512:
17:
149:
1350:
503:
determine that another participant will also have a black pixel in that location. Knowing where black pixels exist in another party's share allows them to create a new share that will combine with the predicted share to form a new secret message. In this way a set of colluding parties that have enough shares to access the secret code can cheat other honest parties.
502:
We know that 2 shares are enough to decode the secret image using the human visual system. But examining two shares also gives some information about the 3rd share. For instance, colluding participants may examine their shares to determine when they both have black pixels and use that information to
131:
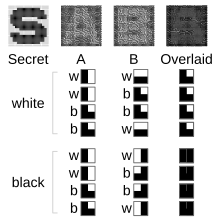
So, when the two component images are superimposed, the original image appears. However, without the other component, a component image reveals no information about the original image; it is indistinguishable from a random pattern of ■□ / □■ pairs. Moreover, if you have one component image, you can
127:
of pixels for every pixel in the original image. These pixel pairs are shaded black or white according to the following rule: if the original image pixel was black, the pixel pairs in the component images must be complementary; randomly shade one ■□, and the other □■. When these complementary pairs
92:
encryption, where one transparency is a shared random pad, and another transparency acts as the ciphertext. Normally, there is an expansion of space requirement in visual cryptography. But if one of the two shares is structured recursively, the efficiency of visual cryptography can be increased to
478:
For instance in the (2,2) sharing case (the secret is split into 2 shares and both shares are required to decode the secret) we use complementary matrices to share a black pixel and identical matrices to share a white pixel. Stacking the shares we have all the subpixels associated with the black
523:
When overlaid, each white pixel of the secret image is represented by three black subpixels, while each black pixel is represented by all four subpixels black. Each corresponding pixel in the component images is randomly rotated to avoid orientation leaking information about the secret image.
474:
325:
498:
colluding parties to cheat an honest party in visual cryptography. They take advantage of knowing the underlying distribution of the pixels in the shares to create new shares that combine with existing shares to form a new secret message of the cheaters choosing.
172:
shares printed on transparencies. The shares appear random and contain no decipherable information about the underlying secret image, however if any 2 of the shares are stacked on top of one another the secret image becomes decipherable by the human eye.
519:
2×2 subpixels can also encode a binary image in each component image, as in the scheme on the right. Each white pixel of each component image is represented by two black subpixels, while each black pixel is represented by three black subpixels.
128:
are overlapped, they will appear dark gray. On the other hand, if the original image pixel was white, the pixel pairs in the component images must match: both ■□ or both □■. When these matching pairs are overlapped, they will appear light gray.
335:
186:
108:
85:
visual cryptography, and using opaque sheets but illuminating them by multiple sets of identical illumination patterns under the recording of only one single-pixel detector.
73:
shares revealed no information about the original image. Each share was printed on a separate transparency, and decryption was performed by overlaying the shares. When all
543:, the protagonist uses a visual cryptography overlay of multiple transparencies to reveal a secret message – the location of a scientist friend who had gone into hiding.
180:) case, a white pixel in the secret image is encoded using a matrix from the following set, where each row gives the subpixel pattern for one of the components:
1330:
1160:
176:
Every pixel from the secret image is encoded into multiple subpixels in each share image using a matrix to determine the color of the pixels. In the (2,
39:
technique which allows visual information (pictures, text, etc.) to be encrypted in such a way that the decrypted information appears as a visual image.
1451:
96:
Some antecedents of visual cryptography are in patents from the 1960s. Other antecedents are in the work on perception and secure communication.
1013:
469:{\displaystyle \mathbf {C_{1}=} {\begin{bmatrix}1&0&...&0\\0&1&...&0\\...\\0&0&...&1\end{bmatrix}}.}
320:{\displaystyle \mathbf {C_{0}=} {\begin{bmatrix}1&0&...&0\\1&0&...&0\\...\\1&0&...&0\end{bmatrix}}.}
152:
Any two transparencies printed with black rectangles, when overlaid reveals the message, here, a letter A (gridlines added for clarity)
1390:
111:
A demonstration of visual cryptography. When two same-sized images of apparently random black-and-white pixels are superimposed, the
646:
Ateniese, Giuseppe; Blundo, Carlo; Santis, Alfredo De; Stinson, Douglas R. (2001). "Extended capabilities for visual cryptography".
