316:
315:
312:Network types
311:
310:
305:
302:
300:
297:
295:
292:
290:
287:
285:
282:
280:
277:
275:
272:
270:
267:
265:
262:
260:
259:Link analysis
257:
255:
252:
250:
249:Graph drawing
247:
245:
242:
240:
237:
235:
232:
230:
227:
225:
222:
220:
217:
215:
212:
210:
207:
205:
202:
201:
200:
199:
193:
190:
189:
187:
186:
177:
168:
167:
164:
161:
160:
156:
152:
151:
148:
140:
137:
129:
118:
115:
111:
108:
104:
101:
97:
94:
90:
87: –
86:
82:
81:Find sources:
75:
71:
65:
64:
59:This article
57:
53:
48:
47:
42:
35:
30:
19:
8355:Cyberwarfare
8014:Cryptography
7566:
7365:
7297:file systems
7189:Time-sharing
6856:
6824:
6798:the original
6788:
6774:
6747:
6726:. Retrieved
6718:The Guardian
6717:
6704:
6692:. Retrieved
6688:the original
6683:
6673:
6662:. Retrieved
6641:
6630:. Retrieved
6578:
6572:
6561:. Retrieved
6547:
6536:. Retrieved
6532:the original
6522:
6514:the original
6504:
6479:the original
6470:
6463:
6443:
6436:
6409:
6402:
6375:
6368:
6357:. Retrieved
6345:
6341:
6328:
6311:
6307:
6301:
6293:the original
6288:
6279:
6268:. Retrieved
6264:
6255:
6244:. Retrieved
6235:
6226:
6215:. Retrieved
6211:the original
6202:
6193:
6182:. Retrieved
6173:
6163:
6144:
6138:
6119:
6113:
6102:the original
6088:
6077:. Retrieved
6050:
6041:
6030:. Retrieved
6003:
5994:
5981:
5972:
5961:. Retrieved
5952:
5943:
5935:the original
5930:
5920:
5909:. Retrieved
5905:the original
5895:
5885:, retrieved
5878:the original
5869:
5862:
5835:
5815:. Retrieved
5811:the original
5806:
5797:
5787:, retrieved
5773:
5748:. Retrieved
5744:
5734:
5723:. Retrieved
5714:
5705:
5684:
5644:. Retrieved
5624:
5616:
5589:
5585:
5575:
5544:
5537:
5528:
5508:
5504:
5491:
5482:
5469:
5447:(2): 18–26.
5444:
5440:
5434:
5412:(1): 38–44.
5409:
5405:
5399:
5388:. Retrieved
5381:the original
5367:
5356:. Retrieved
5352:the original
5347:
5334:
5326:
5320:. Retrieved
5316:
5306:
5297:
5267:
5254:
5246:
5231:
5224:
5215:
5200:
5193:
5179:
5172:
5159:
5152:
5143:
5128:
5121:
5112:
5092:
5088:
5075:
5067:the original
5052:
5043:
5027:
5007:
5001:
4993:
4986:. Retrieved
4979:the original
4974:
4961:
4953:
4947:. Retrieved
4943:the original
4938:
4929:
4921:
4915:. Retrieved
4899:The Guardian
4898:
4888:
4879:
4869:
4857:. Retrieved
4841:
4834:
4825:
4805:
4801:
4768:
4758:
4750:
4735:
4728:
4720:
4705:
4698:
4689:
4685:
4675:
4666:
4646:
4642:
4632:
4607:
4603:
4593:
4582:. Retrieved
4568:
4557:. Retrieved
4543:
4535:
4529:. Retrieved
4501:
4497:
4470:. Retrieved
4450:
4443:
4435:
4407:
4403:
4390:
4382:
4358:(7): 42–48.
