20:
1237:. This means that, unlike most ISPs, they will not terminate a customer for spamming. These hosting firms operate as clients of larger ISPs, and many have eventually been taken offline by these larger ISPs as a result of complaints regarding spam activity. Thus, while a firm may advertise bulletproof hosting, it is ultimately unable to deliver without the connivance of its upstream ISP. However, some spammers have managed to get what is called a
1073:
1193:
terms in the various iterations of misspelling. Other filters target the actual obfuscation methods, such as the non-standard use of punctuation or numerals into unusual places. Similarly, HTML-based email gives the spammer more tools to obfuscate text. Inserting HTML comments between letters can foil some filters. Another common ploy involves presenting the text as an image, which is either sent along or loaded from a remote server.
563:
983:
1250:, or software designed for spammers. Spamware varies widely, but may include the ability to import thousands of addresses, to generate random addresses, to insert fraudulent headers into messages, to use dozens or hundreds of mail servers simultaneously, and to make use of open relays. The sale of spamware is illegal in eight U.S. states.
2347:(2) STATE LAW NOT SPECIFIC TO ELECTRONIC ~ZL.--This Act shall not be construed to preempt the applicability of(A) State laws that are not specific to electronic mail, including State trespass, contract, or tot~ law; or (B) other State laws to the extent that those laws relate to acts of fraud or computer crime.
641:
was 2600 at the time though software limitations meant only slightly more than half of the intended recipients actually received it. As of August 2010, the number of spam messages sent per day was estimated to be around 200 billion. More than 97% of all emails sent over the
Internet in 2008 were
1261:
purportedly containing lists of email addresses, for use in sending spam to these addresses. Such lists are also sold directly online, frequently with the false claim that the owners of the listed addresses have requested (or "opted in") to be included. Such lists often contain invalid addresses. In
681:
A 2004 survey estimated that lost productivity costs
Internet users in the United States $ 21.58 billion annually, while another reported the cost at $ 17 billion, up from $ 11 billion in 2003. In 2004, the worldwide productivity cost of spam has been estimated to be $ 50 billion
444:
Bulk commercial email does not violate CAN-SPAM, provided that it meets certain criteria, such as a truthful subject line, no forged information in the headers. If it fails to comply with any of these requirements it is illegal. Those opposing spam greeted the new law with dismay and disappointment,
1192:
The principle of this method is to leave the word readable to humans (who can easily recognize the intended word for such misspellings), but not likely to be recognized by a computer program. This is only somewhat effective, because modern filter patterns have been designed to recognize blacklisted
646:
security report. MAAWG estimates that 85% of incoming mail is "abusive email", as of the second half of 2007. The sample size for the MAAWG's study was over 100 million mailboxes. In 2018 with growing affiliation networks & email frauds worldwide about 90% of global email traffic is spam as per
391:
member states shall take appropriate measures to ensure that unsolicited communications for the purposes of direct marketing are not allowed either without the consent of the subscribers concerned or in respect of subscribers who do not wish to receive these communications, the choice between these
197:
If a marketer has one database containing names, addresses, and telephone numbers of customers, they can pay to have their database matched against an external database containing email addresses. The company then has the means to send email to people who have not requested email, which may include
633:
The total volume of email spam has been consistently growing, but in 2011 the trend seemed to reverse. The amount of spam that users see in their mailboxes is only a portion of total spam sent, since spammers' lists often contain a large percentage of invalid addresses and many spam filters simply
448:
In practice, it had a little positive impact. In 2004, less than one percent of spam complied with CAN-SPAM, although a 2005 review by the
Federal Trade Commission claimed that the amount of sexually explicit spam had significantly decreased since 2003 and the total volume had begun to level off.
319:
If the sender's address was forged, then the bounce may go to an innocent party. Since these messages were not solicited by the recipients, are substantially similar to each other, and are delivered in bulk quantities, they qualify as unsolicited bulk email or spam. As such, systems that generate
230:
Often, image spam contains nonsensical, computer-generated text which simply annoys the reader. However, new technology in some programs tries to read the images by attempting to find text in these images. These programs are not very accurate, and sometimes filter out innocent images of products,
1323:
refers to whether the people on a mailing list are given the option to be put in, or taken out, of the list. Confirmation (and "double", in marketing speak) refers to an email address transmitted e.g. through a web form being confirmed to actually request joining a mailing list, instead of being
1205:
has become popular as a spam-filtering technique, spammers have started using methods to weaken it. To a rough approximation, Bayesian filters rely on word probabilities. If a message contains many words that are used only in spam, and few that are never used in spam, it is likely to be spam. To
497:
Spoofing can have serious consequences for legitimate email users. Not only can their email inboxes get clogged up with "undeliverable" emails in addition to volumes of spam, but they can mistakenly be identified as a spammer. Not only may they receive irate email from spam victims, but (if spam
146:
report in 2014, there are an average of 54 billion spam messages sent every day. "Pharmaceutical products (Viagra and the like) jumped up 45% from last quarter’s analysis, leading this quarter’s spam pack. Emails purporting to offer jobs with fast, easy cash come in at number two, accounting for
624:
must be correctly set for the outgoing mail server and large swaths of IP addresses are blocked, sometimes pre-emptively, to prevent spam. These measures can pose problems for those wanting to run a small email server off an inexpensive domestic connection. Blacklisting of IP ranges due to spam
493:
chains (the 'Received' header), since the receiving mailserver records the actual connection from the last mailserver's IP address. To counter this, some spammers forge additional delivery headers to make it appear as if the email had previously traversed many legitimate servers.
270:
for gathering valid addresses from an email service provider. Since the goal in such an attack is to use the bounces to separate invalid addresses from the valid ones, spammers may dispense with most elements of the header and the entire message body, and still accomplish their
1273:(DNSBLs), including the MAPS RBL, Spamhaus SBL, SORBS and SPEWS, target the providers of spam-support services as well as spammers. DNSBLs blacklist IPs or ranges of IPs to persuade ISPs to terminate services with known customers who are spammers or resell to spammers.
548:
Brazil produced the most zombies in the first quarter of 2010. Brazil was the source of 20 percent of all zombies, which is down from 14 percent from the fourth quarter of 2009. India had 10 percent, with
Vietnam at 8 percent, and the Russian Federation at 7 percent.
1210:. More broadly machine learning can be used to identify and filter spam. There is a game of escalation between spammers and anti-spam identification and filtering systems where spammers adjust to attempt to evade new identification and filtering techniques.
541:). In June 2006, an estimated 80 percent of email spam was sent by zombie PCs, an increase of 30 percent from the prior year. An estimated 55 billion email spam were sent each day in June 2006, an increase of 25 billion per day from June 2005.
887:
Because of the international nature of spam, the spammer, the hijacked spam-sending computer, the spamvertised server, and the user target of the spam are all often located in different countries. As much as 80% of spam received by
Internet users in
1165:" in the subject line is spam, and instruct their mail program to automatically delete all such messages. To defeat such filters, the spammer may intentionally misspell commonly filtered words or insert other characters, often in a style similar to
1025:. Each method has strengths and weaknesses and each is controversial because of its weaknesses. For example, one company's offer to " some spamtrap and honeypot addresses" from email lists defeats the ability for those methods to identify spammers.
284:
Some spam may appear to be blank when in fact it is not. An example of this is the VBS.Davinia.B email worm which propagates through messages that have no subject line and appears blank, when in fact it uses HTML code to download other
441:, which was in many cases less restrictive. CAN-SPAM also preempted any further state legislation, but it left related laws not specific to e-mail intact. Courts have ruled that spam can constitute, for example, trespass to chattels.
461:
to send out their messages. Spammers often use false names, addresses, phone numbers, and other contact information to set up "disposable" accounts at various
Internet service providers. They also often use falsified or stolen
1152:
is done without the consent (and sometimes against the expressed will) of the address owners. A single spam run may target tens of millions of possible addresses – many of which are invalid, malformed, or undeliverable.
619:
To combat the problems posed by botnets, open relays, and proxy servers, many email server administrators pre-emptively block dynamic IP ranges and impose stringent requirements on other servers wishing to deliver mail.
400:
In the United
Kingdom, for example, unsolicited emails cannot be sent to an individual subscriber unless prior permission has been obtained or unless there is a pre-existing commercial relationship between the parties.
1222:: business services, other than the actual sending of spam itself, which permit the spammer to continue operating. Spam-support services can include processing orders for goods advertised in spam, hosting Web sites or
254:
Blank spam is spam lacking a payload advertisement. Often the message body is missing altogether, as well as the subject line. Still, it fits the definition of spam because of its nature as bulk and unsolicited email.
469:
Senders may go to great lengths to conceal the origin of their messages. Large companies may hire another firm to send their messages so that complaints or blocking of email falls on a third party. Others engage in
544:
For the first quarter of 2010, an estimated 305,000 newly activated zombie PCs were brought online each day for malicious activity. This number is slightly lower than the 312,000 of the fourth quarter of 2009.
102:
Spammers collect email addresses from chat rooms, websites, customer lists, newsgroups, and viruses that harvest users' address books. These collected email addresses are sometimes also sold to other spammers.
2319:
3035:
the date provided is for the original article; the date of revision for the republication is 8 June 2005; verification that content of the republication is the same as the original article is pending
1031:
combines many of the techniques to scan messages exiting out of a service provider's network, identify spam, and taking action such as blocking the message or shutting off the source of the message.
147:
approximately 15% of all spam email. And, rounding off at number three are spam emails about diet products (such as
Garcinia gummi-gutta or Garcinia Cambogia), accounting for approximately 1%."
