285:
387:
62:
159:
331:
to track sessions, when the user logs out, session-only cookies from that site will usually be deleted from the user's computer. In addition, the server invalidates any associations with the session, thereby making any session-handle in the user's cookie store useless.
343:. As a security precaution, one should not rely on implicit means of logging out of a system, especially not on a public computer; instead, one should explicitly log out and wait for confirmation that this request has taken place.
354:
set to activate after some period of inactivity, thereby requiring the user to re-enter their login credentials to unlock the screensaver and gain access to the system.
732:
644:
309:
or clicking on an external link. It can also be done implicitly, such as by the user powering off their workstation, closing a
681:
298:
Once the user is logged in, the login token may be used to track what actions the user has taken while connected to the site.
145:
126:
780:
98:
770:
622:
494:, different technical communities tend to prefer one over another – Unix, Novell, Linux, and Apple typically use
579:
288:
83:
653:
346:
Logging out of a computer, when leaving it, is a common security practice preventing unauthorized users from
105:
295:
Logging in is usually used to enter a specific page, website or application, which trespassers cannot see.
112:
742:
249:
775:
94:
347:
72:
79:
38:
320:
parameter, which specifies where to redirect back after logging in or out. For example, it is
248:
allows a user to use an existing cell phone number, or user credentials from another email or
658:
402:
17:
508:
By contrast, Microsoft's style guides traditionally suggested the opposite and prescribed
8:
448:
306:
51:
544:
471:
connotes the same idea but is based on the analogy of manually signing a log book or
456:
which was historically used to record distance traveled at sea and was recorded in a
413:
284:
195:
167:
47:
694:
617:
372:
302:
218:
211:
119:
574:
336:
317:
191:
313:
window, leaving a website, or not refreshing a website within a defined period.
559:
549:
409:
199:
187:
764:
554:
457:
340:
398:
245:
31:
386:
499:
351:
328:
310:
689:
417:
350:
with it. There are also people who choose to have a password-protected
214:
604:
737:
528:
520:
472:
61:
569:
453:
222:
478:
While there is no agreed difference in meaning between the terms
461:
390:
27:
Process by which an individual gains access to a computer system
564:
452:
of users' access to the system. The term "log" comes from the
718:"Use log on or log on to... Do not use log in, login", 2004,
425:
237:
225:. These credentials themselves are sometimes referred to as
584:
421:
241:
233:
158:
397:
The terms "login" and "logon" became common with the
693:. 30 April 2013. p. 96 & 97. Archived from
504:"Users log in to a file server (not log on to)...".
335:This feature comes in handy if the user is using a
86:. Unsourced material may be challenged and removed.
252:to sign in or create an account on a new website.
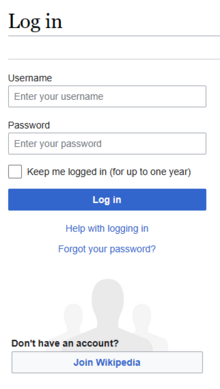
162:A screenshot of the English Knowledge login screen
305:takes an action, such as entering an appropriate
762:
30:"Logon" redirects here. Not to be confused with
260:When access is no longer needed, the user can
186:) is the process by which an individual gains
720:Manual of Style for Technical Publications
146:Learn how and when to remove this message
385:
381:
283:
232:. Modern secure systems often require a
157:
291:, a recent banking security application
14:
763:
535:terminology for local authentication.
301:Logging out may be performed when the
722:, 3rd edition, p. 295, Microsoft.com.
625:from the original on 25 December 2019
416:did not generally require them until
84:adding citations to reliable sources
55:
24:
25:
792:
712:
527:to access the Internet, but from
377:passwords (oral or textual input)
327:In the case of websites that use
244:confirmation for extra security.
50:. To log out from Knowledge, use
60:
316:A login page may have a return
71:needs additional citations for
733:"Sign in to or out of Windows"
725:
674:
637:
597:
580:Personal identification number
393:Version 4 console login prompt
339:or a computer that is using a
13:
1:
618:The Linux Information Project
590:
439:and by analogy with the verb
279:
46:To log in to Knowledge, use
7:
538:
531:onward it has moved to the
10:
797:
605:"Detail and definition of
341:public wireless connection
45:
36:
29:
401:systems of the 1960s and
250:social networking service
446:Computer systems keep a
781:Computer access control
771:Authentication methods
403:Bulletin Board Systems
394:
292:
163:
39:Login (disambiguation)
389:
382:History and etymology
369:Fingerprints scanning
358:Methods of Logging In
287:
161:
435:comes from the verb
405:(BBS) in the 1970s.
