817:, where each byte in a virus is with a constant so that the exclusive-or operation had only to be repeated for decryption. It is suspicious for a code to modify itself, so the code to do the encryption/decryption may be part of the signature in many virus definitions. A simpler older approach did not use a key, where the encryption consisted only of operations with no parameters, like incrementing and decrementing, bitwise rotation, arithmetic negation, and logical NOT. Some viruses, called polymorphic viruses, will employ a means of encryption inside an executable in which the virus is encrypted under certain events, such as the virus scanner being disabled for updates or the computer being
792:. Different antivirus programs will employ different search methods when identifying viruses. If a virus scanner finds such a pattern in a file, it will perform other checks to make sure that it has found the virus, and not merely a coincidental sequence in an innocent file, before it notifies the user that the file is infected. The user can then delete, or (in some cases) "clean" or "heal" the infected file. Some viruses employ techniques that make detection by means of signatures difficult but probably not impossible. These viruses modify their code on each infection. That is, each infected file contains a different variant of the virus.
239:
1058:, ensuring that they would be run when the user booted the computer from the disk, usually inadvertently. Personal computers of the era would attempt to boot first from a floppy if one had been left in the drive. Until floppy disks fell out of use, this was the most successful infection strategy and boot sector viruses were the most common in the "wild" for many years. Traditional computer viruses emerged in the 1980s, driven by the spread of personal computers and the resultant increase in
1178:
864:
the virus. The advantage of using such slow polymorphic code is that it makes it more difficult for antivirus professionals and investigators to obtain representative samples of the virus, because "bait" files that are infected in one run will typically contain identical or similar samples of the virus. This will make it more likely that the detection by the virus scanner will be unreliable, and that some instances of the virus may be able to avoid detection.
5839:
217:". The work of von Neumann was later published as the "Theory of self-reproducing automata". In his essay von Neumann described how a computer program could be designed to reproduce itself. Von Neumann's design for a self-reproducing computer program is considered the world's first computer virus, and he is considered to be the theoretical "father" of computer virology. In 1972, Veith Risak directly building on von Neumann's work on
1513:, or connecting the hard drive to another computer and booting from the second computer's operating system, taking great care not to infect that computer by executing any infected programs on the original drive. The original hard drive can then be reformatted and the OS and all programs installed from original media. Once the system has been restored, precautions must be taken to avoid reinfection from any restored
808:
module, which would (for example) be appended to the end. In this case, a virus scanner cannot directly detect the virus using signatures, but it can still detect the decrypting module, which still makes indirect detection of the virus possible. Since these would be symmetric keys, stored on the infected host, it is entirely possible to decrypt the final virus, but this is probably not required, since
63:
1607:'s character summarizes the problem by stating that "...there's a clear pattern here which suggests an analogy to an infectious disease process, spreading from one...area to the next." To which the replies are stated: "Perhaps there are superficial similarities to disease" and, "I must confess I find it difficult to believe in a disease of machinery."
1425:.com—allow users to upload one or more suspicious files to be scanned and checked by one or more antivirus programs in one operation. Additionally, several capable antivirus software programs are available for free download from the Internet (usually restricted to non-commercial use). Microsoft offers an optional free antivirus utility called
1131:(COM) interface. Some old versions of Microsoft Word allow macros to replicate themselves with additional blank lines. If two macro viruses simultaneously infect a document, the combination of the two, if also self-replicating, can appear as a "mating" of the two and would likely be detected as a virus unique from the "parents".
1007:, packaging tools, etc., which means that malicious code targeting any of these systems will only affect a subset of all users. Many Windows users are running the same set of applications, enabling viruses to rapidly spread among Microsoft Windows systems by targeting the same exploits on large numbers of hosts.
1344:
of known virus "signatures". Virus signatures are just strings of code that are used to identify individual viruses; for each virus, the antivirus designer tries to choose a unique signature string that will not be found in a legitimate program. Different antivirus programs use different "signatures"
984:. The drives may be left in a parking lot of a government building or other target, with the hopes that curious users will insert the drive into a computer. In a 2015 experiment, researchers at the University of Michigan found that 45–98 percent of users would plug in a flash drive of unknown origin.
669:
The most common way of transmission of computer viruses in boot sector is physical media. When reading the VBR of the drive, the infected floppy disk or USB flash drive connected to the computer will transfer data, and then modify or replace the existing boot code. The next time a user tries to start
1537:
dialing capability, randomly dials phone numbers until it hits a modem that is answered by another computer, and then attempts to program the answering computer with its own program, so that the second computer will also begin dialing random numbers, in search of yet another computer to program. The
1142:
to all the contacts (e.g., friends and colleagues' e-mail addresses) stored on an infected machine. If the recipient, thinking the link is from a friend (a trusted source) follows the link to the website, the virus hosted at the site may be able to infect this new computer and continue propagating.
887:
Damage is due to causing system failure, corrupting data, wasting computer resources, increasing maintenance costs or stealing personal information. Even though no antivirus software can uncover all computer viruses (especially new ones), computer security researchers are actively searching for new
863:
Some viruses employ polymorphic code in a way that constrains the mutation rate of the virus significantly. For example, a virus can be programmed to mutate only slightly over time, or it can be programmed to refrain from mutating when it infects a file on a computer that already contains copies of
521:
The virus starts propagating, which is multiplying and replicating itself. The virus places a copy of itself into other programs or into certain system areas on the disk. The copy may not be identical to the propagating version; viruses often "morph" or change to evade detection by IT professionals
1488:
and critical system files to a previous checkpoint. Often a virus will cause a system to "hang" or "freeze", and a subsequent hard reboot will render a system restore point from the same day corrupted. Restore points from previous days should work, provided the virus is not designed to corrupt the
975:
to determine program associations (such as
Microsoft Windows), the extensions may be hidden from the user by default. This makes it possible to create a file that is of a different type than it appears to the user. For example, an executable may be created and named "picture.png.exe", in which the
734:
or by disguising itself within a trusted process. In the 2010s, as computers and operating systems grow larger and more complex, old hiding techniques need to be updated or replaced. Defending a computer against viruses may demand that a file system migrate towards detailed and explicit permission
532:
A dormant virus moves into this phase when it is activated, and will now perform the function for which it was intended. The triggering phase can be caused by a variety of system events, including a count of the number of times that this copy of the virus has made copies of itself. The trigger may
839:
module. In the case of polymorphic viruses, however, this decryption module is also modified on each infection. A well-written polymorphic virus therefore has no parts which remain identical between infections, making it very difficult to detect directly using "signatures". Antivirus software can
1320:
Other commonly used preventive measures include timely operating system updates, software updates, careful
Internet browsing (avoiding shady websites), and installation of only trusted software. Certain browsers flag sites that have been reported to Google and that have been confirmed as hosting
748:
is proprietary. This leaves antivirus software little alternative but to send a "read" request to
Windows files that handle such requests. Some viruses trick antivirus software by intercepting its requests to the operating system. A virus can hide by intercepting the request to read the infected
514:
The virus program is idle during this stage. The virus program has managed to access the target user's computer or software, but during this stage, the virus does not take any action. The virus will eventually be activated by the "trigger" which states which event will execute the virus. Not all
1363:
than using signatures. False positives can be disruptive, especially in a commercial environment, because it may lead to a company instructing staff not to use the company computer system until IT services have checked the system for viruses. This can slow down productivity for regular workers.
807:
which does not change from one infection to the next. In this case, the virus consists of a small decrypting module and an encrypted copy of the virus code. If the virus is encrypted with a different key for each infected file, the only part of the virus that remains constant is the decrypting
485:
The payload is the body of the virus that executes the malicious activity. Examples of malicious activities include damaging files, theft of confidential information or spying on the infected system. Payload activity is sometimes noticeable as it can cause the system to slow down or "freeze".
1508:
copy is one solution—restoring an earlier backup disk "image" is relatively simple to do, usually removes any malware, and may be faster than "disinfecting" the computer—or reinstalling and reconfiguring the operating system and programs from scratch, as described below, then restoring user
1693:" and attempt to hide themselves—the defining characteristic of viruses is that they are self-replicating computer programs that modify other software without user consent by injecting themselves into the said programs, similar to a biological virus which replicates within living cells.
636:. While not opening attachments in e-mails from unknown persons or organizations can help to reduce the likelihood of contracting a virus, in some cases, the virus is designed so that the e-mail appears to be from a reputable organization (e.g., a major bank or credit card company).
1274:(an optional download in the case of Windows XP). Additionally, several capable antivirus software programs are available for free download from the Internet (usually restricted to non-commercial use). Some such free programs are almost as good as commercial competitors. Common
753:
of the actual operating system files that would handle the read request. Thus, an antivirus software attempting to detect the virus will either not be permitted to read the infected file, or, the "read" request will be served with the uninfected version of the same file.
5444:
And there's a clear pattern here which suggests an analogy to an infectious disease process, spreading from one resort area to the next." ... "Perhaps there are superficial similarities to disease." "I must confess I find it difficult to believe in a disease of
1035:, except to install or configure software; as a result, even if a user ran the virus, it could not harm their operating system. The Bliss virus never became widespread, and remains chiefly a research curiosity. Its creator later posted the source code to
911:, rather than maximum power, and a power virus could cause the system to overheat if it does not have logic to stop the processor. This may cause permanent physical damage. Power viruses can be malicious, but are often suites of test software used for
812:
is such a rarity that finding some may be reason enough for virus scanners to at least "flag" the file as suspicious. An old but compact way will be the use of arithmetic operation like addition or subtraction and the use of logical conditions such as
757:
The only reliable method to avoid "stealth" viruses is to boot from a medium that is known to be "clear". Security software can then be used to check the dormant operating system files. Most security software relies on virus signatures, or they employ
1014:
environment without permission, Windows users are generally not prevented from making these changes, meaning that viruses can easily gain control of the entire system on
Windows hosts. This difference has continued partly due to the widespread use of
539:
This is the actual work of the virus, where the "payload" will be released. It can be destructive such as deleting files on disk, crashing the system, or corrupting files or relatively harmless such as popping up humorous or political messages on
1228:, for example). Some antivirus software blocks known malicious websites that attempt to install malware. Antivirus software does not change the underlying capability of hosts to transmit viruses. Users must update their software regularly to
1345:
to identify viruses. The disadvantage of this detection method is that users are only protected from viruses that are detected by signatures in their most recent virus definition update, and not protected from new viruses (see "
445:
A computer virus generally contains three parts: the infection mechanism, which finds and infects new files, the payload, which is the malicious code to execute, and the trigger, which determines when to activate the payload.
1416:
Many websites run by antivirus software companies provide free online virus scanning, with limited "cleaning" facilities (after all, the purpose of the websites is to sell antivirus products and services). Some websites—like
1408:
CD can be used to start the computer if the installed operating systems become unusable. Backups on removable media must be carefully inspected before restoration. The
Gammima virus, for example, propagates via removable
221:, published his article "Selbstreproduzierende Automaten mit minimaler Informationsübertragung" (Self-reproducing automata with minimal information exchange). The article describes a fully functional virus written in
743:
While some kinds of antivirus software employ various techniques to counter stealth mechanisms, once the infection occurs any recourse to "clean" the system is unreliable. In
Microsoft Windows operating systems, the
627:
and embedded into these documents so that when users open the file, the virus code is executed, and can infect the user's computer. This is one of the reasons that it is dangerous to open unexpected or suspicious
681:
is the most commonly used), harvest email addresses from various sources, and may append copies of themselves to all email sent, or may generate email messages containing copies of themselves as attachments.
3830:
1681:
numbers, phone numbers, names, email addresses, passwords, bank information, house addresses, etc.), corrupting data, displaying political, humorous or threatening messages on the user's screen,
1313:
is a deception in which the malicious individual pretends to be a friend, computer security expert, or other benevolent individual, with the goal of convincing the targeted individual to reveal
735:
for every kind of file access. In addition, only a small fraction of known viruses actually cause real incidents, primarily because many viruses remain below the theoretical epidemic threshold.
766:" for Windows OS files, so the security software can identify altered files, and request Windows installation media to replace them with authentic versions. In older versions of Windows, file
343:
professionals do not accept the concept of "benevolent viruses", as any desired function can be implemented without involving a virus (automatic compression, for instance, is available under
936:
Different micro-architectures typically require different machine code to hit their maximum power. Examples of such machine code do not appear to be distributed in CPU reference materials.
1538:
program rapidly spreads exponentially through susceptible computers and can only be countered by a second program called VACCINE. His story was based on an actual computer virus written in
706:
on file changes. Some viruses can infect files without increasing their sizes or damaging the files. They accomplish this by overwriting unused areas of executable files. These are called
1147:
were first reported in 2002, and were academically demonstrated in 2005. There have been multiple instances of the cross-site scripting viruses in the "wild", exploiting websites such as
1661:(BHOs), and other malicious software. The majority of active malware threats are trojan horse programs or computer worms rather than computer viruses. The term computer virus, coined by
1054:, many users regularly exchanged information and programs on floppies. Some viruses spread by infecting programs stored on these disks, while others installed themselves into the disk
323:
wrote his paper "Computer
Viruses – Theory and Experiments". It was the first paper to explicitly call a self-reproducing program a "virus", a term introduced by Cohen's mentor
925:
applications are similar programs which have the same effect as power viruses (high CPU usage) but stay under the user's control. They are used for testing CPUs, for example, when
867:
To avoid being detected by emulation, some viruses rewrite themselves completely each time they are to infect new executables. Viruses that utilize this technique are said to be in
722:
in length, did not add to the size of the file. Some viruses try to avoid detection by killing the tasks associated with antivirus software before it can detect them (for example,
5669:
4102:
1027:". Bliss, however, requires that the user run it explicitly, and it can only infect programs that the user has the access to modify. Unlike Windows users, most Unix users do not
4636:
347:
at the choice of the user). Any virus will by definition make unauthorised changes to a computer, which is undesirable even if no damage is done or intended. The first page of
845:
1496:(improved in Windows 7 and later) can be used to check for, and repair, corrupted system files. Restoring an earlier "clean" (virus-free) copy of the entire partition from a
277:
operating system. Creeper gained access via the ARPANET and copied itself to the remote system where the message, "I'M THE CREEPER. CATCH ME IF YOU CAN!" was displayed. The
5010:
3404:
5287:
1842:
1359:
based on common virus behaviors. This method can detect new viruses for which antivirus security firms have yet to define a "signature", but it also gives rise to more
108:. The virus writes its own code into the host program. When the program runs, the written virus program is executed first, causing infection and damage. By contrast, a
4293:
3808:
549:
Computer viruses infect a variety of different subsystems on their host computers and software. One manner of classifying viruses is to analyze whether they reside in
3756:
1509:
preferences. Reinstalling the operating system is another approach to virus removal. It may be possible to recover copies of essential user data by booting from a
604:(or "non-resident virus"), when executed, scans the disk for targets, infects them, and then exits (i.e. it does not remain in memory after it is done executing).
