587:
more RAM during startup than they did subsequently, and recover and reuse the memory that was no longer needed after startup. They might even remap areas of memory normally used for memory-mapped I/O. Many of these tricks involved assumptions about the functioning of drivers and other components. In effect, memory managers might reverse-engineer and modify other vendors' code on the fly. As might be expected, such tricks did not always work. Therefore, memory managers also incorporated very elaborate systems of configurable options, and provisions for recovery should a selected option render the PC unbootable (a frequent occurrence).
131:
25:
198:(RAM) installed, which was used by DOS and application programs. The first part of this memory was installed on the motherboard of the system (in very early machines, 64 KiB, later revised to 256 KiB). Additional memory could be added with cards plugged into the expansion slots; each card contained straps or switches to control what part of the address space accesses memory and devices on that card.
551:, which when asserted low forces bit 20 of the physical address to be zero for all on-chip cache or external memory accesses. This was necessary since the 80486 introduced an on-chip cache, and therefore masking this bit in external logic was no longer possible. Software still needs to manipulate the gate and must still deal with external peripherals (the
586:
On 386 and subsequent processors, memory managers like QEMM might move the bulk of the code for a driver or TSR into extended memory and replace it with a small fingerhold that was capable of accessing the extended-memory-resident code. They might analyze memory usage to detect drivers that required
422:
keyboard controller. Controlling it was a relatively slow process. Other methods have since been added to allow for more efficient multitasking of programs which require this wrap-around with programs that access all of the system's memory. There was at first a variety of methods, but eventually the
609:
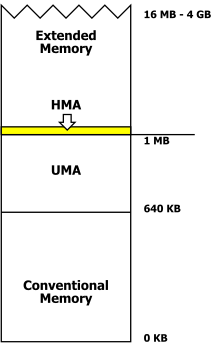
refers to memory in the address space of the 80286 and subsequent processors, beyond the 1 megabyte limit imposed by the 20 address lines of the 8088 and 8086. Such memory is not directly available to DOS applications running in the so-called "real mode" of the 80286 and subsequent processors. This
279:
that worked. Mapping two devices to use the same physical memory addresses could result in a stalled or unstable system. Not all addresses in the upper memory area were used in a typical system; unused physical addresses would return undefined and system-dependent data if accessed by the processor.
174:
The 640 KiB limit imposed great complexity on hardware and software intended to circumvent it; the physical memory in a machine could be organised as a combination of base or conventional memory (including lower memory), upper memory, high memory (not the same as upper memory), extended memory, and
358:
architecture of the Intel family processors had the byproduct of allowing slightly more than 1 MiB of memory to be addressed in the "real" mode. Since the 80286 had more than 20 address lines, certain combinations of segment and offset could point into memory above the 0x0100000 (2) location. The
193:
processor used in the original IBM PC had 20 address lines and so could directly address 1 MiB (2 bytes) of memory. Different areas of this address space were allocated to different kinds of memory used for different purposes. Starting at the lowest end of the address space, the PC had read/write
590:
Installing and configuring a memory manager might involve hours of experimentation with options, repeatedly rebooting the machine, and testing the results. But conventional memory was so valuable that PC owners felt that such time was well-spent if the result was to free up 30 or 40 KiB of
310:
was not supported by the processor hardware, and disk technology of the time would make it too slow and cumbersome to be practical. Expanded memory was a system that allowed application programs to access more RAM than directly visible to the processor's address space. The process was a form of
327:
Allocation and use of expanded memory was not transparent to application programs. The application had to keep track of which bank of expanded memory contained a particular piece of data, and when access to that data was required, the application had to request (through a driver program) the
452:
facilities of the processor: physical memory may be mapped to multiple virtual addresses, thus allowing that the memory mapped at the first megabyte of virtual memory may be mapped again in the second megabyte of virtual memory. The operating system may intercept changes to Gate A20 and make
201:
On the IBM PC, all the address space up to 640 KiB was available for RAM. This part of the address space is called "conventional memory" since it is accessible to all versions of DOS automatically on startup. Segment 0, the first 64 KiB of conventional memory, is also called
359:
80286 could address up to 16 MiB of system memory, thus removing the behavior of memory addresses "wrapping around". Since the required address line now existed, the combination F800:8000 would no longer point to the physical address 0x0000000 but the correct address 0x00100000.
206:. Normally expansion memory is set to be contiguous in the address space with the memory on the motherboard. If there was an unallocated gap between motherboard memory and the expansion memory, the memory would not be automatically detected as usable by DOS.