1291:
Spam promoting a commercial service or product. This is the most common type of spam, but it excludes spams that are hoaxes (e.g. virus warnings), political advocacy, religious messages, and
2563:
2211:
1334:
reference to naïve developers who believe they have invented the perfect spam filter, which will stop all spam from reaching users' inboxes while deleting no legitimate email accidentally.
281:
or other may have contributed to this problem—from poorly written spam software to malfunctioning relay servers, or any problems that may truncate header lines from the message body.
2527:
2138:
482:) has no authentication by default, so the spammer can pretend to originate a message apparently from any email address. To prevent this, some ISPs and domains require the use of
223:
image and displayed in the email. This prevents text-based spam filters from detecting and blocking spam messages. Image spam was reportedly used in the mid-2000s to advertise "
1161:
Many spam-filtering techniques work by searching for patterns in the headers or bodies of messages. For instance, a user may decide that all email they receive with the word "
2369:
62:
is ubiquitous, unavoidable, and repetitive. Email spam has steadily grown since the early 1990s, and by 2014 was estimated to account for around 90% of total email traffic.
1262:
recent years, these have fallen almost entirely out of use due to the low quality email addresses available on them, and because some email lists exceed 20GB in size. The
2164:
1970:
2316:
1811:
2271:
76:
The legal definition and status of spam varies from one jurisdiction to another, but nowhere have laws and lawsuits been particularly successful in stemming spam.
2098:
130:
Spam is sent by both otherwise reputable organizations and lesser companies. When spam is sent by otherwise reputable companies it is sometimes referred to as
2072:
1305:
is a service contract offered by an ISP which offers bulk email service to spamming clients, in violation of that ISP's publicly posted acceptable use policy.
2021:
1058:
If a recipient periodically checks his spam folder, that will cost him time and if there is a lot of spam it is easy to overlook the few legitimate messages.
1705:
1682:
2724:
1218:
A number of other online activities and business practices are considered by anti-spam activists to be connected to spamming. These are sometimes termed
2963:
3077:
384:
3660:
2559:
1929:
Biggio, Battista; Fumera, Giorgio; Pillai, Ignazio; Roli, Fabio (2011). "A survey and experimental evaluation of image spam filtering techniques".
650:
A 2010 survey of US and
European email users showed that 46% of the respondents had opened spam messages, although only 11% had clicked on a link.
637:
The first known spam email, advertising a DEC product presentation, was sent in 1978 by Gary Thuerk to 600 addresses, the total number of users on
466:
numbers to pay for these accounts. This allows them to move quickly from one account to the next as the host ISPs discover and shut down each one.
2295:
4260:
1599:
437:
In the United States, many states enacted anti-spam laws during the late 1990s and early 2000s. All of these were subsequently superseded by the
164:
users into entering personal information on fake Web sites using emails forged to look like they are from banks or other organizations, such as
1867:
2663:
2775:
2454:
1206:
weaken
Bayesian filters, some spammers, alongside the sales pitch, now include lines of irrelevant, random words, in a technique known as
3590:
the link here is to an abstract of a white paper; registration with the authoring organization is required to obtain the full white paper
2533:
2130:
1144:
In order to send spam, spammers need to obtain the email addresses of the intended recipients. To this end, both spammers themselves and
2879:
2827:
2586:"Spammers Continue Innovation: IronPort Study Shows Image-based Spam, Hit & Run, and Increased Volumes Latest Threat to Your Inbox"
2474:
2638:
354:. A number of large civil settlements have been won in this way, although others have been mostly unsuccessful in collecting damages.
346:
If an individual or organisation can identify harm done to them by spam, and identify who sent it; then they may be able to sue for a
2050:
372:
Finally, in most countries specific legislation is in place to make certain forms of spamming a criminal offence, as outlined below:
1189:. This also allows for many different ways to express a given word, making identifying them all more difficult for filter software.
3820:
3556:
2393:
2360:
3631:
2507:
410:
3340:
2160:
1906:
2754:
1999:
1918:
Journal of Machine Learning Research (special issue on Machine Learning in Computer Security), vol. 7, pp. 2699-2720, 12/2006.
1621:
4034:
3710:
3401:
3375:
2996:
991:
3767:
3531:
2426:
1818:
3022:
2692:
2265:
2249:
957:
4074:
2185:
1966:
4049:
3862:
3122:
2054:
3685:
Dow, K; Serenko, A; Turel, O; Wong, J (2006), "Antecedents and consequences of user satisfaction with email systems",
3099:
2092:
498:
victims report the email address owner to the ISP, for example) a naïve ISP may terminate their service for spamming.
79:
Most email spam messages are commercial in nature. Whether commercial or not, many are not only annoying as a form of
3814:
3505:
1120:
606:
341:
274:
Blank spam may also occur when a spammer forgets or otherwise fails to add the payload when they set up the spam run.
238:
image that does not contain clear text in its initial frame, or to contort the shapes of letters in the image (as in
2781:. Report No. 7 – Third and Fourth quarters 2007. Messaging Anti-Abuse Working Group. April 2008. Archived from
1102:
1028:
588:
3143:
2066:
1550:
2029:
1727:
666:
receives four million emails per year, most of them spam. This was originally incorrectly reported as "per day".
3602:
2714:
1789:
1758:
1675:
4235:
1098:
573:
3269:
3248:
3227:
3206:
3185:
3164:
2337:
1845:
174:. Targeted phishing, where known information about the recipient is used to create forged emails, is known as
119:
in 1978 to 600 people. He was reprimanded and told not to do it again. Now the ban on spam is enforced by the
4250:
3810:
3052:
2957:"2010 MAAWG Email Security Awareness and Usage Report, Messing Anti-Abuse Working Group/Ipsos Public Affairs"
2956:
2833:. Report No. 1 – 4th quarter 2005 Report. Messaging Anti-Abuse Working Group. March 2006. Archived from
1391:
1014:
621:
449:
Many other observers viewed it as having failed, although there have been several high-profile prosecutions.
243:
3311:
3073:
4029:
3911:
3290:
2229:
4255:
1871:
1094:
950:
ranks the top three as the United States, China, and Russia, followed by Japan, Canada, and South Korea.
514:. SMTP forwards mail from one server to another—mail servers that ISPs run commonly require some form of
3652:
3480:
4245:
4069:
3361:
2291:
1437:
1406:
3794:
3431:
1571:
2885:. Report No. 2 – 1st quarter 2006. Messaging Anti-Abuse Working Group. June 2006. Archived from
325:
316:
when rejecting or quarantining email (rather than simply rejecting the attempt to send the message).
3584:
2917:
2865:
2813:
4044:
3941:
3906:
2935:
1401:
1396:
1139:
1083:
1017:), checksumming systems to detect bulk email, and by putting some sort of cost on the sender via a
263:
4265:
2659:
1202:
1087:
584:
2782:
2025:
1846:"Only one in 28 emails legitimate, Sophos report reveals rising tide of spam in April–June 2008"
1148:
gather huge lists of potential email addresses. Since spam is, by definition, unsolicited, this
1052:
When legitimate messages are rejected, the sender needs to contact the recipient out of channel.
84:
3879:
3855:
2448:
1464:
3729:
2585:
3571:
2904:
2886:
2852:
2834:
2800:
2483:
1344:
124:
116:
1055:
When legitimate messages are relegated to a spam folder, the sender is not notified of this.
625:
emanating from them also causes problems for legitimate email servers in the same IP range.
215:, or image-based spam, is an obfuscation method by which text of the message is stored as a
4230:
4084:
4054:
4021:
3130:
1938:
1485:
1381:
1361:
1241:(see below) – a contract with the ISP that allows them to spam without being disconnected.
1034:
1018:
977:
647:
IPwarmup.com study, which also effects legitimate email senders to achieve inbox delivery.
486:, allowing positive identification of the specific account from which an email originates.
438:
361:
statutes is also common, particularly if they illegally accessed other computers to create
351:
3432:"Machine learning for email spam filtering: review, approaches and open research problems"
2634:
8:
4059:
3901:
2190:
1006:
961:
673:, owner of the domain name acme.com, was receiving over one million spam emails per day.
490:
475:
295:
55:
3829:
3800:
3552:
2401:
1942:
2501:
1223:
1207:
258:
Blank spam may be originated in different ways, either intentional or unintentionally:
3802:
Why Am I Getting All This Spam? Unsolicited Commercial Email Research Six Month Report
3627:
3402:"I-005c: E-Mail Spamming countermeasures: Detection and prevention of E-Mail spamming"
2560:"Los Angeles Man, First American Convicted Under Anti-Spam Law, Faces Years in Prison"
906:, the major sources of spam in the fourth quarter of 2008 (October to December) were:
277:
Often blank spam headers appear truncated, suggesting that computer glitches, such as
4225:
4039:
3982:
3848:
3706:
3355:
3332:
1991:
1894:
1591:
1448:
1443:
267:
3840:
3018:
2746:
580:
506:
Spammers frequently seek out and make use of vulnerable third-party systems such as
4180:
4127:
3749:
1946:
1655:
1625:
1583:
956:
As of 13 December 2021, the three networks hosting the most spammers are
947:
329:
301:
120:
96:
3776:
3409:
2988:
1453:
1295:
sent by a person to many other people. The term UCE may be most common in the USA.