4355:
4351:
4338:
4319:
4313:
4302:. Retrieved
4293:
4283:
4258:
4250:
4239:. Retrieved
4230:
4221:
4210:. Retrieved
4206:the original
4201:
4192:
4181:. Retrieved
4172:
4163:
4154:
4148:. Retrieved
4122:
4112:
4088:
4081:
4057:
4046:
4022:
4015:
3919:
3893:
3873:
3861:
3849:
3845:peer-to-peer
3834:
3810:
3776:
3745:
3710:
3688:(E2EE) is a
3684:
3664:
3641:civil rights
3638:
3616:to maintain
3611:
3608:
3601:
3591:unauthorized
3581:
3557:
3538:
3522:
3507:
3472:
3465:
3459:
3451:offered load
3433:to maintain
3424:
3411:
3404:
3397:
3382:
3358:
3314:
3313:
3256:
3239:
3226:
3222:
3192:
3182:
3171:networks as
3169:peer-to-peer
3166:
3153:
3146:
3125:
3093:
3089:internetwork
3086:
3081:IP addresses
3061:
3048:
3039:
3023:
3015:
3008:(VPN) is an
3003:
2991:
2967:
2951:
2934:
2918:
2910:
2899:
2887:
2867:
2854:leased lines
2843:
2829:
2801:
2788:
2779:
2705:Campus (CAN)
2626:
2605:
2582:
2576:
2555:Digital AMPS
2520:
2508:
2481:
2463:multiplexing
2457:
2441:
2438:Wireless LAN
2429:
2396:MAC bridging
2393:
2386:
2366:
2347:
2324:
2320:circuit mode
2305:
2276:
2263:technology.
2238:
2219:
2188:
2168:
2164:
2145:Ethernet hub
2142:
2131:
2119:
2093:
2081:
2027:
2005:
1994:, issued as
1968:
1955:technologies
1950:
1938:
1930:
1922:Terrestrial
1921:
1916:
1869:
1836:Twisted pair
1834:
1804:
1799:
1754:
1752:
1733:
1731:
1709:
1697:IP multicast
1678:
1667:
1652:
1649:
1641:peer-to-peer
1633:
1613:
1608:Tree network
1596:Mesh network
1582:Ring network
1572:wireless LAN
1564:Star network
1528:
1520:
1494:
1479:
1477:in between.
1475:payload data
1456:
1441:
1420:
1360:
1340:
1268:Louis Pouzin
1105:time-sharing
1094:digital data
1055:
1046:fax machines
1018:applications
1015:
1005:to organize
992:
961:
924:is a set of
921:
919:
882:Input/output
871:
668:Hierarchical
623:Random graph
471: /
460: /
442:Neighborhood
319:
284:Transitivity
264:Optimization
147:
132:
123:
113:
106:
99:
92:
80:
68:Please help
63:verification
60:
29:
8365:Video games
8345:Digital art
8102:Concurrency
7971:Data mining
7883:Probability
7616:Interpreter
7315:Device file
7305:Boot loader
7219:Round-robin
7144:Cooperative
7080:Rump kernel
7070:Multikernel
7060:Microkernel
6957:Usage share
6851:‹ The
6314:(12): 4–6.
5340:Després, R.
4288:Kitova, O.
3926:open access
3760:Google Talk
3743:for radio.
3443:packet loss
3119:(WWW), the
2673:Local (LAN)
2500:low-latency
2444:IEEE 802.11
2416:IEEE 802.1X
2408:IEEE 802.1Q
2400:IEEE 802.1D
2339:IEEE 802.11
1959:IEEE 802.11
1945:transceiver
1829:power lines
1821:home wiring
1767:radio waves
1534:Bus network
1368:David Boggs
1345:Yogen Dalal
1318:Yogen Dalal
1300:describing
1210:NPL network
1194:reliability
862:File system
714:agent based
628:Erdős–Rényi
269:Reciprocity
234:Percolation
219:Small-world
8423:Glossaries
8295:E-commerce
7888:Statistics
7831:Algorithms
7789:Stochastic
7621:Middleware
7477:Peripheral
7245:protection
7201:algorithms
7199:Scheduling
7148:Preemptive
7094:Components
7065:Monolithic
6932:Comparison
6868:Networking
6728:2012-06-17
6710:James Ball
6664:2009-03-13
6632:2009-03-13
6563:2011-11-12
6538:2003-07-13
6359:2011-10-25
6270:2011-11-12
6246:2011-11-12
6217:2011-11-12
6184:2011-01-29
6174:TechTarget
6079:2022-05-09
6032:2022-05-09
5963:2008-04-08
5911:2014-03-01
5887:2011-11-12
5817:2013-05-25
5789:2011-11-12
5750:2023-05-07
5725:2018-04-09
5646:2021-03-08
5390:2017-09-11
5358:2013-08-30
5322:2024-06-05
5139:0824729005
4949:2020-02-18
4917:2020-07-31
4859:2020-09-15
4610:(1): 1–9.