2665:
1485:
673:
Email viruses are viruses that intentionally, rather than accidentally, use the email system to spread. While virus infected files may be accidentally sent as
97:
into those programs. If this replication succeeds, the affected areas are then said to be "infected" with a computer virus, a metaphor derived from biological
4377:
698:
platform, make sure that the "last modified" date of a host file stays the same when the file is infected by the virus. This approach does not fool antivirus
288:" was the first personal computer virus to appear "in the wild"—that is, outside the single computer or computer lab where it was created. Written in 1981 by
5129:
3114:
4121:
3782:
5344:
5248:
3572:
3028:
2898:
774:
would report that altered system files are authentic, so using file hashes to scan for altered files would not always guarantee finding an infection.
4852:
4243:
4194:
2430:
5154:
3929:
835:
to virus scanners. Just like regular encrypted viruses, a polymorphic virus infects files with an encrypted copy of itself, which is decoded by a
3557:
410:
5537:
4874:
4040:
3612:
2462:
5733:
3172:
1376:
of data (and the operating systems) on different media, that are either kept unconnected to the system (most of the time, as in a hard drive),
944:
As software is often designed with security features to prevent unauthorized use of system resources, many viruses must exploit and manipulate
4076:
4018:
2789:
2317:
312:
virus would be activated, infecting the personal computer and displaying a short poem beginning "Elk Cloner: The program with a personality."
2288:
980:
and most likely is safe, yet when opened, it runs the executable on the client machine. Viruses may be installed on removable media, such as
4434:
1948:
749:
file, handling the request itself, and returning an uninfected version of the file to the antivirus software. The interception can occur by
4610:
4523:
1384:. This way, if data is lost through a virus, one can start again using the backup (which will hopefully be recent). If a backup session on
1340:) and the files stored on fixed or removable drives (hard drives, floppy drives, or USB flash drives), and comparing those files against a
596:, and when the operating system attempts to access the target file or disk sector, the virus code intercepts the request and redirects the
5382:
5266:
5036:
2552:
1305:. Ransomware is a virus that posts a message on the user's screen saying that the screen or system will remain locked or unusable until a
6515:
5087:
4484:
4416:
4362:
4331:
4000:
3873:
3733:
4916:
4595:
4564:
4098:
3907:
3472:
3447:
3386:
3292:
3206:
2530:
2381:
5613:
4502:
3267:
963:
To replicate itself, a virus must be permitted to execute code and write to memory. For this reason, many viruses attach themselves to
4632:
1396:
is closed, it becomes read-only and can no longer be affected by a virus (so long as a virus or infected file was not copied onto the
1290:
is an example of software, free for personal use, that will check a PC for vulnerable out-of-date software, and attempt to update it.
6277:
2351:
486:
Sometimes payloads are non-destructive and their main purpose is to spread a message to as many people as possible. This is called a
4834:
4229:
2415:
1096:
have become common since the mid-1990s. Most of these viruses are written in the scripting languages for
Microsoft programs such as
1547:
971:). If a user attempts to launch an infected program, the virus' code may be executed simultaneously. In operating systems that use
533:
occur when an employee is terminated from their employment or after a set period of time has elapsed, in order to reduce suspicion.
383:
5230:
4943:
3085:
5054:
4985:
4962:
2095:
Yu, Wei; Zhang, Nan; Fu, Xinwen; Zhao, Wei (October 2010). "Self-Disciplinary Worms and
Countermeasures: Modeling and Analysis".
1430:
1259:
210:
3400:
1302:
871:. To enable metamorphism, a "metamorphic engine" is needed. A metamorphic virus is usually very large and complex. For example,
6367:
5404:
5074:
Advanced Data Mining and
Applications: 4th International Conference, ADMA 2008, Chengdu, China, October 8-10, 2008, Proceedings
5006:
1665:
in 1985, is a misnomer. Viruses often perform some type of harmful activity on infected host computers, such as acquisition of
196:
5291:
2619:
6254:
5641:
5518:
5488:
4589:
4558:
4478:
3901:
3005:
2972:
2936:
2524:
2231:
2158:
2071:
2013:
1876:
1832:
1543:
619:
programs to be embedded in documents or emails, so that the programs may be run automatically when the document is opened. A
3804:
5316:
4453:
2839:
1279:
3748:
3695:
1360:
770:
of Windows OS files stored in Windows—to allow file integrity/authenticity to be checked—could be overwritten so that the
6670:
6285:
165:
As of 2013, computer viruses caused billions of dollars' worth of economic damage each year. In response, an industry of
5108:
4285:
2814:
1433:
that is updated as part of the regular Windows update regime, and an older optional anti-malware (malware removal) tool
5726:
4805:
4753:
2648:
888:
ways to enable antivirus solutions to more effectively detect emerging viruses, before they become widely distributed.
142:), desire to send a political message, personal amusement, to demonstrate that a vulnerability exists in software, for
4662:
3532:
Dave Jones. 2001 (December 2001). "Building an e-mail virus detection system for your network. Linux J. 2001, 92, 2-".
1225:
1087:
584:(or simply "resident virus") installs itself as part of the operating system when executed, after which it remains in
6632:
6323:
6217:
5564:
5081:
4410:
4356:
4325:
4244:"Virus Notice: Network Associates' AVERT Discovers First Virus That Can Infect JPEG Files, Assigns Low-Profiled Risk"
4163:
3994:
3967:
3867:
3840:
3727:
3681:
3582:
3466:
3441:
3380:
3353:
3317:
3286:
3261:
3200:
3144:
3061:
2878:
2704:
2662:
2591:
2393:
2269:
2204:
2185:
320:
4385:
3225:
378:, reportedly to deter unauthorized copying of the software they had written. The first virus to specifically target
130:
to initially infect systems and to spread the virus. Viruses use complex anti-detection/stealth strategies to evade
112:
does not need a host program, as it is an independent program or code chunk. Therefore, it is not restricted by the
6013:
4684:
2040:
1894:
1778:
222:
5133:
4142:
Ganesan, Karthik; Jo, Jungho; Bircher, W. Lloyd; Kaseridis, Dimitris; Yu, Zhibin; John, Lizy K. (September 2010).
4117:
3832:
Engineering Information Security: The Application of Systems Engineering Concepts to Achieve Information Assurance
3525:
788:
Most modern antivirus programs try to find virus-patterns inside ordinary programs by scanning them for so-called
6520:
6267:
5554:
3778:
3106:
2721:
1973:
1283:
394:
4148:
Proceedings of the 19th international conference on Parallel architectures and compilation techniques - PACT '10
2488:
1324:
There are two common methods that an antivirus software application uses to detect viruses, as described in the
1086:
for viruses on BBSs. Viruses can increase their chances of spreading to other computers by infecting files on a
6347:
5337:
5244:
1708:
995:
users. The diversity of software systems on a network limits the destructive potential of viruses and malware.
3021:
1325:
6586:
6080:
5719:
5175:
1426:
1255:
267:
182:
120:
677:, email viruses are aware of email system functions. They generally target a specific type of email system (
73:
virus, generally regarded as the first computer virus for the IBM Personal Computer (IBM PC) and compatibles
5584:
5457:
2894:
1713:
1353:
4848:
4247:
4201:
2750:
Gunn, J.B. (June 1984). "Use of virus functions to provide a virtual APL interpreter under user control".
6272:
6193:
5993:
5193:
957:
767:
235:. In his work Kraus postulated that computer programs can behave in a way similar to biological viruses.
42:
3637:
2439:
6685:
6675:
6606:
6249:
6207:
5863:
3921:
1010:
While Linux and Unix in general have always natively prevented normal users from making changes to the
458:
401:. A few years later, in February 1996, Australian hackers from the virus-writing crew VLAD created the
359:
17:
4618:
6690:
6665:
6474:
6110:
5828:
5705:
5529:
5211:
4884:
4047:
3605:
2466:
1783:
1172:
293:
127:
38:
5675:
5442:(film). 201 S. Kinney Road, Tucson, Arizona, USA: Metro-Goldwyn-Mayer. Event occurs at 32 minutes.
3550:
3161:
2307:
1625:. "Malware" encompasses computer viruses along with many other forms of malicious software, such as
262:, in the early 1970s. Creeper was an experimental self-replicating program written by Bob Thomas at
6408:
6398:
6095:
5973:
5868:
5701:
4491:
4072:
4014:
2997:
2785:
1919:
Piqueira, Jose R.C.; de Vasconcelos, Adolfo A.; Gabriel, Carlos E.C.J.; Araujo, Vanessa O. (2008).
1763:
1642:
1461:
1135:
1071:
616:
274:
147:
5480:
2928:
2292:
2150:
1213:, in which they followed the risk of data loss by "the added risk of losing customer confidence."
475:
is activated. This condition may be a particular date, time, presence of another program, size on
6484:
6183:
6135:
5798:
4430:
1920:
1773:
1670:
1599:
made an early mention of the concept of a computer virus, being a central plot theme that causes
1580:
1377:
904:
703:
457:, which locate and infect files on disk. Other viruses infect files as they are run, such as the
5032:
4527:
3959:
2261:
2255:
1525:
The first known description of a self-reproducing program in fiction is in the 1970 short story
915:
and thermal testing of computer components during the design phase of a product, or for product
205:
The first academic work on the theory of self-replicating computer programs was done in 1949 by
6535:
6362:
5451:
5262:
2544:
1758:
1128:
1079:
593:
371:
232:
159:
70:
6469:
5069:
4468:
4400:
4346:
4315:
3984:
3857:
3717:
3456:
3337:
2251:
2223:
2005:
6316:
6224:
5958:
4906:
4579:
4548:
3891:
3537:
3429:
3370:
3309:
3276:
3190:
2870:
2583:
2514:
2376:
1658:
1059:
916:
896:
186:
5596:
5472:
4498:
3251:
2989:
2920:
2215:
2142:
1997:
1328:
article. The first, and by far the most common method of virus detection is using a list of
799:
to encipher (encode) the body of the virus, leaving only the encryption module and a static
588:
from the time the computer is booted up to when it is shut down. Resident viruses overwrite
225:
programming language for a SIEMENS 4004/35 computer system. In 1980, Jürgen Kraus wrote his
6642:
6637:
6596:
6525:
6383:
6244:
6156:
6105:
6050:
5918:
5891:
5873:
5771:
5742:
2177:
1630:
1333:
1291:
1182:
1148:
1144:
1016:
1004:
996:
953:
908:
429:
5838:
4830:
2340:
1164:
238:
8:
6591:
6028:
5803:
5761:
5605:
5473:
4225:
2990:
2921:
2407:
2143:
1690:
1575:
1555:
1533:
which describes a computer program called VIRUS which, when installed on a computer with
1493:
1235:("holes"). Antivirus software also needs to be regularly updated to recognize the latest
912:
809:
783:
771:
731:
715:
472:
374:, created in 1986 and was released in 1987 by Amjad Farooq Alvi and Basit Farooq Alvi in
1689:, or even rendering the computer useless. However, not all viruses carry a destructive "
670:
the desktop, the virus will immediately load and run as part of the master boot record.
6680:
6576:
6413:
6393:
6212:
6140:
6045:
5578:
5226:
4977:
4958:
4939:
4169:
3952:
3687:
3662:
Kephart, J.O.; White, S.R. (1993). "Measuring and modeling computer virus prevalence".
3514:
3077:
2120:
1837:
1452:. An example of a virus that does this is CiaDoor. Many such viruses can be removed by
1217:
1188:
933:
in a poorly written program may cause similar symptoms, if it lasts sufficiently long.
849:
818:
759:
647:
589:
550:
340:
190:
166:
131:
5050:
4708:
956:
strategies that produce large numbers of "bugs" will generally also produce potential
952:
in a system or application software, to spread themselves and infect other computers.
6601:
6555:
6464:
6260:
6018:
5953:
5903:
5850:
5808:
5756:
5637:
5560:
5514:
5484:
5169:
5077:
4775:
4585:
4554:
4474:
4406:
4352:
4321:
4268:
4159:
4143:
3990:
3963:
3897:
3863:
3836:
3723:
3677:
3578:
3518:
3506:
3462:
3437:
3376:
3349:
3342:
3313:
3302:
3282:
3257:
3196:
3140:
3057:
3001:
2968:
2932:
2874:
2863:
2767:
2700:
2587:
2576:
2520:
2389:
2265:
2227:
2216:
2200:
2181:
2154:
2112:
2077:
2067:
2009:
1998:
1940:
1872:
1804:
1753:
1748:
1738:
1718:
1686:
1236:
1229:
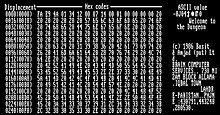
1139:
1125:
1051:
988:
876:
832:
800:
678:
655:
629:
608:
523:
453:
Also called the infection vector, this is how the virus spreads. Some viruses have a
379:
363:
344:
332:
251:
94:
86:
5396:
3665:
Proceedings 1993 IEEE Computer Society Symposium on Research in Security and Privacy
2170:
1807:
in a population decreases the chance of a single disease wiping out a population in
169:
has cropped up, selling or freely distributing virus protection to users of various
6616:
6581:
6309:
6229:
6169:
5933:
5923:
5818:
5592:
4787:
4173:
4151:
3691:
3669:
3498:
2759:
2124:
2104:
1932:
1604:
1595:
1587:
1570:
1565:
1434:
1271:
1224:
or run the executable file (which may be distributed as an email attachment, or on
1105:
1083:
1011:
992:
964:
922:
868:
857:
828:
763:
745:
674:
454:
263:
218:
206:
200:
170:
113:
105:
723:
351:
explains the undesirability of viruses, even those that do nothing but reproduce.
231:
thesis "Selbstreproduktion bei Programmen" (Self-reproduction of programs) at the
6611:
6550:
6454:
6120:
6100:
5998:
5823:
5813:
5664:
5425:
4730:
2669:
2385:
2064:
Computer science and its applications : CSA 2012, Jeju, Korea, 22-25.11.2012
1600:
1534:
1530:
1514:
1346:
1329:
1192:
1101:
1043:
949:
848:
of the encrypted virus body. To enable polymorphic code, the virus has to have a
651:
500:
324:
289:
155:
5312:
4449:
2835:
6571:
6545:
6290:
6188:
6038:
5988:
5928:
5908:
5788:
5776:
4791:
1936:
1733:
1465:
1441:
1332:
definitions. This works by examining the content of the computer's memory (its
1275:
1263:
1247:
Institute publishes evaluations of antivirus software for Windows and Android.