1226:
records referenced in spam messages, or a number of specific services as follows:
70:
65:
Since the expense of the spam is borne mostly by the recipient, it is effectively
4192:
4162:
3896:
3700:
3524:
3520:
3379:
3126:
2547:
2422:
2323:
2118:
1950:
1526:
1426:
1356:
998:
526:
522:
507:
471:
313:
192:
80:
3553:"Spamware – Email Address Harvesting Tools and Anonymous Bulk Emailing Software"
3454:
2688:
4240:
4202:
4172:
4122:
4064:
3987:
3977:
3921:
2719:
2684:
1895:"Spam filtering based on the analysis of text information embedded into images"
1587:
1421:
1371:
515:
388:
381:
358:
309:
3021:. ACME Laboratories republication of article appearing in Detroit Free Press.
1572:"Detecting spamming activities in a campus network using incremental learning"
425:, which covers some types of email and phone spam. Penalties are up to 10,000
4219:
4137:
4102:
4002:
3936:
3686:
1595:
1458:
1311:
1302:
1238:
1045:
Measures to protect against spam can cause collateral damage. This includes:
910:
The United States (the origin of 19.8% of spam messages, up from 18.9% in Q3)
889:
670:
659:
426:
422:
305:
278:
224:
3119:
1544:
4185:
4142:
4112:
3962:
3806:
3541:; the referenced page is an auto-redirect target from the original location
1470:
1320:
1292:
1022:
511:
347:
134:. Mainsleaze makes up approximately 3% of the spam sent over the internet.
3501:
1049:
The measures may consume resources, both in the server and on the network.
4147:
3957:
2609:
1500:
1386:
463:
413:(which took effect in 2014) is Canadian legislation meant to fight spam.
66:
59:
1660:
1263:
4117:
4094:
3967:
3926:
3399:
1432:
1162:
663:
212:
207:
142:
Many spam emails contain URLs to a website or websites. According to a
1719:
19:
4152:
4132:
4007:
3606:
3605:. Coalition Against Unsolicited Bulk Email, Australia. Archived from
3291:"Eight times more malicious email attachments spammed out in Q3 2008"
3048:
2358:
2212:
Privacy and Electronic Communications (EC Directive) Regulations 2003
1781:
1750:
1505:
1166:
994:(CIAC) has provided specific countermeasures against email spamming.
643:
483:
157:
24:
3144:"Sophos reveals 'Dirty Dozen' spam producing countries, August 2004"
1072:
591:. Statements consisting only of original research should be removed.
4197:
4107:
3992:
3972:
3871:
3769:
Email Address Harvesting and the Effectiveness of Anti-SPAM Filters
3228:"Sophos reveals 'Dirty Dozen' spam producing countries for Q3 2007"
1955:
Volume 32, Issue 10, 15 July 2011, Pages 1436-1446, ISSN 0167-8655.
1495:
1490:
1416:
1246:
1010:
429:, or 2,000 penalty units for a person other than a body corporate.
366:
170:
151:
143:
88:
51:
3207:"Sophos reveals 'Dirty Dozen' spam producing countries, July 2007"
308:. It happens when email servers are misconfigured to send a bogus
127:(ToS/AUP) of internet service providers (ISPs) and peer pressure.
4079:
3997:
3931:
2294:. Sydney, AU: AustLII, Faculty of Law, University of Technology.
1480:
1475:
1411:
1037:
to prevent "From:" address spoofing became popular in the 2010s.
638:
362:
239:
112:
92:
3270:"Sophos details dirty dozen spam-relaying countries for Q1 2008"
3249:"Sophos details dirty dozen spam-relaying countries for Q4 2007"
2223:
3455:"A Survey of Learning-Based Techniques of Email Spam Filtering"
1366:
1258:
986:
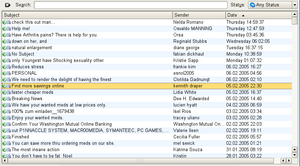
Mozilla Thunderbird alerting a user that an email could be spam
965:
903:
893:
530:
165:
3797:
which contains legislation, analysis, and litigation histories
1646:
Rao, Justin M.; Reiley, David H. (2012), "Economics of Spam",
1001:
based on the content of the email, DNS-based blackhole lists (
4157:
3916:
3476:
1429:, the infamous Dave Rhodes chain letter that jumped to email.
1376:
1331:
1270:
1002:
997:
Some popular methods for filtering and refusing spam include
538:
521:
Increasingly, spammers use networks of malware-infected PCs (
458:
321:
47:
3805:
by Center for Democracy & Technology from the author of
2529:
Six years later, Can Spam act leaves spam problem unresolved
2362:"Trespass to Chattels" Finds New Life In Battle Against Spam
2292:"Commonwealth Consolidated Acts: Spam Act 2003 – Schedule 2"
1927:
Battista Biggio, Giorgio Fumera, Ignazio Pillai, Fabio Roli,
3406:
Computer Incident Advisory Capability Information Bulletins
3186:"Sophos research reveals dirty dozen spam-relaying nations"
2880:"Email Metrics Program: The Network Operators' Perspective"
2828:"Email Metrics Program: The Network Operators' Perspective"
2776:"Email Metrics Program: The Network Operators' Perspective"
2423:"United States set to Legalize Spamming on January 1, 2004"
479:
220:
198:
people who have deliberately withheld their email address.
161:
115:), sending of commercial email was prohibited. Gary Thuerk
3400:
Shawn Hernan; James R. Cutler; David Harris (1997-11-25).
3376:"The Spamhaus Project - the Top 10 Worst Botnet Countries"
2359:
Daniel J. Schwartz; Joseph F. Marinelli (September 2004),
2085:
2068:
Clinton Internet provider wins $ 11B suit against spammer
1868:"Getting it Wrong: Corporate America Spams the Afterlife"
235:
216:
3702:
Inside the spam cartel: trade secrets from the dark side
2931:
1921:
982:
691:
E-mail spam relayed by country in Q2 2007 (% of total)
3555:. MX Logic (abstract hosted by Bit Pipe). 2004-10-01.
3165:"Sophos reveals 'dirty dozen' spam relaying countries"
3100:"Sophos reveals "dirty dozen" spam-relaying countries"
1928:
1570:
Fu, JuiHsi; Lin, PoChing; Lee, SingLing (2014-08-01).
445:
almost immediately dubbing it the "You Can Spam" Act.
3870:
3705:, Elsevier/Syngress; 1st edition, November 27, 2004.
1885:
1327:
Final, Ultimate Solution for the Spam Problem (FUSSP)
320:
email backscatter can end up being listed on various
3628:"Vernon Schryver: You Might Be An Anti-Spam Kook If"
3408:. United States Department of Energy. Archived from
2924:
926:
When grouped by continents, spam comes mostly from:
3730:"Can the Spam: How Spam is Bad for the Environment"
3684:
3312:"Spammers defy Bill Gates's death-of-spam prophecy"
2267:
Canada's Anti-spam Bill C-28 is the Law of the Land
2131:"Bronx man, 'leader' of bank-fraud scam, convicted"
518:to ensure that the user is a customer of that ISP.
2317:Hypertouch v. ValueClick, Inc. et al., Cal.App.4th
653:
392:options to be determined by national legislation.
385:Directive on Privacy and Electronic Communications
234:A newer technique, however, is to use an animated
2476:Effectiveness and Enforcement of the CAN-SPAM Act
4217:
2715:"Email spam level bounces back after record low"
2339:PUBLIC LAW 108-187--DEC. 16, 2003 117 STAT. 2699
1817:(Press release). Sophos Cyberoam. Archived from
1321:Opt-in, confirmed opt-in, double opt-in, opt-out
1317:Opt-in, confirmed opt-in, double opt-in, opt-out
357:Criminal prosecution of spammers under fraud or
2677:
3795:The Electronic Frontier Foundation's spam page
3474:
2683:
1964:
1782:"Companies that spam, and ESPs that help them"
1156:
83:, but also dangerous because they may contain
3856:
3046:
3016:
2712:
2632:
2588:(Press release). IronPort Systems. 2006-06-28
1196:
1013:, enforcing technical requirements of email (
3761:Government reports and industry white papers
3339:. dynamic report. The Spamhaus Project Ltd.
2604:
2602:
2186:"Top Spammer Sentenced to Nearly Four Years"
1773:
1619:
1576:Journal of Network and Computer Applications
300:Backscatter is a side-effect of email spam,
3468:
1891:Giorgio Fumera, Ignazio Pillai, Fabio Roli,
1257:are commonly advertised in spam. These are
1101:. Unsourced material may be challenged and
628:
16:Unsolicited electronic advertising by email
3863:
3849:
3494:
3325:
2635:"Spam Decreased 82.22% Over The Past Year"
2499:
1958:
1840:
1838:
1314:is advertising through the medium of spam.
896:can be traced to fewer than 200 spammers.
46:, is unsolicited messages sent in bulk by
3452:
2872:
2820:
2768:
2599:
2051:CompuServe Inc. v. Cyber Promotions, Inc.
1676:"Getting Started Computing at the AI Lab"
1659:
1645:
1613:
1133:
1121:Learn how and when to remove this message
607:Learn how and when to remove this message
69:advertising. Thus, it is an example of a
3688:International Journal of e-Collaboration
3304:
2578:
1865:
1804:
1667:
1569:
1537:
1213:
981:
335:
18:
3545:
3283:
3262:
3241:
3220:
3199:
3178:
3157:
3136:
2615:(Press release). Commtouch Software Ltd
2610:"Q1 2010 Internet Threats Trend Report"
2251:Fighting Internet and Wireless Spam Act
2002:from the original on September 23, 2015
1967:"Image spam paints a troubling picture"
1835:
1812:"Q1 2014 Internet Threats Trend Report"
1724:Internet and e-mail policy and practice
1324:added to the list without verification.