1446:
956:
Liu, Feng; Yan, Wei Qi (2014) Visual
Cryptography for Image Processing and Security: Theory, Methods, and Applications, Springer
611:
Verheul, Eric R.; Van
Tilborg, Henk C. A. (1997). "Constructions and Properties of k out of n Visual Secret Sharing Schemes".
160:, such that at least 2 of them are required to decode the secret is one form of the visual secret sharing scheme presented by
99:
Visual cryptography can be used to protect biometric templates in which decryption does not require any complex computations.
595:
28:= 4 requires 16 (2) sets of codes each with 8 (2) subpixels, which can be laid out as 3×3 with the extra bit always black
77:
shares were overlaid, the original image would appear. There are several generalizations of the basic scheme including
673:
Jiao, Shuming; Feng, Jun; Gao, Yang; Lei, Ting; Yuan, Xiaocong (2020). "Visual cryptography in single-pixel imaging".
1006:
1603:
534:
1209:
1383:
917:
999:
1434:
1325:
1280:
1093:
1598:
1204:
726:
Gnanaguruparan, Meenakshi; Kak, Subhash (2002). "Recursive Hiding of
Secrets in Visual Cryptography".
1525:
1320:
919:
Analysis of Visual
Cryptography, Steganography Schemes and its Hybrid Approach for Security of Images
1376:
1310:
1300:
1155:
858:
1305:
1295:
1098:
1058:
1051:
1041:
1036:
1046:
830:
Arazi, B.; Dinstein, I.; Kafri, O. (1989). "Intuition, perception, and secure communication".
1644:
1353:
1199:
1145:
553:
1315:
1239:
955:
945:
796:
329:
While a black pixel in the secret image is encoded using a matrix from the following set:
8:
1576:
1078:
882:
Horng, Gwoboa; Chen, Tzungher; Tsai, Du-Shiau (2006). "Cheating in Visual
Cryptography".
479:
pixel now black while 50% of the subpixels associated with the white pixel remain white.
800:
1593:
1413:
1184:
1168:
1115:
899:
743:
708:
682:
628:
659:
1581:
1458:
1244:
1234:
1105:
940:
812:
712:
700:
591:
24:
transparencies A, B,... printed with black rectangles reveal a secret image —
1623:
1179:
974:
903:
891:
839:
804:
747:
735:
692:
655:
620:
583:
787:
Kafri, O.; Keren, E. (1987). "Encryption of pictures and shapes by random grids".
632:
511:
16:
1540:
148:
950:
935:
1571:
1463:
1399:
1254:
1174:
1135:
1083:
1068:
107:
51:
895:
774:
761:
739:
624:
1638:
1618:
1545:
1335:
1290:
1249:
1229:
1125:
1088:
1063:
558:
979:
962:
1499:
1441:
1285:
1130:
1120:
1110:
1073:
1022:
816:
704:
539:
120:
89:
55:
36:
1520:
1429:
1264:
808:
1613:
1608:
1535:
1530:
1494:
1489:
1484:
1479:
1224:
1194:
1189:
1150:
587:
515:
Overlaying component images with letters A and B to reveal the letter S
165:
47:
696:
1566:
1214:
843:
168:
in 1994. In this scheme we have a secret image which is encoded into
161:
123:
has been split into two component images. Each component image has a
112:
43:
857:
Askari, Nazanin; Moloney, Cecilia; Heys, Howard M. (November 2011).
1259:
1219:
687:
582:. Lecture Notes in Computer Science. Vol. 950. pp. 1–12.
482:
136:
component image that combines with it to produce any image at all.
1368:
1586:
88:
Using a similar idea, transparencies can be used to implement a
1140:
860:
Application of Visual
Cryptography to Biometric Authentication
1515:
936:
Java implementation and illustrations of Visual
Cryptography
645:
139:
946:
578:
Naor, Moni; Shamir, Adi (1995). "Visual cryptography".
