177:
185:
228:
25:
157:
298:, and others. The dongle used by Steinberg's products is also known as a Steinberg Key. The Steinberg Key can be purchased separately from its counterpart applications and generally comes bundled with the "Syncrosoft License Control Center" application, which is cross-platform compatible with both Mac OS X and Windows.
333:
that execute program instructions that may be input to the cryptoprocessor only in encrypted form. The original secure cryptoprocessor was designed for copy protection of personal computer software (see US Patent 4,168,396, Sept 18, 1979) to provide more security than dongles could then provide. See
410:
use a dongle. Typically it attaches to the memory card slot of the system, with the disc based software refusing to work if the dongle is not detected. The dongle is also used for holding settings and storage of new codes, added either by the user or through official updates, because the disc, being
269:
In cases such as prepress and printing software, the dongle is encoded with a specific, per-user license key, which enables particular features in the target application. This is a form of tightly controlled licensing, which allows the vendor to engage in vendor lock-in and charge more than it would
305:
Although such medium security may deter a casual hacker, the lack of a processor core in the dongle to authenticate data, perform encryption/decryption, and execute inaccessible binary code makes such a passive dongle inappropriate for all but the lowest-priced software. A simpler and even less
301:
Some software developers use traditional USB flash drives as software license dongles that contain hardware serial numbers in conjunction with the stored device ID strings, which are generally not easily changed by an end-user. A developer can also use the dongle to store user settings or even a
152:
In software protection, dongles are two-interface security tokens with transient data flow with a pull communication that reads security data from the dongle. In the absence of these dongles, certain software may run only in a restricted mode, or not at all. In addition to software protection,
306:
secure option is to use unpartitioned or unallocated storage in the dongle to store license data. Common USB flash drives are relatively inexpensive compared to dedicated security dongle devices, but reading and storing data in a flash drive are easy to intercept, alter, and bypass.
282:
output device is sold to a customer, Prinergy's own license cost is provided separately to the customer, and the base price contains little more than the required licenses to output work to the device.
238:
Efforts to introduce dongle copy-protection in the mainstream software market have met stiff resistance from users. Such copy-protection is more typically used with very expensive packages and
352:
process which transfers encrypted parts of the software vendor's program code or license enforcement into a secure hardware environment (such as in a smart card OS, mentioned above). An
318:
to check for the dongle's presence, returning "true" or "false" accordingly, but the dongle requirement can be easily circumvented by modifying the software to always answer "true".
314:
There are potential weaknesses in the implementation of the protocol between the dongle and the copy-controlled software. For example, a simple implementation might define a
302:
complete "portable" version of the application. Not all flash drives are suitable for this use, as not all manufacturers install unique serial numbers into their devices.
342:
341:
Hardware cloning, where the dongle is emulated by a device driver, is also a threat to traditional dongles. To thwart this, some dongle vendors adopted
647:
349:
1054:
193:
89:
42:
61:
345:, which is widely used in extremely rigid security requirement environments such as military and banking, in their dongle products.
68:
153:
dongles can enable functions in electronic devices, such as receiving and processing encoded video streams on television sets.
137:
and content protection device. When connected to a computer or other electronics, they unlock software functionality or decode
180:
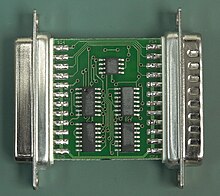
A Rainbow Tech parallel port dongle PCB, front side. Note the numbers rubbed off the chips to make reverse engineering harder
367:, they are easily lost and prone to damage, potentially increasing operational costs such as device cost and delivery cost.