4584:2022-02-12
4559:2022-02-12
4531:2022-02-12
4472:2021-06-04
4304:2021-10-11
4241:2020-01-23
4212:2020-01-23
4183:2020-01-23
4150:2020-05-26
4094:De Gruyter
4008:References
3945:Cyberspace
3877:IP address
3791:key escrow
3694:encrypting
3671:hacktivist
3655:, and the
3630:biometrics
3562:to deploy
3455:throughput
3385:throughput
3373:IP network
3266:throughput
2980:, and the
2727:Wide (WAN)
2693:Home (HAN)
2432:IEEE 802.3
2410:describes
2138:5-4-3 rule
1951:Radio and
1890:(SMF) and
1763:IEEE 802.3
1586:Token ring
1314:John Shoch
1298:Xerox PARC
1259:in Europe.
1177:Paul Baran
1152:mainframes
872:Networking
852:Interrupts
741:Categories
598:Efficiency
593:Modularity
573:Clustering
558:Centrality
546:Algorithms
370:Dependency
345:Biological
224:Scale-free
96:newspapers
8244:Rendering
8239:Animation
7870:computing
7821:Semantics
7512:Processor
7335:Partition
7252:Bus error
7179:Real-time
7159:Interrupt
7085:Unikernel
7050:Exokernel
6490:cite book
5953:webopedia
5931:About.com
5854:748332969
5769:R. Morris
5655:cite book
5525:1558-0857
4907:0261-3077
4766:(2000) .
4663:0018-9219
4624:0096-2244
4424:0018-9219
4372:0163-6804
4063:MIT Press
3837:workgroup
3737:telephony
3706:integrity
3675:Anonymous
3258:Bandwidth
3253:Bandwidth
2816:Bluetooth
2648:Nanoscale
2593:computers
2541:(EV-DO),
2511:last mile
2454:SONET/SDH
2267:Firewalls
2245:modulated
2054:firewalls
2034:repeaters
1924:microwave
1845:crosstalk
1748:OSI model
1716:multicast
1540:, called
1482:bandwidth
1406:Ron Crane
1333:Vint Cerf
1331:In 1974,
1292:In 1973,
1273:In 1973,
1164:In 1965,
1134:In 1959,
1131:in 1963).
1099:In 1959,
999:bandwidth
984:hostnames
926:computers
490:Bipartite
412:Component
330:Transport
279:Homophily
239:Evolution
214:Contagion
126:June 2023
8438:Category
8403:Category
8231:Graphics
8006:Security
7668:Compiler
7567:Networks
7464:Hardware
7381:Live USB
7243:resource
7133:Concepts
6971:Variants
6952:Timeline
6853:template
6722:Archived
6694:12 March
6655:Archived
6626:Archived
6557:Archived
6350:Archived
6240:Archived
6178:Archived
6073:Archived
6026:Archived
5980:(2003).
5957:Archived
5783:archived
5719:Archived
5640:Archived
5461:34735326
5342:(1974).
5109:26876676
5040:Archived
4911:Archived
4850:Archived
4578:Archived
4553:Archived
4522:Archived
4518:26876676
4466:Archived
4432:26876676
4376:Archived
4298:Archived
4235:Archived
4177:Archived
4156:Meeting.