259:
of the CPU after a hardware reset and must have a defined value that endures after power is interrupted to the system. On reset or power up, the CPU loads the address from the system ROM and then jumps to a defined ROM location to begin executing the system
324:, with only 20 address lines, special-purpose expanded memory cards were made containing perhaps a megabyte, or more, of expanded memory, with logic on the board to make that memory accessible to the processor in defined parts of the 8088 address space.
170:
and other 32-bit operating systems not restricted by the original arbitrary 640 KiB limit of the IBM PC, managing the memory of a personal computer no longer requires the user to manually manipulate internal settings and parameters of the system.
251:
memory area ran from 704 to 736 KiB (0xB0000–0xB7FFF). If only a monochrome display adapter was used, the address space between 0xA0000 and 0xAFFFF could be used for RAM, which would be contiguous with the conventional memory.
319:
software would temporarily make a piece of expanded memory accessible to the processor; when the data in that piece of memory was updated, another part could be swapped into the processor's address space. For the IBM PC and
275:, or network adapter could use allocations of memory in many of the upper memory areas, configuration of some combinations of cards required careful reading of documentation, or experimentation, to find card settings and
328:
expanded memory board to map that part of memory into the processor's address space. Although applications could use expanded memory with relative freedom, many other software components such as drivers and
382:
first enables A20 when counting and testing all of the system's memory, and disables it before transferring control to the operating system. Enabling the A20 line is one of the first steps a
517:
for opening/closing A20. DOS itself could utilize the area for some of its storage needs, thereby freeing up more conventional memory for programs. This functionality was enabled by the "
255:
The system BIOS ROMs must be at the upper end of the address space because the CPU starting address is fixed by the design of the processor. The starting address is loaded into the
220:
The upper memory area (UMA) refers to the address space between 640 and 1024 KiB (0xA0000–0xFFFFF). The 128 KiB region between 0xA0000 and 0xBFFFF was reserved for
366:
gate (Gate A20) that made memory addresses on the AT wrap around to low memory as they would have on an 8088 processor. This gate could be controlled, initially through the
162:
Victor 9000, 896 KiB. Memory management on the IBM family was made complex by the need to maintain backward compatibility to the original PC design and
166:
DOS, while allowing computer users to take advantage of large amounts of low-cost memory and new generations of processors. Since DOS has given way to
736:
675:
150:(640*1024 bytes) (KiB) of "conventional memory". The 640 KiB limit was specific to the IBM PC and close compatibles; other machines running
332:(TSRs) were still normally constrained to reside within the 640K "conventional memory" area, which soon became a critically scarce resource.
392:
does in the bootup process, often before control has been passed onto the kernel from the bootstrap (in the case of Linux, for example).
637:
89:
61:
362:
As a result, some DOS programs would no longer work. To maintain compatibility with the PC and XT behavior, the AT included an
42:
571:, which simplified the hardware required to implement expanded memory for DOS applications. Expanded memory managers such as
68:
453:
corresponding changes to the virtual memory address space, which also makes irrelevant the efficiency of Gate-A20 toggling.
370:, to allow running programs which were designed for this to access an additional 65,520 bytes (64 KiB) of memory in
329:
75:
783:
754:
693:
631:
108:
57:
619:
367:
832:
248:
46:
240:. The IBM PC reserved the uppermost 64 KiB of the address space from 0xF0000 to 0xFFFFF for the BIOS and
643:
224:
screen memory and legacy SMM. The 128 KiB region between 0xC0000 and 0xDFFFF was reserved for device
649:
837:
572:
518:
472:(1991), parts of the operating system could be loaded into HMA as well, freeing up to 46 KiB of
159:
82:
355:
299:
35:
272:
610:
memory is only accessible in the protected or virtual modes of 80286 and higher processors.
625:
404:
195:
8:
808:
775:
473:
184:
509:
managers usually provide this functionality. In DOS, high memory area managers, such as
146:
refers to software and techniques employed to give applications access to more than 640
740:
679:
261:
583:
supported the expanded memory standard without requirement for special memory boards.
779:
750:
689:
568:
477:
441:
276:
215:
167:
139:
122:
232:. The 64 KiB of the address space from 0xE0000 to 0xEFFFF was reserved for the
816:
389:
341:
746:
685:
600:
506:
438:
software only cared about the area slightly above 1 MiB, so Gate A20 was enough.
434:
memory accesses above 1 MiB, just those in the 1 MiB, 3 MiB, 5 MiB, etc. ranges.
424:
412:
289:
256:
203:
655:
449:
383:
312:
303:
302:
were changed to take advantage of more and more physical memory in the system.
