337:
ca942b088ed9103726af1fa87b4deb59e50cf3b5c6dcfbcebf5bba22fb39a6be\ 9936c87bfdd7c52fc5e71700993958fa4e7b5e6e2a3672122475c40f9ec816ba CubeHash10+1/1+10-512: eb7f5f80706e8668c61186c3c710ce57f9094fbfa1dbdc7554842cdbb4d10ce4\ 2fce72736d10b152f6216f23fc648bce810a7af4d58e571ec1b852fa514a0a8e CubeHash160+16/32+160-256: 5151e251e348cbbfee46538651c06b138b10eeb71cf6ea6054d7ca5fec82eb79 CubeHash80+8/1+80-256: 94e0c958d85cdfaf554919980f0f50b945b88ad08413e0762d6ff0219aff3e55 CubeHash10+1/1+10-256: 217a4876f2b24cec489c9171f85d53395cc979156ea0254938c4c2c59dfdf8a4
329:
90bc3f2948f7374065a811f1e47a208a53b1a2f3be1c0072759ed49c9c6c7f28\ f26eb30d5b0658c563077d599da23f97df0c2c0ac6cce734ffe87b2e76ff7294 CubeHash10+1/1+10-512: 3f917707df9acd9b94244681b3812880e267d204f1fdf795d398799b584fa8f1\ f4a0b2dbd52fd1c4b6c5e020dc7a96192397dd1bce9b6d16484049f85bb71f2f CubeHash160+16/32+160-256: 44c6de3ac6c73c391bf0906cb7482600ec06b216c7c54a2a8688a6a42676577d CubeHash80+8/1+80-256: 38d1e8a22d7baac6fd5262d83de89cacf784a02caa866335299987722aeabc59 CubeHash10+1/1+10-256: 80f72e07d04ddadb44a78823e0af2ea9f72ef3bf366fd773aa1fa33fc030e5cb
240:
333:
8e2f62fdbf7bbd637ce40fc293286d75b9d09e8dda31bd029113e02ecccfd39b CubeHash10+1/1+10-512: 13cf99c1a71e40b135f5535bee02e151eb4897e4de410b9cb6d7179c677074eb\ 6ef1ae9a9e685ef2d2807509541f484d39559525179d53838eda95eb3f6a401d CubeHash160+16/32+160-256: e712139e3b892f2f5fe52d0f30d78a0cb16b51b217da0e4acb103dd0856f2db0 CubeHash80+8/1+80-256: 692638db57760867326f851bd2376533f37b640bd47a0ddc607a9456b692f70f CubeHash10+1/1+10-256: f63041a946aa98bd47f3175e6009dcb2ccf597b2718617ba46d56f27ffe35d49
1521:
332:
message: "Hello" CubeHash160+16/32+160-512: dcc0503aae279a3c8c95fa1181d37c418783204e2e3048a081392fd61bace883\ a1f7c4c96b16b4060c42104f1ce45a622f1a9abaeb994beb107fed53a78f588c CubeHash80+8/1+80-512: 7ce309a25e2e1603ca0fc369267b4d43f0b1b744ac45d6213ca08e7567566444\
54:. After clarifications from NIST, the author changed the proposal to Cubehash16/32, which "is approximately 16 times faster than CubeHash8/1, easily catching up to both SHA-256 and SHA-512 on the reference platform" while still maintaining a "comfortable security margin".
324:
CubeHash allows for many different parameters to be used to determine the hash output. It is up to the user to decide which parameters they wish to use. Here are several example hashes of different messages, using different parameters. The messages are all in ASCII.