971:
533:(such zombifying malware is known as a
411:Fighting Internet and Wireless Spam Act
4261:Promotion and marketing communications
4218:
3462:University of Trento Technical Reports
2744:
2391:
2161:"'Spam King' pleads guilty in Detroit"
1892:
1717:
1229:Some Internet hosting firms advertise
1062:
939:South America (12.9%, down from 13.2%)
452:
111:At the beginning of the Internet (the
3844:
3822:Spam White Paper – Drowning in Sewage
3595:
3040:
3010:
2986:
2394:"The 'Yes, You Can Spam' Act of 2003"
1779:
1748:
1711:
1276:
992:Computer Incident Advisory Capability
474:of email addresses (much easier than
137:
3775:, United States: FTC, archived from
3504:. The Spamhaus Project. 2006-12-22.
3429:
3393:
3019:"Ballmer checks out my spam problem"
2566:from the original on 10 January 2019
2429:from the original on 12 January 2012
2368:, Association of Corporate Counsel,
1899:Journal of Machine Learning Research
1624:. The ClickZ Network. Archived from
1099:adding citations to reliable sources
1066:
1040:
933:North America (23.6%, up from 21.8%)
556:
231:such as a box that has words on it.
91:web sites or sites that are hosting
3699:Sjouwerman, Stu; Posluns, Jeffrey,
3502:"SBL Policy & Listing Criteria"
3314:(Press release). Sophos. 2009-01-22
3293:(Press release). Sophos. 2008-10-27
3272:(Press release). Sophos. 2008-04-14
3251:(Press release). Sophos. 2008-02-11
3230:(Press release). Sophos. 2007-10-24
3209:(Press release). Sophos. 2007-07-18
3188:(Press release). Sophos. 2007-04-11
3167:(Press release). Sophos. 2006-07-24
3146:(Press release). Sophos. 2004-08-24
2980:
1848:(Press release). Sophos. 2008-07-15
1506:SPIT (SPam over Internet Telephony)
944:In terms of number of IP addresses:
501:
289:
262:Blank spam can have been sent in a
13:
4050:Distributed Checksum Clearinghouse
3678:
3453:Blanzieri, Enrico (January 2008).
3097:
3017:Mike Wendland (December 2, 2004).
2989:"Bill Gates 'most spammed person'"
2706:
2689:"Reaction to the DEC Spam of 1978"
2532:, USA: SC Magazine, archived from
2326:(Google Scholar: January 18, 2011)
2055:School of Visual Arts v. Kuprewicz
1870:. Clueless Mailers. Archived from
1792:from the original on April 1, 2019
1761:from the original on April 1, 2019
1730:from the original on April 1, 2019
1288:Unsolicited commercial email (UCE)
457:Spammers may engage in deliberate
369:or other forms of criminal fraud.
181:
14:
4277:
4035:Challenge–response spam filtering
3872:Unsolicited digital communication
3717:
3337:Spamhaus Blocklist (SBL) database
3333:"Spamhaus Statistics: The Top 10"
3120:Register of Known Spam Operations
2713:Josh Halliday (10 January 2011).
2141:from the original on 8 March 2019
1718:Levine, John (October 18, 2011).
1673:
1622:"Make Spammers Pay Before You Do"
685:
634:delete or reject "obvious spam".
395:
375:
342:Email spam legislation by country
117:sent the first email spam message
27:folder filled with spam messages.
3464:(Technical Report # DIT-06-056).
2747:"Spam overwhelms email messages"
2392:Foster, Ed (November 24, 2003).
2336:"SEC. 8. EFFECT ON OTHER LAWS",
1648:Journal of Economic Perspectives
1169:, as in the following examples:
1071:
561:
489:Senders cannot completely spoof
432:
3751:Worldwide Email Threat Activity
3663:from the original on 2008-05-15
3645:
3634:from the original on 2012-10-14
3620:
3559:from the original on 2007-01-23
3534:from the original on 2004-10-10
3508:from the original on 2007-01-05
3483:from the original on 2014-08-11
3446:
3423:
3368:
3343:from the original on 2007-01-10
3113:
3091:
3080:from the original on 2007-09-04
3066:
3055:from the original on 2010-09-17
3025:from the original on 2010-09-17
2999:from the original on 2011-05-02
2969:from the original on 2013-03-08
2949:
2938:from the original on 2018-10-21
2757:from the original on 2012-12-02
2738:
2727:from the original on 2015-04-03
2695:from the original on 2013-07-30
2666:from the original on 2012-12-14
2652:
2641:from the original on 2012-12-13
2626:
2552:
2540:
2520:
2510:from the original on 2011-09-11
2493:
2467:
2457:from the original on 2008-03-15
2441:
2415:
2385:
2375:from the original on 2019-02-12
2352:
2329:
2309:
2298:from the original on 2011-05-18
2284:
2274:from the original on 2011-03-24
2258:
2242:
2232:from the original on 2014-01-16
2216:
2205:
2178:
2167:from the original on 2009-06-26
2153:
2123:
2111:
2101:from the original on 2012-08-06
2075:from the original on 2018-06-14
2059:
2043:
2014:
1984:
1973:from the original on 2007-02-24
1909:from the original on 2015-02-21
1859:
1688:from the original on 2019-03-23
1602:from the original on 2020-04-30
1553:from the original on 2014-09-26
936:Europe (23.4%, down from 23.9%)
676:
654:Highest amount of spam received
552:
387:(2002/58/EC) provides that the
3828:, Pegasus Mail, archived from
3430:Dada, Emmanuel Gbenga (2019).
1742:
1699:
1639:
1620:Rebecca Lieb (July 26, 2002).
1563:
1519:
990:The U.S. Department of Energy
1:
3811:Mercury Mail Transport System
3694:, vol. 2, pp. 46–64
3603:"Definitions of Words We Use"
3475:Sapient Fridge (2005-07-08).
2745:Waters, Darren (2009-04-08).
1965:Eric B. Parizo (2006-07-26).
1866:Bob West (January 19, 2008).
1512:
1392:Direct Marketing Associations
930:Asia (37.8%, down from 39.8%)
922:Turkey (4.4%, down from 8.2%)
916:Russia (6.4%, down from 8.3%)
622:Forward-confirmed reverse DNS
249:
244:optical character recognition
201:
3047:Jef Poskanzer (2006-05-15).
2662:(in Dutch). Symantec.cloud.
2633:Charlie White (2011-07-04).
2500:Ken Fisher (December 2005),
2450:Is the CAN-SPAM Law Working?
2071:, QC Times, 4 January 2006,
1951:10.1016/j.patrec.2011.03.022
1527:"Merriam Webster Dictionary"
1282:Unsolicited bulk email (UBE)
416:
186:
7:
1931:Pattern Recognition Letters
1349:
1157:Obfuscating message content
919:Brazil (6.3%, up from 4.5%)
900:In terms of volume of spam:
662:in 2004, Microsoft founder
587:the claims made and adding
529:networks are also known as
106:
95:or include malware as file
10:
4282:
4070:Naive Bayes spam filtering
2987:Staff (18 November 2004).
2503:US FTC says CAN-SPAM works
2482:, USA: FTC, archived from
2094:AOL gives up treasure hunt
1751:"What is Mainsleaze Spam?"
1588:10.1016/j.jnca.2014.03.010
1438:news.admin.net-abuse.email
1407:Gordon v. Virtumundo, Inc.
1342:
1338:
1266:is no longer substantial.
1264:amount you can fit on a CD
1197:Defeating Bayesian filters
1137:
975:
913:China (9.9%, up from 5.4%)
339:
326:internet service providers
293:
205:
190:
156:Spam is also a medium for
149:
4171:
4093:
4020:
3950:
3887:
3878:
3518:original location was at
2270:, Circle ID, 2010-12-15,
1992:"Dealing with blank spam"
1454:Pump-and-dump stock fraud
1285:A synonym for email spam.
871:
857:
843:
829:
815:
801:
787:
773:
759:
745:
731:
717:
703:
698:
695:
642:unwanted, according to a
404:
58:in which the name of the
54:). The name comes from a
4045:Disposable email address
3907:Directory harvest attack
1893:Fumera, Giorgio (2006).
1706:Opening Pandora's In-Box
1402:Email address harvesting
1397:Disposable email address
1244:A few companies produce
1140:Email address harvesting
1029:Outbound spam protection
629:Statistics and estimates
264:directory harvest attack
242:) to avoid detection by
60:canned pork product Spam
2562:. AP. 17 January 2007.
478:). The email protocol (
350:, e.g. on the basis of
324:and be in violation of
3579:Cite journal requires
3477:"Spamware vendor list"
3360:: CS1 maint: others (
2932:"IPWarmup.com - Study"
2912:Cite journal requires
2860:Cite journal requires
2808:Cite journal requires
1780:Jefferson, Catherine.
1749:Jefferson, Catherine.
1465:SPAMasterpiece Theater
1134:Gathering of addresses
987:
525:) to send their spam.
34:, also referred to as
28:
4236:Advertising by medium
3074:"Spam Costs Billions"
3051:. ACME Laboratories.
2398:The Gripe Line Weblog
1998:. September 2, 2009.
1720:"The Mainsleaze Blog"
1345:History of email spam
1220:spam-support services
1214:Spam-support services
985:
954:In terms of networks:
365:, or the emails were
336:Legal countermeasures
125:Acceptable Use Policy
22:
4251:Marketing techniques
4055:Email authentication
2137:. 26 February 2016.
1674:Stacy, Christopher.