1232:
1097:
1067:
972:
968:
900:
895:
is a computer program that executes specific machine code to reach the maximum
822:
750:
624:
612:
562:
90:
3663:
2810:
405:
virus (also known as "Boza" virus), which was the first known virus to target
6659:
6530:
6449:
6357:
6200:
6161:
6130:
6125:
5978:
5968:
5938:
5660:
5629:
5104:
4809:
3673:
3510:
3491:"Detecting Boot Sector Viruses- Applying TRIZ to Improve Anti-Virus Programs"
2771:
2116:
2081:
1944:
1626:
1560:
1477:
1449:
1267:
1024:
977:
421:
151:
109:
4745:
4155:
471:, this is the part of the virus that determines the condition for which the
59:
Computer program that modifies other programs to replicate itself and spread
6388:
6234:
6090:
5793:
4658:
2312:
2197:
The Little Black Book of Computer Viruses: Volume 1, The Basic Technologies
1497:
1445:
1410:
1385:
1196:
1168:
1120:. Although most of these viruses did not have the ability to send infected
981:
945:
926:
814:
663:
659:
597:
476:
3490:
2763:
2611:
2108:
1220:
that can detect and eliminate known viruses when the computer attempts to
1177:
354:
An article that describes "useful virus functionalities" was published by
6540:
6459:
6174:
6008:
5983:
5948:
5783:
3502:
3221:
1674:
1621:
The term "virus" is also misused by extension to refer to other types of
1381:
1337:
1221:
1109:
1093:
1055:
1047:
643:
570:
391:
387:
367:
331:
that can perfectly detect all possible viruses. Fred Cohen's theoretical
305:
5695:
4688:
4550:
The Definitive Guide to Controlling Malware, Spyware, Phishing, and Spam
4348:
Real World Linux Security: Intrusion Prevention, Detection, and Recovery
2642:
2032:
1886:
1074:
programs, and viruses were written to infect popularly traded software.
1023:. In 1997, researchers created and released a virus for Linux—known as "
907:). Computer cooling apparatus are designed to dissipate power up to the
718:
files. Because those files have many empty gaps, the virus, which was 1
6499:
6479:
6444:
6239:
6055:
6003:
5886:
5766:
5711:
5094:
2408:"Selbstreproduzierende Automaten mit minimaler Informationsübertragung"
1768:
1682:
1678:
1662:
1501:
1473:
1469:
1422:
1020:
976:
user sees only "picture.png" and therefore assumes that this file is a
872:
836:
796:
574:
558:
487:
468:
414:
406:
355:
316:
309:
297:
285:
139:
5570:
2729:
1981:
6489:
6439:
6115:
6070:
6065:
5913:
5881:
5685:
5099:
5097:
4911:
4879:
3171:. Lecture Notes in Computer Science. Vol. 2965. pp. 26–50.
2492:
1728:
1723:
1666:
1646:
1481:
1457:
1356:
1287:
1251:
1117:
1075:
1032:
804:
711:
691:
566:
328:
301:
123:
1258:(for Windows XP, Vista and Windows 7) for real-time protection, the
690:
To avoid detection by users, some viruses employ different kinds of
6075:
6033:
5896:
4709:
Eugene H. Spafford; Kathleen A. Heaphy; David J. Ferbrache (1989).
1918:
1405:
1341:
1314:
1310:
1295:
1042:
Before computer networks became widespread, most viruses spread on
930:
853:
841:
719:
699:
259:
214:
143:
66:
1243:
and other individuals are always creating new viruses. The German
522:
and anti-virus software. Each infected program will now contain a
6494:
6403:
6332:
6301:
6085:
6060:
6023:
5070:"A Novel Immune Based Approach For Detection of Windows PE Virus"
2699:. Aylesbury, Buckinghamshire, U.K.: S & S International PLC.
1808:
1743:
1654:
1650:
1634:
1622:
1616:
1539:
1510:
1453:
1244:
1185:
727:
504:
402:
398:
336:
327:. In 1987, Fred Cohen published a demonstration that there is no
255:
82:
3159:
600:
to the replication module, infecting the target. In contrast, a
6434:
6429:
5943:
5858:
5679:
4714:
1703:
1638:
1590:
1505:
1418:
1373:
1306:
1240:
1204:
1152:
1113:
1070:–driven software sharing contributed directly to the spread of
1036:
633:
417:(it was also able to infect Windows 3.0 and Windows 9x hosts).
375:
270:
243:
227:
135:
5189:
3749:"Netflix Is Dumping Anti-Virus, Presages Death Of An Industry"
1673:(CPU) time, accessing and stealing private information (e.g.,
339:), but was putatively benevolent (well-intentioned). However,
62:
4978:"Secunia Personal Software Inspector 3.0 Review & Rating"
4038:
3192:
Computer System Security: Basic Concepts and Solved Exercises
2811:"Amjad Farooq Alvi Inventor of first PC Virus post by Zagham"
2694:
2573:
1489:
restore files and does not exist in previous restore points.
1437:
that has been upgraded to an antivirus product in Windows 8.
1380:
or not accessible for other reasons, such as using different
1121:
1063:
1028:
1000:
425:
386:
was discovered in April 1992, two years after the release of
358:
under the title "Use of virus functions to provide a virtual
98:
1372:
One may reduce the damage done by viruses by making regular
409:. In late 1997 the encrypted, memory-resident stealth virus
335:
was an example of a virus which was not malicious software (
246:
virus 'Universal Peace', as displayed on a Mac in March 1988
116:, but can run independently and actively carry out attacks.
5634:
Digital Contagions. A Media Archaeology of Computer Viruses
5559:. Tucson, Arizona 85717: American Eagle Publications, Inc.
4466:
3922:"What is a polymorphic virus? - Definition from WhatIs.com"
2615:
2516:
Digital Contagions: A Media Archaeology of Computer Viruses
2486:
2033:"Worm vs. Virus: What's the Difference and Does It Matter?"
1887:"Worm vs. Virus: What's the Difference and Does It Matter?"
1298:
795:
One method of evading signature detection is to use simple
554:
5690:
5207:
4541:
4433:(Press release). McAfee, via Axel Boldt. 5 February 1997.
526:
of the virus, which will itself enter a propagation phase.
85:
that, when executed, replicates itself by modifying other
5609:
5305:
4141:
4073:"Virus Bulletin : Glossary — Metamorphic virus"
4015:"Virus Bulletin : Glossary – Polymorphic virus"
1401:
1393:
695:
585:
424:
were affected by viruses. The first one to appear on the
5157:. GrnLight.net. Archived from the original on 2014-05-24
4553:. Realtimepublishers.com. 1 January 2005. pp. 48–.
4195:"Thermal Performance Challenges from Silicon to Systems"
4039:
Perriot, Fredrick; Peter Ferrie; Peter Szor (May 2002).
2897:. Virus Test Center, University of Hamburg. 1990-06-05.
1546:
computer in the 1960s, as a proof-of-concept, and which
503:
of the computer virus, described by using an analogy to
3169:
Performance Tools and Applications to Networked Systems
3014:
2958:
2956:
2954:
2952:
2950:
2948:
2378:
Computer viruses: from theory to applications, Volume 1
1397:
1389:
4099:"The contemporary antivirus industry and its problems"
3139:. Upper Saddle River, NJ: Addison-Wesley. p. 43.
1090:
or a file system that is accessed by other computers.
879:
code, 90% of which is part of the metamorphic engine.
623:(or "document virus") is a virus that is written in a
5691:
US Govt CERT (Computer Emergency Readiness Team) site
5385:"afterthoughts" to "The Scarred Man", Gregory Benford
4831:"Detailed test reports — Android mobile devices"
2097:
IEEE Transactions on Parallel and Distributed Systems
762:. Security software may also use a database of file "
3577:(3rd ed.). Boca Raton: CRC Press. p. 874.
3167:. In Calzarossa, Maria Carla; Gelenbe, Erol (eds.).
2945:
987:
The vast majority of viruses target systems running
702:, however, especially those which maintain and date
5330:
3885:
3883:
3344:
Malicious Mobile Code: Virus Protection for Windows
3304:
Malicious Mobile Code: Virus Protection for Windows
3253:
Antivirus Tools and Techniques for Computer Systems
3219:
2865:
Malicious Mobile Code: Virus Protection for Windows
991:. This is due to Microsoft's large market share of
507:. This life cycle can be divided into four phases:
362:interpreter under user control" in 1984. The first
134:. Motives for creating viruses can include seeking
4776:"Capital market reaction to defective IT products"
4473:. Jones & Bartlett Publishers. pp. 360–.
4467:David Kim; Michael G. Solomon (17 November 2010).
3951:
3341:
3301:
3045:
2862:
2575:
2169:
1553:The idea was explored further in two 1972 novels,
1460:" with networking, and then using system tools or
1367:
860:for technical detail on how such engines operate.
479:exceeding a threshold, or opening a specific file.
213:about the "Theory and Organization of Complicated
5464:
4096:
3606:"Computer Virus Strategies and Detection Methods"
2981:
413:was released—the first known virus that targeted
6657:
5696:'Computer Viruses – Theory and Experiments'
5527:
5368:Benford, Gregory (May 1970). "The Scarred Man".
4375:
4115:
3949:
3880:
3531:
3249:
2965:Computer security : principles and practice
2912:
2283:
2281:
1869:Computer security : principles and practice
1124:, those viruses which did take advantage of the
5556:Computer Viruses, Artificial Life and Evolution
4526:. Actlab.utexas.edu. 1996-03-31. Archived from
3797:
3427:
3182:
2612:"School prank starts 25 years of security woes"
2412:Zeitschrift für Maschinenbau und Elektrotechnik
2199:. American Eagle Publications. pp. 16–17.
2194:
1254:and anti-malware software include the optional
1112:. Since Word and Excel were also available for
5698: – The original paper by Fred Cohen, 1984
4460:
4269:"Users Really Do Plug in USB Drives They Find"
3719:The Art of Computer Virus Research and Defense
3638:"What is Rootkit – Definition and Explanation"
3570:
3436:. Prentice Hall Professional. pp. 37–38.
3274:
3220:Brain, Marshall; Fenton, Wesley (April 2000).
3188:
3137:The art of computer virus research and defense
3128:
2644:Computer Viruses – Theory and Experiments
2609:
2512:
2249:
2061:
856:engine") somewhere in its encrypted body. See
726:). A Virus may also hide its presence using a
6317:
5727:
5288:"W32.Gammima.AG Removal — Removing Help"
4608:
4398:
4313:
3335:
3299:
2860:
2713:
2278:
2167:
2145:Computer viruses: from theory to applications
2094:
1573:, and became a major theme of the 1975 novel
1039:, allowing researchers to see how it worked.
967:that may be part of legitimate programs (see
840:detect it by decrypting the viruses using an
831:was the first technique that posed a serious
5636:. Digital Formations. New York: Peter Lang.
4656:
4577:
4470:Fundamentals of Information Systems Security
4307:
3982:
3862:. Addison-Wesley Professional. p. 620.
3855:
3661:
3368:
2719:
2545:"The Creeper Worm, the First Computer Virus"
2213:
2140:
1995:
1971:
1825:
1352:A second method to find viruses is to use a
730:by not showing itself on the list of system
266:in 1971. Creeper used the ARPANET to infect
5051:"Report malicious software (URL) to Google"
4806:"Detailed test reports—(Windows) home user"
4351:. Prentice Hall Professional. p. 365.
4317:Linux: Security, Audit and Control Features
3889:
3160:Serazzi, Giuseppe; Zanero, Stefano (2004).
2338:
1303:Internet Crime Complaint Center noticeboard
23:
6324:
6310:
5734:
5720:
5479:. Show Low, Ariz: American Eagle. p.
5007:"10 Step Guide to Protect Against Viruses"
4633:"Facebook 'photo virus' spreads via email"
4369:
4344:
4338:
3195:. EPFL Press / CRC Press. pp. 21–22.
2996:. Show Low, Ariz: American Eagle. p.
2927:. Show Low, Ariz: American Eagle. p.
2250:Bell, David J.; et al., eds. (2004).
1444:and other important Windows tools such as
1270:", the second Tuesday of each month), and
738:
544:
24:
6278:Security information and event management
5372:. Vol. 4, no. 2. pp. 122–.
5190:"VirusTotal.com (a subsidiary of Google)"
5072:. In Tang, Changjie; et al. (eds.).
5067:
4956:
4937:
4571:
3986:Reversing: Secrets of Reverse Engineering
3454:
2962:
2655:
2455:
1866:
1173:Browser security § Browser hardening
150:, or simply because they wish to explore
5741:
5475:The giant black book of computer viruses
4728:"Ka-Boom: Anatomy of a Computer Virus".
4118:"Breeding power-viruses for ARM devices"
3746:
3556:CS1 maint: numeric names: authors list (
3256:. William Andrew (Elsevier). p. 4.
2992:The giant black book of computer viruses
2923:The giant black book of computer viruses
2695:Alan Solomon; Dmitry O Gryaznov (1995).
2605:
2603:
2574:Russell, Deborah; Gangemi, G.T. (1991).
1542:that Benford had created and run on the
1176:
1003:allow users to choose from a variety of
237:
61:
32:This is an accepted version of this page
5628:
5367:
4682:
4378:"Why Linux Is More Secure Than Windows"
4097:Kaspersky, Eugene (November 21, 2005).
3722:. Boston: Addison-Wesley. p. 285.
3056:. Hoboken, NJ: Wiley Pub. p. 210.
3051:
2350:. University of Illinois Press: 66–87.
1431:Windows Malicious Software Removal Tool
1301:alerts appear as press releases on the
1260:Windows Malicious Software Removal Tool
1165:Malware § Vulnerability to malware
1019:accounts in contemporary versions like
577:(or some combination of all of these).
432:, which was detected in November 1987.
281:program was created to delete Creeper.
14:
6658:
6368:Timeline of computer viruses and worms
5552:
5508:
5470:
5438:Michael Crichton (November 21, 1973).
5290:. Symantec. 2007-08-27. Archived from
4456:from the original on 14 December 2005.
4437:from the original on 17 December 2005.
3989:. John Wiley & Sons. p. 216.
3828:
3759:from the original on September 6, 2015
3488:
2987:
2918:
2487:Thomas Chen; Jean-Marc Robert (2004).
2320:from the original on September 7, 2015
1833:"The Internet comes down with a virus"
1404:). Likewise, an operating system on a
960:"holes" or "entrances" for the virus.
