533:, IBM Watson researchers discovered differential cryptanalytic attacks in 1974 and were asked by the NSA to keep the technique secret. Coppersmith explains IBM's secrecy decision by saying, "that was because can be a very powerful tool, used against many schemes, and there was concern that such information in the public domain could adversely affect national security." Levy quotes Walter Tuchman: "hey asked us to stamp all our documents confidential... We actually put a number on each one and locked them up in safes, because they were considered U.S. government classified. They said do it. So I did it". Bruce Schneier observed that "It took the academic community two decades to figure out that the NSA 'tweaks' actually improved the security of DES."
1244:
2192:—was suggested in 1994 (Kaliski and Robshaw), and was further refined by Biryukov and others. (2004); their analysis suggests that multiple linear approximations could be used to reduce the data requirements of the attack by at least a factor of 4 (that is, 2 instead of 2). A similar reduction in data complexity can be obtained in a chosen-plaintext variant of linear cryptanalysis (Knudsen and Mathiassen, 2000). Junod (2001) performed several experiments to determine the actual time complexity of linear cryptanalysis, and reported that it was somewhat faster than predicted, requiring time equivalent to 2–2 DES evaluations.
38:
1040:
6347:
2115:(FPGAs) of type XILINX Spartan-3 1000 run in parallel. They are grouped in 20 DIMM modules, each containing 6 FPGAs. The use of reconfigurable hardware makes the machine applicable to other code breaking tasks as well. One of the more interesting aspects of COPACOBANA is its cost factor. One machine can be built for approximately $ 10,000. The cost decrease by roughly a factor of 25 over the EFF machine is an example of the continuous improvement of
2890:
1141:
2127:, a spin-off company of the two project partners of COPACOBANA has enhanced and developed successors of COPACOBANA. In 2008 their COPACOBANA RIVYERA reduced the time to break DES to less than one day, using 128 Spartan-3 5000's. SciEngines RIVYERA held the record in brute-force breaking DES, having utilized 128 Spartan-3 5000 FPGAs. Their 256 Spartan-6 LX150 model has further lowered this time.
2055:
1353:
1220:. The Feistel structure ensures that decryption and encryption are very similar processes—the only difference is that the subkeys are applied in the reverse order when decrypting. The rest of the algorithm is identical. This greatly simplifies implementation, particularly in hardware, as there is no need for separate encryption and decryption algorithms.
472:" as evidence of improper interference from the NSA. The suspicion was that the algorithm had been covertly weakened by the intelligence agency so that they—but no one else—could easily read encrypted messages. Alan Konheim (one of the designers of DES) commented, "We sent the S-boxes off to Washington. They came back and were all different." The
529:, a general method for breaking block ciphers. The S-boxes of DES were much more resistant to the attack than if they had been chosen at random, strongly suggesting that IBM knew about the technique in the 1970s. This was indeed the case; in 1994, Don Coppersmith published some of the original design criteria for the S-boxes. According to
2070:
In academia, various proposals for a DES-cracking machine were advanced. In 1977, Diffie and
Hellman proposed a machine costing an estimated US$ 20 million which could find a DES key in a single day. By 1993, Wiener had proposed a key-search machine costing US$ 1 million which would find a key within
2046:
determines the number of possible keys, and hence the feasibility of this approach. For DES, questions were raised about the adequacy of its key size early on, even before it was adopted as a standard, and it was the small key size, rather than theoretical cryptanalysis, which dictated a need for a
503:
In 1973 NBS solicited private industry for a data encryption standard (DES). The first offerings were disappointing, so NSA began working on its own algorithm. Then Howard
Rosenblum, deputy director for research and engineering, discovered that Walter Tuchman of IBM was working on a modification to
2798:
It is easy enough to avoid the weak and semiweak keys in an implementation, either by testing for them explicitly, or simply by choosing keys randomly; the odds of picking a weak or semiweak key by chance are negligible. The keys are not really any weaker than any other keys anyway, as they do not
1231:
scrambles half a block together with some of the key. The output from the F-function is then combined with the other half of the block, and the halves are swapped before the next round. After the final round, the halves are swapped; this is a feature of the
Feistel structure which makes encryption
2875:
Simplified DES (SDES) was designed for educational purposes only, to help students learn about modern cryptanalytic techniques. SDES has similar structure and properties to DES, but has been simplified to make it much easier to perform encryption and decryption by hand with pencil and paper. Some
2134:
announced a system with 48 Xilinx Virtex-6 LX240T FPGAs, each FPGA containing 40 fully pipelined DES cores running at 400 MHz, for a total capacity of 768 gigakeys/sec. The system can exhaustively search the entire 56-bit DES key space in about 26 hours and this service is offered for a fee
2017:
Although more information has been published on the cryptanalysis of DES than any other block cipher, the most practical attack to date is still a brute-force approach. Various minor cryptanalytic properties are known, and three theoretical attacks are possible which, while having a theoretical
603:
The DES can be said to have "jump-started" the nonmilitary study and development of encryption algorithms. In the 1970s there were very few cryptographers, except for those in military or intelligence organizations, and little academic study of cryptography. There are now many active academic
1088:
to customize the transformation, so that decryption can supposedly only be performed by those who know the particular key used to encrypt. The key ostensibly consists of 64 bits; however, only 56 of these are actually used by the algorithm. Eight bits are used solely for checking
512:
NSA worked closely with IBM to strengthen the algorithm against all except brute-force attacks and to strengthen substitution tables, called S-boxes. Conversely, NSA tried to convince IBM to reduce the length of the key from 64 to 48 bits. Ultimately they compromised on a 56-bit
2214:
There have also been attacks proposed against reduced-round versions of the cipher, that is, versions of DES with fewer than 16 rounds. Such analysis gives an insight into how many rounds are needed for safety, and how much of a "security margin" the full version retains.
493:
NSA did not tamper with the design of the algorithm in any way. IBM invented and designed the algorithm, made all pertinent decisions regarding it, and concurred that the agreed upon key size was more than adequate for all commercial applications for which the DES was
612:, "DES did more to galvanize the field of cryptanalysis than anything else. Now there was an algorithm to study." An astonishing share of the open literature in cryptography in the 1970s and 1980s dealt with the DES, and the DES is the standard against which every
312:). However, the NSA also ensured that the key size was drastically reduced so that they could break the cipher by brute force attack. The intense academic scrutiny the algorithm received over time led to the modern understanding of block ciphers and their
2221:
was proposed by
Langford and Hellman in 1994, and combines differential and linear cryptanalysis into a single attack. An enhanced version of the attack can break 9-round DES with 2 chosen plaintexts and has a 2 time complexity (Biham and others, 2002).
1281:
in the diagram, by duplicating half of the bits. The output consists of eight 6-bit (8 × 6 = 48 bits) pieces, each containing a copy of 4 corresponding input bits, plus a copy of the immediately adjacent bit from each of the input pieces to either
2093:
There are many people who will not believe a truth until they can see it with their own eyes. Showing them a physical machine that can crack DES in a few days is the only way to convince some people that they really cannot trust their security to
1396:
check bits. The 56 bits are then divided into two 28-bit halves; each half is thereafter treated separately. In successive rounds, both halves are rotated left by one or two bits (specified for each round), and then 48 subkey bits are selected by
393:
generating key, and was a commercial success. Banks and credit card companies were fearful that Atalla would dominate the market, which spurred the development of an international encryption standard. Atalla was an early competitor to
2188:(Matsui, 1993); the method was implemented (Matsui, 1994), and was the first experimental cryptanalysis of DES to be reported. There is no evidence that DES was tailored to be resistant to this type of attack. A generalization of LC—
498:
Another member of the DES team, Walter
Tuchman, stated "We developed the DES algorithm entirely within IBM using IBMers. The NSA did not dictate a single wire!" In contrast, a declassified NSA book on cryptologic history states:
1405:)—24 bits from the left half, and 24 from the right. The rotations (denoted by "<<<" in the diagram) mean that a different set of bits is used in each subkey; each bit is used in approximately 14 out of the 16 subkeys.
484:
that a reduced key size was sufficient; indirectly assisted in the development of the S-box structures; and certified that the final DES algorithm was, to the best of their knowledge, free from any statistical or mathematical
2322:
405:
On 15 May 1973, after consulting with the NSA, NBS solicited proposals for a cipher that would meet rigorous design criteria. None of the submissions was suitable. A second request was issued on 27 August 1974. This time,
4853:
3707:
S. Kumar, C. Paar, J. Pelzl, G. Pfeiffer, A. Rupp, M. Schimmler, "How to Break DES for Euro 8,980". 2nd
Workshop on Special-purpose Hardware for Attacking Cryptographic Systems—SHARCS 2006, Cologne, Germany, April 3–4,
1408:
The key schedule for decryption is similar—the subkeys are in reverse order compared to encryption. Apart from that change, the process is the same as for encryption. The same 28 bits are passed to all rotation boxes.
2071:
7 hours. However, none of these early proposals were ever implemented—or, at least, no implementations were publicly acknowledged. The vulnerability of DES was practically demonstrated in the late 1990s. In 1997,
3005:
Pub 46–3); it involves applying DES three times with two (2TDES) or three (3TDES) different keys. TDES is regarded as adequately secure, although it is quite slow. A less computationally expensive alternative is
545:
PUB 46, authorized for use on all unclassified data. It was subsequently reaffirmed as the standard in 1983, 1988 (revised as FIPS-46-1), 1993 (FIPS-46-2), and again in 1999 (FIPS-46-3), the latter prescribing
4074:
997:
GPU costing US$ 1000 recovers a key in an average of 15 days (full exhaustive search taking 30 days). Systems have been built with eight GTX 1080 Ti GPUs which can recover a key in an average of under 2 days.
335:). There are also some analytical results which demonstrate theoretical weaknesses in the cipher, although they are infeasible in practice. The algorithm is believed to be practically secure in the form of
2863:
is not a group, nor "close" to being a group. This was an open question for some time, and if it had been the case, it would have been possible to break DES, and multiple encryption modes such as
1213:(IP "undoes" the action of FP, and vice versa). IP and FP have no cryptographic significance, but were included in order to facilitate loading blocks in and out of mid-1970s 8-bit based hardware.
599:
The introduction of DES is considered to have been a catalyst for the academic study of cryptography, particularly of methods to crack block ciphers. According to a NIST retrospective about DES,
2083:, and Justin Dolske, using idle cycles of thousands of computers across the Internet. The feasibility of cracking DES quickly was demonstrated in 1998 when a custom DES-cracker was built by the
3657:
William E. Burr, "Data
Encryption Standard", in NIST's anthology "A Century of Excellence in Measurements, Standards, and Technology: A Chronicle of Selected NBS/NIST Publications, 1901–2000.