344:
830b2bd5273d616fd785876a4a500218a5388963eeb702fb47547842459f8d89\ 8727a1c8ba40bd48cef47fe82543c2735c033052ae9fcd632d4541bde6b6cb0d\ cb8a9cdf579f5b67b2ae00968180af6e51ebdf0ca597cd2bf91f981f7ab29a62\ 01ad72d946e6c075c6d1337e0a293d6f90c438ac38be153f32aa288ffc5eca8a
336:
message: "The quick brown fox jumps over the lazy dog" CubeHash160+16/32+160-512: bdba44a28cd16b774bdf3c9511def1a2baf39d4ef98b92c27cf5e37beb8990b7\ cdb6575dae1a548330780810618b8a5c351c1368904db7ebdf8857d596083a86 CubeHash80+8/1+80-512:
294:
6998f35dfb0930c760948910e626160f36077cf3b58b0d0c57cf193d3341e7b8\ a334805b2089f9ef31ffc4142aef3850fe121839e940a4527d5293a27045ca12\ 9358096e81bf70349a90a44a93c33edb14c3e9844a87dbd0bc451df25212b3ac\ 6aabe51c5df0f63bddbb8ae8fad3cf0fd52582fbad2e2446094025a521a23d5c
328:
message: "" (the zero-length string) CubeHash160+16/32+160-512: 4a1d00bbcfcb5a9562fb981e7f7db3350fe2658639d948b9d57452c22328bb32\ f468b072208450bad5ee178271408be0b16e5633ac8a1e3cf9864cfbfc8e043a CubeHash80+8/1+80-512:
57:
CubeHash advanced to the second round of the competition, but was not chosen as one of the 5 finalists. Bernstein has since tuned the parameters further and his main recommendation is CubeHash512, defined as CubeHash16+16/32+32–512.
302:
message "Hello" (hex: 0x48, 0x65, 0x6c, 0x6c, 0x6f) uses 6 message blocks. There are 5 blocks from the message, and since this is a byte-aligned input, there is 1 block for padding. The 512 bit hash value is:
163:
The internal state is defined as a five-dimensional array of words (four-byte integers), 0-1 in both dimensions. The words are referred to with their coordinates to . The words are treated as little-endian.
340:
The
Initialization Vectors for the four variants shown are all different as well. For example, the Initialization Vector for CubeHash80+8/1+80-512 can be seen above, and the IV for CubeHash80+8/1+80-256 is:
361:
increases. So CubeHash 8/1-512 is stronger (more secure) than CubeHash 1/1-512, and CubeHash 1/1-512 is stronger than CubeHash 1/2-512. The weakest possible version of this algorithm is CubeHash 1/128-
1501:
1331:
183:
rounds, and the initialization stage is complete. The state is now the
Initialization Vector (IV). The IV can be saved and reused for a given combination of
365:. However, there is a security versus time tradeoff. A more secure version will take longer to compute a hash value than a weakened version.
1184:
1104:
492:
521:
316:
01ee7f4eb0e0ebfdb8bf77460f64993faf13afce01b55b0d3d2a63690d25010f\ 7127109455a7c143ef12254183e762b15575e0fcc49c79a0471a970ba8a66638
306:
7ce309a25e2e1603ca0fc369267b4d43f0b1b744ac45d6213ca08e7567566444\ 8e2f62fdbf7bbd637ce40fc293286d75b9d09e8dda31bd029113e02ecccfd39b
1549:
1120:
881:
1048:
1177:
313:. Hashing the message "hello" (which only differs from "Hello" in 1 bit position) gives the following hash value:
485:
1380:
1089:
574:
526:
27:
876:
309:
A small change in the message, such as flipping a single bit, will wildly change the hash output, due to the
202:-byte blocks. The padding appends a 1 bit, followed by as many 0 bits as necessary to make a complete block.
1170:
1094:
1496:
1451:
1264:
863:
505:
501:
23:
1375:
478:
1491:
759:
564:
1481:
1471:
1326:
1099:
935:
634:
629:
1476:
1466:
1269:
1229:
1222:
1212:
1207:
1022:
842:
39:
1217:
1130:
516:
35:
287:
This example uses CubeHash80+8/1+80-512. The initialization vector is the same for all 80+8/1+
1524:
1370:
1316:
1145:
795:
749:
639:
597:
582:
50:
transformation between blocks. The initial NIST proposal ("Cubehash8/1") required about 200
1486:
1410:
815:
719:
669:
644:
8:
1249:
1140:
1017:
966:
905:
805:
724:
684:
664:
31:
1355:
1339:
1286:
1074:
1058:
1007:
592:
1415:
1405:
1276:
951:
401:
1350:
1038:
992:
754:
310:
66:
This description refers to the latest specification, and not the NIST submission.
