253:
port is on the same computer as the SSH client, and this port is the "forwarded port". On the same computer, any client that wants to connect to the same destination host and port can be configured to connect to the forwarded port (rather than directly to the destination host and port). After this connection is established, the SSH client listens on the forwarded port and directs all data sent by applications to that port, through a secure tunnel to the SSH server. The server decrypts the data, and then redirects it to the destination host and port.
20:
302:
DPF can be implemented by setting up a local application, such as SSH, as a SOCKS proxy server, which can be used to process data transmissions through the network or over the
Internet. Programs, such as web browsers, must be configured individually to direct traffic through the proxy, which acts as
252:
Connections from an SSH client are forwarded, via an SSH server, to the intended destination server. The SSH server is configured to redirect data from a specified port (which is local to the host that runs the SSH client) through a secure tunnel to some specified destination host and port. The local
193:
kernels, this is DNAT rule). The source address and port are, in this case, left unchanged. When used on machines that are not the default gateway of the network, the source address must be changed to be the address of the translating machine, or packets will bypass the translator and the connection
298:
Dynamic port forwarding (DPF) is an on-demand method of traversing a firewall or NAT through the use of firewall pinholes. The goal is to enable clients to connect securely to a trusted server that acts as an intermediary for the purpose of sending/receiving data to one or many destination servers.
284:
An employee of a company hosts an FTP server at their own home and wants to give access to the FTP service to employees using computers in the workplace. In order to do this, an employee can set up remote port forwarding through SSH on the company's internal computers by including their FTP server’s
272:
This form of port forwarding enables applications on the server side of a Secure Shell (SSH) connection to access services residing on the SSH's client side. In addition to SSH, there are proprietary tunnelling schemes that utilize remote port forwarding for the same general purpose. In other words,
113:
When configuring port forwarding, the network administrator sets aside one port number on the gateway for the exclusive use of communicating with a service in the private network, located on a specific host. External hosts must know this port number and the address of the gateway to communicate with
306:
Once the connection is established, DPF can be used to provide additional security for a user connected to an untrusted network. Since data must pass through the secure tunnel to another server before being forwarded to its original destination, the user is protected from packet sniffing that may
208:
Unix-like operating systems sometimes use port forwarding where port numbers smaller than 1024 can only be created by software running as the root user. Running with superuser privileges (in order to bind the port) may be a security risk to the host, therefore port forwarding is used to redirect a
310:
DPF is a powerful tool with many uses; for example, a user connected to the
Internet through a coffee shop, hotel, or otherwise minimally secure network may wish to use DPF as a way of protecting data. DPF can also be used to bypass firewalls that restrict access to outside websites, such as in
114:
the network-internal service. Often, the port numbers of well-known
Internet services, such as port number 80 for web services (HTTP), are used in port forwarding, so that common Internet services may be implemented on hosts within private networks.
244:
Local port forwarding is the most common type of port forwarding. It is used to let a user connect from the local computer to another server, i.e. forward data securely from another client application running on the same computer as a
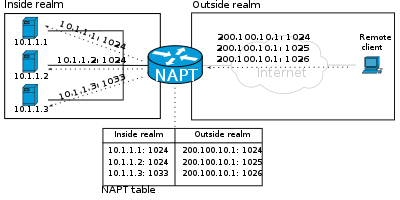
110:. The NAT device's external interface is configured with a public IP address. The computers behind the router, on the other hand, are invisible to hosts on the Internet as they each communicate only with a private IP address.
224:(SSDP). An application that provides an Internet-based service may discover such gateways and use the UPnP IGD protocol to reserve a port number on the gateway and cause the gateway to forward packets to its listening
201:
based firewalls, or via TCP circuit proxies), then no packets are actually translated, only data is proxied. This usually results in the source address (and port number) being changed to that of the proxy machine.
288:
Opening remote desktop sessions is a common use of remote port forwarding. Through SSH, this can be accomplished by opening the virtual network computing port (5900) and including the destination computer’s
276:
To use remote port forwarding, the address of the destination server (on the tunnel's client side) and two port numbers must be known. The port numbers chosen depend on which application is to be used.
303:
a secure tunnel to another server. Once the proxy is no longer needed, the programs must be reconfigured to their original settings. Because of the manual requirements of DPF, it is not often used.
71:(internal) network available to hosts on the opposite side of the gateway (external network), by remapping the destination IP address and port number of the communication to an internal host.
205:
Usually only one of the private hosts can use a specific forwarded port at one time, but configuration is sometimes possible to differentiate access by the originating host's source address.
377:
273:
remote port forwarding lets users connect from the server side of a tunnel, SSH or another, to a remote network service located at the tunnel's client side.
561:
209:
low-numbered port to another high-numbered port, so that application software may execute as a common operating system user with reduced privileges.
591:
216:
protocol (UPnP) provides a feature to automatically install instances of port forwarding in residential
Internet gateways. UPnP defines the
432:
189:
When used on gateway devices, a port forward may be implemented with a single rule to translate the destination address and port. (On
699: – Lightweight and easy-to-use .NET class library to allow port forwarding in NAT devices that support UPNP and PMP.