2736:
1127:
Decryption uses the same structure as encryption, but with the keys used in reverse order. (This has the advantage that the same hardware or software can be used in both directions.)
2198:: while linear and differential cryptanalysis are general techniques and can be applied to a number of schemes, Davies' attack is a specialized technique for DES, first suggested by
2793:
2557:
476:
reviewed the NSA's actions to determine whether there had been any improper involvement. In the unclassified summary of their findings, published in 1978, the
Committee wrote:
3259:
2352:
266:(NBS) following the agency's invitation to propose a candidate for the protection of sensitive, unclassified electronic government data. In 1976, after consultation with the
963:
of the
Universities of Bochum and Kiel, Germany, breaks DES in 9 days at a $ 10,000 hardware cost. Within a year software improvements reduced the average time to 6.4 days.
2155:. However, the attacks are theoretical and are generally considered infeasible to mount in practice; these types of attack are sometimes termed certificational weaknesses.
2600:
1255:
1254:
1253:
1252:
1251:
1250:
1249:
2837:
1248:
1368:
1366:
1364:
1367:
1365:
1363:
1360:
1359:
1358:
1357:
1043:
2661:
2634:
2405:
1362:
1361:
1048:
608:
companies and consultants. A generation of cryptanalysts has cut its teeth analyzing (that is, trying to "crack") the DES algorithm. In the words of cryptographer
2066:
contained 1,856 custom chips and could brute-force a DES key in a matter of days—the photo shows a DES Cracker circuit board fitted with several Deep Crack chips.
1356:
1247:
2867:
would not increase the security, because repeated encryption (and decryptions) under different keys would be equivalent to encryption under another, single key.
2428:
2379:
2075:
sponsored a series of contests, offering a $ 10,000 prize to the first team that broke a message encrypted with DES for the contest. That contest was won by the
3318:
2857:
2467:
2447:
6327:
6157:
3017:
On
January 2, 1997, NIST announced that they wished to choose a successor to DES. In 2001, after an international competition, NIST selected a new cipher, the
1332:. This is designed so that, after permutation, the bits from the output of each S-box in this round are spread across four different S-boxes in the next round.
4942:
National Bureau of Standards, Data Encryption Standard, FIPS-Pub.46. National Bureau of Standards, U.S. Department of Commerce, Washington D.C., January 1977.
247:
of digital data. Although its short key length of 56 bits makes it too insecure for modern applications, it has been highly influential in the advancement of
1116:
may be utilized for error detection in key generation, distribution, and storage. Bits 8, 16,..., 64 are for use in ensuring that each byte is of odd parity.
473:
452:. Public comments were requested, and in the following year two open workshops were held to discuss the proposed standard. There was criticism received from
4976:
3416:
3216:
2051:. As a result of discussions involving external consultants including the NSA, the key size was reduced from 256 bits to 56 bits to fit on a single chip.
285:
The publication of an NSA-approved encryption standard led to its quick international adoption and widespread academic scrutiny. Controversies arose from
592:
in 1998 that demonstrated that DES could be attacked very practically, and highlighted the need for a replacement algorithm. These and other methods of
3055:
2236:
6385:
4746:
4633:
4627:
4018:
3922:
1314:. Each of the eight S-boxes replaces its six input bits with four output bits according to a non-linear transformation, provided in the form of a
6380:
3589:
3224:
344:
3648:
Bruce Schneier, Applied Cryptography, Protocols, Algorithms, and Source Code in C, Second edition, John Wiley and Sons, New York (1996) p. 267
3098:
1256:
1032:
For brevity, the following description omits the exact transformations and permutations which specify the algorithm. For further details, see
1021:
in 25 seconds. A new rainbow table has to be calculated per plaintext. A limited set of rainbow tables have been made available for download.
941:
6010:
4429:
2876:
people feel that learning SDES gives insight into DES and other block ciphers, and insight into various cryptanalytic attacks against them.
5945:
5026:
3661:
517:
Some of the suspicions about hidden weaknesses in the S-boxes were allayed in 1990, with the independent discovery and open publication by
4765:
4752:
3834:
van Oorschot, Paul C.; Wiener, Michael J. (1991), Damgård, Ivan Bjerre (ed.), "A Known-Plaintext Attack on Two-Key Triple Encryption",
1047:
1046:
1045:
1044:
504:
Lucifer for general use. NSA gave Tuchman a clearance and brought him in to work jointly with the Agency on his Lucifer modification."
3671:
2907:
1158:
3295:
2170:; it was known earlier to both IBM and the NSA and kept secret. To break the full 16 rounds, differential cryptanalysis requires 2
1216:
Before the main rounds, the block is divided into two 32-bit halves and processed alternately; this criss-crossing is known as the
17:
5772:
5128:
3503:
3463:
3002:
2959:
542:
279:
410:
submitted a candidate which was deemed acceptable—a cipher developed during the period 1973–1974 based on an earlier algorithm,
4949:, free online lectures on Chapter 3 of "Understanding Cryptography, A Textbook for Students and Practitioners". Springer, 2009.
4540:
4472:
3014:
was a DES variant proposed as a way to speed up encryption, but it was shown to be susceptible to differential cryptanalysis.
5762:
5256:
4933:
4898:
4722:
3853:
3628:
3608:
1336:
The alternation of substitution from the S-boxes, and permutation of bits from the P-box and E-expansion provides so-called "
4946:
4485:
1384:
for encryption—the algorithm which generates the subkeys. Initially, 56 bits of the key are selected from the initial 64 by
5925:
5899:
5767:
5663:
3229:
551:
2111:. Unlike the EFF machine, COPACOBANA consists of commercially available, reconfigurable integrated circuits. 120 of these
3767:
1318:. The S-boxes provide the core of the security of DES—without them, the cipher would be linear, and trivially breakable.
5740:
4360:
4327:
4294:
4212:
4179:
4054:
3986:
2143:
There are three attacks known that can break the full 16 rounds of DES with less complexity than a brute-force search:
4409:
6390:
6003:
4861:
4810:
4659:
4651:
4386:
4146:
3904:
3322:
3185:
2929:
2218:
1180:
541:
Despite the criticisms, DES was approved as a federal standard in November 1976, and published on 15 January 1977 as
5909:
5019:
3021:(AES), as a replacement. The algorithm which was selected as the AES was submitted by its designers under the name
1124:. FIPS-81 specifies several modes for use with DES. Further comments on the usage of DES are contained in FIPS-74.
5788:
4817:
4129:
Biryukov, Alex; Cannière, Christophe De; Quisquater, Michaël (2004-08-15). "On Multiple Linear Approximations".
1240:
The F-function, depicted in Figure 2, operates on half a block (32 bits) at a time and consists of four stages:
6206:
5966:
4820:
4699:
4092:
Alanazi, Hamdan O.; et al. (2010). "New Comparative Study Between DES, 3DES and AES within Nine Factors".
3427:
3233:
2982:
of DES, and could act as a "drop-in" replacement, although they typically used a 64-bit or 128-bit key. In the
2911:
2669:
2084:
2059:
1162:
1121:
848:
585:
550:" (see below). On 26 May 2002, DES was finally superseded by the Advanced Encryption Standard (AES), following
390:
389:(HSM), the so-called "Atalla Box" which was commercialized in 1973. It protected offline devices with a secure
328:
6395:
4971:
3629:"ISO/IEC 18033-3:2010 Information technology—Security techniques—Encryption algorithms—Part 3: Block ciphers"
2112:
993:
added in DES brute force searching on general purpose GPUs. Benchmarking shows a single off the shelf Nvidia
956:
3593:
2469:
denote plaintext and ciphertext blocks respectively. The complementation property means that the work for a
1193:
The algorithm's overall structure is shown in Figure 1: there are 16 identical stages of processing, termed
6400:
5996:
5056:
3493:"American Cryptology during the Cold War, 1945-1989.Book III: Retrenchment and Reform, 1972-1980, page 232"
3453:"American Cryptology during the Cold War, 1945-1989.Book III: Retrenchment and Reform, 1972-1980, page 232"
3417:"American Cryptology during the Cold War, 1945-1989.Book III: Retrenchment and Reform, 1972-1980, page 232"
3018:
1120:
Like other block ciphers, DES by itself is not a secure means of encryption, but must instead be used in a
901:
367:
340:
308:
that had prompted those suspicions were designed by the NSA to address a vulnerability they secretly knew (
263:
2741:
1292:
using an XOR operation. Sixteen 48-bit subkeys—one for each round—are derived from the main key using the
398:
in the banking market, and was cited as an influence by IBM employees who worked on the DES standard. The
6322:
6277:
6090:
5852:
5012:
350:
Some documents distinguish between the DES standard and its algorithm, referring to the algorithm as the
4790:, "Exhaustive Cryptanalysis of the NBS Data Encryption Standard" IEEE Computer 10(6), June 1977, pp74–84
4310:
Biham, Eli; Dunkelman, Orr; Keller, Nathan (2002-12-01). "Enhancing Differential-Linear Cryptanalysis".
6201:
5869:
5779:
5757:
5070:
3919:
3061:
2504:
2159:
2144:
1033:
975:
960:
793:
779:
526:
309:
271:
3149:
6317:
5874:
5730:
5683:
5158:
4314:. Lecture Notes in Computer Science. Vol. 2501. Springer, Berlin, Heidelberg. pp. 254–266.
4199:. Lecture Notes in Computer Science. Vol. 2259. Springer, Berlin, Heidelberg. pp. 199–211.
4166:. Lecture Notes in Computer Science. Vol. 1978. Springer, Berlin, Heidelberg. pp. 262–272.
3517:
3477:
2979:
2330:
1372:
1081:
1056:
374:
identified a need for a government-wide standard for encrypting unclassified, sensitive information.
124:
4805:, "Cracking DES: Secrets of Encryption Research, Wiretap Politics and Chip Design", 1998, O'Reilly,
4039:. Lecture Notes in Computer Science. Vol. 765. Springer, Berlin, Heidelberg. pp. 386–397.
1304:: after mixing in the subkey, the block is divided into eight 6-bit pieces before processing by the
821:
The first experimental cryptanalysis of DES is performed using linear cryptanalysis (Matsui, 1994).