50:, who developed it in 1994. They demonstrated a visual
1161:
Cryptographically secure pseudorandom number generator
359:
210:
42:
One of the best-known techniques has been credited to
338:
189:
156:
Sharing a secret with an arbitrary number of people,
987:
832:IEEE Transactions on Systems, Man, and Cybernetics
829:
610:
468:
319:
856:
725:
1636:
960:
672:
1384:
1007:
881:
963:"Personalized Shares in Visual Cryptography"
941:Python implementation of Visual Cryptography
762:Cryptographic process and enciphered product
332:{all permutations of the columns of} :
183:{all permutations of the columns of} :
491:Horng et al. proposed a method that allows
1391:
1377:
1014:
1000:
961:Hammoudi, Karim; Melkemi, Mahmoud (2018).
786:
577:
66:shares could decrypt the image, while any
978:
686:
132:use the shading rules above to produce a
775:Information encoding and decoding method
510:
147:
106:
15:
951:Doug Stinson's visual cryptography page
506:
20:Development of masks to let overlaying
1637:
1372:
995:
580:Advances in Cryptology – EUROCRYPT'94
527:
62:shares so that only someone with all
1398:
13:
144:) visual cryptography sharing case
14:
1656:
929:
777:, United States patent 3,279,095.
764:, United States patent 4,682,954.
1349:
1348:
1021:
350:
345:
341:
201:
196:
192:
910:
884:Designs, Codes and Cryptography
875:
850:
613:Designs, Codes and Cryptography
537:", a 1967 episode of TV series
535:Do Not Forsake Me Oh My Darling
1210:Information-theoretic security
823:
780:
767:
754:
719:
666:
639:
604:
571:
487:) visual secret sharing scheme
1:
916:M. Pramanik, Kalpana Sharma,
660:10.1016/S0304-3975(99)00127-9
564:
648:Theoretical Computer Science
7:
1326:Message authentication code
1281:Cryptographic hash function
1094:Cryptographic hash function
547:
10:
1661:
1599:Observer-expectancy effect
1205:Harvest now, decrypt later
102:
1559:
1526:Paranoiac-critical method
1508:
1472:
1422:
1406:
1344:
1321:Post-quantum cryptography
1273:
1029:
991:
896:10.1007/s10623-005-6342-0
740:10.1080/0161-110291890768
1311:Quantum key distribution
1301:Authenticated encryption
1156:Random number generation
922:, Computer Science, 2014
773:Carlson, Carl O. (1961)
760:Cook, Richard C. (1960)
1306:Public-key cryptography
1296:Symmetric-key algorithm
1099:Key derivation function
1059:Cryptographic primitive
1052:Authentication protocol
1042:Outline of cryptography
1037:History of cryptography
980:10.3390/jimaging4110126
625:10.1023/A:1008280705142
1047:Cryptographic protocol
516:
470:
321:
153:
116:
29:
1200:End-to-end encryption
1146:Cryptojacking malware
554:Grille (cryptography)
514:
471:
322:
151:
119:In this example, the
110:
19:
1316:Quantum cryptography
1240:Trusted timestamping
809:10.1364/OL.12.000377
507:Visual steganography
336:
187:
1604:Pattern recognition
1577:Clustering illusion
1551:Visual cryptography
1079:Cryptographic nonce
801:1987OptL...12..377K
58:was broken up into
33:Visual cryptography
1414:Subliminal message
1185:Subliminal channel
1169:Pseudorandom noise
1116:Key (cryptography)
967:Journal of Imaging
588:10.1007/BFb0053419
528:In popular culture
517:
466:
457:
317:
308:
154:
117:
30:
1632:
1631:
1582:Cryptic crossword
1459:Phonetic reversal
1366:
1365:
1362:
1361:
1245:Key-based routing
1235:Trapdoor function
1106:Digital signature
697:10.1364/OE.383240
597:978-3-540-60176-0
483:Cheating the (2,
1652:
1624:Unconscious mind
1393:
1386:
1379:
1370:
1369:
1352:
1351:
1180:Insecure channel
1016:
1009:
1002:
993:
992:
989:
988:
984:
982:
923:
914:
908:
907:
879:
873:
872:
870:
868:
854:
848:
847:
844:10.1109/21.44016
838:(5): 1016–1020.