694:. Some old viruses, especially on the
197:Timeline of computer viruses and worms
6305:
6255:Host-based intrusion detection system
5715:
5616:from the original on 4 September 2016
5540:from the original on 7 September 2015
5407:from the original on 17 December 2018
5224:
5105:"Good Security Habits | US-CERT"
4975:
4773:
4611:"Macro Virus Identification Problems"
4447:
4105:from the original on October 5, 2013.
3461:. Sams Publishing. pp. 331–333.
2758:(4). ACM New York, NY, USA: 163–168.
2640:
2622:from the original on 20 December 2014
2600:
2428:
2405:
2341:"Theory of Self-Reproducing Automata"
2305:
1921:"Dynamic models for computer viruses"
104:Computer viruses generally require a
5511:Computer Viruses and Data Protection
4431:"McAfee discovers first Linux virus"
3715:
3618:from the original on 23 October 2013
3134:
2749:
2683:Computer Viruses and Data Protection
2519:. New York: Peter Lang. p. 50.
2489:"The Evolution of Viruses and Worms"
2025:
939:
777:
304:3.3 operating system and spread via
6286:Runtime application self-protection
5528:Granneman, Scott (6 October 2003).
5401:The Encyclopedia of Science Fiction
4957:Rubenking, Neil J. (Jan 10, 2013).
4938:Rubenking, Neil J. (Feb 17, 2012).
4584:. Informing Science. pp. 27–.
4567:from the original on 16 March 2017.
4499:"1980s – Kaspersky IT Encyclopedia"
4487:from the original on 16 March 2017.
4399:Raggi, Emilio; et al. (2011).
4314:Mookhey, K.K.; et al. (2005).
3910:from the original on 16 March 2017.
3162:"Computer Virus Propagation Models"
2788:. Antivirus.about.com. 2010-06-10.
2610:Anick Jesdanun (1 September 2007).
2168:Harley, David; et al. (2001).
1845:from the original on April 11, 2020
852:(also called "mutating engine" or "
56:
6331:
5837:
5702:Hacking Away at the Counterculture
5509:Burger, Ralf (16 February 2010) .
5501:
5227:"The Best Free Antivirus for 2014"
4940:"The Best Free Antivirus for 2012"
4919:from the original on June 22, 2012
4855:from the original on June 21, 2012
3954:Guide to Computer Network Security
3859:Computer Security: Art and Science
3430:"Infection mechanisms and targets"
2842:from the original on 8 August 2016
2357:from the original on June 13, 2010
2043:from the original on 15 March 2021
1897:from the original on 15 March 2021
1520:
1158:
875:consisted of over 14,000 lines of
607:Many common applications, such as
126:and exploit detailed knowledge of
57:
6702:
6633:Computer and network surveillance
6218:Security-focused operating system
5652:
5394:
4875:"Malicious Software Removal Tool"
4711:Dealing With Electronic Vandalism
4581:Navigating Information Challenges
3890:John Aycock (19 September 2006).
3785:from the original on July 7, 2015
3228:from the original on 29 June 2013
2752:ACM SIGAPL APL Quote Quad Archive
2432:Selbstreproduktion bei Programmen
1211:Dealing With Electronic Vandalism
321:University of Southern California
6014:Insecure direct object reference
5431:
5419:
5388:
5376:
5361:
5280:
5255:
5251:from the original on 2013-06-29.
5237:
5233:from the original on 2017-08-30.
5218:
5214:from the original on 2013-01-26.
5200:
5196:from the original on 2012-06-16.
5182:
5147:
5122:
5090:from the original on 2017-03-16.
5061:
5057:from the original on 2014-09-12.
5043:
5039:from the original on 2014-09-14.
5025:
5013:from the original on 24 May 2014
4999:
4969:
4965:from the original on 2016-04-25.
4950:
4946:from the original on 2017-08-30.
4931:
4899:
4837:from the original on 2013-04-07.
4685:"The Cross-site Scripting Virus"
4598:from the original on 2017-12-19.
4419:from the original on 2017-03-16.
4376:Noyes, Katherine (Aug 3, 2010).
4365:from the original on 2016-12-01.
4334:from the original on 2016-12-01.
4232:from the original on 2013-10-03.
4144:"System-level max power (SYMPO)"
4003:from the original on 2017-03-16.
3876:from the original on 2017-03-16.
3736:from the original on 2017-03-16.
3475:from the original on 2014-07-06.
3450:from the original on 2017-03-16.
3434:Malware: Fighting Malicious Code
3389:from the original on 2017-03-16.
3295:from the original on 2017-03-16.
3278:Foundations of Computer Security
3270:from the original on 2017-03-16.
3209:from the original on 2017-03-16.
3178:from the original on 2013-08-18.
2967:. Boston: Pearson. p. 183.
2697:Dr. Solomon's Virus Encyclopedia
2555:from the original on 28 May 2022
2533:from the original on 2017-03-16.
1871:. Boston: Pearson. p. 182.
1779:Windows Security and Maintenance
1610:
1456:the computer, entering Windows "
390:. The virus did not contain any
349:Dr Solomon's Virus Encyclopaedia
6268:Information security management
5350:from the original on 2016-04-19
5319:from the original on 2016-04-07
5269:from the original on 2015-01-31
5111:from the original on 2016-04-20
5068:Zhang, Yu; et al. (2008).
4988:from the original on 2013-01-16
4867:
4849:"Microsoft Security Essentials"
4841:
4823:
4798:
4767:
4756:from the original on 2021-04-18
4738:
4734:. December 3, 1990. p. 60.
4721:
4702:
4687:. bindshell.net. Archived from
4676:
4665:from the original on 2014-07-04
4659:"XSS bug in hotmail login page"
4650:
4639:from the original on 2014-05-29
4625:
4602:
4516:
4505:from the original on 2021-04-18
4448:Boldt, Axel (19 January 2000).
4441:
4423:
4392:
4296:from the original on 2015-05-12
4286:"Operating system market share"
4278:
4261:
4236:
4218:
4187:
4135:
4124:from the original on 2024-03-24
4116:Norinder, Ludvig (2013-12-03).
4109:
4090:
4079:from the original on 2010-07-22
4065:
4032:
4021:from the original on 2010-10-01
4007:
3976:
3943:
3932:from the original on 2018-04-08
3914:
3849:
3822:
3811:from the original on 2016-04-25
3779:"How Anti-Virus Software Works"
3771:
3740:
3709:
3698:from the original on 2023-02-09
3655:
3630:
3598:
3564:
3482:
3418:
3407:from the original on 2015-11-18
3393:
3362:
3329:
3240:
3213:
3153:
3117:from the original on 2023-09-30
3099:
3088:from the original on 2023-12-06
3070:
3034:from the original on 2016-05-09
2901:from the original on 2012-02-08
2887:
2854:
2828:
2817:from the original on 2013-07-06
2803:
2792:from the original on 2011-01-12
2778:
2743:
2688:
2675:
2651:from the original on 2007-02-18
2634:
2567:
2537:
2506:
2480:
2429:Kraus, Jürgen (February 1980),
2422:
2418:from the original on 2010-10-05
2399:
2369:
2332:
2299:
1951:from the original on 2022-12-28
1797:
1368:Recovery strategies and methods
1317:or other personal information.
1284:National Vulnerability Database
428:was a boot sector virus called
6348:Comparison of computer viruses
5428:. Retrieved November 28, 2015.
3574:Instrument engineers' handbook
3107:"What is a malicious payload?"
2663:An Undetectable Computer Virus
2388:, Birkhäuser, 2005, pp. 19–38
2257:Cyberculture: The Key Concepts
2243:
2131:
2088:
2055:
1962:
1912:
1857:
1709:Comparison of computer viruses
1250:Examples of Microsoft Windows
714:, or Chernobyl Virus, infects
658:, or removable storage media (
13:
1:
6587:Data loss prevention software
4959:"The Best Antivirus for 2013"
4808:. AV-Test.org. Archived from
3829:Jacobs, Stuart (2015-12-01).
1818:
1427:Microsoft Security Essentials
1256:Microsoft Security Essentials
1082:software were equally common
183:History of antivirus software
4615:FRISK Software International
4017:. Virusbtn.com. 2009-10-01.
3896:. Springer. pp. 35–36.
3893:Computer Viruses and Malware
3571:Béla G. Lipták, ed. (2002).
3401:"What is boot sector virus?"
3372:Computer Viruses and Malware
3281:. Springer. pp. 47–48.
3054:Computer viruses for dummies
2218:Computer Viruses and Malware
2000:Computer Viruses and Malware
1714:Computer fraud and abuse act
1239:. This is because malicious
1116:, most could also spread to
846:statistical pattern analysis
768:cryptographic hash functions
685:
300:, it attached itself to the
7:
6273:Information risk management
6194:Multi-factor authentication
5750:Related security categories
5612:)). Microsoft Corporation.
5530:"Linux vs. Windows Viruses"
4833:. AV-Test.org. 2019-10-22.
4774:Hovav, Anat (August 2005).
4717:Software Industry Division.
4524:"What is a Computer Virus?"
3222:"How Computer Viruses Work"
2963:Stallings, William (2012).
2720:Alan Solomon (2011-06-14).
2348:Essays on Cellular Automata
2308:"Linux vs. Windows Viruses"
2289:"Viruses that can cost you"
1972:Alan Solomon (2011-06-14).
1867:Stallings, William (2012).
1696:
1108:by infecting documents and
1066:use, and software sharing.
1050:. In the early days of the
284:In 1982, a program called "
10:
6707:
6671:Computer security exploits
6607:Intrusion detection system
6250:Intrusion detection system
6208:Computer security software
5864:Advanced persistent threat
5598:Advanced Malware Cleaning
5426:IMDB synopsis of Westworld
5403:. Orion Publishing Group.
5245:"Microsoft Safety Scanner"
5132:. Symantec. Archived from
4792:10.1016/j.cose.2005.02.003
3082:encyclopedia.kaspersky.com
2786:"Boot sector virus repair"
2339:von Neumann, John (1966).
1937:10.1016/j.cose.2008.07.006
1614:
1548:he told John Brunner about
1264:Windows (Security) Updates
1207:Software Industry Division
1162:
1143:Viruses that spread using
999:operating systems such as
882:
781:
366:virus in the "wild" was a
194:
180:
176:
6625:
6564:
6508:
6475:Privacy-invasive software
6422:
6376:
6340:
6149:
5849:
5835:
5829:Digital rights management
5749:
5708: (On hacking, 1990)
5686:Microsoft Security Portal
5174:: CS1 maint: unfit URL (
5076:. Springer. p. 250.
3950:Kizza, Joseph M. (2009).
3835:. John Wiley & Sons.
3250:Polk, William T. (1995).
2066:. Springer. p. 515.
1803:This is analogous to how
1784:Zombie (computer science)
1151:(with the Samy worm) and
602:non-memory-resident virus
494:
435:
294:Mount Lebanon High School
209:who gave lectures at the
5974:Denial-of-service attack
5869:Arbitrary code execution
5583:: CS1 maint: location (
5456:: CS1 maint: location (
4450:"Bliss, a Linux 'virus'"
3674:10.1109/RISP.1993.287647
3489:Mishra, Umakant (2012).
3428:Skoudis, Edward (2004).
3375:. Springer. p. 89.
3022:"Basic malware concepts"
2578:Computer Security Basics
2195:Ludwig, Mark A. (1996).
2039:. Avast Software s.r.o.
1925:Computers & Security
1893:. Avast Software s.r.o.
1790:
1764:Trojan horse (computing)
1687:logging their keystrokes
1462:Microsoft Safety Scanner
1276:security vulnerabilities
1233:security vulnerabilities
1134:A virus may also send a
1031:as an administrator, or
905:central processing units
704:cyclic redundancy checks
642:specifically target the
515:viruses have this stage.
440:
258:, the forerunner of the
128:security vulnerabilities
39:latest accepted revision
6485:Rogue security software
6184:Computer access control
6136:Rogue security software
5799:Electromagnetic warfare
5670:considered for deletion
5513:. Abacus. p. 353.
5370:Venture Science Fiction
5313:"support.microsoft.com"
4405:. Apress. p. 148.
4156:10.1145/1854273.1854282
4041:"Striking Similarities"
3781:. Stanford University.
3495:SSRN Electronic Journal
3275:Salomon, David (2006).
3189:Avoine, Gildas (2007).
3052:Gregory, Peter (2004).
2513:Parikka, Jussi (2007).
2176:. McGraw-Hill. p.
2062:Yeo, Sang-Soo. (2012).
1774:Windows 7 File Recovery
1685:their e-mail contacts,
1671:central processing unit
739:Read request intercepts
561:), data files (such as
545:Targets and replication
160:evolutionary algorithms
6521:Classic Mac OS viruses
6363:List of computer worms
6230:Obfuscation (software)
5959:Browser Helper Objects
5843:
5033:"Google Safe Browsing"
4780:Computers and Security
4402:Beginning Ubuntu Linux
4320:. ISACA. p. 128.
3747:Fox-Brewster, Thomas.
3545:Cite journal requires
3336:Grimes, Roger (2001).
3300:Grimes, Roger (2001).
2861:Grimes, Roger (2001).
2549:History of information
1759:Technical support scam
1199:
1129:Component Object Model
1104:and spread throughout
308:. On its 50th use the
273:computers running the
254:was first detected on
247:
233:University of Dortmund
211:University of Illinois
74:
6225:Data-centric security
6106:Remote access trojans
5841:
5553:Ludwig, Mark (1993).
5471:Ludwig, Mark (1998).
5263:"Virus removal -Help"
5155:"Viruses! In! Space!"
4578:Eli B. Cohen (2011).
4053:on September 27, 2007
3983:Eilam, Eldad (2011).
3856:Bishop, Matt (2003).
3369:Aycock, John (2006).
3308:. O'Reilly. pp.
3224:. HowStuffWorks.com.
2988:Ludwig, Mark (1998).
2919:Ludwig, Mark (1998).
2869:. O'Reilly. pp.
2764:10.1145/384283.801093
2681:Burger, Ralph, 1991.
2406:Risak, Veith (1972),
2260:. Routledge. p.
2214:Aycock, John (2006).
2141:Filiol, Eric (2005).
2109:10.1109/tpds.2009.161
1996:Aycock, John (2006).
1659:Browser Helper Object
1440:Some viruses disable
1282:and listed in the US
1180:
1060:bulletin board system
897:CPU power dissipation
582:memory-resident virus
397:, instead relying on
241:
195:Further information:
187:History of ransomware
65:
6643:Operation: Bot Roast
6157:Application security
6051:Privilege escalation
5919:Cross-site scripting
5772:Cybersex trafficking
5743:Information security
3958:. Springer. p.
3716:Szor, Peter (2005).