1549:, M3AAWG, Nov 2014,
1546:Email metrics report
1382:CAN-SPAM Act of 2003
1362:Anti-spam techniques
1095:improve this section
1035:Email authentication
1019:proof-of-work system
978:Anti-spam techniques
972:Anti-spam techniques
732:China (+ Hong Kong)
439:CAN-SPAM Act of 2003
352:trespass to chattels
71:negative externality
3902:Bulk email software
3754:, Barracuda Central
2840:on December 8, 2006
2489:on January 10, 2006
2163:. UPI. 2009-06-23.
1969:. Search Security.
1943:2011PaReL..32.1436B
1824:on 24 February 2021
1786:The Mainsleaze Blog
1755:The Mainsleaze Blog
1661:10.1257/jep.26.3.87
1235:bulletproof hosting
1063:Methods of spammers
692:
476:IP address spoofing
453:Deception and fraud
296:Backscatter (email)
168:. This is known as
56:Monty Python sketch
4256:Online advertising
3125:2007-06-12 at the
2691:. Brad Templeton.
2322:2017-04-15 at the
1277:Related vocabulary
1208:Bayesian poisoning
1203:Bayesian filtering
1150:address harvesting
988:
690:
572:possibly contains
380:Article 13 of the
138:Spamvertised sites
29:
4246:Digital marketing
4213:
4212:
4040:Context filtering
4016:
4015:
3711:978-1-932266-86-3
2097:, Boston Herald,
1937:(10): 1436–1446.
1905:(98): 2699–2720.
1874:on April 14, 2013
1449:Project Honey Pot
1131:
1130:
1123:
1041:Collateral damage
885:
884:
669:At the same time
617:
616:
609:
574:original research
268:dictionary attack
4273:
4181:Advance-fee scam
4128:Keyword stuffing
3885:
3884:
3865:
3858:
3851:
3842:
3841:
3836:
3834:
3827:
3790:
3789:
3787:
3781:
3774:
3755:
3737:
3695:
3693:
3672:
3671:
3669:
3668:
3649:
3643:
3642:
3640:
3639:
3630:. Rhyolite.com.
3624:
3618:
3617:
3615:
3614:
3599:
3593:
3588:
3582:
3577:
3575:
3567:
3565:
3564:
3549:
3543:
3540:
3539:
3522:
3516:
3514:
3513:
3498:
3492:
3491:
3489:
3488:
3472:
3466:
3465:
3459:
3450:
3444:
3443:
3427:
3421:
3420:
3418:
3417:
3397:
3391:
3390:
3388:
3387:
3378:. Archived from
3372:
3366:
3365:
3359:
3351:
3349:
3348:
3329:
3323:
3322:
3320:
3319:
3308:
3302:
3301:
3299:
3298:
3287:
3281:
3280:
3278:
3277:
3266:
3260:
3259:
3257:
3256:
3245:
3239:
3238:
3236:
3235:
3224:
3218:
3217:
3215:
3214:
3203:
3197:
3196:
3194:
3193:
3182:
3176:
3175:
3173:
3172:
3161:
3155:
3154:
3152:
3151:
3140:
3134:
3117:
3111:
3110:
3108:
3107:
3095:
3089:
3088:
3086:
3085:
3070:
3064:
3063:
3061:
3060:
3049:"Mail Filtering"
3044:
3038:
3033:
3031:
3030:
3014:
3008:
3007:
3005:
3004:
2984:
2978:
2977:
2975:
2974:
2968:
2961:
2953:
2947:
2946:
2944:
2943:
2928:
2922:
2921:
2915:
2910:
2908:
2900:
2898:
2897:
2891:
2884:
2876:
2870:
2869:
2863:
2858:
2856:
2848:
2846:
2845:
2839:
2832:
2824:
2818:
2817:
2811:
2806:
2804:
2796:
2794:
2793:
2787:
2780:
2772:
2766:
2765:
2763:
2762:
2742:
2736:
2735:
2733:
2732:
2710:
2704:
2703:
2701:
2700:
2687:(8 March 2005).
2681:
2675:
2674:
2672:
2671:
2656:
2650:
2649:
2647:
2646:
2637:. Mashable.com.
2630:
2624:
2623:
2621:
2620:
2614:
2606:
2597:
2596:
2594:
2593:
2582:
2576:
2575:
2573:
2571:
2556:
2550:
2544:
2538:
2537:
2524:
2518:
2517:
2516:
2515:
2506:, Ars Technica,
2497:
2491:
2490:
2488:
2481:
2471:
2465:
2464:
2463:
2462:
2445:
2439:
2438:
2436:
2434:
2425:. Spamhaus.org.
2419:
2413:
2412:
2410:
2409:
2400:. Archived from
2389:
2383:
2382:
2381:
2380:
2374:
2367:
2356:
2350:
2349:
2344:
2333:
2327:
2313:
2307:
2306:
2304:
2303:
2288:
2282:
2281:
2280:
2279:
2262:
2256:
2255:
2246:
2240:
2239:
2238:
2237:
2220:
2214:
2209:
2203:
2202:
2200:
2199:
2182:
2176:
2175:
2173:
2172:
2157:
2151:
2150:
2148:
2146:
2127:
2121:
2115:
2109:
2108:
2107:
2106:
2089:
2083:
2082:
2081:
2080:
2063:
2057:
2047:
2041:
2040:
2038:
2037:
2028:. Archived from
2018:
2012:
2011:
2009:
2007:
1988:
1982:
1981:
1979:
1978:
1962:
1956:
1954:
1925:
1919:
1917:
1915:
1914:
1889:
1883:
1882:
1880:
1879:
1863:
1857:
1856:
1854:
1853:
1842:
1833:
1832:
1830:
1829:
1823:
1816:
1808:
1802:
1801:
1799:
1797:
1777:
1771:
1770:
1768:
1766:
1746:
1740:
1739:
1737:
1735:
1715:
1709:
1703:
1697:
1696:
1694:
1693:
1687:
1680:
1671:
1665:
1664:
1663:
1643:
1637:
1636:
1634:
1633:
1617:
1611:
1610:
1608:
1607:
1567:
1561:
1560:
1559:
1558:
1541:
1535:
1534:
1523:
1188:
1184:
1180:
1176:
1172:
1126:
1119:
1115:
1112:
1106:
1075:
1067:
948:Spamhaus Project
880:
879:
866:
865:
852:
851:
838:
837:
824:
823:
810:
809:
796:
795:
782:
781:
768:
767:
754:
753:
740:
739:
726:
725:
712:
711:
693:
689:
612:
605:
601:
598:
592:
589:inline citations
565:
564:
557:
508:open mail relays
502:Theft of service
330:Terms of Service
290:Backscatter spam
121:Terms of Service
4281:
4280:
4276:
4275:
4274:
4272:
4271:
4270:
4216:
4215:
4214:
4209:
4193:Make Money Fast
4167:
4163:URL redirection
4089:
4012:
3946:
3897:Address munging
3874:
3869:
3832:
3825:
3819:
3785:
3783:
3779:
3772:
3766:
3748:
3736:, June 15, 2009
3728:
3720:
3691:
3681:
3679:Further reading
3676:
3675:
3666:
3664:
3651:
3650:
3646:
3637:
3635:
3626:
3625:
3621:
3612:
3610:
3601:
3600:
3596:
3580:
3578:
3569:
3568:
3562:
3560:
3551:
3550:
3546:
3537:
3535:
3519:
3511:
3509:
3500:
3499:
3495:
3486:
3484:
3479:. Spam Sights.