827:
821:
820:
784:
778:
771:
765:
758:
752:
751:
723:
717:
716:
690:
681:(5): 7301–7313.
670:
664:
663:
654:(1–2): 143–161.
643:
637:
636:
608:
602:
601:
575:
497:
475:
473:
472:
467:
462:
461:
353:
349:
348:
326:
324:
323:
318:
313:
312:
204:
200:
199:
72:
54:scheme, where a
1660:
1659:
1655:
1654:
1653:
1651:
1650:
1649:
1635:
1634:
1633:
1628:
1555:
1541:Sacred geometry
1504:
1468:
1418:
1402:
1400:Hidden messages
1397:
1367:
1358:
1340:
1269:
1025:
1020:
932:
927:
926:
915:
911:
880:
876:
866:
864:
855:
851:
828:
824:
785:
781:
772:
768:
759:
755:
724:
720:
671:
667:
644:
640:
609:
605:
598:
576:
572:
567:
550:
530:
509:
492:
489:
456:
455:
450:
439:
434:
428:
427:
415:
414:
409:
398:
393:
387:
386:
381:
370:
365:
355:
354:
344:
340:
339:
337:
334:
333:
307:
306:
301:
290:
285:
279:
278:
266:
265:
260:
249:
244:
238:
237:
232:
221:
216:
206:
205:
195:
191:
190:
188:
185:
184:
146:
105:
67:
12:
11:
5:
1658:
1648:
1647:
1630:
1629:
1627:
1626:
1621:
1616:
1611:
1606:
1601:
1596:
1591:
1590:
1589:
1579:
1574:
1572:Asemic writing
1569:
1563:
1561:
1557:
1556:
1554:
1553:
1548:
1543:
1538:
1533:
1528:
1523:
1518:
1512:
1510:
1506:
1505:
1503:
1502:
1497:
1492:
1487:
1482:
1476:
1474:
1470:
1469:
1467:
1466:
1464:Reverse speech
1461:
1456:
1455:
1454:
1449:
1439:
1438:
1437:
1426:
1424:
1420:
1419:
1417:
1416:
1410:
1408:
1404:
1403:
1396:
1395:
1388:
1381:
1373:
1364:
1363:
1360:
1359:
1357:
1356:
1345:
1342:
1341:
1339:
1338:
1333:
1331:Random numbers
1328:
1323:
1318:
1313:
1308:
1303:
1298:
1293:
1288:
1283:
1277:
1275:
1271:
1270:
1268:
1267:
1262:
1257:
1255:Garlic routing
1252:
1247:
1242:
1237:
1232:
1227:
1222:
1217:
1212:
1207:
1202:
1197:
1192:
1187:
1182:
1177:
1175:Secure channel
1172:
1166:
1165:
1164:
1153:
1148:
1143:
1138:
1136:Key stretching
1133:
1128:
1123:
1118:
1113:
1108:
1103:
1102:
1101:
1096:
1086:
1084:Cryptovirology
1081:
1076:
1071:
1069:Cryptocurrency
1066:
1061:
1056:
1055:
1054:
1044:
1039:
1033:
1031:
1027:
1026:
1019:
1018:
1011:
1004:
996:
986:
985:
958:
953:
948:
943:
938:
931:
930:External links
928:
925:
924:
909:
890:(2): 219–236.
874:
849:
822:
789:Optics Letters
779:
766:
753:
718:
675:Optics Express
665:
638:
619:(2): 179–196.