3503:10.2139/ssrn.1981886
3135:Szor, Peter (2005).
3027:. cs.colostate.edu.
2641:Cohen, Fred (1984),
2582:. O'Reilly. p.
2222:. Springer. p.
2149:. Springer. p.
2004:. Springer. p.
1334:Random Access Memory
1145:cross-site scripting
1005:desktop environments
954:Software development
909:thermal design power
650:(MBR) of the host's
499:Virus phases is the
292:, a ninth grader at
6592:Defensive computing
6509:By operating system
5804:Information warfare
5762:Automotive security
5225:Rubenking, Neil J.
4976:Rubenking, Neil J.
4609:Vesselin Bontchev.
4345:Toxen, Bob (2003).
2722:"All About Viruses"
1974:"All About Viruses"
1576:The Shockwave Rider
1556:When HARLIE Was One
1494:System File Checker
1321:malware by Google.
1262:(now included with
1216:Many users install
1118:Macintosh computers
1088:network file system
913:integration testing
810:self-modifying code
784:Self-modifying code
772:System File Checker
716:Portable Executable
710:. For example, the
640:Boot sector viruses
459:Jerusalem DOS virus
450:Infection mechanism
29:Page version status
6577:Antivirus software
6423:Malware for profit
6394:Man-in-the-browser
6341:Infectious malware
6213:Antivirus software
6081:Social engineering
6046:Polymorphic engine
5999:Fraudulent dialers
5904:Hardware backdoors
5844:
4907:"Windows Defender"
4657:Berend-Jan Wever.
4290:netmarketshare.com
3455:Anonymous (2003).
2668:2014-05-25 at the
2384:2017-01-14 at the
2306:Granneman, Scott.
1841:. August 6, 2014.
1838:The New York Times
1326:antivirus software
1218:antivirus software
1200:
1189:antivirus software
1181:Screenshot of the
850:polymorphic engine
648:Master Boot Record
590:interrupt handling
551:binary executables
248:
191:History of malware
167:antivirus software
132:antivirus software
121:social engineering
119:Virus writers use
75:
35:
6686:Security breaches
6676:Internet security
6651:
6650:
6602:Internet security
6556:HyperCard viruses
6465:Keystroke logging
6455:Fraudulent dialer
6399:Man-in-the-middle
6299:
6298:
6261:Anomaly detection
6166:Secure by default
6019:Keystroke loggers
5954:Drive-by download
5842:vectorial version
5809:Internet security
5757:Computer security
5643:978-0-8204-8837-0
5595:(November 2006).
5520:978-1-55755-123-8
5490:978-0-929408-23-1
5338:"www.us-cert.gov"
4591:978-1-932886-47-4
4560:978-1-931491-44-0
4480:978-1-4496-7164-8
3903:978-0-387-34188-0
3668:. pp. 2–15.
3642:www.kaspersky.com
3007:978-0-929408-23-1
2974:978-0-13-277506-9
2938:978-0-929408-23-1
2526:978-0-8204-8837-0
2233:978-0-387-30236-2
2160:978-2-287-23939-7
2103:(10): 1501–1514.
2073:978-94-007-5699-1
2015:978-0-387-30236-2
1878:978-0-13-277506-9
1805:genetic diversity
1754:Spam (electronic)
1749:Source code virus
1739:Keystroke logging
1719:Computer security
1309:payment is made.
1126:Microsoft Outlook
1052:personal computer
989:Microsoft Windows
940:Infection vectors
877:assembly language
821:. This is called
801:cryptographic key
778:Self-modification
679:Microsoft Outlook
675:email attachments
656:solid-state drive
609:Microsoft Outlook
518:Propagation phase
380:Microsoft Windows
364:IBM PC compatible
333:compression virus
171:operating systems
148:denial of service
87:computer programs
47:17 September 2024
26:
16:(Redirected from
6698:
6691:Types of malware
6666:Computer viruses
6617:Network security
6582:Browser security
6326:
6319:
6312:
6303:
6302:
6170:Secure by design
6101:Hardware Trojans
5934:History sniffing
5924:Cross-site leaks
5819:Network security
5736:
5729:
5722:
5713:
5712:
5673:
5647:
5625:
5623:
5621:
5593:Mark Russinovich
5588:
5582:
5574:
5573:on July 4, 2008.
5569:. Archived from
5549:
5547:
5545:
5524:
5495:
5494:
5478:
5468:
5462:
5461:
5455:
5447:
5435:
5429:
5423:
5417:
5416:
5414:
5412:
5392:
5386:
5380:
5374:
5373:
5365:
5359:
5358:
5356:
5355:
5349:
5342:
5334:
5328:
5327:
5325:
5324:
5309:
5303:
5302:
5300:
5299:
5284:
5278:
5277:
5275:
5274:
5259:
5253:
5252:
5241:
5235:
5234:
5222:
5216:
5215:
5204:
5198:
5197:
5186:
5180:
5179:
5173:
5165:
5163:
5162:
5151:
5145:
5144:
5142:
5141:
5130:"W32.Gammima.AG"
5126:
5120:
5119:
5117:
5116:
5101:
5092:
5091:
5065:
5059:
5058:
5047:
5041:
5040:
5029:
5023:
5022:
5020:
5018:
5009:. GrnLight.net.
5003:
4997:
4996:
4994:
4993:
4973:
4967:
4966:
4954:
4948:
4947:
4935:
4929:
4928:
4926:
4924:
4903:
4897:
4896:
4894:
4892:
4887:on June 21, 2012
4883:. Archived from
4871:
4865:
4864:
4862:
4860:
4845:
4839:
4838:
4827:
4821:
4820:
4818:
4817:
4802:
4796:
4795:
4771:
4765:
4764:
4762:
4761:
4750:trove.nla.gov.au
4742:
4736:
4735:
4725:
4719:
4718:
4706:
4700:
4699:
4697:
4696:
4680:
4674:
4673:
4671:
4670:
4654:
4648:
4647:
4645:
4644:
4629:
4623:
4622:
4617:. Archived from
4606:
4600:
4599:
4575:
4569:
4568:
4545:
4539:
4538:
4536:
4535:
4520:
4514:
4513:
4511:
4510:
4495:
4489:
4488:
4464:
4458:
4457:
4445:
4439:
4438:
4427:
4421:
4420:
4396:
4390:
4389:
4384:. Archived from
4373:
4367:
4366:
4342:
4336:
4335:
4311:
4305:
4304:
4302:
4301:
4282:
4276:
4275:
4273:
4265:
4259:
4258:
4256:
4255:
4246:. Archived from
4240:
4234:
4233:
4222:
4216:
4215:
4213:
4212:
4206:
4200:. Archived from
4199:
4191:
4185:
4184:
4182:
4180:
4139:
4133:
4132:
4130:
4129:
4113:
4107:
4106:
4094:
4088:
4087:
4085:
4084:
4075:. Virusbtn.com.
4069:
4063:
4062:
4060:
4058:
4052:
4046:. Archived from
4045:
4036:
4030:
4029:
4027:
4026:
4011:
4005:
4004:
3980:
3974:
3973:
3957:
3947:
3941:
3940:
3938:
3937:
3918:
3912:
3911:
3887:
3878:
3877:
3853:
3847:
3846:
3826:
3820:
3819:
3817:
3816:
3801:
3795:
3794:
3792:
3790:
3775:
3769:
3768:
3766:
3764:
3744:
3738:
3737:
3713:
3707:
3706:
3704:
3703:
3659:
3653:
3652:
3650:
3649:
3634:
3628:
3627:
3625:
3623:
3617:
3610:
3602:
3596:
3595:
3593:
3591:
3568:
3562:
3561:
3554:
3548:
3543:
3541:
3533:
3529:
3523:
3522:
3486:
3480:
3476:
3458:Maximum Security
3451:
3422:
3416:
3415:
3413:
3412:
3397:
3391:
3390:
3366:
3360:
3359:
3347:
3333:
3327:
3323:
3307:
3296:
3271:
3244:
3238:
3237:
3235:
3233:
3217:
3211:
3210:
3186:
3180:
3179:
3177:
3166:
3157:
3151:
3150:
3132:
3126:
3125:
3123:
3122:
3103:
3097:
3096:
3094:
3093:
3074:
3068:
3067:
3049:
3043:
3042:
3040:
3039:
3033:
3026:
3018:
3012:
3011:
2995:
2985:
2979:
2978:
2960:
2943:
2942:
2926:
2916:
2910:
2909:
2907:
2906:
2891:
2885:
2884:
2868:
2858:
2852:
2851:
2849:
2847:
2832:
2826:
2825:
2823:
2822:
2807:
2801:
2800:
2798:
2797:
2782:
2776:
2775:
2747:
2741:
2740:
2738:
2737:
2728:. Archived from
2717:
2711:
2710:
2692:
2686:
2679:
2673:
2659:
2653:
2652:
2638:
2632:
2631:
2629:
2627:
2607:
2598:
2597:
2581:
2571:
2565:
2564:
2562:
2560:
2541:
2535:
2534:
2510:
2504:
2503:
2501:
2500:
2491:. Archived from
2484:
2478:
2477:
2475:
2474:
2465:. Archived from
2459:
2453:
2452:
2451:
2450:
2444:
2438:, archived from
2437:
2426:
2420:
2419:
2403:
2397:
2373:
2367:
2366:
2364:
2362:
2356:
2345:
2336:
2330:
2329:
2327:
2325:
2303:
2297:
2296:
2291:. Archived from
2285:
2276:
2275:
2247:
2241:
2237:
2221:
2210:
2191:
2175:
2172:Viruses Revealed
2164:
2148:
2135:
2129:
2128:
2092:
2086:
2085:
2059:
2053:
2052:
2050:
2048:
2029:
2023:
2019:
2003:
1992:
1990:
1989:
1980:. Archived from
1966:
1960:
1959:
1957:
1956:
1931:(7–8): 355–359.
1916:
1910:
1906:
1904:
1902:
1882:
1861:
1855:
1854:
1852:
1850:
1829:
1812:
1801:
1627:computer "worms"
1605:Alan Oppenheimer
1588:Michael Crichton
1571:Michael Crichton
1566:The Terminal Man
1515:executable files
1484:can restore the
1435:Windows Defender
1272:Windows Defender
1226:USB flash drives
1136:web address link
1106:Microsoft Office
1012:operating system
993:desktop computer
965:executable files
950:security defects
869:metamorphic code
858:polymorphic code
829:Polymorphic code
790:virus signatures
746:NTFS file system
529:Triggering phase
467:Also known as a
376:Lahore, Pakistan
264:BBN Technologies
219:self-replication
207:John von Neumann
201:Malware research
21:
6706:
6705:
6701:
6700:
6699:
6697:
6696:
6695:
6656:
6655:
6652:
6647:
6626:Countermeasures
6621:
6612:Mobile security
6560:
6551:Palm OS viruses
6516:Android malware
6504:
6418:
6414:Zombie computer
6372:
6336:
6330:
6300:
6295:
6145:
5845:
5833:
5824:Copy protection
5814:Mobile security
5745:
5740:
5658:
5655:
5650:
5644:
5619:
5617:
5591:
5576:
5575:
5567:
5543:
5541:
5521:
5504:
5502:Further reading
5499:
5498:
5491:
5469:
5465:
5449:
5448:
5437:
5436:
5432:
5424:
5420:
5410:
5408:
5397:"Brunner, John"
5393:
5389:
5381:
5377:
5366:
5362:
5353:
5351:
5347:
5340:
5336:
5335:
5331:
5322:
5320:
5311:
5310:
5306:
5297:
5295:
5286:
5285:
5281:
5272:
5270:
5261:
5260:
5256:
5243:
5242:
5238:
5223:
5219:
5206:
5205:
5201:
5188:
5187:
5183:
5167:
5166:
5160:
5158:
5153:
5152:
5148:
5139:
5137:
5128:
5127:
5123:
5114:
5112:
5107:. 2 June 2009.
5103:
5102:
5095:
5084:
5066:
5062:
5049:
5048:
5044:
5031:
5030:
5026:
5016:
5014:
5005:
5004:
5000:
4991:
4989:
4974:
4970:
4955:
4951:
4936:
4932:
4922:
4920:
4905:
4904:
4900:
4890:
4888:
4873:
4872:
4868:
4858:
4856:
4847:
4846:
4842:
4829:
4828:
4824:
4815:
4813:
4804:
4803:
4799:
4772:
4768:
4759:
4757:
4744:
4743:
4739:
4731:InformationWeek
4727:
4726:
4722:
4707:
4703:
4694:
4692:
4681:
4677:
4668:
4666:
4655:
4651:
4642:
4640:
4631:
4630:
4626:
4607:
4603:
4592:
4576:
4572:
4561:
4547:
4546:
4542:
4533:
4531:
4522:
4521:
4517:
4508:
4506:
4497:
4496:
4492:
4481:
4465:
4461:
4446:
4442:
4429:
4428:
4424:
4413:
4397:
4393:
4374:
4370:
4359:
4343:
4339:
4328:
4312:
4308:
4299:
4297:
4284:
4283:
4279:
4271:
4267:
4266:
4262:
4253:
4251:
4242:
4241:
4237:
4224:
4223:
4219:
4210:
4208:
4204:
4197:
4193:
4192:
4188:
4178:
4176:
4166:
4140:
4136:
4127:
4125:
4114:
4110:
4101:. SecureLight.