3473:
3469:
3457:
3451:
3447:
3428:
3424:
3415:
3413:
3398:
3394:
3385:
3383:
3374:
3373:
3369:
3353:
3352:
3346:
3344:
3331:
3330:
3326:
3317:
3315:
3310:
3309:
3305:
3296:
3294:
3289:
3288:
3284:
3275:
3273:
3268:
3267:
3263:
3254:
3252:
3247:
3246:
3242:
3233:
3231:
3226:
3225:
3221:
3212:
3210:
3205:
3204:
3200:
3191:
3189:
3184:
3183:
3179:
3170:
3168:
3163:
3162:
3158:
3149:
3147:
3142:
3141:
3137:
3127:Wayback Machine
3118:
3114:
3105:
3103:
3102:(Press release)
3096:
3092:
3083:
3081:
3072:
3071:
3067:
3058:
3056:
3045:
3041:
3028:
3026:
3015:
3011:
3002:
3000:
2985:
2981:
2972:
2970:
2966:
2959:
2955:
2954:
2950:
2941:
2939:
2930:
2929:
2925:
2913:
2911:
2902:
2901:
2895:
2893:
2889:
2882:
2878:
2877:
2873:
2861:
2859:
2850:
2849:
2843:
2841:
2837:
2830:
2826:
2825:
2821:
2809:
2807:
2798:
2797:
2791:
2789:
2785:
2778:
2774:
2773:
2769:
2760:
2758:
2743:
2739:
2730:
2728:
2711:
2707:
2698:
2696:
2682:
2678:
2669:
2667:
2658:
2657:
2653:
2644:
2642:
2631:
2627:
2618:
2616:
2612:
2608:
2607:
2600:
2591:
2589:
2584:
2583:
2579:
2569:
2567:
2558:
2557:
2553:
2548:Oleg Nikolaenko
2545:
2541:
2526:
2525:
2521:
2513:
2511:
2498:
2494:
2486:
2479:
2473:
2472:
2468:
2460:
2458:
2447:
2446:
2442:
2432:
2430:
2421:
2420:
2416:
2407:
2405:
2390:
2386:
2378:
2376:
2372:
2365:
2357:
2353:
2342:
2335:
2334:
2330:
2324:Wayback Machine
2315:But see, e.g.,
2314:
2310:
2301:
2299:
2290:
2289:
2285:
2277:
2275:
2264:
2263:
2259:
2248:
2247:
2243:
2235:
2233:
2222:
2221:
2217:
2210:
2206:
2197:
2195:
2184:
2183:
2179:
2170:
2168:
2159:
2158:
2154:
2144:
2142:
2129:
2128:
2124:
2119:Sanford Wallace
2116:
2112:
2104:
2102:
2091:
2090:
2086:
2078:
2076:
2065:
2064:
2060:
2048:
2044:
2035:
2033:
2020:
2019:
2015:
2005:
2003:
1990:
1989:
1985:
1976:
1974:
1963:
1959:
1926:
1922:
1912:
1910:
1890:
1886:
1877:
1875:
1864:
1860:
1851:
1849:
1844:
1843:
1836:
1827:
1825:
1821:
1814:
1810:
1809:
1805:
1795:
1793:
1778:
1774:
1764:
1762:
1747:
1743:
1733:
1731:
1716:
1712:
1704:
1700:
1691:
1689:
1685:
1678:
1672:
1668:
1644:
1640:
1631:
1629:
1618:
1614:
1605:
1603:
1568:
1564:
1556:
1554:
1543:
1542:
1538:
1531:Merriam-Webster
1525:
1524:
1520:
1515:
1510:
1427:Make money fast
1357:Address munging
1352:
1347:
1341:
1279:
1216:
1199:
1186:
1182:
1178:
1174:
1170:
1159:
1142:
1136:
1127:
1116:
1110:
1107:
1092:
1076:
1065:
1043:
999:email filtering
980:
974:
881:
877:
876:
867:
863:
862:
853:
849:
848:
844:United Kingdom
839:
835:
834:
825:
821:
820:
811:
807:
806:
797:
793:
792:
783:
779:
778:
769:
765:
764:
755:
751:
750:
741:
737:
736:
727:
723:
722:
713:
709:
708:
688:
679:
656:
631:
613:
602:
596:
593:
578:
566:
562:
555:
504:
455:
435:
419:
407:
398:
378:
344:
338:
314:envelope sender
298:
292:
252:
210:
204:
195:
193:Email appending
189:
184:
182:Spam techniques
154:
140:
109:
81:attention theft
17:
12:
11:
5:
4279:
4269:
4268:
4266:Internet fraud
4263:
4258:
4253:
4248:
4243:
4238:
4233:
4228:
4211:
4210:
4208:
4207:
4206:
4205:
4195:
4190:
4189:
4188:
4177:
4175:
4173:Internet fraud
4169:
4168:
4166:
4165:
4160:
4155:
4150:
4145:
4140:
4135:
4130:
4125:
4123:Google bombing
4120:
4115:
4110:
4105:
4099:
4097:
4091:
4090:
4088:
4087:
4082:
4077:
4072:
4067:
4065:List poisoning
4062:
4057:
4052:
4047:
4042:
4037:
4032:
4026:
4024:
4018:
4017:
4014:
4013:
4011:
4010:
4005:
4000:
3995:
3990:
3985:
3980:
3975:
3970:
3965:
3960:
3954:
3952:
3948:
3947:
3945:
3944:
3939:
3934:
3929:
3924:
3922:Email spoofing
3919:
3914:
3909:
3904:
3899:
3893:
3891:
3882:
3876:
3875:
3868:
3867:
3860:
3853:
3845:
3839:
3838:
3817:
3798:
3792:
3758:
3757:
3740:
3739:
3719:
3718:External links
3716:
3715:
3714:
3697:
3680:
3677:
3674:
3673:
3644:
3619:
3594:
3581:|journal=
3544:
3493:
3467:
3445:
3422:
3392:
3367:
3324:
3303:
3282:
3261:
3240:
3219:
3198:
3177:
3156:
3135:
3112:
3090:
3065:
3039:
3009:
2979:
2948:
2923:
2914:|journal=
2871:
2862:|journal=
2819:
2810:|journal=
2767:
2737:
2720:guardian.co.uk
2705:
2685:Brad Templeton
2676:
2651:
2625:
2598:
2577:
2551:
2539:
2519:
2492:
2466:
2440:
2414:
2384:
2351:
2328:
2308:
2283:
2257:
2241:
2215:
2204:
2177:
2152:
2122:
2110:
2084:
2058:
2042:
2013:
1983:
1957:
1920:
1884:
1858:
1834:
1803:
1772:
1741:
1710:
1698:
1666:
1638:
1612:
1562:
1536:
1517:
1516:
1514:
1511:
1509:
1508:
1503:
1498:
1493:
1488:
1483:
1478:
1473:
1468:
1461:
1456:
1451:
1446:
1441:
1435:
1430:
1424:
1422:List poisoning
1419:
1414:
1409:
1404:
1399:
1394:
1389:
1384:
1379:
1374:
1372:Boulder Pledge
1369:
1364:
1359:
1353:
1351:
1348:
1343:Main article:
1340:
1337:
1336:
1335:
1328:
1325:
1318:
1315:
1309:
1306:
1299:
1296:
1289:
1286:
1283:
1278:
1275:
1271:DNS blacklists
1215:
1212:
1198:
1195:
1158:
1155:
1146:list merchants
1138:Main article:
1135:
1132:
1129:
1128:
1079:
1077:
1070:
1064:
1061:
1060:
1059:
1056:
1053:
1050:
1042:
1039:
976:Main article:
973:
970:
941:
940:
937:
934:
931:
924:
923:
920:
917:
914:
911:
883:
882:
875:
873:
869:
868:
861:
859:
855:
854:
847:
845:
841:
840:
833:
831:
827:
826:
819:
817:
813:
812:
805:
803:
799:
798:
791:
789:
785:
784:
777:
775:
771:
770:
763:
761:
757:
756:
749:
747:
743:
742:
735:
733:
729:
728:
721:
719:
715:
714:
707:
705:
704:United States
701:
700:
697:
687:
686:Origin of spam
684:
678:
675:
655:
652:
630:
627:
615:
614:
569:
567:
560:
554:
551:
516:authentication
503:
500:
491:email delivery
454:
451:
434:
431:
418:
415:
406:
403:
397:
396:United Kingdom
394:
382:European Union
377:
376:European Union
374:
359:computer crime
337:
334:
310:bounce message
294:Main article:
291:
288:
287:
286:
282:
275:
272:
251:
248:
206:Main article:
203:
200:
191:Main article:
188:
185:
183:
180:
176:spear-phishing
150:Main article:
139:
136:
108:
105:
15:
9:
6:
4:
3:
2:
4278:
4267:
4264:
4262:
4259:
4257:
4254:
4252:
4249:
4247:
4244:
4242:
4239:
4237:
4234:
4232:
4229:
4227:
4224:
4223:
4221:
4204:
4201:
4200:
4199:
4196:
4194:
4191:
4187:
4184:
4183:
4182:
4179:
4178:
4176:
4174:
4170:
4164:
4161:
4159:
4156:
4154:
4151:
4149:
4146:
4144:
4141:
4139:
4138:Referrer spam
4136:
4134:
4131:
4129:
4126:
4124:
4121:
4119:
4116:
4114:
4111:
4109:
4106:
4104:
4101:
4100:
4098:
4096:
4092:
4086:
4083:
4081:
4078:
4076:
4073:
4071:
4068:
4066:
4063:
4061:
4058:
4056:
4053:
4051:
4048:
4046:
4043:
4041:
4038:
4036:
4033:
4031:
4028:
4027:
4025:
4023:
4019:
4009:
4006:
4004:
4003:Telemarketing
4001:
3999:
3996:
3994:
3991:
3989:
3986:
3984:
3981:
3979:
3976:
3974:
3971:
3969:
3966:
3964:
3961:
3959:
3956:
3955:
3953:
3949:
3943:
3940:
3938:
3937:Pink contract
3935:
3933:
3930:
3928:
3925:
3923:
3920:
3918:
3915:
3913:
3910:
3908:
3905:
3903:
3900:
3898:
3895:
3894:
3892:
3890:
3886:
3883:
3881:
3877:
3873:
3866:
3861:
3859:
3854:
3852:
3847:
3846:
3843:
3835:on 2007-11-28
3831:
3824:
3823:
3818:
3816:
3812:
3808:
3804:
3803:
3799:
3796:
3793:
3782:on 2007-11-28
3778:
3771:
3770:
3765:
3764:
3763:
3762:
3753:
3752:
3747:
3746:
3745:
3744:
3735:
3734:The Economist
3731:
3727:
3726:
3725:
3724:
3712:
3708:
3704:
3703:
3698:
3690:
3689:
3683:
3682:
3662:
3658:
3654:
3648:
3633:
3629:
3623:
3609:on 2007-01-06
3608:
3604:
3598:
3591:
3586:
3573:
3558:
3554:
3548:
3542:
3533:
3528:
3527:
3525:SBL rationale
3523:
3521:
3507:
3503:
3497:
3482:
3478:
3471:
3463:
3456:
3449:
3441:
3437:
3433:
3426:
3412:on 2007-01-04
3411:
3407:
3403:
3396:
3382:on 2021-10-22
3381:
3377:
3371:
3363:
3357:
3342:
3338:
3334:
3328:
3313:
3307:
3292:
3286:
3271:
3265:
3250:
3244:
3229:
3223:
3208:
3202:
3187:
3181:
3166:
3160:
3145:
3139:
3132:
3128:
3124:
3121:
3116:
3101:
3094:
3079:
3075:
3069:
3054:
3050:
3043:
3036:
3024:
3020:
3013:
2998:
2994:
2990:
2983:
2965:
2958:
2952:
2937:
2933:
2927:
2919:
2906:
2892:on 2006-09-24
2888:
2881:
2875:
2867:
2854:
2836:
2829:
2823:
2815:
2802:
2788:on 2008-07-24
2784:
2777:
2771:
2756:
2752:
2748:
2741:
2726:
2722:
2721:
2716:
2709:
2694:
2690:
2686:
2680:
2665:
2661:
2655:
2640:
2636:
2629:
2611:
2605:
2603:
2587:
2581:
2565:
2561:
2555:
2549:
2543:
2536:on 2010-09-03
2535:
2531:
2530:
2523:
2509:
2505:
2504:
2496:
2485:
2478:
2477:
2470:
2456:
2452:
2451:
2444:
2428:
2424:
2418:
2404:on 2007-04-06
2403:
2399:
2395:
2388:
2371:
2364:
2363:
2355:
2348:
2341:
2340:
2332:
2325:
2321:
2318:
2312:
2297:
2293:
2287:
2273:
2269:
2268:
2261:
2253:
2252:
2245:
2231:
2227:
2226:
2219:
2213:
2208:
2193:
2192:
2187:
2181:
2166:
2162:
2156:
2140:
2136:
2132:
2126:
2120:
2114:
2100:
2096:
2095:
2088:
2074:
2070:
2069:
2062:
2056:
2052:
2046:
2032:on 2012-11-20
2031:
2027:
2023:
2017:
2001:
1997:
1993:
1987:
1972:
1968:
1961:
1952:
1948:
1944:
1940:
1936:
1932:
1924:
1908:
1904:
1900:
1896:
1888:
1873:
1869:
1862:
1847:
1841:
1839:
1820:
1813:
1807:
1791:
1787:
1783:
1776:
1760:
1756:
1752:
1745:
1729:
1725:
1721:
1714:
1707:
1702:
1684:
1677:
1670:
1662:
1657:
1654:(3): 87–110,
1653:
1649:
1642:
1628:on 2007-08-07
1627:
1623:
1616:
1601:
1597:
1593:
1589:
1585:
1581:
1577:
1573:
1566:
1552:
1548:
1547:
1540:
1532:
1528:
1522:
1518:
1507:
1504:
1502:
1499:
1497:
1494:
1492:
1489:
1487:
1484:
1482:
1479:
1477:
1474:
1472:
1469:
1467:
1466:
1462:
1460:
1459:Shotgun email
1457:
1455:
1452:
1450:
1447:
1445:
1444:Nigerian spam
1442:
1439:
1436:
1434:
1431:
1428:
1425:
1423:
1420:
1418:
1415:
1413:
1410:
1408:
1405:
1403:
1400:
1398:
1395:
1393:
1390:
1388:
1385:
1383:
1380:
1378:
1375:
1373:
1370:
1368:
1365:
1363:
1360:
1358:
1355:
1354:
1346:
1333:
1329:
1326:
1322:
1319:
1316:
1313:
1312:Spamvertising
1310:
1308:Spamvertising
1307:
1304:
1303:pink contract
1300:
1298:Pink contract
1297:
1294:
1293:chain letters
1290:
1287:
1284:
1281:
1280:
1274:
1272:
1267:
1265:
1260:
1256:
1251:
1249:
1248:
1242:
1240:
1239:pink contract
1236:
1232:
1231:bulk-friendly
1227:
1225:
1221:
1211:
1209:
1204:
1194:
1190:
1168:
1164:
1154:
1151:
1147:
1141:
1125:
1122:
1114:
1111:November 2011
1104:
1100:
1096:
1090:
1089:
1085:
1080:This section
1078:
1074:
1069:
1068:
1057:
1054:
1051:
1048:
1047:
1046:
1038:
1036:
1032:
1030:
1026:
1024:
1020:
1016:
1012:
1008:
1004:
1000:
995:
993:
984:
979:
969:
967:
963:
959:
955:
951:
949:
945:
938:
935:
932:
929:
928:
927:
921:
918:
915:
912:
909:
908:
907:
905:
902:According to
901:
897:
895:
891:
890:North America
874:
870:
860:
856:
846:
842:
832:
828:
818:
814:
804:
800:
790:
786:
776:
772:
762:
758:
748:
744:
734:
730:
720:
716:
706:
702:
694:
683:
674:
672:
671:Jef Poskanzer
667:
665:
661:
660:Steve Ballmer
658:According to
651:
648:
645:
640:
635:
626:
623:
611:
608:
600:
590:
586:
582:
576:
575:
570:This article
568:
559:
558:
550:
546:
542:
540:
536:
532:
528:
524:
519:
517:
513:
512:proxy servers
509:
499:
495:
492:
487:
485:
481:
477:
473:
467:
465:
460:
450:
446:
442:
440:
433:United States
430:
428:
427:penalty units
424:
423:Spam Act 2003
414:
412:
402:
393:
390:
386:
383:
373:
370:
368:
364:
360:
355:
353:
349:
343:
333:
331:
327:
323:
317:
315:
311:
307:
303:
297:
283:
280:
279:software bugs
276:
273:
269:
265:
261:
260:
259:
256:
247:
245:
241:
237:
232:
228:
226:
225:pump and dump
222:
218:
214:
209:
199:
194:
179:
177:
173:
172:
167:
163:
159:
153:
148:
145:
135:
133:
128:
126:
122:
118:
114:
104:
100:
98:
94:
90:
87:that lead to
86:
82:
77:
74:
72:
68:
63:
61:
57:
53:
49:
45:
41:
37:
33:
26:
21:
4186:Lottery scam
4143:Scraper site
4113:Doorway page
3983:Mobile phone
3963:Cold calling
3888:
3830:the original
3821:
3815:David Harris
3807:Pegasus Mail
3801:
3784:, retrieved
3777:the original
3768:
3760:
3759:
3750:
3743:Spam reports
3742:
3741:
3733:
3722:
3721:
3701:
3687:
3665:. Retrieved
3656:
3653:"Richi'Blog"
3647:
3636:. Retrieved
3622:
3611:. Retrieved
3607:the original
3597:
3589:
3572:cite journal
3561:. Retrieved
3547:
3536:, retrieved
3529:
3526:
3517:
3510:. Retrieved
3496:
3485:. Retrieved
3470:
3461:
3448:
3439:
3435:
3425:
3414:. Retrieved
3410:the original
3405:
3395:
3384:. Retrieved
3380:the original
3370:
3345:. Retrieved
3336:
3327:
3316:. Retrieved
3306:
3295:. Retrieved
3285:
3274:. Retrieved
3264:
3253:. Retrieved
3243:
3232:. Retrieved
3222:
3211:. Retrieved
3201:
3190:. Retrieved
3180:
3169:. Retrieved
3159:
3148:. Retrieved
3138:
3115:
3104:. Retrieved
3093:
3082:. Retrieved
3068:
3057:. Retrieved
3042:
3034:
3027:. Retrieved
3012:
3001:. Retrieved
2992:
2982:
2971:. Retrieved
2951:
2940:. Retrieved
2926:
2905:cite journal
2894:. Retrieved
2887:the original
2874:
2853:cite journal
2842:. Retrieved
2835:the original
2822:
2801:cite journal
2790:. Retrieved
2783:the original
2770:
2759:. Retrieved
2750:
2740:
2729:. Retrieved
2718:
2708:
2697:. Retrieved
2679:
2668:. Retrieved
2654:
2643:. Retrieved
2628:
2617:. Retrieved
2590:. Retrieved
2580:
2568:. Retrieved
2554:
2542:
2534:the original
2528:
2522:
2512:, retrieved
2502:
2495:
2484:the original
2475:
2469:
2459:, retrieved
2453:, PC World,
2449:
2443:
2431:. Retrieved
2417:
2406:. Retrieved
2402:the original
2397:
2387:
2377:, retrieved
2361:
2354:
2346:
2338:
2331:
2311:
2300:. Retrieved
2286:
2276:, retrieved
2266:
2260:
2250:
2244:
2234:, retrieved
2224:
2218:
2207:
2196:. Retrieved
2194:. 2008-07-22
2189:
2180:
2169:. Retrieved
2155:
2143:. Retrieved
2134:
2125:
2113:
2103:, retrieved
2093:
2087:
2077:, retrieved
2067:
2061:
2045:
2034:. Retrieved
2030:the original
2016:
2004:. Retrieved
1995:
1986:
1975:. Retrieved
1960:
1934:
1930:
1923:
1911:. Retrieved
1902:
1898:
1887:
1876:. Retrieved
1872:the original
1861:
1850:. Retrieved
1826:. Retrieved
1819:the original
1806:
1794:. Retrieved
1785:
1775:
1763:. Retrieved
1754:
1744:
1732:. Retrieved
1723:
1713:
1701:
1690:. Retrieved
1669:
1651:
1647:
1641:
1630:. Retrieved
1626:the original
1615:
1604:. Retrieved
1579:
1575:
1565:
1555:, retrieved
1545:
1539:
1530:
1521:
1471:Spamusement!