603:
596:
569:
568:
566:
563:
562:
561:
556:
549:
546:
545:
544:
529:
526:
508:
505:
488:
481:
465:
460:
454:
451:
449:
446:
443:
440:
438:
435:
433:
430:
429:
426:
423:
420:
417:
416:
413:
410:
408:
405:
402:
399:
397:
394:
392:
389:
388:
385:
382:
380:
377:
374:
371:
369:
366:
364:
361:
360:
358:
352:
347:
343:
316:
311:
305:
302:
300:
297:
294:
291:
289:
286:
284:
281:
280:
277:
274:
271:
268:
267:
264:
261:
259:
256:
253:
250:
248:
245:
243:
240:
239:
236:
233:
231:
228:
225:
222:
220:
217:
215:
212:
211:
209:
203:
198:
194:
145:
138:
104:
101:
52:secret sharing
9:
6:
4:
3:
2:
1657:
1646:
1643:
1642:
1640:
1625:
1622:
1620:
1619:Synchronicity
1617:
1615:
1612:
1610:
1607:
1605:
1602:
1600:
1597:
1595:
1592:
1588:
1585:
1584:
1583:
1580:
1578:
1575:
1573:
1570:
1568:
1565:
1564:
1562:
1558:
1552:
1549:
1547:
1546:Steganography
1544:
1542:
1539:
1537:
1534:
1532:
1529:
1527:
1524:
1522:
1519:
1517:
1514:
1513:
1511:
1507:
1501:
1498:
1496:
1493:
1491:
1488:
1486:
1483:
1481:
1478:
1477:
1475:
1471:
1465:
1462:
1460:
1457:
1453:
1450:
1448:
1445:
1444:
1443:
1440:
1436:
1433:
1432:
1431:
1428:
1427:
1425:
1421:
1415:
1412:
1411:
1409:
1405:
1401:
1394:
1389:
1387:
1382:
1380:
1375:
1374:
1371:
1355:
1347:
1346:
1343:
1337:
1336:Steganography
1334:
1332:
1329:
1327:
1324:
1322:
1319:
1317:
1314:
1312:
1309:
1307:
1304:
1302:
1299:
1297:
1294:
1292:
1291:Stream cipher
1289:
1287:
1284:
1282:
1279:
1278:
1276:
1272:
1266:
1263:
1261:
1258:
1256:
1253:
1251:
1250:Onion routing
1248:
1246:
1243:
1241:
1238:
1236:
1233:
1231:
1230:Shared secret
1228:
1226:
1223:
1221:
1218:
1216:
1213:
1211:
1208:
1206:
1203:
1201:
1198:
1196:
1193:
1191:
1188:
1186:
1183:
1181:
1178:
1176:
1173:
1170:
1167:
1162:
1159:
1158:
1157:
1154:
1152:
1149:
1147:
1144:
1142:
1139:
1137:
1134:
1132:
1129:
1127:
1126:Key generator
1124:
1122:
1119:
1117:
1114:
1112:
1109:
1107:
1104:
1100:
1097:
1095:
1092:
1091:
1090:
1089:Hash function
1087:
1085:
1082:
1080:
1077:
1075:
1072:
1070:
1067:
1065:
1064:Cryptanalysis
1062:
1060:
1057:
1053:
1050:
1049:
1048:
1045:
1043:
1040:
1038:
1035:
1034:
1032:
1028:
1024:
1017:
1012:
1010:
1005:
1003:
998:
997:
994:
990:
981:
976:
972:
968:
964:
959:
957:
954:
952:
949:
947:
944:
942:
939:
937:
934:
933:
921:
920:
913:
905:
901:
897:
893:
889:
885:
878:
862:
861:
853:
845:
841:
837:
833:
826:
818:
814:
810:
806:
802:
798:
794:
790:
783:
776:
770:
763:
757:
749:
745:
741:
737:
733:
729:
722:
714:
710:
706:
702:
698:
694:
689:
684:
680:
676:
669:
661:
657:
653:
649:
642:
634:
630:
626:
622:
618:
614:
607:
599:
593:
589:
585:
581:
574:
570:
560:
559:Steganography
557:
555:
552:
551:
542:
541:
536:
532:
531:
525:
521:
513:
504:
500:
495:
486:
480:
476:
463:
458:
452:
447:
444:
441:
436:
431:
424:
421:
418:
411:
406:
403:
400:
395:
390:
383:
378:
375:
372:
367:
362:
356:
330:
327:
314:
309:
303:
298:
295:
292:
287:
282:
275:
272:
269:
262:
257:
254:
251:
246:
241:
234:
229:
226:
223:
218:
213:
207:
181:
179:
174:
171:
167:
163:
159:
150:
143:
137:
135:
129:
126:
122:
115:logo appears.