6307:
6297:
6152:
5940:
5822:
5697:
4881:
4840:
3718:
3499:
3459:
3423:
3129:
2495:
2123:. Adjusting for inflation over 8 years yields an even higher improvement of about 30x. Since 2007,
386:
267:
4541:"Cryptography Research: Devising a Better Way to Teach and Learn the Advanced Encryption Standard"
4426:
4281:. Lecture Notes in Computer Science. Vol. 839. Springer, Berlin, Heidelberg. pp. 17–25.
4133:. Lecture Notes in Computer Science. Vol. 3152. Springer, Berlin, Heidelberg. pp. 1–22.
2562:
6302:
6292:
6095:
6055:
6048:
6038:
6033:
5879:
5668:
5039:
4802:
4162:
Knudsen, Lars R.; Mathiassen, John Erik (2000-04-10). "A Chosen-Plaintext Linear Attack on DES".
3563:
3177:
2900:
2474:
1337:
1261:
1151:
1010:
613:
453:
294:
240:
4916:
Matsui, Mitsuru (1994). "The First Experimental Cryptanalysis of the Data Encryption Standard".
4352:
4345:
3868:
3658:
6375:
6043:
5971:
5847:
5842:
5794:
4960:
4876:
2860:
2809:
1257:
286:
4566:
4459:
3171:
1052:
1051:
1050:
1049:
171:) and are now available on the market as a service. As of 2008, the best analytical attack is
6350:
6196:
6142:
5961:
5784:
5643:
5221:
4621:
4592:
2990:
algorithm was introduced, with a 64-bit block size and a 256-bit key, which was also used in
4846:
Langford, Susan K., Martin E. Hellman: Differential-Linear Cryptanalysis. CRYPTO 1994: 17–25
2997:
DES itself can be adapted and reused in a more secure scheme. Many former DES users now use
792:
Biham and Shamir report the first theoretical attack with less complexity than brute force:
604:
cryptologists, mathematics departments with strong programs in cryptography, and commercial
6312:
6236:
5864:
5747:
5673:
5356:
5336:
4553:
4111:
3746:
2639:
2612:
2383:
2177:
2148:
605:
301:
172:
145:
4529:"Breaking of Simplified Data Encryption Standard Using Binary Particle Swarm Optimization"
4277:
Langford, Susan K.; Hellman, Martin E. (1994-08-21). "Differential-Linear Cryptanalysis".
3668:
2091:). Their motivation was to show that DES was breakable in practice as well as in theory: "
8:
6075:
5827:
5804:
5123:
3820:
3038:
2803:
885:
DES is reaffirmed for the fourth time as FIPS 46-3, which specifies the preferred use of
4967:
COPACOBANA, a $ 10,000 DES cracker based on FPGAs by the Universities of Bochum and Kiel
4115:
2410:
2361:
2099:
The next confirmed DES cracker was the COPACOBANA machine built in 2006 by teams of the
584:
Another theoretical attack, linear cryptanalysis, was published in 1994, but it was the
37:
6181:
6165:
6112:
5812:
5720:
5432:
5361:
5331:
5276:
4904:
4740:
4728:
4609:
4259:
4101:
4012:
4000:
3520:
FOIA request. This version is differently redacted than the version on the NSA website.
3480:
FOIA request. This version is differently redacted than the version on the NSA website.
3287:
3121:
2842:
2470:
2452:
2432:
2355:
2104:
2039:
1085:
382:
275:
164:
3492:
3452:
2087:(EFF), a cyberspace civil rights group, at the cost of approximately US$ 250,000 (see
6241:
6231:
6102:
5532:
5231:
5191:
5186:
5153:
5113:
5061:
4929:
4894:
4857:
4806:
4718:
4695:
4655:
4647:
4646:, Differential Cryptanalysis of the Data Encryption Standard, Springer Verlag, 1993.
4613:
4382:
4356:
4323:
4290:
4251:
4208:
4175:
4142:
4050:
3992:
3982:
3900:
3849:
3279:
3181:
3066:
2955:
2950:
designs, which started to appear in the late 1980s and early 1990s: examples include
2152:
2131:
994:
371:
320:
4908:
4732:
4075:"Investigation of a potential weakness in the DES algorithm, Private communications"
2482:
163:
DES has been considered unsecure right from the start because of the feasibility of
6176:
5904:
5799:
5678:
5537:
5417:
5386:
5080:
4921:
4886:
4783:
4710:
4601:
4511:
4315:
4282:
4263:
4241:
4200:
4167:
4134:
4040:
4004:
3974:
3839:
3838:, vol. 473, Berlin, Heidelberg: Springer Berlin Heidelberg, pp. 318–325,
3397:
3291:
3271:
3125:
3113:
3034:
2171:
2116:
2096:" The machine brute-forced a key in a little more than 2 days' worth of searching.
2076:
2023:
1306:
1210:
926:
The withdrawal of FIPS 46-3 (and a couple of related standards) is proposed in the
833:
797:
726:
469:
461:
448:
435:
415:
195:
76:
4528:
4473:"Cryptanalysis of Simplified Data Encryption Standard via Optimisation Heuristics"
3894:
3687:
3010:, which increases the key size by XORing extra key material before and after DES.
5751:
5735:
5724:
5658:
5617:
5582:
5512:
5492:
5366:
5246:
5241:
5196:
4854:
Crypto: How the Code Rebels Beat the Government—Saving Privacy in the Digital Age
4836:
4769:
4761:
4758:
Campbell, Keith W., Michael J. Wiener: DES is not a Group. CRYPTO 1992: pp512–520
4498:
4446:
4433:
3926:
3675:
3665:
3026:
2317:{\displaystyle E_{K}(P)=C\iff E_{\overline {K}}({\overline {P}})={\overline {C}}}
2207:
2185:
2124:
2100:
2088:
2063:
2019:
871:
852:
589:
423:
418:
cipher. The team at IBM involved in cipher design and analysis included Feistel,
339:, although there are theoretical attacks. This cipher has been superseded by the
324:
176:
168:
138:
4987:
RFC4772 : Security Implications of Using the Data Encryption Standard (DES)
4138:
3426:, DOCID 3417193 (file released on 2009-12-18, hosted at nsa.gov). Archived from
6251:
6171:
6132:
6080:
6065:
5889:
5837:
5648:
5633:
5572:
5567:
5452:
5201:
4991:
4868:
4787:
4696:
Cracking DES: Secrets of Encryption Research, Wiretap Politics, and Chip Design
2181:
2120:
1341:
1324:: finally, the 32 outputs from the S-boxes are rearranged according to a fixed
1217:
1076:
bits and transforms it through a series of complicated operations into another
730:
609:
457:
419:
378:
4795:
4672:: An Improvement of Davies' Attack on DES. J. Cryptology 10(3): 195–206 (1997)
4515:
3978:
3968:
3401:
3275:
3205:. ACM Press/Addison-Wesley Publishing Co. New York, NY, USA. pp. 275–280.
402:
later adopted a similar PIN verification system to the earlier Atalla system.
6369:
6332:
6287:
6246:
6226:
6122:
6085:
6060:
5884:
5832:
5711:
5693:
5482:
5457:
5447:
5271:
5261:
5108:
4704:
4679:
4669:
4554:"Announcing Development of FIPS for Advanced Encryption Standard | CSRC"
4319:
4255:
4204:
4171:
4045:
3844:
3771:
3283:
2987:
2203:
2199:
1014:
593:
431:
411:
313:
259:
156:
4986:
4925:
4705:
Biryukov, A, C. De Canniere and M. Quisquater (2004). Franklin, Matt (ed.).
4402:
4286:
4035:
Matsui, Mitsuru (1993-05-23). "Linear Cryptanalysis Method for DES Cipher".
3996:
3117:
2018:
complexity less than a brute-force attack, require an unrealistic number of
767:
DES is reaffirmed for the second time as FIPS 46-1, superseding FIPS PUB 46
6282:
6127:
6117:
6107:
6070:
6019:
5817:
5638:
5602:
5467:
5346:
5301:
5133:
5085:
5035:
4830:
4826:
4376:
3596:
Recommendation for the Triple Data Encryption Algorithm (TDEA) Block Cipher
2983:
2947:
2072:
1315:
1294:
1065:
978:, the RIVYERA machine, reduced the average time to less than a single day.
297:
248:
102:
4890:
4833:: Linear Cryptanalysis Using Multiple Approximations. CRYPTO 1994: pp26–39
4246:
4229:
3201:
Walter Tuchman (1997). "A brief history of the data encryption standard".
270:(NSA), the NBS selected a slightly modified version (strengthened against
6261:
5427:
5422:
5306:
4992:
Python code of DES Cipher implemented using DES Chapter from NIST SP 958
4849:
2080:
1344:
in the 1940s as a necessary condition for a secure yet practical cipher.
1325:
1198:
1104:, each with odd parity. According to ANSI X3.92-1981 (Now, known as ANSI
753:
530:
331:
collaborated to publicly break a DES key in 22 hours and 15 minutes (see
4981:
3388:
P. Kinnucan (October 1978). "Data Encryption Gurus: Tuchman and Meyer".
6221:
6191:
6186:
6147:
5859:
5577:
5517:
5401:
5396:
5341:
5211:
5074:
4972:
DES step-by-step presentation and reliable message encoding application
4966:
4643:
4605:
4587:
4510:
Edward F. Schaefer. "A Simplified Data Encryption Standard Algorithm".
3260:"Automated teller machines: their history and authentication protocols"
3217:"The Economic Impacts of NIST's Data Encryption Standard (DES) Program"
3071:
3001:(TDES) which was described and analysed by one of DES's patentees (see
2998:
2914: in this section. Unsourced material may be challenged and removed.
2864:
2167:
2043:
1417:
1393:
1165: in this section. Unsourced material may be challenged and removed.
1094:
1090:
1077:
886:
867:
756:
II, a TV satellite scrambling system based upon DES, begins use by HBO
559:
547:
522:
465:
336:
290:
244:
86:
4875:. Lecture Notes in Computer Science. Vol. 765. pp. 386–397.
4343:
Menezes, Alfred J.; van Oorschot, Paul C.; Vanstone, Scott A. (1996).
2477:
assumption. By definition, this property also applies to TDES cipher.
6211:
5592:
5587:
5477:
5391:
5286:
5266:
4689:
4683:
4675:
4665:
4639:
4583:
2163:
2048:
1073:
1069:
518:
427:
4709:. Lecture Notes in Computer Science. Vol. 3152. pp. 1–22.
4427:"Image Encryption using Simplified Data Encryption Standard (S-DES)"
4195:
Junod, Pascal (2001-08-16). "On the Complexity of Matsui's Attack".