268:
241:
476:. Other components, such as device drivers and TSRs, could be loaded into the
121:
This article is about the DOS operating systems. For the general concept, see
826:
316:
709:
16:
Techniques employed to give applications access to more than 640 kibibytes
564:
540:
457:
445:
295:
803:
812:
522:
419:
237:
229:
225:
190:
155:
130:
510:
461:
435:
371:
351:
321:
163:
147:
24:
534:
496:
345:
552:
544:
484:
375:
483:
80286 introduced a MMIO memory hole (15 MiB to 16 MiB) for some
580:
469:
465:
151:
408:
576:
379:
307:
233:
448:, allows the A20 wrap-around to be simulated by using the
514:
386:
221:
505:
is software controlling access to the high memory area.
294:
As memory prices declined, application programs such as
456:
The first user of the HMA among
Microsoft products was
418:
Originally, the logic gate was a gate connected to the
423:
industry settled on the PS/2 method of using a bit in
804:
335:
513:had the extra task of managing A20 and provided an
407:area consisting of the first 64 KiB, minus 16
49:. Unsourced material may be challenged and removed.
558:
824:
175:expanded memory, all handled in different ways.
605:In the context of IBM PC-compatible computers,
528:
464:device driver. Starting with versions 5.0 of
415:on an IBM PC/AT or compatible microcomputer.
763:
731:
729:
264:, and eventually load an operating system.
638:Extended Virtual Control Program Interface
134:Physical memory areas of the IBM PC family
109:Learn how and when to remove this message
726:
668:
129:
769:
735:
674:
825:
178:
154:had different limits, for example the
772:Protected mode software architecture
330:terminate-and-stay-resident programs
209:
47:adding citations to reliable sources
18:
13:
594:
336:The 80286 and the high memory area
283:
14:
849:
796:
632:Virtual Control Program Interface
430:Disconnecting A20 would not wrap
158:could have up to 768 KiB and the
23:
710:"Memory Map (x86) - OSDev Wiki"
620:Global EMM Import Specification
559:80386 and subsequent processors
34:needs additional citations for
702:
490:
460:in 1987, which introduced the
1:
661:
427:92h to control the A20 line.
315:. When extra RAM was needed,
644:DOS Protected Mode Interface
529:A20 gate on later processors
7:
742:Upgrading and Repairing PCs
681:Upgrading and Repairing PCs
650:DOS Protected Mode Services
613:
591:conventional memory space.
10:
854:
598:
563:Intel processors from the
547:added a special pin named
532:
494:
339:
287:
213:
182:
120:
271:such as a video adapter,
579:product and Microsoft's
521:=HIGH" directive in the
249:monochrome video adapter
244:read-only memory (ROM).
300:computer-aided drafting
58:"DOS memory management"
813:High Memory Management
444:, introduced with the
135:
833:DOS memory management
770:Shanley, Tom (1996).
739:(1999). "6: Memory".
273:hard drive controller
144:DOS memory management
133:
776:Taylor & Francis
626:Virtual DMA Services
525:configuration file.
354:was introduced, the
196:random access memory
43:improve this article
809:Computer Chronicles
802:Microsoft support:
474:conventional memory
368:keyboard controller
185:Conventional memory
179:Conventional memory
262:power-on self-test
136:
838:Memory management
745:(11th ed.).
569:virtual 8086 mode
567:onward allowed a
478:upper memory area
442:Virtual 8086 mode
247:For example, the
216:Upper memory area
210:Upper memory area
168:Microsoft Windows
140:IBM PC compatible
123:memory management
119:
118:
111:
93:
845:
817:Internet Archive
790:
789:
767:
761:
760:
733:
724:
723:
721:
720:
706:
700:
699:
684:(4th ed.).
672:
397:high memory area
390:operating system
356:segmented memory
342:High memory area
306:in the 8088 and
114:
107:
103:
100:
94:
92:
51:
27:
19:
853:
852:
848:
847:
846:
844:
843:
842:
823:
822:
799:
794:
793:
786:
768:
764:
757:
747:Que Corporation
734:
727:
718:
716:
708:
707:
703:
696:
673:
669:
664:
616:
607:extended memory
603:
601:Extended memory
597:
595:Extended memory
561:
537:
531:
507:Extended memory
499:
493:
413:extended memory
348:
340:Main articles:
338:
292:
290:Expanded memory
286:
284:Expanded memory
277:memory mappings
257:program counter
218:
212:
204:low memory area
187:
181:
126:
115:
104:
98:
95:
52:
50:
40:
28:
17:
12:
11:
5:
851:
841:
840:
835:
821:
820:
806:
798:
797:External links
795:
792:
791:
784:
778:. p. 60.