114:
109:
100:
97:
94:
91:
86:
84:
80:
76:
70:
65:
61:
57:
53:
49:
45:
40:
38:
37:cryptographic
34:
27:
23:
18:
1645:Cryptography
1550:
1442:Hidden track
1286:Block cipher
1131:Key schedule
1121:Key exchange
1111:Kleptography
1074:Cryptosystem
1023:Cryptography
970:
966:
918:
912:
887:
883:
877:
865:. Retrieved
863:. NECEC 2011
859:
852:
835:
831:
825:
795:(6): 377–9.
792:
788:
782:
769:
756:
731:
727:
721:
678:
674:
668:
651:
647:
641:
616:
612:
606:
579:
573:
540:The Prisoner
538:
522:
518:
501:
493:
490:
484:
477:
331:
328:
182:
177:
175:
169:
157:
155:
141:
133:
130:
124:
121:binary image
118:
98:
95:
90:one-time pad
87:
82:
78:
74:
68:
63:
59:
56:binary image
41:
32:
31:
25:
21:
1521:Hidden text
1452:pregap list
1430:Backmasking
1274:Mathematics
1265:Mix network
973:(11): 126.
867:12 February
728:Cryptologia
134:counterfeit
1614:Simulacrum
1609:Palindrome
1594:Easter egg
1536:Psychorama
1531:Pareidolia
1500:Cryptology
1495:Bible code
1490:Theomatics
1485:Numerology
1480:Chronogram
1225:Ciphertext
1195:Decryption
1190:Encryption
1151:Ransomware
688:1911.05033
565:References
166:Adi Shamir
48:Adi Shamir
1567:Apophenia
1215:Plaintext
734:: 68–76.
713:207863416
162:Moni Naor
113:Knowledge
44:Moni Naor
1639:Category
1354:Category
1260:Kademlia
1220:Codetext
1163:(CSPRNG)
817:19741737
705:32225961
548:See also
81:-out-of-
1587:Anagram
1473:Numeric
1030:General
904:2109660
797:Bibcode
748:7995141
103:Example
1509:Visual
1141:Keygen
902:
815:
746:
711:
703:
633:479227
631:
594:
93:100%.
1560:Other
1516:Fnord
1423:Audio
1171:(PRN)
900:S2CID
744:S2CID
709:S2CID
683:arXiv
629:S2CID
35:is a
1447:list
1435:list
1407:Main
869:2015
813:PMID
701:PMID
592:ISBN
533:In "
164:and
140:(2,
125:pair
46:and
975:doi
892:doi
840:doi
805:doi
736:doi
693:doi
656:doi
652:250
621:doi
584:doi
496:− 1
71:− 1
1641::
969:.
965:.
898:.
888:38
886:.
836:19
834:.
811:.
803:.
793:12
791:.
742:.
732:26
730:.
707:.
699:.
691:.
679:28
677:.
650:.
627:.
617:11
615:.
590:.
1392:e
1385:t
1378:v
1015:e
1008:t
1001:v
983:.
977::
971:4
906:.
894::
871:.
846:.
842::
819:.
807::
799::
750:.
738::
715:.
695::
685::
662:.
658::
635:.
623::
600:.
586::
494:n
485:n
464:.
459:]
453:1
448:.
445:.
442:.
437:0
432:0
425:.
422:.
419:.
412:0
407:.
404:.
401:.
396:1
391:0
384:0
379:.
376:.
373:.
368:0
363:1
357:[
351:=
346:1
342:C
315:.
310:]
304:0
299:.
296:.
293:.
288:0
283:1
276:.
273:.
270:.
263:0
258:.
255:.
252:.
247:0
242:1
235:0
230:.
227:.
224:.
219:0
214:1
208:[
202:=
197:0
193:C
178:n
170:n
158:n
142:n
83:n
79:k
75:n
69:n
64:n
60:n
26:n
22:n
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.