3869:"Getting Started, COPACOBANA — Cost-optimized Parallel Code-Breaker"
2942:
Concerns about security and the relatively slow operation of DES in
2889:
1140:
6256:
6216:
5930:
5894:
5688:
5351:
5226:
5206:
5118:
4920:. Lecture Notes in Computer Science. Vol. 839. pp. 1–11.
4793:
Ehrsam and others., Product Block Cipher System for Data Security,
4766:
The data encryption standard (DES) and its strength against attacks
4714:
3022:
2943:
399:
300:
design, and the involvement of the NSA, raising suspicions about a
114:
4106:
2210:, has a computational complexity of 2, and has a 51% success rate.
836:
breaks a message encrypted with DES for the first time in public.
645:
NBS publishes a first request for a standard encryption algorithm
5597:
5547:
5507:
5497:
5442:
5437:
5281:
5090:
4839:, John Erik Mathiassen: A Chosen-Plaintext Linear Attack on DES.
3042:
2108:
4590:(1991). "Differential Cryptanalysis of DES-like Cryptosystems".
6137:
5935:
5557:
5552:
5487:
5472:
5462:
5407:
5381:
5376:
5371:
5251:
5236:
3612:
3373:
Robert Sugarman, ed. (July 1979). "On foiling computer crime".
2991:
2963:
2035:
1105:
1017:
can recover the DES key for a single specific chosen plaintext
990:
574:
570:
98:
4682:, Nathan Keller: Enhancing Differential-Linear Cryptanalysis.
3768:"FIPS 74 - Guidelines for Implementing and Using the NBS Data"
3099:"Exhaustive Cryptanalysis of the NBS Data Encryption Standard"
210:
204:
5653:
5612:
5562:
5542:
5527:
5316:
5296:
5216:
5181:
3007:
2971:
2967:
305:
94:
90:
4961:
FIPS 46-3: The official document describing the DES standard
4501:. Section 3.4: The Simplified Version of DES (S-DES). p. 96.
3973:. Shamir, Adi. New York: Springer-Verlag. pp. 487–496.
2473:
could be reduced by a factor of 2 (or a single bit) under a
1428:// Pre-processing: padding with the size difference in bytes
562:
through the year 2030 for sensitive government information.
5502:
5411:
5326:
5321:
5311:
5291:
5163:
5148:
4567:
http://csrc.nist.gov/publications/fips/fips197/fips-197.pdf
4342:
3011:
2975:
2054:
1392:)—the remaining eight bits are either discarded or used as
1101:
693:
Second workshop, discussing mathematical foundation of DES
578:
577:
92), NIST SP 800-67 and ISO/IEC 18033-3 (as a component of
566:
555:
228:
216:
4582:
4527:
Lavkush Sharma; Bhupendra Kumar Pathak; and Nidhi Sharma.
4449:. 2012. Section "8.8 Simplified DES: sDES". p. 183 to 190.
4128:
3970:
Differential cryptanalysis of the data encryption standard
3808:
Cryptography and network security: principles and practice
2946:
motivated researchers to propose a variety of alternative
554:. On 19 May 2005, FIPS 46-3 was officially withdrawn, but
5607:
5522:
5143:
5138:
3966:
3030:
2951:
1273:: the 32-bit half-block is expanded to 48 bits using the
1224:
656:
NBS publishes a second request for encryption algorithms
481:
407:
395:
255:
58:
4447:"Introduction to Cryptography with Open-Source Software"
2206:(1997). The most powerful form of the attack requires 2
733:
argue that the DES cipher can be broken by brute force.
446:
On 17 March 1975, the proposed DES was published in the
2230:
DES exhibits the complementation property, namely that
167:. Such attacks have been demonstrated in practice (see
6158:
Cryptographically secure pseudorandom number generator
1080:
bitstring of the same length. In the case of DES, the
68:
1975 (Federal Register) (standardized in January 1977)
4947:"The Data Encryption Standard (DES) and Alternatives"
3617:
American National Standard, Data Encryption Algorithm
3173:
Cash and Dash: How ATMs and Computers Changed Banking
2845:
2812:
2744:
2672:
2642:
2636:, operates identically to decryption with the other,
2615:
2565:
2507:
2455:
2435:
2413:
2386:
2364:
2333:
2239:
1674:// To decrypt a message reverse the order of the keys
474:
United States Senate Select Committee on Intelligence
231:
219:
207:
198:
5034:
4996:
4309:
2609:. Encryption with one of the pair of semiweak keys,
1093:, and are thereafter discarded. Hence the effective
889:, with single DES permitted only in legacy systems.
782:, and apply it to a 15-round DES-like cryptosystem.
596:
are discussed in more detail later in this article.
225:
201:
3732:
3097:Diffie, Whitfield; Hellman, Martin E. (June 1977).
343:(AES). DES has been withdrawn as a standard by the
213:
4344:
3938:
3833:
3203:Internet besieged: countering cyberspace scofflaws
3056:Brute Force: Cracking the Data Encryption Standard
2851:
2831:
2787:
2730:
2655:
2628:
2594:
2551:
2461:
2441:
2422:
2399:
2373:
2346:
2316:
2138:
811:DES is reaffirmed for the third time as FIPS 46-2
441:
4977:A Fast New DES Implementation in Software - Biham
4161:
3733:"Crack.sh | the World's Fastest DES Cracker"
3490:
3450:
3414:
2225:
2026:to carry out, and are not a concern in practice.
6367:
3555:
3357:
1100:The key is nominally stored or transmitted as 8
715:DES is published as a FIPS standard FIPS PUB 46
4915:
4867:
4276:
3701:
3372:
1355:
1246:
1042:
3892:
3800:
3590:National Institute of Standards and Technology
3225:National Institute of Standards and Technology
3200:
536:
345:National Institute of Standards and Technology
6004:
5020:
4227:
3096:
2494:) under a weak key have the same effect (see
2012:
179:and has a time complexity of 2 (Junod, 2001).
27:Early unclassified symmetric-key block cipher
4745:: CS1 maint: multiple names: authors list (
4626:: CS1 maint: multiple names: authors list (
4017:: CS1 maint: multiple names: authors list (
3316:
2826:
2813:
874:break a DES key in 22 hours and 15 minutes.
319:DES is insecure due to the relatively short
4692:: A Fast New DES Implementation in Software
3585:
3583:
3387:
2202:in the eighties, and improved by Biham and
1235:
989:The Open Source password cracking software
855:(Deep Crack) breaks a DES key in 56 hours.
6011:
5997:
5027:
5013:
3169:
3150:"The Legacy of DES - Schneier on Security"
2269:
2265:
4880:
4245:
4230:"An improvement of Davies' attack on DES"
4228:Biham, Eli; Biryukov, Alex (1997-06-01).
4105:
4044:
3843:
2930:Learn how and when to remove this message
2879:
2731:{\displaystyle E_{K_{1}}(E_{K_{2}}(P))=P}
2174:. DES was designed to be resistant to DC.
1265:—The Feistel function (F-function) of DES
1181:Learn how and when to remove this message
480:In the development of DES, NSA convinced
426:, Alan Konheim, Carl Meyer, Mike Matyas,
6386:1977 establishments in the United States
3580:
3561:
3408:
3092:
3090:
3088:
3086:
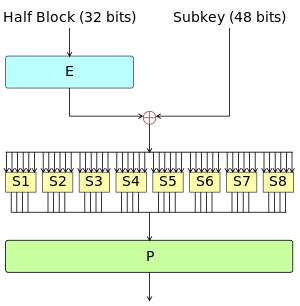
2978:. Most of these designs kept the 64-bit
2053:
2042:—trying every possible key in turn. The
1351:
1340:" respectively, a concept identified by
1242:
1038:
796:. However, it requires an unrealistic 2
366:The origins of DES date to 1972, when a
44:The Feistel function (F function) of DES
4818:"On the Complexity of Matsui's Attack."
4774:IBM Journal of Research and Development
4312:Advances in Cryptology — ASIACRYPT 2002
4091:
3954:David Hulton, Ian Foster, BSidesLV 2017
3952:Think Complex Passwords Will Save You?,
3544:
3542:
3257:
280:Federal Information Processing Standard
14:
6381:Computer-related introductions in 1977
6368:
4873:Advances in Cryptology — EUROCRYPT '93
4072:
4037:Advances in Cryptology — EUROCRYPT '93
4034:
3836:Advances in Cryptology – EUROCRYPT ’90
3360:Security for computer networks, 2nd ed
3251:
3165:
3163:
2162:was rediscovered in the late 1980s by
1060:— The overall Feistel structure of DES
282:(FIPS) for the United States in 1977.
278:), which was published as an official
5992:
5008:
4194:
4068:
4066:
4030:
4028:
3962:
3960:
3611:, ANSI X3.92-1981 (now known as ANSI
3609:American National Standards Institute
3564:"Saluting the data encryption legacy"
3083:
2802:DES has also been proved not to be a
2038:, the most basic method of attack is
2029:
1425:// All variables are unsigned 64 bits
1197:. There is also an initial and final
743:DES is reaffirmed for the first time
262:, the algorithm was submitted to the
4707:Advances in Cryptology – CRYPTO 2004
4381:. 16 August 1992. pp. 512–520.
4131:Advances in Cryptology – CRYPTO 2004
3791:
3539:
3342:
3264:Journal of Cryptographic Engineering
3230:United States Department of Commerce
3144:
3142:
2912:adding citations to reliable sources
2883:
2788:{\displaystyle E_{K_{2}}=D_{K_{1}}.}
1163:adding citations to reliable sources
1134:
1130:
1072:that takes a fixed-length string of
289:design elements, a relatively short
4918:Advances in Cryptology – CRYPTO '94
4499:"Cryptography and Network Security"
4279:Advances in Cryptology — CRYPTO '94
3920:Break DES in less than a single day
3893:Reinhard Wobst (October 16, 2007).
3530:
3209:
3160:
565:The algorithm is also specified in
24:
4425:Sanjay Kumar; Sandeep Srivastava.
4063:
4025:
3967:Biham, E. & Shamir, A (1993).
3957:
3747:"FIPS 81 - Des Modes of Operation"
3533:Computer Security and Cryptography
1866:// Substitution (48bits to 32bits)
1232:and decryption similar processes.
1112:One bit in each 8-bit byte of the
942:Federal Register vol 70, number 96
258:and based on an earlier design by
36:
25:
6412:
4982:On Multiple Linear Approximations
4954:
3939:"The World's fastest DES cracker"
3358:Davies, D.W.; W.L. Price (1989).
3258:Konheim, Alan G. (1 April 2016).