1053:
1002:
997:
785:
500:
51:
419:
383:
1425:
1345:
1306:
1254:
1239:
1043:
771:
243:
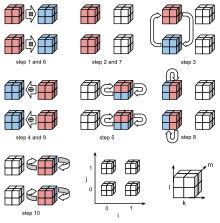
The ten steps of the mixing function. Two of the five dimensions are unrolled.
46:
into the initial bits of a 128-byte state, which then goes through an r-round
1543:
1506:
1461:
1420:
1400:
1296:
1259:
1234:
1135:
1012:
167:
The internal state is initialized by setting the first three words (, , ) to
714:
120:
is the size of the hash output in bits, defined for {8, 16, 24, 32, ... 512}
1456:
1301:
1291:
1281:
1244:
1193:
239:
206:
1435:
1125:
971:
900:
896:
1395:
1365:
1360:
1321:
440:
179:
respectively, all other words to zero. The state is then run through
1385:
800:
679:
47:
587:
69:
CubeHash has 5 parameters, a certain instance is denoted by CubeHash
1430:
1390:
1079:
976:
961:
956:
946:
910:
830:
744:
915:
871:
649:
1311:
1084:
825:
820:
790:
780:
739:
734:
729:
709:
704:
674:
659:
619:
810:
699:
654:
602:
559:
554:
548:
299:
247:
CubeHash round function consists of the following ten steps:
457:
925:
920:
891:
886:
850:
108:
is the block size in bytes, defined for {1, 2, 3, ... 128}
694:
689:
542:
43:
1332:
Cryptographically secure pseudorandom number generator
462:
417:
399:
381:
393:
220:Finally, 1 is XORed to the state word , and then
1541:
269:Rotate x upwards by 11 bits, for each (j,k,l,m).
438:
254:Rotate x upwards by 7 bits, for each (j,k,l,m).
411:
227:The output hash is now contained in the first
1178:
486:
375:
420:"CubeHash parameter tweak: 16 times faster"
353:The strength of this function increases as
1185:
1171:
493:
479:
266:Add x into x modulo 2, for each (j,k,l,m).
251:Add x into x modulo 2, for each (j,k,l,m).
434:
432:
238:
224:rounds of transformation are performed.
213:bytes of the state, and then performing
402:"CubeHash efficiency estimates (2.B.2)"
1542:
429:
34:. CubeHash has a 128 byte state, uses
1166:
474:
319:
198:The message is padded and split to
13:
418:Daniel J. Bernstein (2009-07-15).
400:Daniel J. Bernstein (2008-10-28).
382:Daniel J. Bernstein (2009-09-14).
14:
1561:
451:
282:
275:Xor x into x, for each (j,k,l,m).
260:Xor x into x, for each (j,k,l,m).
234:
124:In the original NIST submission,
102:is the number of rounds per block
1520:
1519:
1192:
384:"CubeHash specification (2.B.1)"
291:-512 hashes, and is as follows:
278:Swap x with x, for each (j,k,l).
272:Swap x with x, for each (j,l,m).
263:Swap x with x, for each (j,k,m).
257:Swap x with x, for each (k,l,m).
136:. The obsolete notation CubeHash
96:is the number of initial rounds
1550:NIST hash function competition
1381:Information-theoretic security
1090:NIST hash function competition
231:/8 bytes of this final state.
28:NIST hash function competition
1:
368:
114:is the number of final rounds
1095:Password Hashing Competition
506:message authentication codes
502:Cryptographic hash functions
357:decreases towards 1, and as
61:
7:
1497:Message authentication code
1452:Cryptographic hash function
1265:Cryptographic hash function
1049:Merkle–Damgård construction
348:
24:cryptographic hash function
16:Cryptographic hash function
10:
1566:
1376:Harvest now, decrypt later
441:"Introduction to CubeHash"
217:rounds of transformation.
205:Each block is inputted by
1515:
1492:Post-quantum cryptography
1444:
1200:
1162:
1113:
1067:
1031:
985:
934:
862:
839:
768:
612:
573:
535:
512:
470:
466:
1482:Quantum key distribution
1472:Authenticated encryption
1327:Random number generation
843:key derivation functions
1477:Public-key cryptography
1467:Symmetric-key algorithm
1270:Key derivation function
1230:Cryptographic primitive
1223:Authentication protocol
1213:Outline of cryptography
1208:History of cryptography
1121:Hash-based cryptography
1023:Length extension attack
1218:Cryptographic protocol
1131:Message authentication
244:
36:wide pipe construction
1371:End-to-end encryption
1317:Cryptojacking malware
458:The CubeHash web site
439:Daniel J. Bernstein.