75:
231:
640:
1064:
57:
537:
329:— essential parts of the software may actually be stored and executed on the dongle. Thus dongles have become
108:
699:
633:
491:
46:
1069:
682:
247:
1074:
930:
353:
82:
878:
215:
claimed the word dongle was derived from the name "Don Gall". Though untrue, this has given rise to an
993:
719:
483:
420:
259:
321:
Modern dongles include built-in strong encryption and use fabrication techniques designed to thwart
1059:
903:
1023:
523:
35:
842:
714:
381:
330:
862:
704:
656:
450:
243:
472:
145:
or other cryptographic protection mechanism and functions via an electrical connector to an
953:
837:
827:
709:
692:
326:
212:
201:
8:
958:
943:
740:
322:
1018:
1008:
963:
677:
435:
263:
1033:
973:
948:
772:
620:
543:
533:
497:
487:
364:
279:
589:
568:
411:
read only, cannot store them. Some dongles will also double as normal memory cards.
847:
664:
357:
291:
1028:
1003:
985:
852:
789:
745:
425:
387:
239:
192:
Dongles rapidly evolved into active devices that contained a serial transceiver (
138:
134:
1079:
529:
445:
440:
335:
255:
197:
605:
1048:
908:
687:
547:
501:
430:
407:
392:
176:
184:
832:
794:
782:
757:
479:
376:
146:
395:, in order to circumvent the authentication chip embedded in the console.
173:" was in 1981 and that the etymology was "perhaps alteration of dangle."
1013:
938:
888:
752:
205:
142:
625:
920:
893:
857:
399:
315:
227:
216:
968:
915:
811:
799:
403:
287:
24:
777:
767:
762:
672:
275:
169:
The
Merriam-Webster dictionary states that the "First known use of
156:
898:
883:
804:
200:
to handle transactions with the host. Later versions adopted the
735:
295:
170:
160:
HASP (Hardware
Against Software Piracy) key dongle for LPT port
363:
In addition, dongles have been criticized because as they are
271:
251:
204:
interface, which became the preferred choice over the
348:A more innovative modern dongle is designed with a
49:. Unsourced material may be challenged and removed.
471:
188:A Rainbow Tech parallel port dongle PCB, back side
391:) used dongles to connect to officially licensed
290:'s audio production and editing systems, such as
270:otherwise for the product. An example is the way
1046:
641:
648:
634:
16:Electronic software copy protection device
655:
356:can port thousands of lines of important
258:hospitality and special retail software,
109:Learn how and when to remove this message
469:
252:cellphone flasher/JTAG debugger software
226:
183:
175:
155:
141:. The hardware key is programmed with a
1047:
521:
234:parallel port copy protection dongles.
629:
470:Amos, S. W.; Amos, Roger S. (2002).
47:adding citations to reliable sources
18:
325:. Typical dongles also now contain
286:USB dongles are also a big part of
13:
1055:Copyright infringement of software
14:
1091:
614:
474:Newnes Dictionary of Electronics
370:
23:
34:needs additional citations for
599:
583:
561:
515:
463:
149:of the computer or appliance.
1:
456:
164:
58:"Software protection dongle"
7:
931:Software release life cycle
522:Stobbs, Gregory A. (2012).
414:
375:Some unlicensed titles for
10:
1096:
999:Software protection dongle
879:Unwanted software bundling
123:software protection dongle
1065:Digital rights management
994:Digital rights management
984:
929:
871:
820:
728:
663:
421:Digital rights management
309:
260:digital audio workstation
211:A 1992 advertisement for
872:Deceptive and/or illicit
222:
1024:Software license server
331:secure cryptoprocessors
294:, WaveLab, Hypersonic,
262:applications, and some
208:or parallel interface.
700:Freely redistributable
360:code into the dongle.
235:
189:
181:
161:
863:Software as a service
657:Software distribution
451:Software monetization
402:devices, such as the
278:to customers: When a
230:
187:
179:
159:
125:(commonly known as a
1070:Proprietary hardware
954:Software maintenance
828:Digital distribution
683:Free and open-source
213:Rainbow Technologies
43:improve this article
959:Software maintainer
741:Commercial software
729:Compensation models
621:Jargon File: dongle
606:US Patent 4,168,396
382:Super 3D Noah's Ark
327:non-volatile memory
323:reverse engineering
133:) is an electronic
1075:Software licensing
1019:Software copyright
1009:Product activation
964:Software publisher
678:Floating licensing
528:(Third ed.).