4141:Archived
4028:ABC-Clio
3933:See also
3928:journal)
3869:extranet
3864:intranet
3813:Netscape
3768:Facebook
3746:Typical
3622:criminal
3554:Security
3447:blocking
3361:transmit
3203:printing
3096:Internet
3071:Internet
3064:extranet
3058:Extranet
3051:intranet
3045:Intranet
2812:FireWire
2737:Internet
2710:Backbone
2700:Building
2631:by scale
2608:bridging
2561:(iDEN).
2553:(DECT),
2549:(UMTS),
2545:(EDGE),
2535:CDMA2000
2529:(GPRS),
2492:Ethernet
2448:IEEE 802
2426:Ethernet
2388:IEEE 802
2383:IEEE 802
2214:Ethernet
2116:Repeater
2046:switches
1899:Wireless
1841:Ethernet
1771:infrared
1693:DiffServ
1645:Internet
1538:Ethernet
1471:trailers
1391:created
1361:Internet
1337:Bob Kahn
1302:Ethernet
1264:CYCLADES
1230:Bob Kahn
1042:printers
1022:services
877:Security
757:Software
719:Epidemic
701:Dynamics
615:Topology
588:Distance
525:Weighted
500:Directed
495:Complete
399:Features
360:Semantic
155:a series
153:Part of
8413:Outline
7376:Live CD
7330:Journal
7294:access,
7292:Storage
7169:Process
7075:vkernel
6942:History
6925:General
6855:below (
6605:2204780
5426:1558618
5294:2930578
4822:8172150
3891:(DNS).
3857:subnets
3801:SSL/TLS
3783:clients
3772:Dropbox
3756:servers
3752:clients
3645:privacy
3544:service
3495:CSMA/CA
3445:or the
3323:latency
3270:goodput
3233:), and
3173:sharing
3154:friends
3149:darknet
3143:Darknet
3107:of the
2668:Near-me
2587:direct
2578:Routing
2565:Routing
2531:cdmaOne
2525:(GSM),
2194:Routers
2050:routers
2042:bridges
1810:second.
1701:routers
1689:IntServ
1663:routing
1546:10BASE2
1542:10BASE5
1473:, with
1225:ARPANET
1216:at the
1198:routers
1076:(SAGE)
1052:History
968:servers
949:optical
938:digital
541:Metrics
510:Labeled
380:on-Chip
365:Spatial
274:Closure
110:scholar
41:Network
7184:Thread
7055:Hybrid
7033:Kernel
6872:Curlie
6858:Curlie
6836:, and
6603:
6593:
6451:
6285:"Maps"
6151:
6126:
6065:
6018:
5852:
5842:
5693:
5632:
5608:429216
5606:
5523:
5459:
5424:
5292:
5282:
5239:
5208:
5136:
5114:Walden
5107:
5014:
4905:
4820:
4776:
4743:
4713:
4661:
4622:
4516:
4458:
4430:
4422:
4370:
4326:
4271:
4133:
4100:
4069:
4034:
3770:, and
3748:server
3739:, and
3673:group
3669:. The
3651:, the
3548:faults
3527:
3499:window
3491:802.11
3405:In an
3389:jitter
3223:nm.lan
3199:E-mail
2496:frames
2414:, and
2261:DOCSIS
2229:Modems
2179:frames
2122:signal
2104:octets
1998:
1755:family
1695:, and
1490:queued
1393:ARCNET
1355:
1208:. The
1064:, and
752:Topics
606:Models
563:Degree
520:Random
473:matrix
462:matrix
452:Vertex
407:Clique
389:Graphs
335:Social
192:Theory
112:
105:
98:
91:
83:
7816:Logic
7650:tools
7386:Shell
7325:Inode
6785:from
6684:ZDNet
6658:(PDF)
6651:(PDF)
6601:S2CID
6482:(PDF)
6475:(PDF)
6353:(PDF)
6348:(4).