4095:
4091:
4082:
4080:
4071:
4070:
4066:
4056:
4054:
4050:
4043:
4037:
4033:
4024:
4022:
4013:
4012:
4008:
3997:
3981:
3977:
3970:
3948:
3944:
3935:
3933:
3920:
3919:
3915:
3904:
3888:
3881:
3870:
3854:
3850:
3843:
3827:
3823:
3814:
3812:
3803:
3802:
3798:
3788:
3786:
3777:
3776:
3772:
3762:
3760:
3745:
3741:
3730:
3714:
3710:
3701:
3699:
3684:
3660:
3656:
3647:
3645:
3636:
3635:
3631:
3621:
3619:
3615:
3608:
3604:
3603:
3599:
3589:
3587:
3585:
3569:
3565:
3555:
3546:
3544:
3535:
3534:
3530:
3526:
3487:
3483:
3479:
3469:
3444:
3423:
3419:
3410:
3408:
3399:
3398:
3394:
3383:
3367:
3363:
3356:
3338:"Macro Viruses"
3334:
3330:
3326:
3320:
3289:
3264:
3245:
3241:
3231:
3229:
3218:
3214:
3203:
3187:
3183:
3175:
3164:
3158:
3154:
3147:
3133:
3129:
3120:
3118:
3105:
3104:
3100:
3091:
3089:
3076:
3075:
3071:
3064:
3050:
3046:
3037:
3035:
3031:
3024:
3020:
3019:
3015:
3008:
2986:
2982:
2975:
2961:
2946:
2939:
2917:
2913:
2904:
2902:
2893:
2892:
2888:
2881:
2859:
2855:
2845:
2843:
2834:
2833:
2829:
2820:
2818:
2809:
2808:
2804:
2795:
2793:
2784:
2783:
2779:
2748:
2744:
2735:
2733:
2718:
2714:
2707:
2693:
2689:
2680:
2676:
2670:Wayback Machine
2660:
2656:
2639:
2635:
2625:
2623:
2608:
2601:
2594:
2572:
2568:
2558:
2556:
2543:
2542:
2538:
2527:
2511:
2507:
2498:
2496:
2485:
2481:
2472:
2470:
2461:
2460:
2456:
2448:
2446:
2442:
2435:
2427:
2423:
2404:
2400:
2386:Wayback Machine
2374:
2370:
2360:
2358:
2354:
2343:
2337:
2333:
2323:
2321:
2304:
2300:
2287:
2286:
2279:
2272:
2248:
2244:
2240:
2234:
2207:
2188:
2161:
2136:
2132:
2093:
2089:
2074:
2060:
2056:
2046:
2044:
2031:
2030:
2026:
2022:
2016:
1987:
1985:
1967:
1963:
1954:
1952:
1917:
1913:
1909:
1900:
1898:
1885:
1879:
1862:
1858:
1848:
1846:
1831:
1830:
1826:
1821:
1816:
1815:
1802:
1798:
1793:
1788:
1699:
1619:
1613:
1535:telephone modem
1531:Gregory Benford
1527:The Scarred Man
1523:
1521:Popular culture
1370:
1361:false positives
1347:zero-day attack
1330:virus signature
1175:
1161:
1159:Countermeasures
1140:instant message
1102:Microsoft Excel
1046:, particularly
1044:removable media
973:file extensions
942:
903:output for the
885:
786:
780:
741:
688:
652:hard disk drive
547:
536:Execution phase
497:
443:
438:
325:Leonard Adleman
290:Richard Skrenta
203:
193:
179:
156:artificial life
60:
55:
54:
53:
52:
51:
50:
34:
22:
15:
12:
11:
5:
6704:
6694:
6693:
6688:
6683:
6678:
6673:
6668:
6649:
6648:
6646:
6645:
6640:
6635:
6629:
6627:
6623:
6622:
6620:
6619:
6614:
6609:
6604:
6599:
6594:
6589:
6584:
6579:
6574:
6572:Anti-keylogger
6568:
6566:
6562:
6561:
6559:
6558:
6553:
6548:
6546:Mobile malware
6543:
6538:
6533:
6528:
6523:
6518:
6512:
6510:
6506:
6505:
6503:
6502:
6497:
6492:
6487:
6482:
6477:
6472:
6467:
6462:
6457:
6452:
6447:
6442:
6437:
6432:
6426:
6424:
6420:
6419:
6417:
6416:
6411:
6406:
6401:
6396:
6391:
6386:
6380:
6378:
6374:
6373:
6371:
6370:
6365:
6360:
6355:
6353:Computer virus
6350:
6344:
6342:
6338:
6337:
6329:
6328:
6321:
6314:
6306:
6297:
6296:
6294:
6293:
6291:Site isolation
6288:
6283:
6282:
6281:
6275:
6265:
6264:
6263:
6258:
6247:
6242:
6237:
6232:
6227:
6222:
6221:
6220:
6215:
6205:
6204:
6203:
6198:
6197:
6196:
6189:Authentication
6181:
6180:
6179:
6178:
6177:
6167:
6164:
6153:
6151:
6147:
6146:
6144:
6143:
6138:
6133:
6128:
6123:
6118:
6113:
6108:
6103:
6098:
6093:
6088:
6083:
6078:
6073:
6068:
6063:
6058:
6053:
6048:
6043:
6042:
6041:
6031:
6026:
6021:
6016:
6011:
6006:
6001:
5996:
5991:
5989:Email spoofing
5986:
5981:
5976:
5971:
5966:
5961:
5956:
5951:
5946:
5941:
5936:
5931:
5929:DOM clobbering
5926:
5921:
5916:
5911:
5909:Code injection
5906:
5901:
5900:
5899:
5894:
5889:
5884:
5876:
5871:
5866:
5861:
5855:
5853:
5847:
5846:
5836:
5834:
5832:
5831:
5826:
5821:
5816:
5811:
5806:
5801:
5796:
5791:
5789:Cyberterrorism
5786:
5781:
5780:
5779:
5777:Computer fraud
5774:
5764:
5759:
5753:
5751:
5747:
5746:
5739:
5738:
5731:
5724:
5716:
5710:
5709:
5699:
5693:
5688:
5683:
5654:
5653:External links
5651:
5649:
5648:
5642:
5630:Parikka, Jussi
5626:
5589:
5565:
5550:
5525:
5519:
5505:
5503:
5500:
5497:
5496:
5489:
5463:
5430:
5418:
5387:
5375:
5360:
5329:
5304:
5279:
5254:
5236:
5217:
5199:
5181:
5146:
5121:
5093:
5082:
5060:
5042:
5024:
4998:
4968:
4949:
4930:
4898:
4866:
4840:
4822:
4797:
4786:(5): 409–424.
4766:
4737:
4720:
4701:
4675:
4649:
4635:. 2012-07-19.
4624:
4621:on 2012-08-05.
4601:
4590:
4570:
4559:
4540:
4515:
4490:
4479:
4459:
4440:
4422:
4411:
4391:
4388:on 2013-09-01.
4368:
4357:
4337:
4326:
4306:
4277:
4260:
4235:
4226:"Virus Basics"
4217:
4186:
4164:
4150:. p. 19.
4134:
4108:
4089:
4064:
4031:
4006:
3995:
3975:
3968:
3942:
3926:SearchSecurity
3913:
3902:
3879:
3868:
3848:
3841:
3821:
3805:"www.sans.org"
3796:
3770:
3739:
3728:
3708:
3682:
3654:
3629:
3597:
3583:
3563:
3547:|journal=
3524:
3481:
3478:
3477:
3467:
3452:
3442:
3424:
3417:
3392:
3381:
3361:
3354:
3328:
3325:
3324:
3318:
3297:
3287:
3272:
3262:
3246:
3239:
3212:
3201:
3181:
3152:
3145:
3127:
3098:
3069:
3062:
3044:
3013:
3006:
2980:
2973:
2944:
2937:
2911:
2886:
2879:
2853:
2836:"winvir virus"
2827:
2802:
2777:
2742:
2712:
2705:
2687:
2674:
2654:
2633:
2599:
2592:
2566:
2536:
2525:
2505:
2479:
2454:
2421:
2398:
2368:
2331:
2298:
2295:on 2013-09-25.
2277:
2270:
2242:
2239:
2238:
2232:
2211:
2205:
2192:
2186:
2165:
2159:
2137:
2130:
2087:
2072:
2054:
2024:
2021:
2020:
2014:
1993:
1968:
1961:
1911:
1908:
1907:
1883:
1877:
1863:
1856:
1823:
1822:
1820:
1817:
1814:
1813:
1795:
1794:
1792:
1789:
1787:
1786:
1781:
1776:
1771:
1766:
1761:
1756:
1751:
1746:
1741:
1736:
1734:Cryptovirology
1731:
1726:
1721:
1716:
1711:
1706:
1700:
1698:
1695:
1615:Main article:
1612:
1609:
1522:
1519:
1466:System Restore
1442:System Restore
1369:
1366:
1160:
1157:
1122:email messages
1098:Microsoft Word
1068:Bulletin board
969:code injection
941:
938:
923:Stability test
901:thermal energy
884:
881:
823:cryptovirology
779:
776:
751:code injection
740:
737:
708:cavity viruses
687:
684:
625:macro language
613:Microsoft Word
592:code or other
573:of the host's
563:Microsoft Word
546:
543:
542:
541:
537:
534:
530:
527:
519:
516:
512:
496:
493:
492:
491:
483:
480:
465:
462:
455:search routine
451:
442:
439:
437:
434:
422:home computers
399:DOS interrupts
178:
175:
79:computer virus
58:
36:
30:
27:
25:
9:
6:
4:
3:
2:
6703:
6692:
6689:
6687:
6684:
6682:
6679:
6677:
6674:
6672:
6669:
6667:
6664:
6663:
6661:
6654:
6644:
6641:
6639:
6636:
6634:
6631:
6630:
6628:
6624:
6618:
6615:
6613:
6610:
6608:
6605:
6603:
6600:
6598:
6595:
6593:
6590:
6588:
6585:
6583:
6580:
6578:
6575:
6573:
6570:
6569:
6567:
6563:
6557:
6554:
6552:
6549:
6547:
6544:
6542:
6539:
6537:
6536:MacOS malware
6534:
6532:
6531:Linux malware
6529:
6527:
6524:
6522:
6519:
6517:
6514:
6513:
6511:
6507:
6501:
6498:
6496:
6493:
6491:
6488:
6486:
6483:
6481:
6478:
6476:
6473:
6471:
6468:
6466:
6463:
6461:
6458:
6456:
6453:
6451:
6450:Form grabbing
6448:
6446:
6443:
6441:
6438:
6436:
6433:
6431:
6428:
6427:
6425:
6421:
6415:
6412:
6410:
6407:
6405:
6402:
6400:
6397:
6395:
6392:
6390:
6387:
6385:
6382:
6381:
6379:
6375:
6369:
6366:
6364:
6361:
6359:
6358:Computer worm
6356:
6354:
6351:
6349:
6346:
6345:
6343:
6339:
6334:
6327:
6322:
6320:
6315:
6313:
6308:
6307:
6304:
6292:
6289:
6287:
6284:
6279:
6276:
6274:
6271:
6270:
6269:
6266:
6262:
6259:
6256:
6253:
6252:
6251:
6248:
6246:
6243:
6241:
6238:
6236:
6233:
6231:
6228:
6226:
6223:
6219:
6216:
6214:
6211:
6210:
6209:
6206:
6202:
6201:Authorization
6199:
6195:
6192:
6191:
6190:
6187:
6186:
6185:
6182:
6176:
6173:
6172:
6171:
6168:
6165:
6163:
6162:Secure coding
6160:
6159:
6158:
6155:
6154:
6152:
6148:
6142:
6139:
6137:
6134:
6132:
6131:SQL injection
6129:
6127:
6124:
6122:
6119:
6117:
6114:
6112:
6111:Vulnerability
6109:
6107:
6104:
6102:
6099:
6097:
6096:Trojan horses
6094:
6092:
6091:Software bugs
6089:
6087:
6084:
6082:
6079:
6077:
6074:
6072:
6069:
6067:
6064:
6062:
6059:
6057:
6054:
6052:
6049:
6047:
6044:
6040:
6037:
6036:
6035:
6032:
6030:
6027:
6025:
6022:
6020:
6017:
6015:
6012:
6010:
6007:
6005:
6002:
6000:
5997:
5995:
5992:
5990:
5987:
5985:
5982:
5980:
5979:Eavesdropping
5977:
5975:
5972:
5970:
5969:Data scraping
5967:
5965:
5962:
5960:
5957:
5955:
5952:
5950:
5947:
5945:
5942:
5940:
5939:Cryptojacking
5937:
5935:
5932:
5930:
5927:
5925:
5922:
5920:
5917:
5915:
5912:
5910:
5907:
5905:
5902:
5898:
5895:
5893:
5890:
5888:
5885:
5883:
5880:
5879:
5877:
5875:
5872:
5870:
5867:
5865:
5862:
5860:
5857:
5856:
5854:
5852:
5848:
5840:
5830:
5827:
5825:
5822:
5820:
5817:
5815:
5812:
5810:
5807:
5805:
5802:
5800:
5797:
5795:
5792:
5790:
5787:
5785:
5782:
5778:
5775:
5773:
5770:
5769:
5768:
5765:
5763:
5760:
5758:
5755:
5754:
5752:
5748:
5744:
5737:
5732:
5730:
5725:
5723:
5718:
5717:
5714:
5707:
5703:
5700:
5697:
5694:
5692:
5689:
5687:
5684:
5681:
5677:
5671:
5667:
5666:
5662:
5657:
5656:
5645:
5639:
5635:
5631:
5627:
5615:
5611:
5607:
5603:
5602:
5601:
5594:
5590:
5586:
5580:
5572:
5568:
5566:0-929408-07-1
5562:
5558:
5557:
5551:
5539:
5535:
5531:
5526:
5522:
5516:
5512:
5507:
5506:
5492:
5486:
5482:
5477:
5476:
5467:
5459:
5453:
5452:cite AV media
5446:
5441:
5434:
5427:
5422:
5406:
5402:
5398:
5395:Clute, John.
5391:
5384:
5383:November 1999
5379:
5371:
5364:
5346:
5339:
5333:
5318:
5314:
5308:
5294:on 2014-08-04
5293:
5289:
5283:
5268:
5264:
5258:
5250:
5246:
5240:
5232:
5229:. pcmag.com.
5228:
5221:
5213:
5209:
5208:"VirScan.org"
5203:
5195:
5191:
5185:
5177:
5171:
5156:
5150:
5136:on 2014-07-13
5135:
5131:
5125:
5110:
5106:
5100:
5098:
5089:
5085:
5083:9783540881919
5079:
5075:
5071:
5064:
5056:
5052:
5046:
5038:
5034:
5028:
5012:
5008:
5002:
4987:
4983:
4979:
4972:
4964:
4961:. pcmag.com.
4960:
4953:
4945:
4942:. pcmag.com.
4941:
4934:
4918:
4914:
4913:
4908:
4902:
4886:
4882:
4881:
4876:
4870:
4854:
4850:
4844:
4836:
4832:
4826:
4812:on 2013-04-07
4811:
4807:
4801:
4793:
4789:
4785:
4781:
4777:
4770:
4755:
4751:
4747:
4741:
4733:
4732:
4724:
4716:
4712:
4705:
4691:on 2014-08-23
4690:
4686:
4683:Wade Alcorn.