662:
385:
728:
687: – Free software which uses UPnP and the Internet Gateway Device Protocol (IGD) to automate port forwarding
718:
221:
220:(IGD) which is a network service by which an Internet gateway advertises its presence on a private network via the
217:
236:
Port forwarding may be distinguished by the following specific types: local, remote, and dynamic port forwarding.
569:
280:
Remote port forwarding allows other computers to access applications hosted on remote servers. Two examples:
519:
473:"Local and Remote Port Forwarding and the Reflection for Secure IT Client 7.1 or Higher - Tech Note 2433"
40:
520:"Example — Using Local Port Forwarding to Receive Mail (System Administration Guide: Security Services)"
249:(SSH) client. By using local port forwarding, firewalls that block certain web pages, can be bypassed.
103:
690:
637:
595:
326:
540:
347:
106:(NAT/NAPT). Hosts on the private network are connected to an Ethernet switch or communicate via a
213:
616:
498:
460:
197:
When a port forward is implemented by a proxy process (such as on application layer firewalls,
440:
320:
60:
8:
666:
28:
670:
358:
99:
84:
56:
342:
684:
723:
472:
332:
638:"SSH Dynamic Port Forwarding (Hacking Illustrated Series InfoSec Tutorial Videos)"
353:
285:
address and using the correct port numbers for FTP (standard FTP port is TCP/21)
225:
68:
146:
Administrators configure port forwarding in the gateway's operating system. In
64:
52:
712:
411:
337:
183:
179:
167:
79:
Port forwarding facilitates the connection by remote computers, for example,
407:
246:
129:
107:
381:
95:
90:
In a typical residential network, nodes obtain
Internet access through a
48:
696:
171:
44:
155:
91:
693: – Source code in C# explaining/PoC TCP forwarding.
151:
80:
541:"Tunneling with Secure Shell - Appendix A: Remote Port Forwarding"
436:
702:
685:
Using UPnP for
Programmatic Port Forwardings and NAT Traversal
499:"SSH/OpenSSH/PortForwarding - Community Ubuntu Documentation"
198:
190:
175:
163:
147:
142:
Running a publicly available game server within a private LAN
63:. This technique is most commonly used to make services on a
122:
19:
430:
159:
136:
408:"Using ssh Port Forwarding to Print at Remote Locations"
150:
kernels, this is achieved by packet filter rules in the
263:
Connect from a laptop to a website using an SSH tunnel.
594:. Compnetworking.about.com. 2013-12-19. Archived from
43:(NAT) that redirects a communication request from one
132:
access to a host on the private LAN from the
Internet
139:
access to a host on a private LAN from the
Internet
83:hosts, to a specific computer or service within a
710:
663:"Warp Speed Web Access: Sharing the Bandwidth"
260:Using local port forwarding to receive mail
117:Typical applications include the following:
55:are traversing a network gateway, such as a
293:
256:Some uses of local port forwarding :
660:
493:
491:
489:
267:
239:
18:
405:
711:
486:
562:"Local versus Remote Port Forwarding"
475:. Support.attachmate.com. 2012-11-09
13:
592:"FTP Port Number 21 - Port 21 TCP"
14:
740:
654:
433:"How to set up a home web server"
222:Simple Service Discovery Protocol
178:operating systems beginning with
170:(OS 10.10.X) implement it in the
51:combination to another while the
691:TCP forwarding source code in C#
378:"Definition of: port forwarding"
218:Internet Gateway Device Protocol
630:
609:
584:
554:
533:
512:
465:
454:
424:
399:
370:
23:Port forwarding via NAT router
1:
501:. Help.ubuntu.com. 2013-12-13
364:
705:Port Forwarding Testing Tool
7:
729:Network address translation
314:
166:operating systems prior to
125:server within a private LAN
67:residing on a protected or
41:network address translation
16:Computer networking feature
10:
745:
104:network address translator
74:
719:Computer network security
543:. Vandyke.com. 2005-06-12
327:NAT Port Mapping Protocol
348:Port address translation
231:
461:OpenSSH Port forwarding
294:Dynamic port forwarding
214:Universal Plug and Play
268:Remote port forwarding
24:
431:Jeff "Crash" Goldin.
321:Port Control Protocol
240:Local port forwarding
39:is an application of
22:
311:corporate networks.
182:implement it in the
174:(ipfw) module while
619:. Pages.cs.wisc.edu
158:kernel components.
29:computer networking
572:on 4 November 2016
359:UDP Helper Address
307:occur on the LAN.