242:
42:. Message blocks are
1487:Quantum cryptography
1411:Trusted timestamping
1250:Cryptographic nonce
1018:Side-channel attack
156:being implicitly 10
32:Daniel J. Bernstein
1356:Subliminal channel
1340:Pseudorandom noise
1287:Key (cryptography)
1075:CAESAR Competition
1059:HAIFA construction
1008:Brute-force attack
245:
1537:
1536:
1533:
1532:
1416:Key-based routing
1406:Trapdoor function
1277:Digital signature
1158:
1157:
1154:
1153:
952:ChaCha20-Poly1305
769:Password hashing/
320:Parameter changes
26:submitted to the
1557:
1523:
1522:
1351:Insecure channel
1187:
1180:
1173:
1164:
1163:
1039:Avalanche effect
993:Collision attack
536:Common functions
495:
488:
481:
472:
471:
468:
467:
464:
463:
445:
444:
436:
427:
426:
424:
415:
409:
408:
406:
397:
391:
390:
388:
379:
311:avalanche effect
1565:
1564:
1560:
1559:
1558:
1556:
1555:
1554:
1540:
1539:
1538:
1529:
1511:
1440:
1196:
1191:
1150:
1109:
1068:Standardization
1063:
1054:Sponge function
1027:
1003:Birthday attack
998:Preimage attack
981:
937:
930:
858:
841:
840:General purpose
835:
770:
764:
613:Other functions
608:
575:SHA-3 finalists
569:
531:
508:
499:
454:
449:
448:
437:
430:
422:
416:
412:
404:
398:
394:
386:
380:
376:
371:
351:
346:
338:
334:
330:
322:
317:
307:
296:
285:
237:
132:was fixed to 10
64:
52:cycles per byte
17:
12:
11:
5:
1563:
1553:
1552:
1535:
1534:
1531:
1530:
1528:
1527:
1516:
1513:
1512:
1510:
1509:
1504:
1502:Random numbers
1499:
1494:
1489:
1484:
1479:
1474:
1469:
1464:
1459:
1454:
1448:
1446:
1442:
1441:
1439:
1438:
1433:
1428:
1426:Garlic routing
1423:
1418:
1413:
1408:
1403:
1398:
1393:
1388:
1383:
1378:
1373:
1368:
1363:
1358:
1353:
1348:
1346:Secure channel
1343:
1337:
1336:
1335:
1324:
1319:
1314:
1309:
1307:Key stretching
1304:
1299:
1294:
1289:
1284:
1279:
1274:
1273:
1272:
1267:
1257:
1255:Cryptovirology
1252:
1247:
1242:
1240:Cryptocurrency
1237:
1232:
1227:
1226:
1225:
1215:
1210:
1204:
1202:
1198:
1197:
1190:
1189:
1182:
1175:
1167:
1160:
1159:
1156:
1155:
1152:
1151:
1149:
1148:
1143:
1138:
1133:
1128:
1123:
1117:
1115:
1111:
1110:
1108:
1107:
1102:
1097:
1092:
1087:
1082:
1077:
1071:
1069:
1065:
1064:
1062:
1061:
1056:
1051:
1046:
1044:Hash collision
1041:
1035:
1033:
1029:
1028:
1026:
1025:
1020:
1015:
1010:
1005:
1000:
995:
989:
987:
983:
982:
980:
979:
974:
969:
964:
959:
954:
949:
943:
941:
932:
931:
929:
928:
923:
918:
913:
908:
903:
894:
889:
884:
879:
874:
868:
866:
860:
859:
857:
856:
853:
847:
845:
837:
836:
834:
833:
828:
823:
818:
813:
808:
803:
798:
793:
788:
783:
777:
775:
772:key stretching
766:
765:
763:
762:
757:
752:
747:
742:
737:
732:
727:
722:
717:
712:
707:
702:
697:
692:
687:
682:
677:
672:
667:
662:
657:
652:
647:
642:
637:
632:
627:
622:
616:
614:
610:
609:
607:
606:
600:
595:
590:
585:
579:
577:
571:
570:
568:
567:
562:
557:
552:
546:
539:
537:
533:
532:
530:
529:
524:
519:
513:
510:
509:
498:
497:
490:
483:
475:
461:
460:
453:
452:External links
450:
447:
446:
428:
410:
392:
373:
372:
370:
367:
350:
347:
343:
335:
331:
327:
321:
318:
315:
305:
293:
284:
283:Example hashes
281:
280:
279:
276:
273:
270:
267:
264:
261:
258:
255:
252:
236:
235:Round function
233:
122:
121:
115:
109:
103:
97:
63:
60:
15:
9:
6:
4:
3:
2:
1562:
1551:
1548:
1547:
1545:
1526:
1518:
1517:
1514:
1508:
1507:Steganography
1505:
1503:
1500:
1498:
1495:
1493:
1490:
1488:
1485:
1483:
1480:
1478:
1475:
1473:
1470:
1468:
1465:
1463:
1462:Stream cipher
1460:
1458:
1455:
1453:
1450:
1449:
1447:
1443:
1437:
1434:
1432:
1429:
1427:
1424:
1422:
1421:Onion routing
1419:
1417:
1414:
1412:
1409:
1407:
1404:
1402:
1401:Shared secret
1399:
1397:
1394:
1392:
1389:
1387:
1384:
1382:
1379:
1377:
1374:
1372:
1369:
1367:
1364:
1362:
1359:
1357:
1354:
1352:
1349:
1347:
1344:
1341:
1338:
1333:
1330:
1329:
1328:
1325:
1323:
1320:
1318:
1315:
1313:
1310:
1308:
1305:
1303:
1300:
1298:
1297:Key generator
1295:
1293:
1290:
1288:
1285:
1283:
1280:
1278:
1275:
1271:
1268:
1266:
1263:
1262:
1261:
1260:Hash function
1258:
1256:
1253:
1251:
1248:
1246:
1243:
1241:
1238:
1236:
1235:Cryptanalysis
1233:
1231:
1228:
1224:
1221:
1220:
1219:
1216:
1214:
1211:
1209:
1206:
1205:
1203:
1199:
1195:
1188:
1183:
1181:
1176:
1174:
1169:
1168:
1165:
1161:
1147:
1144:
1142:
1139:
1137:
1136:Proof of work
1134:
1132:
1129:
1127:
1124:
1122:
1119:
1118:
1116:
1112:
1106:
1103:
1101:
1098:
1096:
1093:
1091:
1088:
1086:
1083:
1081:
1078:
1076:
1073:
1072:
1070:
1066:
1060:
1057:
1055:
1052:
1050:
1047:
1045:
1042:
1040:
1037:
1036:
1034:
1030:
1024:
1021:
1019:
1016:
1014:
1013:Rainbow table
1011:
1009:
1006:
1004:
1001:
999:
996:
994:
991:
990:
988:
984:
978:
975:
973:
970:
968:
965:
963:
960:
958:
955:
953:
950:
948:
945:
944:
942:
939:
936:Authenticated
933:
927:
924:
922:
919:
917:
914:
912:
909:
907:
904:
902:
898:
895:
893:
890:
888:
885:
883:
880:
878:
875:
873:
870:
869:
867:
865:
864:MAC functions
861:
854:
852:
849:
848:
846:
844:
838:
832:
829:
827:
824:
822:
819:
817:
814:
812:
809:
807:
804:
802:
799:
797:
794:
792:
789:
787:
784:
782:
779:
778:
776:
773:
767:
761:
758:
756:
753:
751:
748:
746:
743:
741:
738:
736:
733:
731:
728:
726:
723:
721:
718:
716:
713:
711:
708:
706:
703:
701:
698:
696:
693:
691:
688:
686:
683:
681:
678:
676:
673:
671:
668:
666:
663:
661:
658:
656:
653:
651:
648:
646:
643:
641:
638:
636:
633:
631:
628:
626:
623:
621:
618:
617:
615:
611:
604:
601:
599:
596:
594:
591:
589:
586:
584:
581:
580:
578:
576:
572:
566:
563:
561:
558:
556:
553:
551:(compromised)
550:
547:
545:(compromised)
544:
541:
540:
538:
534:
528:
527:Known attacks
525:
523:
520:
518:
515:
514:
511:
507:
503:
496:
491:
489:
484:
482:
477:
476:
473:
469:
465:
459:
456:
455:
442:
435:
433:
421:
414:
403:
396:
385:
378:
374:
366:
364:
360:
356:
342:
326:
314:
312:
304:
301:
292:
290:
277:
274:
271:
268:
265:
262:
259:
256:
253:
250:
249:
248:
241:
232:
230:
225:
223:
218:
216:
212:
209:to the first
208:
203:
201:
196:
194:
190:
186:
182:
178:
174:
170:
165:
161:
159:
155:
151:
147:
143:
139:
135:
131:
127:
119:
116:
113:
110:
107:
104:
101:
98:
95:
92:
91:
90:
88:
84:
80:
76:
72:
67:
59:
55:
53:
49:
45:
41:
37:
33:
29:
25:
21:
1457:Block cipher
1302:Key schedule
1292:Key exchange
1282:Kleptography
1245:Cryptosystem
1194:Cryptography
624:
413:
395:
377:
362:
358:
354:
352:
339:
323:
308:
298:Hashing the
297:
288:
286:
246:
228:
226:
221:
219:
214:
210:
204:
199:
197:
192:
188:
184:
180:
176:
172:
168:
166:
162:
157:
153:
149:
145:
141:
137:
133:
129:
125:
123:
117:
111:
105:
99:
93:
86:
82:
78:
74:
70:
68:
65:
56:
19:
18:
1445:Mathematics
1436:Mix network
1126:Merkle tree
1114:Utilization
1100:NSA Suite B
1396:Ciphertext
1366:Decryption
1361:Encryption
1322:Ransomware
938:encryption
715:RadioGatún
522:Comparison
369:References
148:indicates
1386:Plaintext
855:KDF1/KDF2
774:functions
760:Whirlpool
62:Operation
48:bijective
40:ARX based
38:, and is
1544:Category
1525:Category
1431:Kademlia
1391:Codetext
1334:(CSPRNG)
1080:CRYPTREC
911:Poly1305
831:yescrypt
745:Streebog
625:CubeHash
605:(winner)
349:Security
20:CubeHash
1201:General
986:Attacks
916:SipHash
872:CBC-MAC
806:LM hash
786:Balloon
650:HAS-160
1312:Keygen
1146:Pepper
1085:NESSIE
1032:Design
826:scrypt
821:PBKDF2
796:Catena
791:bcrypt
781:Argon2
740:Snefru
735:Shabal
730:SWIFFT
710:RIPEMD
705:N-hash
680:MASH-2
675:MASH-1
660:Kupyna
620:BLAKE3
603:Keccak
588:Grøstl
565:BLAKE2
207:XORing
175:, and
22:is a
1342:(PRN)
940:modes
816:Makwa
811:Lyra2
801:crypt
750:Tiger
700:MDC-2
655:HAVAL
640:Fugue
598:Skein
583:BLAKE
560:SHA-3
555:SHA-2
549:SHA-1
423:(PDF)
405:(PDF)
387:(PDF)
300:ASCII
44:XORed
1141:Salt
1105:CNSA
972:IAPM
926:VMAC
921:UMAC
906:PMAC
901:CMAC
897:OMAC
892:NMAC
887:HMAC
882:GMAC
851:HKDF
720:SIMD
670:Lane
645:GOST
630:ECOH
517:List
504:and
171:/8,
152:and
128:and
977:OCB
967:GCM
962:EAX
957:CWC
947:CCM
877:DAA
755:VSH
725:SM3
695:MD6
690:MD4
685:MD2
665:LSH
635:FSB
543:MD5
30:by
1546::
593:JH
431:^
195:.
191:,
187:,
160:.
89:.
1186:e
1179:t
1172:v
899:/
494:e
487:t
480:v
443:.
425:.
407:.
389:.
363:h
359:r
355:b
289:f
229:h
222:f
215:r
211:b
200:b
193:r
189:b
185:h
181:i
177:r
173:b
169:h
158:r
154:f
150:i
146:h
144:-
142:b
140:/
138:r
134:r
130:f
126:i
118:h
112:f
106:b
100:r
94:i
87:h
85:-
83:f
81:+
79:b
77:/
75:r
73:+
71:i
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.