4679:
4664:
4660:
4653:
4638:
4634:
4628:
4620:
4616:
4612:
4605:
4597:
4593:
4587:
4583:
4582:
4574:
4566:
4562:
4556:
4552:
4551:
4544:
4530:on 2010-05-27
4529:
4525:
4519:
4504:
4500:
4494:
4486:
4482:
4476:
4472:
4471:
4463:
4455:
4451:
4444:
4436:
4432:
4426:
4418:
4414:
4412:9781430236276
4408:
4404:
4403:
4395:
4387:
4383:
4379:
4372:
4364:
4360:
4358:9780130464569
4354:
4350:
4349:
4341:
4333:
4329:
4327:9781893209787
4323:
4319:
4318:
4310:
4295:
4291:
4287:
4281:
4270:
4264:
4250:on 2005-05-04
4249:
4245:
4239:
4231:
4227:
4221:
4207:on 2018-02-09
4203:
4196:
4190:
4175:
4171:
4167:
4165:9781450301787
4161:
4157:
4153:
4149:
4145:
4138:
4123:
4119:
4112:
4104:
4100:
4093:
4078:
4074:
4068:
4049:
4042:
4035:
4020:
4016:
4010:
4002:
3998:
3996:9781118079768
3992:
3988:
3987:
3979:
3971:
3969:9781848009165
3965:
3961:
3956:
3955:
3946:
3931:
3927:
3923:
3917:
3909:
3905:
3899:
3895:
3894:
3886:
3884:
3875:
3871:
3869:9780201440997
3865:
3861:
3860:
3852:
3844:
3842:9781119104711
3838:
3834:
3833:
3825:
3810:
3806:
3800:
3784:
3780:
3774:
3758:
3754:
3750:
3743:
3735:
3731:
3729:0-321-30454-3
3725:
3721:
3720:
3712:
3697:
3693:
3689:
3685:
3683:0-8186-3370-0
3679:
3675:
3671:
3667:
3666:
3658:
3643:
3639:
3633:
3614:
3607:
3601:
3586:
3584:9781439863442
3580:
3576:
3575:
3567:
3559:
3552:
3539:
3528:
3520:
3516:
3512:
3508:
3504:
3500:
3496:
3492:
3485:
3474:
3470:
3468:9780672324598
3464:
3460:
3459:
3453:
3449:
3445:
3443:9780131014053
3439:
3435:
3431:
3426:
3425:
3421:
3406:
3402:
3396:
3388:
3384:
3382:9780387341880
3378:
3374:
3373:
3365:
3357:
3355:9781565926820
3351:
3346:
3345:
3339:
3332:
3321:
3319:9781565926820
3315:
3311:
3306:
3305:
3298:
3294:
3290:
3288:9781846283413
3284:
3280:
3279:
3273:
3269:
3265:
3263:9780815513643
3259:
3255:
3254:
3248:
3247:
3243:
3227:
3223:
3216:
3208:
3204:
3202:9781420046205
3198:
3194:
3193:
3185:
3174:
3170:
3163:
3156:
3148:
3146:0-321-30454-3
3142:
3138:
3131:
3116:
3112:
3108:
3102:
3087:
3083:
3079:
3073:
3065:
3063:0-7645-7418-3
3059:
3055:
3048:
3030:
3023:
3017:
3009:
3003:
2999:
2994:
2993:
2984:
2976:
2970:
2966:
2959:
2957:
2955:
2953:
2951:
2949:
2940:
2934:
2930:
2925:
2924:
2915:
2900:
2896:
2890:
2882:
2880:9781565926820
2876:
2872:
2867:
2866:
2857:
2841:
2837:
2831:
2816:
2812:
2806:
2791:
2787:
2781:
2773:
2769:
2765:
2761:
2757:
2753:
2746:
2732:on 2012-01-17
2731:
2727:
2723:
2716:
2708:
2706:1-897661-00-2
2702:
2698:
2691:
2684:
2678:
2671:
2667:
2664:
2661:Cohen, Fred,
2658:
2650:
2646:
2645:
2637:
2621:
2617:
2613:
2606:
2604:
2595:
2593:0-937175-71-4
2589:
2585:
2580:
2579:
2570:
2554:
2550:
2546:
2540:
2532:
2528:
2522:
2518:
2517:
2509:
2495:on 2013-08-09
2494:
2490:
2483:
2469:on 2006-10-16
2468:
2464:
2458:
2445:on 2015-07-14
2441:
2434:
2433:
2425:
2417:
2413:
2409:
2402:
2395:
2394:2-287-23939-1
2391:
2387:
2383:
2380:
2379:
2375:Éric Filiol,
2372:
2353:
2349:
2342:
2335:
2319:
2315:
2314:
2309:
2302:
2294:
2290:
2284:
2282:
2273:
2271:9780203647059
2267:
2263:
2259:
2258:
2253:
2246:
2235:
2229:
2225:
2220:
2219:
2212:
2208:
2206:0-929408-02-0
2202:
2198:
2193:
2189:
2187:0-07-222818-0
2183:
2179:
2174:
2173:
2166:
2162:
2156:
2152:
2147:
2146:
2139:
2138:
2134:
2126:
2122:
2118:
2114:
2110:
2106:
2102:
2098:
2091:
2083:
2079:
2075:
2069:
2065:
2058:
2042:
2038:
2037:Avast Academy
2034:
2028:
2017:
2011:
2007:
2002:
2001:
1994:
1984:on 2012-01-17
1983:
1979:
1975:
1970:
1969:
1965:
1950:
1946:
1942:
1938:
1934:
1930:
1926:
1922:
1915:
1896:
1892:
1891:Avast Academy
1888:
1884:
1880:
1874:
1870:
1865:
1864:
1860:
1844:
1840:
1839:
1834:
1828:
1824:
1810:
1806:
1800:
1796:
1785:
1782:
1780:
1777:
1775:
1772:
1770:
1767:
1765:
1762:
1760:
1757:
1755:
1752:
1750:
1747:
1745:
1742:
1740:
1737:
1735:
1732:
1730:
1727:
1725:
1722:
1720:
1717:
1715:
1712:
1710:
1707:
1705:
1702:
1701:
1694:
1692:
1688:
1684:
1680:
1676:
1672:
1668:
1664:
1660:
1656:
1652:
1648:
1644:
1643:trojan horses
1640:
1636:
1632:
1628:
1624:
1618:
1611:Other malware
1608:
1606:
1603:to run amok.
1602:
1598:
1597:
1592:
1589:
1584:
1582:
1578:
1577:
1572:
1568:
1567:
1562:
1561:David Gerrold
1558:
1557:
1551:
1549:
1545:
1541:
1536:
1532:
1528:
1518:
1516:
1512:
1507:
1503:
1499:
1495:
1490:
1487:
1483:
1479:
1478:Windows Vista
1475:
1471:
1467:
1463:
1459:
1455:
1451:
1447:
1443:
1438:
1436:
1432:
1428:
1424:
1420:
1414:
1412:
1407:
1403:
1399:
1395:
1391:
1387:
1386:optical media
1383:
1379:
1375:
1365:
1362:
1358:
1355:
1350:
1348:
1343:
1339:
1335:
1331:
1327:
1322:
1318:
1316:
1312:
1308:
1304:
1300:
1297:
1293:
1289:
1285:
1281:
1278:are assigned
1277:
1273:
1269:
1268:Patch Tuesday
1265:
1261:
1257:
1253:
1248:
1246:
1242:
1238:
1234:
1231:
1227:
1223:
1219:
1214:
1212:
1208:
1206:
1198:
1194:
1190:
1187:
1184:
1179:
1174:
1170:
1166:
1156:
1154:
1150:
1146:
1141:
1137:
1132:
1130:
1127:
1123:
1119:
1115:
1111:
1107:
1103:
1099:
1095:
1094:Macro viruses
1091:
1089:
1085:
1081:
1077:
1073:
1069:
1065:
1061:
1057:
1053:
1049:
1045:
1040:
1038:
1034:
1030:
1026:
1022:
1018:
1017:administrator
1013:
1008:
1006:
1002:
998:
994:
990:
985:
983:
979:
978:digital image
974:
970:
966:
961:
959:
955:
951:
947:
946:security bugs
937:
934:
932:
928:
924:
920:
918:
914:
910:
906:
902:
898:
894:
889:
880:
878:
874:
870:
865:
861:
859:
855:
851:
847:
843:
838:
834:
830:
826:
824:
820:
816:
811:
806:
802:
798:
793:
791:
785:
775:
773:
769:
765:
761:
755:
752:
747:
736:
733:
729:
725:
721:
717:
713:
709:
705:
701:
697:
693:
683:
680:
676:
671:
667:
665:
661:
657:
653:
649:
645:
641:
637:
635:
631:
626:
622:
618:
614:
610:
605:
603:
599:
595:
591:
587:
583:
578:
576:
572:
569:), or in the
568:
565:documents or
564:
560:
556:
552:
538:
535:
531:
528:
525:
520:
517:
513:
511:Dormant phase
510:
509:
508:
506:
502:
489:
484:
481:
478:
474:
470:
466:
463:
460:
456:
452:
449:
448:
447:
433:
431:
427:
423:
418:
416:
412:
411:Win32.Cabanas
408:
404:
400:
396:
393:
389:
385:
381:
377:
373:
370:virus dubbed
369:
365:
361:
357:
352:
350:
346:
342:
338:
334:
330:
326:
322:
318:
313:
311:
307:
303:
299:
295:
291:
287:
282:
280:
276:
272:
269:
265:
261:
257:
253:
252:Creeper virus
245:
240:
236:
234:
230:
229:
224:
220:
216:
212:
208:
202:
198:
192:
188:
184:
174:
172:
168:
163:
161:
157:
153:
152:cybersecurity
149:
145:
141:
137:
133:
129:
125:
122:
117:
115:
111:
110:computer worm
107:
102:
100:
96:
92:
88:
84:
81:is a type of
80:
72:
68:
64:
48:
44:
40:
33:
28:
19:
6653:
6409:Trojan horse
6389:Clickjacking
6352:
6235:Data masking
5963:
5794:Cyberwarfare
5663:
5633:
5618:. Retrieved
5599:
5597:
5571:the original
5555:
5542:. Retrieved
5534:The Register
5533:
5510:
5474:
5466:
5443:
5439:
5433:
5421:
5409:. Retrieved
5400:
5390:
5378:
5369:
5363:
5352:. Retrieved
5332:
5321:. Retrieved
5307:
5296:. Retrieved
5292:the original
5282:
5271:. Retrieved
5257:
5239:
5220:
5202:
5184:
5159:. Retrieved
5149:
5138:. Retrieved
5134:the original
5124:
5113:. Retrieved
5073:
5063:
5045:
5027:
5015:. Retrieved
5001:
4990:. Retrieved
4981:
4971:
4952:
4933:
4921:. Retrieved
4910:
4901:
4889:. Retrieved
4885:the original
4878:
4869:
4857:. Retrieved
4843:
4825:
4814:. Retrieved
4810:the original
4800:
4783:
4779:
4769:
4758:. Retrieved
4749:
4740:
4729:
4723:
4710:
4704:
4693:. Retrieved
4689:the original
4678:
4667:. Retrieved
4652:
4641:. Retrieved
4627:
4619:the original
4614:
4604:
4580:
4573:
4549:
4543:
4532:. Retrieved
4528:the original
4518:
4507:. Retrieved
4493:
4469:
4462:
4443:
4425:
4401:
4394:
4386:the original
4381:
4371:
4347:
4340:
4316:
4309:
4298:. Retrieved
4289:
4280:
4263:
4252:. Retrieved
4248:the original
4238:
4220:
4209:. Retrieved
4202:the original
4189:
4177:. Retrieved
4147:
4137:
4126:. Retrieved
4111:
4092:
4081:. Retrieved
4067:
4057:September 9,
4055:. Retrieved
4048:the original
4034:
4023:. Retrieved
4009:
3985:
3978:
3953:
3945:
3934:. Retrieved
3925:
3916:
3892:
3858:
3851:
3831:
3824:
3813:. Retrieved
3799:
3789:September 4,
3787:. Retrieved
3773:
3763:September 4,
3761:. Retrieved
3752:
3742:
3718:
3711:
3700:. Retrieved
3664:
3657:
3646:. Retrieved
3644:. 2022-03-09
3641:
3632:
3620:. Retrieved
3600:
3590:September 4,
3588:. Retrieved
3573:
3566:
3538:cite journal
3527:
3494:
3484:
3457:
3433:
3420:
3409:. Retrieved
3395:
3371:
3364:
3348:. O'Reilly.
3343:
3331:
3303:
3277:
3252:
3242:
3230:. Retrieved
3215:
3191:
3184:
3168:
3155:
3136:
3130:
3119:. Retrieved
3110:
3101:
3090:. Retrieved
3081:
3072:
3053:
3047:
3036:. Retrieved
3016:
2991:
2983:
2964:
2922:
2914:
2903:. Retrieved
2889:
2864:
2856:
2844:. Retrieved
2830:
2819:. Retrieved
2805:
2794:. Retrieved
2780:
2755:
2751:
2745:
2734:. Retrieved
2730:the original
2725:
2715:
2696:
2690:
2682:
2677:
2657:
2643:
2636:
2624:. Retrieved
2577:
2569:
2557:. Retrieved
2548:
2539:
2515:
2508:
2497:. Retrieved
2493:the original
2482:
2471:. Retrieved
2467:the original
2463:"Virus list"
2457:
2447:, retrieved
2440:the original
2431:
2424:
2411:
2401:
2377:
2371:
2359:. Retrieved
2347:
2334:
2324:September 4,
2322:. Retrieved
2313:The Register
2311:
2301:
2293:the original
2256:
2245:
2217:
2196:
2171:
2144:
2133:
2100:
2096:
2090:
2063:
2057:
2045:. Retrieved
2036:
2027:
1999:
1986:. Retrieved
1982:the original
1977:
1964:
1953:. Retrieved
1928:
1924:
1914:
1899:. Retrieved
1890:
1868:
1859:
1849:September 3,
1847:. Retrieved
1836:
1827:
1799:
1657:, malicious
1620:
1594:
1585:
1581:John Brunner
1574:
1564:
1554:
1552:
1526:
1524:
1492:Microsoft's
1491:
1446:Task Manager
1439:
1415:
1411:flash drives
1382:file systems
1371:
1351:
1338:boot sectors
1323:
1319:
1249:
1215:
1210:
1203:
1202:In 1989 The
1201:
1197:Ubuntu Linux
1169:Anti-malware
1133:
1110:spreadsheets
1092:
1072:Trojan horse
1048:floppy disks
1041:
1009:
986:
982:flash drives
962:
948:, which are
943:
935:
927:overclocking
921:
917:benchmarking
892:
890:
886:
866:
862:
827:
794:
789:
787:
756:
742:
707:
689:
672:
668:
664:floppy disks
660:flash drives
639:
638:
620:
606:
601:
598:control flow
581:
579:
548:
498:
444:
419:
353:
348:
314:
283:
278:
249:
226:
204:
164:
138:(e.g., with
118:
114:host program
106:host program
103:
78:
76:
46:
37:This is the
31:
6541:Macro virus
6526:iOS malware
6500:Web threats
6460:Infostealer
6377:Concealment
6175:Misuse case
6009:Infostealer
5984:Email fraud
5949:Data breach
5784:Cybergeddon
5706:Andrew Ross
4228:. US-CERT.