436:Product activation
343:smart card product
264:translation memory
236:
190:
182:
162:
1042:
1041:
1034:Torrent poisoning
949:Long-term support
773:Pay what you want
571:. Merriam-Webster
532:. pp. 2–90.
280:computer-to-plate
242:software such as
119:
118:
111:
93:
1087:
848:Product bundling
821:Delivery methods
720:Source-available
650:
643:
636:
627:
626:
608:
603:
597:
596:Magazine, p. 148
587:
581:
580:
578:
576:
565:
559:
558:
556:
554:
525:Software Patents
519:
513:
512:
510:
508:
478:(4th ed.).
477:
467:
358:computer program
114:
107:
103:
100:
94:
92:
51:
27:
19:
1095:
1094:
1090:
1089:
1088:
1086:
1085:
1084:
1060:Copy protection
1045:
1044:
1043:
1038:
1029:Software patent
1004:License manager
986:Copy protection
980:
925:
867:
853:Retail software
816:
790:Open-core model
746:Retail software
724:
659:
654:
617:
612:
611:
604:
600:
590:Sentinel advert
588:
584:
574:
572:
567:
566:
562:
552:
550:
540:
520:
516:
506:
504:
494:
468:
464:
459:
426:License manager
417:
388:Little Red Hood
373:
312:
240:vertical market
225:
167:
135:copy protection
115:
104:
98:
95:
52:
50:
40:
28:
17:
12:
11:
5:
1093:
1083:
1082:
1077:
1072:
1067:
1062:
1057:
1040:
1039:
1037:
1036:
1031:
1026:
1021:
1016:
1011:
1006:
1001:
996:
990:
988:
982:
981:
979:
978:
977:
976:
966:
961:
956:
951:
946:
941:
935:
933:
927:
926:
924:
923:
918:
913:
912:
911:
906:
901:
896:
891:
881:
875:
873:
869:
868:
866:
865:
860:
855:
850:
845:
840:
835:
830:
824:
822:
818:
817:
815:
814:
809:
808:
807:
797:
792:
787:
786:
785:
780:
770:
765:
760:
755:
750:
749:
748:
738:
732:
730:
726:
725:
723:
722:
717:
712:
707:
702:
697:
696:
695:
690:
680:
675:
669:
667:
661:
660:
653:
652:
645:
638:
630:
624:
623:
616:
615:External links
613:
610:
609:
598:
582:
560:
538:
530:Wolters Kluwer
514:
492:
461:
460:
458:
455:
454:
453:
448:
446:Trusted client
443:
441:Security token
438:
433:
428:
423:
416:
413:
393:ROM cartridges
372:
369:
336:bus encryption
311:
308:
256:MICROS Systems
224:
221:
198:microprocessor
166:
163:
117:
116:
31:
29:
22:
15:
9:
6:
4:
3:
2:
1092:
1081:
1078:
1076:
1073:
1071:
1068:
1066:
1063:
1061:
1058:
1056:
1053:
1052:
1050:
1035:
1032:
1030:
1027:
1025:
1022:
1020:
1017:
1015:
1012:
1010:
1007:
1005:
1002:
1000:
997:
995:
992:
991:
989:
987:
983:
975:
972:
971:
970:
967:
965:
962:
960:
957:
955:
952:
950:
947:
945:
942:
940:
937:
936:
934:
932:
928:
922:
919:
917:
914:
910:
907:
905:
902:
900:
897:
895:
892:
890:
887:
886:
885:
882:
880:
877:
876:
874:
870:
864:
861:
859:
856:
854:
851:
849:
846:
844:
843:Pre-installed
841:
839:
836:
834:
831:
829:
826:
825:
823:
819:
813:
810:
806:
803:
802:
801:
798:
796:
793:
791:
788:
784:
781:
779:
776:
775:
774:
771:
769:
766:
764:
761:
759:
756:
754:
751:
747:
744:
743:
742:
739:
737:
734:
733:
731:
727:
721:
718:
716:
715:Public domain
713:
711:
708:
706:
703:
701:
698:
694:
691:
689:
686:
685:
684:
681:
679:
676:
674:
671:
670:
668:
666:
662:
658:
651:
646:
644:
639:
637:
632:
631:
628:
622:
619:
618:
607:
602:
595:
591:
586:
570:
564:
549:
545:
541:
539:9781454811978
535:
531:
527:
526:
518:
503:
499:
495:
489:
485:
481:
476:
475:
466:
462:
452:
449:
447:
444:
442:
439:
437:
434:
432:
431:Lock-out chip
429:
427:
424:
422:
419:
418:
412:
409:
408:Action Replay
405:
401:
396:
394:
390:
389:
384:
383:
378:
377:game consoles
371:Game consoles
368:
366:
361:
359:
355:
351:
346:
344:
339:
337:
332:
328:
324:
319:
317:
307:
303:
299:
297:
293:
289:
284:
281:
277:
273:
267:
265:
261:
257:
253:
249:
245:
241:
233:
232:Daisy chained
229:
220:
218:
214:
209:
207:
203:
199:
196:) and even a
195:
186:
178:
174:
172:
158:
154:
150:
148:
144:
140:
136:
132:
128:
124:
113:
110:
102:
91:
88:
84:
81:
77:
74:
70:
67:
63:
60: –
59:
55:
54:Find sources:
48:
44:
38:
37:
32:This article
30:
26:
21:
20:
998:
904:Trojan horse
833:File sharing
795:Postcardware
783:Donationware
758:Crowdfunding
705:License-free
601:
593:
585:
573:. Retrieved
563:
551:. Retrieved
524:
517:
505:. Retrieved
480:Newnes Press
473:
465:
397:
386:
380:
374:
362:
350:code porting
347:
340:
320:
313:
304:
300:
285:
268:
237:
210:
191:
168:
151:
147:external bus
130:
126:
122:
120:
105:
96:
86:
79:
72:
65:
53:
41:Please help
36:verification
33:
1014:Product key
944:End-of-life
939:Abandonware
889:Infostealer
838:On-premises
753:Crippleware
710:Proprietary
693:Open source
143:product key
1049:Categories
921:Shovelware
894:Ransomware
858:Sneakernet
493:0750643315
482:. p.
457:References
400:cheat code
266:packages.
250:software,
217:urban myth
99:March 2008
69:newspapers
969:Vaporware
916:Scareware
812:Trialware
800:Shareware
548:802867781
502:144646016
404:GameShark
379:(such as
288:Steinberg
274:licenses
165:Etymology
778:Careware
768:Freeware
763:Freemium
673:Beerware
665:Licenses
569:"Dongle"
415:See also
365:hardware
316:function
276:Prinergy
899:Spyware
884:Malware
805:Nagware
575:11 June
139:content
83:scholar
736:Adware
553:4 July
546:
536:
507:4 July
500:
490:
310:Issues
296:HALion
292:Cubase
206:serial
171:dongle
127:dongle
85:
78:
71:
64:
56:
1080:Warez
398:Some
334:also
272:Kodak
223:Usage
90:JSTOR
76:books
974:list
909:Worm
688:Free
594:Byte
577:2019
555:2013
544:OCLC
534:ISBN
509:2013
498:OCLC
488:ISBN
406:and
194:UART
62:news
484:152
385:or
354:ISV
248:CAM
244:CAD
202:USB
131:key
129:or
45:by
1051::
592:,
542:.
496:.
486:.
338:.
254:,
219:.
121:A
649:e
642:t
635:v
579:.
557:.
511:.
246:/
112:)
106:(
101:)
97:(
87:·
80:·
73:·
66:·
39:.
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.