1463:
1269:A number of
1268:
1255:millions CDs
1254:
1252:
1245:
1243:
1234:
1230:
1228:
1219:
1217:
1200:
1191:
1160:
1149:
1145:
1143:
1117:
1108:
1093:Please help
1081:
1044:
1033:
1027:
1023:micropayment
996:
989:
966:Airtel India
953:
952:
943:
942:
925:
899:
898:
886:
746:South Korea
680:
677:Cost of spam
668:
657:
649:
636:
632:
618:
603:
597:October 2015
594:
571:
553:Side effects
547:
543:
537:, short for
534:
520:
505:
496:
488:
468:
456:
447:
443:
436:
420:
408:
399:
379:
371:
356:
348:legal remedy
345:
318:
299:
266:, a form of
257:
253:
233:
229:
211:
196:
175:
169:
155:
141:
131:
129:
110:
101:
78:
75:
64:
43:
42:, or simply
39:
35:
31:
30:
4231:Advertising
4148:Social spam
4060:Greylisting
4030:Client-side
3958:Auto dialer
3657:richi.co.uk
2225:Enforcement
1501:Spider trap
1387:Chain email
1007:greylisting
718:EU (Top 5)
699:Percentage
464:credit card
97:attachments
67:postage due
4220:Categories
4153:Spam blogs
4118:Forum spam
4095:Spamdexing
3968:Flyposting
3927:Image spam
3889:Email spam
3667:2008-03-17
3638:2012-12-10
3613:2007-01-06
3563:2007-01-06
3538:2004-10-12
3512:2007-01-06
3487:2007-01-06
3416:2007-01-06
3386:2021-12-13
3347:2007-01-06
3318:2009-01-22
3297:2008-11-02
3276:2008-06-07
3255:2008-02-12
3234:2007-11-09
3213:2007-07-24
3192:2007-06-15
3171:2007-01-06
3150:2007-01-06
3106:2020-04-13
3084:2008-01-18
3059:2010-09-23
3029:2010-09-23
3003:2010-09-23
2973:2012-12-10
2942:2018-10-21
2896:2007-01-06
2844:2007-01-06
2792:2008-05-08
2761:2012-12-10
2731:2011-01-11
2699:2007-01-21
2670:2012-12-10
2645:2012-12-10
2619:2010-09-23
2592:2007-01-05
2514:2017-06-14
2461:2008-03-21
2408:2007-03-09
2379:2019-02-11
2302:2010-09-23
2278:2011-03-14
2236:2014-01-16
2198:2010-10-24
2171:2009-06-23
2145:11 January
2105:2008-01-18
2079:2010-12-03
2036:2012-12-10
2022:"Symantec"
2006:August 17,
1977:2007-01-06
1913:2013-03-19
1878:2010-09-23
1852:2008-10-12
1828:2015-11-01
1692:2018-10-15
1632:2010-09-23
1606:2022-10-30
1557:2010-12-17
1513:References
1433:Netiquette
1253:So-called
664:Bill Gates
581:improve it
340:See also:
250:Blank spam
227:" stocks.
213:Image spam
208:Image spam
202:Image spam
158:fraudsters
132:Mainsleaze
36:junk email
32:Email spam
4133:Link farm
4103:Blog spam
4022:Anti-spam
3988:Newsgroup
3978:Messaging
3880:Protocols
3723:Spam info
2570:9 January
2433:7 January
1596:1084-8045
1582:: 56–65.
1440:newsgroup
1167:leetspeak
1082:does not
1011:spamtraps
682:in 2005.
644:Microsoft
585:verifying
510:and open
484:SMTP-AUTH
417:Australia
409:The 2010
187:Appending
40:spam mail
25:email box
4226:Spamming
4198:Phishing
4108:Cloaking
4085:Spamhaus
3993:Robocall
3973:Junk fax
3661:Archived
3632:Archived
3557:Archived
3532:archived
3506:Archived
3481:Archived
3356:cite web
3341:Archived
3123:Archived
3098:Sophos.
3078:Archived
3053:Archived
3023:Archived
2997:Archived
2993:BBC News
2964:Archived
2936:Archived
2755:Archived
2751:BBC News
2725:Archived
2693:Archived
2664:Archived
2639:Archived
2564:Archived
2508:archived
2455:archived
2427:Archived
2370:archived
2320:Archived
2296:Archived
2272:archived
2254:, CA: GC
2230:archived
2191:PC World
2165:Archived
2139:Archived
2099:archived
2073:archived
2026:Symantec
2000:Archived
1971:Archived
1907:Archived
1796:April 1,
1790:Archived
1765:April 1,
1759:Archived
1734:April 1,
1728:Archived
1683:Archived
1600:Archived
1551:archived
1496:Spamware
1491:Spamtrap
1486:Spamhaus
1417:Junk fax
1350:See also
1247:spamware
958:ChinaNet
774:Germany
696:Country
472:spoofing
367:phishing
171:phishing
152:Phishing
144:Cyberoam
107:Overview
89:phishing
52:spamming
4080:SpamCop
3998:Spambot
3942:Spambot
3932:Joe job
3436:Heliyon
2345:, FTC,
2228:, ICO,
1939:Bibcode
1681:. MIT.
1481:SpamCop
1476:Spambot
1412:Happy99
1339:History
1259:CD-ROMs
1187:\/iagra
1179:Vi@graa
1175:Via'gra
1103:removed
1088:sources
830:Turkey
816:Russia
802:France
788:Brazil
760:Poland
639:ARPANET
579:Please
531:botnets
523:zombies
363:botnets
312:to the
302:viruses
246:tools.
240:CAPTCHA
113:ARPANET
93:malware
3786:13 Oct
3709:
2660:"Spam"
1594:
1367:Botnet
1332:ironic
1183:vi*gra
1171:V1agra
1163:Viagra
964:, and
962:Amazon
904:Sophos
894:Europe
872:India
858:Italy
527:Zombie
405:Canada
322:DNSBLs
304:, and
285:files.
271:goals.
166:PayPal
4241:Email
4203:Voice
4158:Sping
4075:SORBS
3951:Other
3917:DNSWL
3912:DNSBL
3833:(PDF)
3826:(PDF)
3780:(PDF)
3773:(PDF)
3692:(PDF)
3458:(PDF)
3131:ROKSO
2967:(PDF)
2960:(PDF)
2890:(PDF)
2883:(PDF)
2838:(PDF)
2831:(PDF)
2786:(PDF)
2779:(PDF)
2613:(PDF)
2546:e.g.
2487:(PDF)
2480:(PDF)
2373:(PDF)
2366:(PDF)
2343:(PDF)
2135:Iohud
2117:e.g.
2049:e.g.
1822:(PDF)
1815:(PDF)
1686:(PDF)
1679:(PDF)
1377:CAUCE
1021:or a
1003:DNSBL
539:robot
459:fraud
306:worms
85:links
48:email
4008:VoIP
3809:and
3788:2007
3707:ISBN
3585:help
3442:(6).
3362:link
2918:help
2866:help
2814:help
2572:2019
2435:2015
2147:2019
2008:2015
1996:CNET
1798:2019
1767:2019
1736:2019
1592:ISSN
1086:any
1084:cite
1015:SMTP
946:the
892:and
724:17.9
710:19.6
480:SMTP
421:The
221:JPEG
162:scam
44:spam
1947:doi
1656:doi
1584:doi
1330:An
1233:or
1224:DNS
1201:As
1097:by
1005:),
878:2.5
864:2.8
850:2.8
836:2.9
822:3.1
808:3.3
794:4.1
780:4.2
766:4.8
752:6.5
738:8.4
583:by
535:bot
236:GIF
219:or
217:GIF
160:to
23:An
4222::
3813:–
3732:,
3659:.
3655:.
3576::
3574:}}
3570:{{
3530:,
3460:.
3438:.
3434:.
3404:.
3358:}}
3354:{{
3335:.
3133:).
3076:.
2995:.
2991:.
2962:.
2934:.
2909::
2907:}}
2903:{{
2857::
2855:}}
2851:{{
2805::
2803:}}
2799:{{
2753:.
2749:.
2723:.
2717:.
2601:^
2396:.
2188:.
2133:.
2053:,
2024:.
1994:.
1945:.
1935:32
1933:.
1901:.
1897:.
1837:^
1788:.
1784:.
1757:.
1753:.
1726:.
1722:.
1652:26
1650:,
1598:.
1590:.
1580:43
1578:.
1574:.
1529:.
1301:A
1185:,
1181:,
1177:,
1173:,
1009:,
968:.
960:,
389:EU
332:.
328:'
178:.
99:.
73:.
38:,
3864:e
3857:t
3850:v
3837:.
3791:.
3756:.
3738:.
3713:.
3696:.
3670:.
3641:.
3616:.
3592:.
3587:)
3583:(
3566:.
3515:.
3490:.
3440:5
3419:.
3389:.
3364:)
3350:.
3321:.
3300:.
3279:.
3258:.
3237:.
3216:.
3195:.
3174:.
3153:.
3129:(
3109:.
3087:.
3062:.
3037:.
3032:.
3006:.
2976:.
2945:.
2920:)
2916:(
2899:.
2868:)
2864:(
2847:.
2816:)
2812:(
2795:.
2764:.
2734:.
2702:.
2673:.
2648:.
2622:.
2595:.
2574:.
2437:.
2411:.
2305:.
2201:.
2174:.
2149:.
2039:.
2010:.
1980:.
1953:.
1949::
1941::
1916:.
1903:7
1881:.
1855:.
1831:.
1800:.
1769:.
1738:.
1708:.
1695:.
1658::
1635:.
1609:.
1586::
1533:.
1124:)
1118:(
1113:)
1109:(
1105:.
1091:.
610:)
604:(
599:)
595:(
577:.
123:/
50:(
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.