4179:19 November
3622:2 September
2895:"SCA virus"
2813:. YouTube.
2685:, pp. 19–20
2672:, 1987, IBM
1675:credit card
1498:cloned disk
1421:subsidiary
1336:(RAM), and
1288:Secunia PSI
1191:running in
1183:open-source
1056:boot sector
1033:"root user"
997:Open-source
958:exploitable
893:power virus
646:and/or the
644:boot sector
630:attachments
621:macro virus
571:boot sector
392:Windows API
388:Windows 3.0
368:boot sector
306:floppy disk
6660:Categories
6565:Protection
6480:Ransomware
6445:Fleeceware
6240:Encryption
6116:Web shells
6056:Ransomware
6004:Hacktivism
5767:Cybercrime
5445:machinery.
5411:30 January
5354:2016-04-16
5323:2016-04-16
5298:2014-07-17
5273:2015-01-31
5161:2014-07-17
5140:2014-07-17
5115:2016-04-16
4992:2013-01-19
4816:2013-04-08
4760:2020-09-03
4695:2015-10-13
4669:2014-04-07
4643:2014-04-28
4534:2010-08-27
4509:2021-03-16
4300:2015-05-16
4254:2002-06-13
4211:2021-08-29
4128:2024-03-24
4083:2010-08-27
4025:2010-08-27
3936:2018-08-07
3815:2016-04-16
3702:2023-10-13
3648:2022-06-26
3411:2015-10-16
3121:2022-06-26
3111:CloudFlare
3092:2022-06-26
3038:2016-04-25
2905:2014-01-14
2821:2010-08-27
2796:2010-08-27
2736:2014-07-17
2726:VX Heavens
2499:2009-02-16
2473:2008-02-07
2449:2015-05-08
1988:2014-07-17
1978:VX Heavens
1955:2022-10-30
1819:References
1769:Virus hoax
1679:debit card
1663:Fred Cohen
1647:keyloggers
1631:ransomware
1502:disk image
1474:Windows XP
1470:Windows Me
1423:VirusTotal
1292:Ransomware
1252:anti virus
1209:published
1163:See also:
1021:Windows XP
873:W32/Simile
837:decryption
797:encryption
782:See also:
760:heuristics
575:hard drive
559:.COM files
501:life cycle
488:virus hoax
469:logic bomb
415:Windows NT
407:Windows 95
356:J. B. Gunn
317:Fred Cohen
310:Elk Cloner
298:Pittsburgh
286:Elk Cloner
181:See also:
140:ransomware
124:deceptions
18:Boot virus
6681:Deception
6490:Scareware
6440:Crimeware
6071:Shellcode
6066:Scareware
5914:Crimeware
5874:Backdoors
5668:is being
5579:cite book
5544:10 August
5440:Westworld
4982:PCMag.com
4912:Microsoft
4880:Microsoft
3519:109103460
3511:1556-5068
3078:"Payload"
2772:0163-6006
2626:April 12,
2117:1045-9219
2082:897634290
1945:0167-4048
1729:Core Wars
1724:Crimeware
1677:numbers,
1669:space or
1667:hard disk
1596:Westworld
1586:The 1973
1550:in 1970.
1482:Windows 7
1458:safe mode
1454:rebooting
1378:read-only
1357:algorithm
1354:heuristic
1315:passwords
1076:Shareware
805:cleartext
732:processes
724:Conficker
712:CIH virus
692:deception
686:Detection
666:, etc.).
594:functions
567:PDF files
553:(such as
430:SCA virus
341:antivirus
329:algorithm
319:from the
315:In 1984,
302:Apple DOS
223:assembler
91:inserting
6638:Honeypot
6597:Firewall
6384:Backdoor
6245:Firewall
6150:Defenses
6076:Spamming
6061:Rootkits
6034:Phishing
5994:Exploits
5661:template
5632:(2007).
5614:Archived
5538:Archived
5405:Archived
5345:Archived
5317:Archived
5267:Archived
5249:Archived
5231:Archived
5212:Archived
5194:Archived
5170:cite web
5109:Archived
5088:Archived
5055:Archived
5037:Archived
5011:Archived
4986:Archived
4963:Archived
4944:Archived
4923:June 21,
4917:Archived
4891:June 21,
4859:June 21,
4853:Archived
4835:Archived
4754:Archived
4663:Archived
4637:Archived
4596:Archived
4565:Archived
4503:Archived
4485:Archived
4454:Archived
4435:Archived
4417:Archived
4363:Archived
4332:Archived
4294:Archived
4230:Archived
4122:Archived
4103:Archived
4077:Archived
4019:Archived
4001:Archived
3930:Archived
3908:Archived
3874:Archived
3809:Archived
3783:Archived
3757:Archived
3734:Archived
3696:Archived
3613:Archived
3473:Archived
3448:Archived
3405:Archived
3387:Archived
3293:Archived
3268:Archived
3226:Archived
3207:Archived
3173:Archived
3115:Archived
3086:Archived
3029:Archived
2899:Archived
2840:Archived
2815:Archived
2790:Archived
2666:Archived
2649:archived
2620:Archived
2553:Archived
2531:Archived
2416:archived
2382:Archived
2361:June 10,
2352:Archived
2318:Archived
2041:Archived
1949:Archived
1895:Archived
1843:Archived
1697:See also
1683:spamming
1655:bootkits
1651:rootkits
1601:androids
1486:registry
1406:bootable
1342:database
1311:Phishing
1296:phishing
1222:download
931:Spinlock
854:mutation
844:, or by
842:emulator
819:rebooted
700:software
615:, allow
372:(c)Brain
260:Internet
215:Automata
154:issues,
144:sabotage
93:its own
67:Hex dump
43:reviewed
6495:Spyware
6404:Rootkit
6333:Malware
6086:Spyware
6029:Payload
6024:Malware
5964:Viruses
5944:Botnets
5851:Threats
5676:Viruses
5620:24 July
4746:"Trove"
4382:PCWorld
4174:6995371
3692:8436288
3232:16 June
2846:10 June
2559:16 June
2252:"Virus"
2125:2242419
2047:9 March
1901:9 March
1809:biology
1744:Malware
1691:payload
1635:spyware
1623:malware
1617:Malware
1540:FORTRAN
1511:live CD
1504:, or a
1374:backups
1280:CVE IDs
1245:AV-TEST
1241:hackers
1237:threats
1186:ClamWin
1149:MySpace
1084:vectors
1080:bootleg
1062:(BBS),
883:Effects
728:rootkit
634:e-mails
540:screen.
505:biology
482:Payload
473:payload
464:Trigger
403:Bizatch
345:Windows
337:malware
256:ARPANET
177:History
99:viruses
83:malware
69:of the
6470:Malbot
6435:Botnet
6430:Adware
6335:topics
6280:(SIEM)
6257:(HIDS)
6141:Zombie
5878:Bombs
5859:Adware
5682:(DMOZ)
5680:Curlie
5674:
5665:Curlie
5640:
5604:(Web (
5563:
5517:
5487:
5080:
5017:23 May
4715:ADAPSO
4588:
4557:
4477:
4409:
4355:
4324:
4172:
4162:
3993:
3966:
3900:
3866:
3839:
3753:Forbes
3726:
3690:
3680:
3581:
3517:
3509:
3465:
3440:
3379:
3352:
3316:
3285:
3260:
3199:
3143:
3060:
3004:
2971:
2935:
2877:
2873:–100.
2770:
2703:
2590:
2523:
2392:
2268:
2230:
2203:
2184:
2157:
2123:
2115:
2080:
2070:
2012:
1943:
1875:
1704:Botnet
1639:adware
1591:sci-fi
1506:backup
1419:Google
1307:ransom
1205:ADAPSO
1171:, and
1153:Yahoo!
1138:as an
1114:Mac OS
1037:Usenet
1029:log in
833:threat
815:XORing
764:hashes
495:Phases
436:Design
384:WinVir
279:Reaper
271:PDP-10
244:MacMag
228:Diplom
189:, and
136:profit
6126:Worms
6121:Wiper
6039:Voice
5887:Logic
5659:‹The
5600:video
5348:(PDF)
5341:(PDF)
4272:(PDF)
4205:(PDF)
4198:(PDF)
4170:S2CID
4051:(PDF)
4044:(PDF)
3688:S2CID
3616:(PDF)
3609:(PDF)
3515:S2CID
3312:–38.
3176:(PDF)
3165:(PDF)
3032:(PDF)
3025:(PDF)
2443:(PDF)
2436:(PDF)
2355:(PDF)
2344:(PDF)
2121:S2CID
1791:Notes
1593:film
1388:like
1230:patch
1064:modem
1025:Bliss
1001:Linux
617:macro
524:clone
441:Parts
426:Amiga
420:Even
395:calls
296:near
275:TENEX
71:Brain
5892:Time
5882:Fork
5638:ISBN
5622:2011
5585:link
5561:ISBN
5546:2017
5515:ISBN
5485:ISBN
5458:link
5413:2013
5176:link
5078:ISBN
5019:2014
4925:2012
4893:2012
4861:2012
4586:ISBN
4555:ISBN
4475:ISBN
4407:ISBN
4353:ISBN
4322:ISBN
4181:2013
4160:ISBN
4059:2007
3991:ISBN
3964:ISBN
3898:ISBN
3864:ISBN
3837:ISBN
3791:2015
3765:2015
3724:ISBN
3678:ISBN
3624:2008
3592:2015
3579:ISBN
3558:link
3551:help
3507:ISSN
3463:ISBN
3438:ISBN
3377:ISBN
3350:ISBN
3314:ISBN
3283:ISBN
3258:ISBN
3234:2013
3197:ISBN
3141:ISBN
3058:ISBN
3002:ISBN
2969:ISBN
2933:ISBN
2875:ISBN
2848:2016
2768:ISSN
2701:ISBN
2628:2013
2616:CNBC
2588:ISBN
2561:2022
2521:ISBN
2390:ISBN
2363:2010
2326:2015
2266:ISBN
2228:ISBN
2201:ISBN
2182:ISBN
2155:ISBN
2113:ISSN
2078:OCLC
2068:ISBN
2049:2021
2010:ISBN
1941:ISSN
1903:2021
1873:ISBN
1851:2020
1563:and
1500:, a
1480:and
1448:and
1429:, a
1392:and
1349:").
1299:scam
1294:and
1266:on "
1193:Wine
1100:and
1078:and
611:and
555:.EXE
477:disk
250:The
242:The
199:and
158:and
146:and
95:code
89:and
5897:Zip
5704:by
5678:at
5610:MP4
5606:WMV
4788:doi
4152:doi
3960:341
3670:doi
3499:doi
2998:292
2760:doi
2262:154
2105:doi
1933:doi
1579:by
1569:by
1559:by
1544:lab
1529:by
1468:on
1450:CMD
1402:DVD
1394:DVD
1195:on
803:in
696:DOS
632:in
586:RAM
557:or
360:APL
268:DEC
45:on
6662::
5672:.›
5608:/
5581:}}
5577:{{
5536:.
5532:.
5483:.
5481:13
5454:}}
5450:{{
5399:.
5343:.
5315:.
5265:.
5247:.
5210:.
5192:.
5172:}}
5168:{{
5096:^
5086:.
5053:.
5035:.
4984:.
4980:.
4915:.
4909:.
4877:.
4851:.
4784:24
4782:.
4778:.
4752:.
4748:.
4713:.
4661:.
4613:.
4594:.
4563:.
4501:.
4483:.
4452:.
4415:.
4380:.
4361:.
4330:.
4292:.
4288:.
4168:.
4158:.
4146:.
4120:.
3999:.
3962:.
3928:.
3924:.
3906:.
3882:^
3872:.
3807:.
3755:.
3751:.
3732:.
3694:.
3686:.
3676:.
3640:.
3611:.
3542::
3540:}}
3536:{{
3513:.
3505:.
3497:.
3493:.
3471:.
3446:.
3432:.
3403:.
3385:.
3340:.
3310:37
3291:.
3266:.
3205:.
3113:.
3109:.
3084:.
3080:.
3000:.
2947:^
2931:.
2929:15
2871:99
2838:.
2766:.
2756:14
2754:.
2724:.
2647:,
2618:.
2614:.
2602:^
2586:.
2584:86
2551:.
2547:.
2529:.
2414:,
2410:,
2346:.
2316:.
2310:.
2280:^
2264:.
2254:.
2226:.
2224:27
2180:.
2153:.
2119:.
2111:.
2101:21
2099:.
2076:.
2035:.
2008:.
2006:14
1976:.
1947:.
1939:.
1929:27
1927:.
1923:.
1889:.
1835:.
1653:,
1649:,
1645:,
1641:,
1637:,
1633:,
1629:,
1583:.
1517:.
1476:,
1472:,
1464:.
1413:.
1398:CD
1390:CD
1286:.
1167:,
1155:.
929:.
919:.
891:A
825:.
720:KB
662:,
654:,
580:A
382:,
185:,
173:.
162:.
101:.
77:A
41:,
6325:e
6318:t
6311:v
5735:e
5728:t
5721:v
5646:.
5624:.
5587:)
5548:.
5523:.
5493:.
5460:)
5415:.
5357:.
5326:.
5301:.
5276:.
5178:)
5164:.
5143:.
5118:.
5021:.
4995:.
4927:.
4895:.
4863:.
4819:.
4794:.
4790::
4763:.
4698:.
4672:.
4646:.
4537:.
4512:.
4303:.
4274:.
4257:.
4214:.
4183:.
4154::
4131:.
4086:.
4061:.
4028:.
3972:.
3939:.
3845:.
3818:.
3793:.
3767:.
3705:.
3672::
3651:.
3626:.
3594:.
3560:)
3553:)
3549:(
3521:.
3501::
3414:.
3358:.
3322:.
3236:.
3149:.
3124:.
3095:.
3066:.
3041:.
3010:.
2977:.
2941:.
2908:.
2883:.
2850:.
2824:.
2799:.
2774:.
2762::
2739:.
2709:.
2630:.
2596:.
2563:.
2502:.
2476:.
2396:.
2365:.
2328:.
2274:.
2236:.
2209:.
2190:.
2178:6
2163:.
2151:8
2127:.
2107::
2084:.
2051:.
2018:.
1991:.
1958:.
1935::
1905:.
1881:.
1853:.
1811:.
1400:/
899:(
490:.
461:.
49:.
20:)
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.