85:local area network
25:
522:. Docs.oracle.com
343:Packet forwarding
121:Running a public
736:
681:
679:
678:
669:. Archived from
649:
648:
646:
645:
634:
628:
627:
625:
624:
613:
607:
606:
604:
603:
588:
582:
581:
579:
577:
568:. Archived from
558:
552:
551:
549:
548:
537:
531:
530:
528:
527:
516:
510:
509:
507:
506:
495:
484:
483:
481:
480:
469:
463:
458:
452:
451:
449:
448:
439:. Archived from
428:
422:
421:
419:
418:
403:
397:
396:
394:
393:
384:. Archived from
374:
333:Firewall pinhole
744:
743:
739:
738:
737:
735:
734:
733:
709:
708:
676:
674:
661:Alan Stafford.
657:
652:
643:
641:
636:
635:
631:
622:
620:
617:"DPF Mechanism"
615:
614:
610:
601:
599:
590:
589:
585:
575:
573:
560:
559:
555:
546:
544:
539:
538:
534:
525:
523:
518:
517:
513:
504:
502:
497:
496:
487:
478:
476:
471:
470:
466:
459:
455:
446:
444:
429:
425:
416:
414:
404:
400:
391:
389:
376:
375:
371:
367:
354:Port triggering
317:
296:
270:
242:
234:
98:connected to a
77:
33:port forwarding
17:
12:
11:
5:
742:
732:
731:
726:
721:
707:
706:
700:
694:
688:
682:
656:
655:External links
653:
651:
650:
640:. Irongeek.com
629:
608:
583:
553:
532:
511:
485:
464:
453:
423:
398:
368:
366:
363:
362:
361:
356:
351:
345:
340:
335:
330:
324:
316:
313:
295:
292:
291:
290:
286:
269:
266:
265:
264:
261:
241:
238:
233:
230:
144:
143:
140:
133:
126:
76:
73:
15:
9:
6:
4:
3:
2:
741:
730:
727:
725:
722:
720:
717:
716:
714:
704:
701:
698:
695:
692:
689:
686:
683:
673:on 2008-03-18
672:
668:
664:
659:
658:
639:
633:
618:
612:
598:on 2014-02-03
597:
593:
587:
571:
567:
563:
557:
542:
536:
521:
515:
500:
494:
492:
490:
474:
468:
462:
457:
443:on 2008-10-04
442:
438:
434:
427:
413:
412:Linux Journal
409:
406:Rory Krause.
402:
388:on 2012-06-03
387:
383:
379:
373:
369:
360:
357:
355:
352:
349:
346:
344:
341:
339:
338:NAT traversal
336:
334:
331:
328:
325:
322:
319:
318:
312:
308:
304:
300:
287:
283:
282:
281:
278:
274:
262:
259:
258:
257:
254:
250:
248:
237:
229:
227:
223:
219:
215:
210:
206:
203:
200:
195:
192:
187:
186:(pf) module.
185:
184:Packet Filter
181:
177:
173:
169:
165:
161:
157:
153:
149:
141:
138:
134:
131:
127:
124:
120:
119:
118:
115:
111:
109:
105:
101:
97:
93:
88:
86:
82:
72:
70:
66:
62:
58:
54:
50:
46:
42:
38:
34:
30:
21:
703:Port Checker
675:. Retrieved
671:the original
642:. Retrieved
632:
621:. Retrieved
611:
600:. Retrieved
596:the original
586:
574:. Retrieved
570:the original
566:NetworkActiv
565:
556:
545:. Retrieved
535:
524:. Retrieved
514:
503:. Retrieved
477:. Retrieved
467:
456:
445:. Retrieved
441:the original
426:
415:. Retrieved
401:
390:. Retrieved
386:the original
372:
309:
305:
301:
297:
279:
275:
271:
255:
251:
247:Secure Shell
243:
235:
211:
207:
204:
196:
188:
145:
130:Secure Shell
116:
112:
108:wireless LAN
89:
78:
37:port mapping
36:
32:
26:
382:PC Magazine
194:will fail.
135:Permitting
128:Permitting
96:cable modem
69:masqueraded
49:port number
713:Categories
677:2008-10-11
644:2014-01-30
623:2014-01-30
602:2014-01-30
547:2014-01-30
526:2014-01-30
505:2014-01-30
479:2014-01-30
447:2008-10-11
417:2008-10-11
392:2008-10-11
365:References
172:Ipfirewall
329:(NAT-PMP)
156:netfilter
697:Open.NAT
667:PC World
315:See also
289:address.
180:Yosemite
168:Yosemite
152:iptables
81:Internet
61:firewall
724:Routing
437:Red Hat
87:(LAN).
75:Purpose
53:packets
45:address
576:8 June
226:socket
100:router
57:router
350:(PAT)
323:(PCP)
232:Types
199:SOCKS
191:Linux
176:macOS
164:macOS
148:Linux
578:2014
212:The
162:and
123:HTTP
65:host
47:and
160:BSD
154:or
137:FTP
102:or
94:or
92:DSL
59:or
35:or
27:In
715::
665:.
564:.
488:^
435:.
410:.
380:.
228:.
31:,
680:.
647:.
626:.
605:.
580:.
550:.
529:.
508:.
482:.
450:.
420:.
395:.
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.