6338:(PDF)
6105:(PDF)
6098:(PDF)
5881:(PDF)
5874:(PDF)
5604:S2CID
5501:(PDF)
5479:(PDF)
5457:S2CID
5422:S2CID
5384:(PDF)
5377:(PDF)
5290:S2CID
5264:(PDF)
5184:(PDF)
5164:(PDF)
5105:S2CID
5085:(PDF)
5036:(PDF)
4982:(PDF)
4971:(PDF)
4853:(PDF)
4846:(PDF)
4818:S2CID
4668:work.
4525:(PDF)
4514:S2CID
4494:(PDF)
4428:S2CID
4400:(PDF)
4379:(PDF)
4348:(PDF)
4144:(PDF)
4127:(PDF)
3996:Cloud
3789:, or
3741:TETRA
3721:email
3713:HTTPS
3515:ITU-T
3262:bit/s
3162:ports
3105:DARPA
2836:ITU-T
2732:Cloud
2629:types
2488:cells
2412:VLANs
2325:In a
2235:Modem
2183:ports
1963:Wi-Fi
1814:ITU-T
1785:Wired
1086:modem
1078:radar
1034:audio
976:hosts
936:over
738:Lists
568:Motif
515:Multi
505:Hyper
482:Types
422:Cycle
204:Graph
117:JSTOR
103:books
7648:and
7521:Form
7517:Size
6947:List
6766:2547
6696:2013
6591:ISBN
6496:link
6449:ISBN
6428:1035
6394:5321
6312:2009
6149:ISBN
6124:ISBN
6063:ISBN
6016:ISBN
5850:OCLC
5840:ISBN
5691:ISBN
5665:link
5661:link
5630:ISBN
5550:IETF
5521:ISSN
5280:ISBN
5237:ISBN
5206:ISBN
5134:ISBN
5063:UCLA
5012:ISBN
4990:2017
4903:ISSN
4774:ISBN
4741:ISBN
4711:ISBN
4659:ISSN
4620:ISSN
4456:ISBN
4420:ISSN
4368:ISSN
4324:ISBN
4269:ISBN
4131:ISBN
4098:ISBN
4067:ISBN
4032:ISBN
3902:and
3754:and
3735:for
3733:ZRTP
3727:for
3719:for
3704:and
3643:and
3529:2914
3518:G.hn
3481:and
3365:link
3296:and
3288:and
3217:and
3205:and
3193:The
3131:and
3094:The
2928:and
2906:Cat5
2839:G.hn
2818:and
2810:and
2658:Body
2377:IPv6
2367:The
2331:HTTP
2243:are
2210:ADSL
2159:and
2038:hubs
2000:1149
1847:and
1817:G.hn
1661:and
1616:FDDI
1544:and
1469:and
1448:data
1382:X.75
1378:X.25
1335:and
1277:put
1212:, a
1187:for
1179:and
1141:OGAS
1044:and
1032:and
1020:and
447:Path
437:Loop
432:Edge
375:Flow
89:news
7403:PXE
7391:CLI
7371:HAL
7361:API
7164:IPC
6870:at
6763:RFC
6753:doi
6583:doi
6425:RFC
6415:doi
6391:RFC
6381:doi
6316:doi
6207:ITU
6055:doi
6008:doi
5594:doi
5567:675
5564:RFC
5554:doi
5513:doi
5449:doi
5414:doi
5272:doi
5097:doi
4810:doi
4651:doi
4612:doi
4506:doi
4412:doi
4360:doi
3781:of
3725:OTR
3717:PGP
3566:or
3525:RFC
3493:'s
3300:).
3268:or
3260:in
3158:F2F
3087:An
3062:An
3049:An
2992:An
2876:or
2808:USB
2335:TCP
2314:or
2076:ATM
2074:An
1996:RFC
1868:An
1674:map
1634:An
1417:Use
1357:675
1353:RFC
1234:IMP
723:SIR
417:Cut
72:by
8440::
7519:/
7146:,
6823:,
6792:.