3139:
2870:
2552:{\displaystyle E_{K}(E_{K}(P))=P}
2219:Differential-linear cryptanalysis
6346:
6345:
6018:
4415:from the original on 2011-04-09.
4347:Handbook of Applied Cryptography
3594:NIST Special Publication 800-67
3491:Thomas R. Johnson (2009-12-18).
3451:Thomas R. Johnson (2009-12-18).
3415:Thomas R. Johnson (2009-12-18).
2888:
1288:: the result is combined with a
1139:
254:Developed in the early 1970s at
194:
4772: (archived June 15, 2007).
4560:
4546:
4534:
4521:
4504:
4491:
4478:
4465:
4452:
4439:
4419:
4395:
4369:
4336:
4303:
4270:
4221:
4188:
4155:
4122:
4085:
3945:
3931:
3913:
3886:
3861:
3827:
3813:
3785:
3760:
3739:
3725:
3711:
3680:
3651:
3642:
3621:
3602:
3524:
3509:from the original on 2015-04-25
3484:
3469:from the original on 2015-04-25
3444:
3381:
3366:
2899:needs additional citations for
2347:{\displaystyle {\overline {x}}}
2139:Attacks faster than brute force
1420:for the DES algorithm follows.
1347:
1150:needs additional citations for
442:NSA's involvement in the design
377:Around the same time, engineer
332:
6207:Information-theoretic security
4871:(1994). Helleseth, Tor (ed.).
4821:Selected Areas in Cryptography
4700:Electronic Frontier Foundation
4197:Selected Areas in Cryptography
3770:. Itl.nist.gov. Archived from
3562:Schneier, Bruce (2004-09-27).
3351:
3336:
3310:
3232:. October 2001. Archived from
3194:
3025:. Other finalists in the NIST
2799:give an attack any advantage.
2719:
2716:
2710:
2690:
2540:
2537:
2531:
2518:
2298:
2285:
2266:
2256:
2250:
2226:Minor cryptanalytic properties
2113:field-programmable gate arrays
2085:Electronic Frontier Foundation
1027:
940:NIST withdraws FIPS 46-3 (see
704:DES is approved as a standard
586:Electronic Frontier Foundation
329:Electronic Frontier Foundation
13:
1:
4575:
4471:Nalini N; G Raghavendra Rao.
3170:Bátiz-Lazo, Bernardo (2018).
2806:, or more precisely, the set
2190:multiple linear cryptanalysis
1467:// The keys given by the user
1412:
620:
434:, Bill Notz, Lynn Smith, and
4460:"Appendix G: Simplified DES"
3810:. Prentice Hall, 2006. p. 73
3796:(1st ed.). p. 271.
3347:(2nd ed.). p. 280.
3019:Advanced Encryption Standard
2605:There are also six pairs of
2595:{\displaystyle E_{K}=D_{K}.}
2480:DES also has four so-called
2407:denotes encryption with key
2339:
2309:
2293:
2279:
1491:// PC1 (64 bits to 56 bits)
1084:is 64 bits. DES also uses a
902:Advanced Encryption Standard
778:Biham and Shamir rediscover
569:X3.92 (Today X3 is known as
489:However, it also found that
368:National Bureau of Standards
341:Advanced Encryption Standard
264:National Bureau of Standards
7:
6323:Message authentication code
6278:Cryptographic hash function
6091:Cryptographic hash function
4139:10.1007/978-3-540-28628-8_1
3048:
537:The algorithm as a standard
10:
6417:
6202:Harvest now, decrypt later
4945:Christof Paar, Jan Pelzl,
3180:. pp. 284 & 311.
3062:DES supplementary material
2160:Differential cryptanalysis
2145:differential cryptanalysis
2130:In 2012, David Hulton and
2013:Security and cryptanalysis
1034:DES supplementary material
1031:
915:The AES becomes effective
794:differential cryptanalysis
780:differential cryptanalysis
527:differential cryptanalysis
361:
310:differential cryptanalysis
272:differential cryptanalysis
6341:
6318:Post-quantum cryptography
6270:
6026:
5988:
5954:
5918:
5910:Time/memory/data tradeoff
5707:
5626:
5172:
5099:
5047:
5004:
5000:
4799:, Filed February 24, 1975
4516:10.1080/0161-119691884799
4378:Campbell and Wiener, 1992
3979:10.1007/978-1-4613-9314-6
3899:. John Wiley & Sons.
3518:National Security Archive
3478:National Security Archive
3402:10.1080/0161-117891853270
3276:10.1007/s13389-015-0104-3
2832:{\displaystyle \{E_{K}\}}
1641:// PC2 (56bits to 48bits)
1380:Figure 3 illustrates the
1376:— The key-schedule of DES
1223:The ⊕ symbol denotes the
904:is published in FIPS 197
356:Data Encryption Algorithm
162:
154:
144:
133:
123:
113:
108:
82:
72:
64:
54:
49:
35:
6391:Data Encryption Standard
6308:Quantum key distribution
6298:Authenticated encryption
6153:Random number generation
5698:Whitening transformation
4841:Fast Software Encryption
4320:10.1007/3-540-36178-2_16
4205:10.1007/3-540-45537-X_16
4172:10.1007/3-540-44706-7_18
4164:Fast Software Encryption
4046:10.1007/3-540-48285-7_33
3845:10.1007/3-540-46877-3_29
3690:. Edocket.access.gpo.gov
3500:National Security Agency
3460:National Security Agency
3424:National Security Agency
3362:. John Wiley & Sons.
3077:
1944:// Concat right and left
1422:
1236:The Feistel (F) function
959:-based parallel machine
667:DES is published in the
616:since has been compared.
387:hardware security module
385:and developed the first
268:National Security Agency
187:Data Encryption Standard
31:Data Encryption Standard
18:Data encryption standard
6303:Public-key cryptography
6293:Symmetric-key algorithm
6096:Key derivation function
6056:Cryptographic primitive
6049:Authentication protocol
6039:Outline of cryptography
6034:History of cryptography
5669:Confusion and diffusion
4926:10.1007/3-540-48658-5_1
4287:10.1007/3-540-48658-5_3
3178:Oxford University Press
3118:10.1109/C-M.1977.217750
2839:(for all possible keys
2196:Improved Davies' attack
2079:, led by Rocke Verser,
1824:// E (32bits to 48bits)
1338:confusion and diffusion
1108:92–1981), section 3.5:
1011:chosen-plaintext attack
614:symmetric key algorithm
573:and ANSI X3.92 as ANSI
454:public-key cryptography
370:study of US government
274:, but weakened against
241:symmetric-key algorithm
6044:Cryptographic protocol
4079:Private Communications
4073:Davies, D. W. (1987).
3319:"Has DES been broken?"
2880:Replacement algorithms
2861:functional composition
2853:
2833:
2789:
2732:
2657:
2630:
2596:
2553:
2463:
2443:
2424:
2401:
2375:
2348:
2318:
2101:Universities of Bochum
2067:
1377:
1266:
1118:
1064:DES is the archetypal
1061:
682:First workshop on DES
515:
506:
496:
487:
41:
6197:End-to-end encryption
6143:Cryptojacking malware
5962:Initialization vector
4891:10.1007/3-540-48285-7
4843:- FSE 2000: pp262–272
4796:U.S. patent 3,962,539
4593:Journal of Cryptology
4351:. CRC Press. p.
4247:10.1007/s001459900027
4234:Journal of Cryptology
3631:. Iso.org. 2010-12-14
2854:
2834:
2790:
2733:
2658:
2656:{\displaystyle K_{2}}
2631:
2629:{\displaystyle K_{1}}
2597:
2554:
2464:
2444:
2425:
2402:
2400:{\displaystyle E_{K}}
2376:
2349:
2319:
2057:
1698:// Encrypt or Decrypt
1370:
1275:expansion permutation
1259:
1227:(XOR) operation. The
1110:
1054:
510:
501:
491:
478:
464:, citing a shortened
40:
6396:Broken block ciphers
6313:Quantum cryptography
6237:Trusted timestamping
5741:3-subset MITM attack
5357:Intel Cascade Cipher
5337:Hasty Pudding cipher
4094:Journal of Computing
3794:Applied Cryptography
3345:Applied Cryptography
2908:improve this article
2843:
2810:
2742:
2670:
2640:
2613:
2563:
2505:
2453:
2433:
2411:
2384:
2362:
2331:
2237:
2178:Linear cryptanalysis
2149:linear cryptanalysis
2064:DES cracking machine
1159:improve this article
606:information security
552:a public competition
468:and the mysterious "
173:linear cryptanalysis
6401:American inventions
6076:Cryptographic nonce
5780:Differential-linear
4458:William Stallings.
4445:Alasdair McAndrew.
4116:2010arXiv1003.4085A
3896:Cryptology Unlocked
3874:. December 12, 2006
995:GeForce GTX 1080 Ti
323:. In January 1999,
276:brute-force attacks
175:, which requires 2
165:brute-force attacks
32:
6182:Subliminal channel
6166:Pseudorandom noise
6113:Key (cryptography)
5853:Differential-fault
5071:internal mechanics
4827:Kaliski, Burton S.
4823:, 2001, pp199–211.
4606:10.1007/BF00630563
4569:November 26, 2001.
4556:. 10 January 2017.
4432:2015-12-22 at the
3925:2017-08-28 at the
3674:2006-08-23 at the
3664:2009-06-19 at the
3317:RSA Laboratories.
3156:. October 6, 2004.
2849:
2829:
2785:
2728:
2653:
2626:
2592:
2549:
2490:) and decryption (
2471:brute-force attack
2459:
2439:
2423:{\displaystyle K.}
2420:
2397:
2374:{\displaystyle x.}
2371:
2356:bitwise complement
2344:
2314:
2180:was discovered by
2068:
2030:Brute-force attack
1378:
1312:substitution boxes
1298:(described below).
1267:
1062:
383:Atalla Corporation
42:
30:
6363:
6362:
6359:
6358:
6242:Key-based routing
6232:Trapdoor function
6103:Digital signature
5984:
5983:
5980:
5979:
5967:Mode of operation
5644:Lai–Massey scheme
4935:978-3-540-58333-2
4900:978-3-540-57600-6
4784:Diffie, Whitfield
4724:978-3-540-22668-0
4497:Dr. Manoj Kumar.
4484:Minh Van Nguyen.