80:improve this article
37:For other uses, see
700:on 17 February 2015
682:"Apple Style Guide"
654:Oxford Dictionaries
745:on 28 October 2012
661:on 7 February 2014
414:personal computers
395:
293:
289:Finger print login
164:
52:Special:UserLogout
545:Computer security
366:Image recognition
168:computer security
156:
155:
148:
130:
48:Special:UserLogin
16:(Redirected from
788:
755:
754:
752:
750:
741:. Archived from
729:
723:
716:
710:
709:
707:
705:
699:
686:
678:
672:
670:
668:
666:
657:. Archived from
641:
635:
634:
632:
630:
601:
323:
206:User Credentials
151:
144:
140:
137:
131:
129:
88:
64:
56:
21:
796:
795:
791:
790:
789:
787:
786:
785:
776:User interfaces
761:
760:
759:
758:
748:
746:
731:
730:
726:
717:
713:
703:
701:
697:
684:
680:
679:
675:
664:
662:
645:"Definition of
643:
642:
638:
628:
626:
603:
602:
598:
593:
575:Password policy
541:
384:
337:public computer
321:
282:
192:computer system
152:
141:
135:
132:
89:
87:
77:
65:
54:
42:
35:
28:
23:
22:
15:
12:
11:
5:
794:
784:
783:
778:
773:
757:
756:
724:
711:
673:
636:
595:
594:
592:
589:
588:
587:
582:
577:
572:
567:
562:
560:Login spoofing
557:
552:
550:Credential lag
547:
540:
537:
498:, and Apple's
473:visitor's book
428:in the 1990s.
410:home computers
383:
380:
379:
378:
375:
370:
367:
362:They include:
324:on this site.
281:
278:
200:authenticating
194:or program by
154:
153:
68:
66:
59:
26:
9:
6:
4:
3:
2:
793:
782:
779:
777:
774:
772:
769:
768:
766:
744:
740:
739:
734:
728:
721:
715:
696:
692:
691:
683:
677:
660:
656:
655:
650:
648:
640:
624:
620:
619:
614:
612:
608:
600:
596:
586:
585:/var/log/wtmp
583:
581:
578:
576:
573:
571:
568:
566:
563:
561:
558:
556:
555:Login session
553:
551:
548:
546:
543:
542:
536:
534:
530:
526:
522:
519:In the past,
517:
515:
511:
506:
505:
501:
497:
493:
489:
485:
481:
476:
474:
470:
465:
463:
459:
455:
451:
450:
444:
442:
438:
434:
429:
427:
423:
419:
415:
411:
406:
404:
400:
392:
388:
376:
374:
371:
368:
365:
364:
363:
360:
359:
355:
353:
349:
344:
342:
338:
333:
330:
325:
319:
314:
312:
308:
304:
299:
296:
290:
286:
277:
275:
271:
267:
263:
258:
257:
253:
251:
247:
243:
239:
235:
234:second factor
231:
228:
224:
220:
217:consist of a
216:
213:
208:
207:
203:
201:
197:
193:
189:
185:
181:
177:
173:
169:
160:
150:
147:
139:
136:February 2024
128:
125:
121:
118:
114:
111:
107:
104:
100:
97: –
96:
92:
91:Find sources:
85:
81:
75:
74:
69:This article
67:
63:
58:
57:
53:
49:
44:
40:
33:
19:
747:. Retrieved
743:the original
736:
727:
719:
714:
702:. Retrieved
695:the original
688:
676:
663:. Retrieved
659:the original
652:
646:
639:
627:. Retrieved
616:
610:
606:
599:
532:
524:
518:
513:
509:
507:
503:
495:
491:
487:
483:
479:
477:
468:
466:
447:
445:
440:
436:
432:
430:
407:
399:time sharing
396:
361:
357:
356:
345:
334:
326:
315:
300:
297:
294:
273:
269:
265:
261:
259:
255:
254:
246:Social login
229:
226:
209:
205:
204:
202:themselves.
183:
179:
175:
171:
165:
142:
133:
123:
116:
109:
102:
90:
78:Please help
73:verification
70:
43:
32:Logone River
500:style guide
441:to clock in
437:(to) log in
352:screensaver
311:web browser
256:Logging Out
215:credentials
210:Typically,
196:identifying
765:Categories
749:28 October
665:8 February
611:logging in
591:References
458:ship's log
418:Windows NT
236:, such as
184:signing on
180:signing in
176:logging on
172:logging in
106:newspapers
738:Microsoft
629:1 January
529:Windows 8
523:reserved
521:Microsoft
431:The term
348:tampering
322:returnto=
280:Procedure
623:Archived
570:Password
539:See also
454:chip log
373:eye scan
274:sign off
270:sign out
223:password
219:username
533:sign-in
525:sign-in
469:sign in
462:logbook
391:IBM AIX
329:cookies
307:command
266:log off
262:log out
120:scholar
95:"Login"
704:17 May
565:OpenID
510:log on
408:Early
221:and a
188:access
122:
115:
108:
101:
93:
698:(PDF)
690:Apple
685:(PDF)
647:login
607:login
514:logon
502:says
496:login
484:logon
480:login
433:login
426:Linux
238:email
230:login
190:to a
182:, or
127:JSTOR
113:books
18:Logon
751:2012
706:2015
667:2014
631:2014
609:and
512:and
488:sign
486:and
424:and
422:OS/2
412:and
303:user
212:user
198:and
174:(or
99:news
467:To
460:or
449:log
318:URL
272:or
242:SMS
240:or
166:In
82:by
767::
735:.
687:.
651:.
621:.
615:.
516:.
492:in
482:,
475:.
464:.
443:.
420:,
276:.
268:,
264:,
178:,
170:,
753:.
708:.
671:.
669:.
649:"
633:.
613:"
490:-
227:a
149:)
143:(
138:)
134:(
124:·
117:·
110:·
103:·
76:.
41:.
34:.
20:)
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.