6761:.
6751:.
6737:^
6720:.
6716:.
6682:.
6613:^
6599:.
6589:.
6492:}}
6488:{{
6423:.
6413:.
6389:.
6379:.
6346:16
6344:.
6340:.
6310:.
6287:.
6263:.
6238:.
6234:.
6205:.
6201:.
6176:.
6172:.
6071:.
6061:.
6049:.
6024:.
6014:.
6002:.
5951:.
5929:.
5848:.
5826:^
5805:.
5781:,
5777:,
5759:^
5743:.
5713:.
5673:^
5657:}}
5653:{{
5638:.
5602:.
5590:19
5588:.
5584:.
5562:.
5552:.
5548:.
5527:.
5519:.
5509:22
5507:.
5503:.
5481:,
5455:.
5445:47
5443:.
5420:.
5410:21
5408:.
5346:.
5325:.
5315:.
5296:.
5288:.
5278:.
5266:.
5245:.
5214:.
5142:.
5111:.
5103:.
5093:66
5091:.
5087:.
5061:.
4992:.
4973:.
4952:.
4937:.
4920:.
4909:.
4901:.
4897:.
4878:.
4824:.
4816:.
4804:.
4800:.
4788:^
4749:.
4719:.
4688:.
4684:.
4665:.
4657:.
4647:66
4645:.
4641:.
4618:.
4608:12
4606:.
4602:.
4534:.
4520:.
4512:.
4502:66
4500:.
4496:.
4481:^
4464:.
4434:.
4426:.
4418:.
4408:66
4406:.
4402:.
4374:.
4366:.
4356:40
4354:.
4350:.
4292:.
4267:.
4265:13
4233:.
4229:.
4200:.
4175:.
4171:.
4153:.
4139:.
4096:.
4092:.
4061:.
4026:.
3898:,
3774:.
3766:,
3762:,
3731:,
3723:,
3708:.
3574:.
3477:,
3470:.
3441:,
3391:,
3387:,
3371:.
3284:,
3280:,
3276:,
3215:IP
3201:,
3197:,
3164:.
3147:A
3032:.
3024:A
3004:A
2984:.
2968:A
2960:.
2952:A
2919:A
2900:A
2888:A
2868:A
2830:A
2802:A
2789:A
2537:,
2533:,
2406:.
2306:A
2282:.
2140:.
2048:,
2044:,
2040:,
2036:,
2032:,
1742:,
1691:,
1647:.
1461:,
1454:.
1316:,
1200:,
1060:,
1040:,
1028:,
1001:,
990:.
970:,
966:,
959:.
920:A
157:on
7457:.
7437:e
7430:t
7423:v
7240:,
7150:)
7142:(
6910:e
6903:t
6896:v
6768:.
6755::
6731:.
6698:.
6667:.
6635:.
6607:.
6585::
6566:.
6541:.
6498:)
6457:.
6430:.
6417::
6396:.
6383::
6362:.
6322:.
6318::
6273:.
6249:.
6220:.
6187:.
6157:.
6132:.
6082:.
6057::
6035:.
6010::
5988:.
5966:.
5914:.
5856:.
5820:.
5753:.
5728:.
5699:.
5667:)
5649:.
5610:.
5596::
5569:.
5556::
5515::
5463:.
5451::
5428:.
5416::
5393:.
5361:.
5274::
5099::
5020:.
4862:.
4812::
4806:9
4782:.
4653::
4626:.
4614::
4587:.
4562:.
4508::
4475:.
4414::
4362::
4332:.
4307:.
4277:.
4244:.
4215:.
4186:.
4106:.
4075:.
4040:.
3924:(
3156:(
2769:e
2762:t
2755:v
2398:(
1984:.
1965:.
1947:.
1823:(
1578:.
1154:.
909:e
902:t
895:v
801:e
794:t
787:v
721:/
139:)
133:(
128:)
124:(
114:·
107:·
100:·
93:·
66:.
43:.
36:.
20:)
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.