762:
755:
737:Mueller, Scott
725:
714:wiki.osdev.org
701:
694:
676:Mueller, Scott
666:
665:
663:
660:
659:
658:
656:Helix Cloaking
653:
647:
641:
635:
629:
623:
615:
612:
599:Main article:
596:
593:
560:
557:
533:Main article:
530:
527:
495:Main article:
492:
489:
468:(1990) and of
450:virtual memory
384:protected mode
337:
334:
313:bank switching
304:Virtual memory
288:Main article:
285:
282:
269:expansion card
242:Cassette BASIC
214:Main article:
211:
208:
183:Main article:
180:
177:
117:
116:
31:
29:
22:
15:
9:
6:
4:
3:
2:
850:
839:
836:
834:
831:
830:
828:
818:
814:
810:
807:
805:
801:
800:
787:
785:0-201-55447-X
781:
777:
773:
766:
758:
756:0-7897-1903-7
752:
748:
744:
743:
738:
732:
730:
715:
711:
705:
697:
695:1-56529-932-9
691:
687:
683:
682:
678:(1994). "7".
677:
671:
667:
657:
654:
651:
648:
645:
642:
639:
636:
633:
630:
627:
624:
621:
618:
617:
611:
608:
602:
592:
588:
584:
582:
578:
574:
570:
566:
556:
554:
550:
546:
542:
536:
526:
524:
520:
516:
512:
508:
504:
498:
488:
486:
481:
479:
475:
471:
467:
463:
459:
454:
451:
447:
443:
439:
437:
433:
428:
426:
421:
416:
414:
410:
406:
402:
398:
393:
391:
388:
385:
381:
377:
373:
369:
365:
360:
357:
353:
347:
343:
333:
331:
325:
323:
318:
314:
309:
305:
301:
297:
291:
281:
278:
274:
270:
265:
263:
258:
253:
250:
245:
243:
239:
235:
231:
227:
223:
217:
207:
205:
199:
197:
192:
186:
176:
172:
169:
165:
161:
157:
153:
149:
145:
141:
132:
128:
124:
113:
110:
102:
91:
88:
84:
81:
77:
74:
70:
67:
63:
60: –
59:
55:
54:Find sources:
48:
44:
38:
37:
32:This article
30:
26:
21:
20:
815:". From the
771:
765:
741:
717:. Retrieved
713:
704:
680:
670:
606:
604:
589:
585:
562:
555:) for that.
548:
538:
502:
500:
482:
455:
440:
431:
429:
417:
400:
396:
394:
363:
361:
349:
326:
296:spreadsheets
293:
266:
254:
246:
228:, including
219:
200:
188:
173:
143:
137:
127:
105:
96:
86:
79:
72:
65:
53:
41:Please help
36:verification
33:
573:Quarterdeck
541:Intel 80486
503:A20 handler
491:A20 handler
458:Windows 2.0
446:Intel 80386
238:Option ROMs
226:Option ROMs
142:computing,
827:Categories
719:2020-12-20
662:References
523:CONFIG.SYS
420:Intel 8042
378:time, the
230:Video BIOS
191:Intel 8088
156:Apricot PC
99:March 2011
69:newspapers
811:(1990). "
511:HIMEM.SYS
487:devices.
462:HIMEM.SYS
436:Real mode
411:, of the
403:) is the
372:real mode
352:IBM PC/AT
350:When the
322:IBM PC/XT
267:Since an
164:real-mode
148:kibibytes
622:(GEMMIS)
614:See also
535:A20 line
497:A20 line
364:A20 line
346:A20 line
640:(XVCPI)
553:chipset
545:Pentium
480:(UMA).
83:scholar
782:
753:
692:
652:(DPMS)
646:(DPMI)
634:(VCPI)
581:EMM386
470:MS-DOS
466:DR-DOS
317:driver
160:Sirius
152:MS-DOS
85:
78:
71:
64:
56:
628:(VDS)
549:A20M#
409:bytes
374:. At
90:JSTOR
76:books
780:ISBN
751:ISBN
690:ISBN
577:QEMM
543:and
539:The
501:The
425:port
395:The
380:BIOS
376:boot
344:and
308:8086
298:and
234:BIOS
189:The
62:news
686:Que
575:'s
565:386
519:DOS
515:API
485:ISA
432:all
405:RAM
401:HMA
387:x86
236:or
222:VGA
138:In
45:by
829::
774:.
749:.
728:^
712:.
688:.
819:.
788:.
759:.
722:.
698:.
399:(
125:.
112:)
106:(
101:)
97:(
87:·
80:·
73:·
66:·
39:.
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.