3855:978-3-540-53587-4
3688:"FR Doc 04-16894"
3239:on 30 August 2017
3067:Skipjack (cipher)
2940:
2939:
2932:
2852:{\displaystyle K}
2738:or equivalently,
2559:or equivalently,
2462:{\displaystyle C}
2442:{\displaystyle P}
2342:
2312:
2296:
2282:
2172:chosen plaintexts
2132:Moxie Marlinspike
2044:length of the key
2024:chosen plaintexts
1399:Permuted Choice 2
1386:Permuted Choice 1
1191:
1190:
1183:
1131:Overall structure
1122:mode of operation
1025:
1024:
974:The successor of
798:chosen plaintexts
372:computer security
333:§ Chronology
183:
182:
16:(Redirected from
6408:
6349:
6348:
6177:Insecure channel
6013:
6006:
5999:
5990:
5989:
5838:Power-monitoring
5679:Avalanche effect
5387:Khufu and Khafre
5040:security summary
5029:
5022:
5015:
5006:
5005:
5002:
5001:
4998:
4997:
4939:
4912:
4884:
4798:
4762:Coppersmith, Don
4750:
4744:
4736:
4631:
4625:
4617:
4570:
4564:
4558:
4557:
4550:
4544:
4538:
4532:
4525:
4519:
4508:
4502:
4495:
4489:
4486:"Simplified DES"
4482:
4476:
4469:
4463:
4456:
4450:
4443:
4437:
4423:
4417:
4416:
4414:
4407:
4399:
4393:
4392:
4373:
4367:
4366:
4350:
4340:
4334:
4333:
4307:
4301:
4300:
4274:
4268:
4267:
4249:
4225:
4219:
4218:
4192:
4186:
4185:
4159:
4153:
4152:
4126:
4120:
4119:
4109:
4089:
4083:
4082:
4070:
4061:
4060:
4048:
4032:
4023:
4022:
4016:
4008:
3964:
3955:
3949:
3943:
3942:
3935:
3929:
3917:
3911:
3910:
3890:
3884:
3883:
3881:
3879:
3873:
3865:
3859:
3858:
3847:
3831:
3825:
3824:
3817:
3811:
3804:
3798:
3797:
3789:
3783:
3782:
3780:
3779:
3764:
3758:
3757:
3755:
3754:
3743:
3737:
3736:
3729:
3723:
3722:
3715:
3709:
3705:
3699:
3698:
3696:
3695:
3684:
3678:
3655:
3649:
3646:
3640:
3639:
3637:
3636:
3625:
3619:
3606:
3600:
3587:
3578:
3577:
3575:
3574:
3559:
3553:
3546:
3537:
3536:
3528:
3522:
3521:
3515:
3514:
3508:
3497:
3488:
3482:
3481:
3475:
3474:
3468:
3457:
3448:
3442:
3441:
3439:
3438:
3432:
3421:
3412:
3406:
3405:
3385:
3379:
3378:
3370:
3364:
3363:
3355:
3349:
3348:
3340:
3334:
3333:
3331:
3330:
3321:. Archived from
3314:
3308:
3307:
3305:
3303:
3294:. Archived from
3255:
3249:
3248:
3246:
3244:
3238:
3221:
3213:
3207:
3206:
3198:
3192:
3191:
3167:
3158:
3157:
3154:www.schneier.com
3146:
3137:
3136:
3134:
3128:. Archived from
3103:
3094:
2935:
2928:
2924:
2921:
2915:
2892:
2884:
2858:
2856:
2855:
2850:
2838:
2836:
2835:
2830:
2825:
2824:
2794:
2792:
2791:
2786:
2781:
2780:
2779:
2778:
2761:
2760:
2759:
2758:
2737:
2735:
2734:
2729:
2709:
2708:
2707:
2706:
2689:
2688:
2687:
2686:
2662:
2660:
2659:
2654:
2652:
2651:
2635:
2633:
2632:
2627:
2625:
2624:
2601:
2599:
2598:
2593:
2588:
2587:
2575:
2574:
2558:
2556:
2555:
2550:
2530:
2529:
2517:
2516:
2475:chosen-plaintext
2468:
2466:
2465:
2460:
2448:
2446:
2445:
2440:
2429:
2427:
2426:
2421:
2406:
2404:
2403:
2398:
2396:
2395:
2380:
2378:
2377:
2372:
2353:
2351:
2350:
2345:
2343:
2335:
2323:
2321:
2320:
2315:
2313:
2305:
2297:
2289:
2284:
2283:
2275:
2249:
2248:
2208:known plaintexts
2186:known plaintexts
2117:digital hardware
2077:DESCHALL Project
2008:
2005:
2002:
1999:
1996:
1993:
1990:
1987:
1984:
1981:
1978:
1975:
1972:
1969:
1966:
1963:
1960:
1957:
1954:
1951:
1948:
1945:
1942:
1939:
1936:
1933:
1930:
1927:
1924:
1921:
1918:
1915:
1912:
1909:
1906:
1903:
1900:
1897:
1894:
1891:
1888:
1885:
1882:
1879:
1876:
1873:
1870:
1867:
1864:
1861:
1858:
1855:
1852:
1849:
1846:
1843:
1840:
1837:
1834:
1831:
1828:
1825:
1822:
1819:
1816:
1813:
1810:
1807:
1804:
1801:
1798:
1795:
1792:
1789:
1786:
1783:
1780:
1777:
1774:
1771:
1768:
1765:
1762:
1759:
1756:
1753:
1750:
1747:
1744:
1741:
1738:
1735:
1732:
1729:
1726:
1723:
1720:
1717:
1714:
1711:
1708:
1705:
1702:
1699:
1696:
1693:
1690:
1687:
1684:
1681:
1678:
1675:
1672:
1669:
1666:
1663:
1660:
1657:
1654:
1651:
1648:
1645:
1642:
1639:
1636:
1633:
1630:
1627:
1624:
1621:
1618:
1615:
1612:
1609:
1606:
1603:
1600:
1597:
1594:
1591:
1588:
1585:
1582:
1579:
1576:
1573:
1570:
1567:
1564:
1561:
1558:
1555:
1552:
1549:
1546:
1543:
1540:
1537:
1534:
1531:
1528:
1525:
1522:
1519:
1516:
1513:
1510:
1507:
1504:
1501:
1498:
1495:
1492:
1489:
1488:// Generate Keys
1486:
1483:
1480:
1477:
1474:
1471:
1468:
1465:
1462:
1459:
1456:
1453:
1450:
1447:
1444:
1441:
1438:
1435:
1432:
1429:
1426:
1354:
1245:
1186:
1179:
1175:
1172:
1166:
1143:
1135:
1041:
1019:1122334455667788
928:Federal Register
834:DESCHALL Project
669:Federal Register
625:
624:
462:Whitfield Diffie
449:Federal Register
436:Bryant Tuckerman
381:in 1972 founded
238:
237:
234:
233:
230:
227:
222:
221:
218:
215:
212:
209:
206:
203:
200:
177:known plaintexts
33:
29:
21:
6416:
6415:
6411:
6410:
6409:
6407:
6406:
6405:
6366:
6365:
6364:
6355:
6337:
6266:
6022:
6017:
5976:
5950:
5919:Standardization
5914:
5843:Electromagnetic
5795:Integral/Square
5752:Piling-up lemma
5736:Biclique attack
5725:EFF DES cracker
5709:
5703:
5634:Feistel network
5622:
5247:CIPHERUNICORN-E
5242:CIPHERUNICORN-A
5174:
5168:
5101:
5095:
5049:
5043:
5033:
4957:
4952:
4936:
4901:
4869:Matsui, Mitsuru
4816:Junod, Pascal.
4794:
4770:Wayback Machine
4738:
4737:
4725:
4686:2002: pp254–266
4619:
4618:
4578:
4573:
4565:
4561:
4552:
4551:
4547:
4539:
4535:
4526:
4522:
4509:
4505:
4496:
4492:
4483:
4479:
4470:
4466:
4457:
4453:
4444:
4440:
4434:Wayback Machine
4424:
4420:
4412:
4405:
4401:
4400:
4396:
4389:
4375:
4374:
4370:
4363:
4341:
4337:
4330:
4308:
4304:
4297:
4275:
4271:
4226:
4222:
4215:
4193:
4189:
4182:
4160:
4156:
4149:
4127:
4123:
4090:
4086:
4071:
4064:
4057:
4033:
4026:
4010:
4009:
3989:
3965:
3958:
3950:
3946:
3937:
3936:
3932:
3927:Wayback Machine
3918:
3914:
3907:
3891:
3887:
3877:
3875:
3871:
3867:
3866:
3862:
3856:
3832:
3828:
3819:
3818:
3814:
3805:
3801:
3790:
3786:
3777:
3775:
3766:
3765:
3761:
3752:
3750:
3749:. csrc.nist.gov
3745:
3744:
3740:
3731:
3730:
3726:
3717:
3716:
3712:
3706:
3702:
3693:
3691:
3686:
3685:
3681:
3676:Wayback Machine
3666:Wayback Machine
3656:
3652:
3647:
3643:
3634:
3632:
3627:
3626:
3622:
3607:
3603:
3588:
3581:
3572:
3570:
3560:
3556:
3547:
3540:
3529:
3525:
3512:
3510:
3506:
3495:
3489:
3485:
3472:
3470:
3466:
3455:
3449:
3445:
3436:
3434:
3430:
3419:
3413:
3409:
3386:
3382:
3371:
3367:
3356:
3352:
3341:
3337:
3328:
3326:
3315:
3311:
3301:
3299:
3298:on 22 July 2019
3256:
3252:
3242:
3240:
3236:
3219:
3215:
3214:
3210:
3199:
3195:
3188:
3168:
3161:
3148:
3147:
3140:
3132:
3101:
3095:
3084:
3080:
3051:
3027:AES competition
2936:
2925:
2919:
2916:
2905:
2893:
2882:
2873:
2844:
2841:
2840:
2820:
2816:
2811:
2808:
2807:
2774:
2770:
2769:
2765:
2754:
2750:
2749:
2745:
2743:
2740:
2739:
2702:
2698:
2697:
2693:
2682:
2678:
2677:
2673:
2671:
2668:
2667:
2647:
2643:
2641:
2638:
2637:
2620:
2616:
2614:
2611:
2610:
2583:
2579:
2570:
2566:
2564:
2561:
2560:
2525:
2521:
2512:
2508:
2506:
2503:
2502:
2454:
2451:
2450:
2434:
2431:
2430:
2412:
2409:
2408:
2391:
2387:
2385:
2382:
2381:
2363:
2360:
2359:
2334:
2332:
2329:
2328:
2304:
2288:
2274:
2270:
2244:
2240:
2238:
2235:
2234:
2228:
2141:
2125:SciEngines GmbH
2089:EFF DES cracker
2062:'s US$ 250,000
2032:
2015:
2010:
2009:
2006:
2003:
2000:
1997:
1994:
1991:
1988:
1985:
1982:
1979:
1976:
1973:
1970:
1967:
1964:
1961:
1958:
1955:
1952:
1949:
1946:
1943:
1940:
1937:
1934:
1931:
1928:
1925:
1922:
1919:
1916:
1913:
1910:
1907:
1904:
1901:
1898:
1895:
1892:
1889:
1886:
1883:
1880:
1877:
1874:
1871:
1868:
1865:
1862:
1859:
1856:
1853:
1850:
1847:
1844:
1841:
1838:
1835:
1832:
1829:
1826:
1823:
1820:
1817:
1814:
1811:
1808:
1805:
1802:
1799:
1796:
1793:
1790:
1787:
1784:
1781:
1778:
1775:
1772:
1769:
1766:
1763:
1760:
1757:
1754:
1751:
1748:
1745:
1742:
1739:
1736:
1733:
1730:
1727:
1724:
1721:
1718:
1715:
1712:
1709:
1706:
1703:
1700:
1697:
1694:
1691:
1688:
1685:
1682:
1679:
1676:
1673:
1670:
1667:
1664:
1661:
1658:
1655:
1652:
1649:
1646:
1643:
1640:
1637:
1634:
1631:
1628:
1625:
1622:
1619:
1616:
1613:
1610:
1607:
1604:
1601:
1598:
1595:
1592:
1589:
1586:
1583:
1580:
1577:
1574:
1571:
1568:
1565:
1562:
1559:
1556:
1553:
1550:
1547:
1544:
1541:
1538:
1535:
1532:
1529:
1526:
1523:
1520:
1517:
1514:
1511:
1508:
1505:
1502:
1499:
1496:
1493:
1490:
1487:
1484:
1481:
1478:
1475:
1472:
1469:
1466:
1463:
1460:
1457:
1454:
1451:
1448:
1445:
1442:
1439:
1436:
1433:
1430:
1427:
1424:
1415:
1369:
1352:
1350:
1258:
1243:
1238:
1187:
1176:
1170:
1167:
1156:
1144:
1133:
1053:
1039:
1037:
1030:
872:distributed.net
623:
539:
444:
424:Don Coppersmith
364:
325:distributed.net
321:56-bit key size
224:
197:
193:
169:EFF DES cracker
139:Feistel network
65:First published
45:
28:
23:
22:
15:
12:
11:
5:
6414:
6404:
6403:
6398:
6393:
6388:
6383:
6378:
6361:
6360:
6357:
6356:
6354:
6353:
6342:
6339:
6338:
6336:
6335:
6330:
6328:Random numbers
6325:
6320:
6315:
6310:
6305:
6300:
6295:
6290:
6285:
6280:
6274:
6272:
6268:
6267:
6265:
6264:
6259:
6254:
6252:Garlic routing
6249:
6244:
6239:
6234:
6229:
6224:
6219:
6214:
6209:
6204:
6199:
6194:
6189:
6184:
6179:
6174:
6172:Secure channel
6169:
6163:
6162:
6161:
6150:
6145:
6140:
6135:
6133:Key stretching
6130:
6125:
6120:
6115:
6110:
6105:
6100:
6099:
6098:
6093:
6083:
6081:Cryptovirology
6078:
6073:
6068:
6066:Cryptocurrency
6063:
6058:
6053:
6052:
6051:
6041:
6036:
6030:
6028:
6024:
6023:
6016:
6015:
6008:
6001:
5993:
5986:
5985:
5982:
5981:
5978:
5977:
5975:
5974:
5969:
5964:
5958:
5956:
5952:
5951:
5949:
5948:
5943:
5938:
5933:
5928:
5922:
5920:
5916:
5915:
5913:
5912:
5907:
5902:
5897:
5892:
5887:
5882:
5877:
5872:
5867:
5862:
5857:
5856:
5855:
5850:
5845:
5840:
5835:
5825:
5820:
5815:
5810:
5802:
5797:
5792:
5785:Distinguishing
5782:
5777:
5776:
5775:
5770:
5765:
5755:
5745:
5744:
5743:
5738:
5728:
5717:
5715:
5705:
5704:
5702:
5701:
5691:
5686:
5681:
5676:
5671:
5666:
5661:
5656:
5651:
5649:Product cipher
5646:
5641:
5636:
5630:
5628:
5624:
5623:
5621:
5620:
5615:
5610:
5605:
5600:
5595:
5590:
5585:
5580:
5575:
5570:
5565:
5560:
5555:
5550:
5545:
5540:
5535:
5530:
5525:
5520:
5515:
5510:
5505:
5500:
5495:
5490:
5485:
5480:
5475:
5470:
5465:
5460:
5455:
5450:
5445:
5440:
5435:
5430:
5425:
5420:
5415:
5404:
5399:
5394:
5389:
5384:
5379:
5374:
5369:
5364:
5359:
5354:
5349:
5344:
5339:
5334:
5329:
5324:
5319:
5314:
5309:
5304:
5299:
5294:
5289:
5284:
5279:
5277:Cryptomeria/C2
5274:
5269:
5264:
5259:
5254:
5249:
5244:
5239:
5234:
5229:
5224:
5219:
5214:
5209:
5204:
5199:
5194:
5189:
5184:
5178:
5176:
5170:
5169:
5167:
5166:
5161:
5156:
5151:
5146:
5141:
5136:
5131:
5126:
5121:
5116:
5111:
5105:
5103:
5097:
5096:
5094:
5093:
5088:
5083:
5078:
5064:
5059:
5053:
5051:
5045:
5044:
5032:
5031:
5024:
5017:
5009:
4995:
4994:
4989:
4984:
4979:
4974:
4969:
4964:
4956:
4955:External links
4953:
4951:
4950:
4943:
4940:
4934:
4913:
4899:
4882:10.1.1.50.8472
4865:
4847:
4844:
4834:
4824:
4814:
4800:
4791:
4788:Martin Hellman
4781:
4759:
4756:
4723:
4715:10.1007/b99099
4702:
4693:
4687:
4673:
4663:
4637:
4579:
4577:
4574:
4572:
4571:
4559:
4545:
4533:
4520:
4503:
4490:
4477:
4464:
4451:
4438:
4418:
4394:
4387:
4368:
4362:978-0849385230
4361:
4335:
4329:978-3540361787
4328:
4302:
4296:978-3540486589
4295:
4269:
4240:(3): 195–205.
4220:
4214:978-3540455370
4213:
4187:
4181:978-3540447061
4180:
4154:
4147:
4121:
4084:
4062:
4056:978-3540482857
4055:
4024:
3988:978-0387979304
3987:
3956:
3944:
3930:
3912:
3905:
3885:
3860:
3854:
3826:
3812:
3806:Stallings, W.
3799:
3784:
3759:
3738:
3724:
3710:
3700:
3679:
3650:
3641:
3620:
3601:
3579:
3554:
3538:
3535:. p. 301.
3523:
3483:
3443:
3407:
3380:
3365:
3350:
3335:
3309:
3250:
3208:
3193:
3186:
3159:
3138:
3135:on 2014-02-26.
3081:
3079:
3076:
3075:
3074:
3069:
3064:
3059:
3050:
3047:
2938:
2937:
2896:
2894:
2887:
2881:
2878:
2872:
2871:Simplified DES
2869:
2848:
2828:
2823:
2819:
2815:
2796:
2795:
2784:
2777:
2773:
2768:
2764:
2757:
2753:
2748:
2727:
2724:
2721:
2718:
2715:
2712:
2705:
2701:
2696:
2692:
2685:
2681:
2676:
2650:
2646:
2623:
2619:
2607:semi-weak keys
2603:
2602:
2591:
2586:
2582:
2578:
2573:
2569:
2548:
2545:
2542:
2539:
2536:
2533:
2528:
2524:
2520:
2515:
2511:
2486:. Encryption (
2458:
2438:
2419:
2416:
2394:
2390:
2370:
2367:
2341:
2338:
2325:
2324:
2311:
2308:
2303:
2300:
2295:
2292:
2287:
2281:
2278:
2273:
2268:
2264:
2261:
2258:
2255:
2252:
2247:
2243:
2227:
2224:
2212:
2211:
2193:
2184:, and needs 2
2182:Mitsuru Matsui
2175:
2153:Davies' attack
2140:
2137:
2031:
2028:
2014:
2011:
1423:
1414:
1411:
1349:
1346:
1342:Claude Shannon
1334:
1333:
1319:
1299:
1283:
1237:
1234:
1218:Feistel scheme
1189:
1188:
1147:
1145:
1138:
1132:
1129:
1029:
1026:
1023:
1022:
1007:
1004:
1000:
999:
987:
984:
980:
979:
972:
969:
965:
964:
953:
950:
946:
945:
938:
935:
931:
930:
924:
921:
917:
916:
913:
910:
906:
905:
898:
895:
891:
890:
883:
880:
876:
875:
864:
861:
857:
856:
845:
842:
838:
837:
830:
827:
823:
822:
819:
816:
813:
812:
809:
806:
802:
801:
790:
787:
784:
783:
776:
773:
769:
768:
765:
762:
758:
757:
751:
748:
745:
744:
741:
738:
735:
734:
724:
721:
717:
716:
713:
710:
706:
705:
702:
699:
695:
694:
691:
688:
684:
683:
680:
677:
673:
672:
665:
662:
658:
657:
654:
651:
647:
646:
643:
640:
636:
635:
632:
629:
622:
619:
618:
617:
610:Bruce Schneier
538:
535:
458:Martin Hellman
443:
440:
420:Walter Tuchman
379:Mohamed Atalla
363:
360:
181:
180:
160:
159:
152:
151:
148:
142:
141:
135:
131:
130:
127:
121:
120:
117:
111:
110:
106:
105:
84:
80:
79:
74:
70:
69:
66:
62:
61:
56:
52:
51:
47:
46:
43:
26:
9:
6:
4:
3:
2:
6413:
6402:
6399:
6397:
6394:
6392:
6389:
6387:
6384:
6382:
6379:
6377:
6376:Block ciphers
6374:
6373:
6371:
6352:
6344:
6343:
6340:
6334:
6333:Steganography
6331:
6329:
6326:
6324:
6321:
6319:
6316:
6314:
6311:
6309:
6306:
6304:
6301:
6299:
6296:
6294:
6291:
6289:
6288:Stream cipher
6286:
6284:
6281:
6279:
6276:
6275:
6273:
6269:
6263:
6260:
6258:
6255:
6253:
6250:
6248:
6247:Onion routing
6245:
6243:
6240:
6238:
6235:
6233:
6230:
6228:
6227:Shared secret
6225:
6223:
6220:
6218:
6215:
6213:
6210:
6208:
6205:
6203:
6200:
6198:
6195:
6193:
6190:
6188:
6185:
6183:
6180:
6178:
6175:
6173:
6170:
6167:
6164:
6159:
6156:
6155:
6154:
6151:
6149:
6146:
6144:
6141:
6139:
6136:
6134:
6131:
6129:
6126:
6124:
6123:Key generator
6121:
6119:
6116:
6114:
6111:
6109:
6106:
6104:
6101:
6097:
6094:
6092:
6089:
6088:
6087:
6086:Hash function
6084:
6082:
6079:
6077:
6074:
6072:
6069:
6067:
6064:
6062:
6061:Cryptanalysis
6059:
6057:
6054:
6050:
6047:
6046:
6045:
6042:
6040:
6037:
6035:
6032:
6031:
6029:
6025:
6021:
6014:
6009:
6007:
6002:
6000:
5995:
5994:
5991:
5987:
5973:
5970:
5968:
5965:
5963:
5960:
5959:
5957:
5953:
5947:
5944:
5942:
5939:
5937:
5934:
5932:
5929:
5927:
5924:
5923:
5921:
5917:
5911:
5908:
5906:
5903:
5901:
5898:
5896:
5893:
5891:
5888:
5886:
5883:
5881:
5878:
5876:
5873:
5871:
5868:
5866:
5865:Interpolation
5863:
5861:
5858:
5854:
5851:
5849:
5846:
5844:
5841:
5839:
5836:
5834:
5831:
5830:
5829:
5826:
5824:
5821:
5819:
5816:
5814:
5811:
5809:
5808:
5803:
5801:
5798:
5796:
5793:
5790:
5786:
5783:
5781:
5778:
5774:
5771:
5769:
5766:
5764:
5761:
5760:
5759:
5756:
5753:
5749:
5746:
5742:
5739:
5737:
5734:
5733:
5732:
5729:
5726:
5722:
5719:
5718:
5716:
5713:
5712:cryptanalysis
5706:
5699:
5695:
5694:Key whitening
5692:
5690:
5687:
5685:
5682:
5680:
5677:
5675:
5672:
5670:
5667:
5665:
5662:
5660:
5657:
5655:
5652:
5650:
5647:
5645:
5642:
5640:
5637:
5635:
5632:
5631:
5629:
5625:
5619:
5616:
5614:
5611:
5609:
5606:
5604:
5601:
5599:
5596:
5594:
5591:
5589:
5586:
5584:
5581:
5579:
5576:
5574:
5571:
5569:
5566:
5564:
5561:
5559:
5556:
5554:
5551:
5549:
5546:
5544:
5541:
5539:
5536:
5534:
5531:
5529:
5526:
5524:
5521:
5519:
5516:
5514:
5511:
5509:
5506:
5504:
5501:
5499:
5496:
5494:
5491:
5489:
5486:
5484:
5483:New Data Seal
5481:
5479:
5476:
5474:
5471:
5469:
5466:
5464:
5461:
5459:
5456:
5454:
5451:
5449:
5446:
5444:
5441:
5439:
5436:
5434:
5431:
5429:
5426:
5424:
5421:
5419:
5416:
5413:
5409:
5405:
5403:
5400:
5398:
5395:
5393:
5390:
5388:
5385:
5383:
5380:
5378:
5375:
5373:
5370:
5368:
5365:
5363:
5360:
5358:
5355:
5353:
5350:
5348:
5345:
5343:
5340:
5338:
5335:
5333:
5330:
5328:
5325:
5323:
5320:
5318:
5315:
5313:
5310:
5308:
5305:
5303:
5300:
5298:
5295:
5293:
5290:
5288:
5285:
5283:
5280:
5278:
5275:
5273:
5270:
5268:
5265:
5263:
5260:
5258:
5255:
5253:
5250:
5248:
5245:
5243:
5240:
5238:
5235:
5233:
5230:
5228:
5225:
5223:
5222:BEAR and LION
5220:
5218:
5215:
5213:
5210:
5208:
5205:
5203:
5200:
5198:
5195:
5193:
5190:
5188:
5185:
5183:
5180:
5179:
5177:
5171:
5165:
5162:
5160:
5157:
5155:
5152:
5150:
5147:
5145:
5142:
5140:
5137:
5135:
5132:
5130:
5127:
5125:
5122:
5120:
5117:
5115:
5112:
5110:
5107:
5106:
5104:
5098:
5092:
5089:
5087:
5084:
5082:
5079:
5076:
5072:
5068:
5065:
5063:
5060:
5058:
5055:
5054:
5052:
5046:
5041:
5037:
5036:Block ciphers
5030:
5025:
5023:
5018:
5016:
5011:
5010:
5007:
5003:
4999:
4993:
4990:
4988:
4985:
4983:
4980:
4978:
4975:
4973:
4970:
4968:
4965:
4962:
4959:
4958:
4948:
4944:
4941:
4937:
4931:
4927:
4923:
4919:
4914:
4910:
4906:
4902:
4896:
4892:
4888:
4883:
4878:
4874:
4870:
4866:
4863:
4862:0-14-024432-8
4859:
4855:
4851:
4848:
4845:
4842:
4838:
4837:Knudsen, Lars
4835:
4832:
4828:
4825:
4822:
4819:
4815:
4812:
4811:1-56592-520-3
4808:
4804:
4803:Gilmore, John
4801:
4797:
4792:
4789:
4785:
4782:
4780:(3), 243–250.
4779:
4775:
4771:
4767:
4763:
4760:
4757:
4754:
4748:
4742:
4734:
4730:
4726:
4720:
4716:
4712:
4708:
4703:
4701:
4697:
4694:
4691:
4688:
4685:
4681:
4680:Orr Dunkelman
4677:
4674:
4671:
4670:Alex Biryukov
4667:
4664:
4661:
4660:3-540-97930-1
4657:
4653:
4652:0-387-97930-1
4649:
4645:
4641:
4638:
4635:
4629:
4623:
4615:
4611:
4607:
4603:
4599:
4595:
4594:
4589:
4585:
4581:
4580:
4568:
4563:
4555:
4549:
4542:
4537:
4530:
4524:
4517:
4513:
4507:
4500:
4494:
4487:
4481:
4474:
4468:
4461:
4455:
4448:
4442:
4435:
4431:
4428:
4422:
4411:
4404:
4398:
4390:
4388:9783540573401
4384:
4380:
4379:
4372:
4364:
4358:
4354:
4349:
4348:
4339:
4331:
4325:
4321:
4317:
4313:
4306:
4298:
4292:
4288:
4284:
4280:
4273:
4265:
4261:
4257:
4253:
4248:
4243:
4239:
4235:
4231:
4224:
4216:
4210:
4206:
4202:
4198:
4191:
4183:
4177:
4173:
4169:
4165:
4158:
4150:
4148:9783540226680
4144:
4140:
4136:
4132:
4125:
4117:
4113:
4108:
4103:
4099:
4095:
4088:
4080:
4076:
4069:
4067:
4058:
4052:
4047:
4042:
4038:
4031:
4029:
4020:
4014:
4006:
4002:
3998:
3994:
3990:
3984:
3980:
3976:
3972:
3971:
3963:
3961:
3953:
3948:
3940:
3934:
3928:
3924:
3921:
3916:
3908:
3906:9780470060643
3902:
3898:
3897:
3889:
3870:
3864:
3857:
3851:
3846:
3841:
3837:
3830:
3822:
3821:"Bruting DES"
3816:
3809:
3803:
3795:
3788:
3774:on 2014-01-03
3773:
3769:
3763:
3748:
3742:
3734:
3728:
3720:
3719:"8x1080Ti.md"
3714:
3704:
3689:
3683:
3677:
3673:
3670:
3667:
3663:
3660:
3654:
3645:
3630:
3624:
3618:
3614:
3610:
3605:
3599:
3598:, Version 1.1
3597:
3591:
3586:
3584:
3569:
3565:
3558:
3551:
3545:
3543:
3534:
3527:
3519:
3505:
3501:
3494:
3487:
3479:
3465:
3461:
3454:
3447:
3433:on 2013-09-18
3429:
3425:
3418:
3411:
3403:
3399:
3395:
3391:
3384:
3376:
3375:IEEE Spectrum
3369:
3361:
3354:
3346:
3339:
3325:on 2016-05-17
3324:
3320:
3313:
3297:
3293:
3289:
3285:
3281:
3277:
3273:
3269:
3265:
3261:
3254:
3235:
3231:
3227:
3226:
3218:
3212:
3204:
3197:
3189:
3187:9780191085574
3183:
3179:
3175:
3174:
3166:
3164:
3155:
3151:
3145:
3143:
3131:
3127:
3123:
3119:
3115:
3111:
3107:
3100:
3093:
3091:
3089:
3087:
3082:
3073:
3070:
3068:
3065:
3063:
3060:
3058:
3057:
3053:
3052:
3046:
3044:
3040:
3036:
3032:
3028:
3024:
3020:
3015:
3013:
3009:
3004:
3000:
2995:
2993:
2989:
2988:GOST 28147-89
2985:
2981:
2977:
2973:
2969:
2965:
2961:
2957:
2953:
2949:
2945:
2934:
2931:
2923:
2920:November 2009
2913:
2909:
2903:
2902:
2897:This section
2895:
2891:
2886:
2885:
2877:
2868:
2866:
2862:
2846:
2821:
2817:
2805:
2800:
2782:
2775:
2771:
2766:
2762:
2755:
2751:
2746:
2725:
2722:
2713:
2703:
2699:
2694:
2683:
2679:
2674:
2666:
2665:
2664:
2648:
2644:
2621:
2617:
2608:
2589:
2584:
2580:
2576:
2571:
2567:
2546:
2543:
2534:
2526:
2522:
2513:
2509:
2501:
2500:
2499:
2497:
2493:
2489:
2485:
2484:
2478:
2476:
2472:
2456:
2436:
2417:
2414:
2392:
2388:
2368:
2365:
2357:
2336:
2306:
2301:
2290:
2276:
2271:
2262:
2259:
2253:
2245:
2241:
2233:
2232:
2231:
2223:
2220:
2216:
2209:
2205:
2201:
2200:Donald Davies
2197:
2194:
2191:
2187:
2183:
2179:
2176:
2173:
2169:
2165:
2161:
2158:
2157:
2156:
2154:
2150:
2146:
2136:
2133:
2128:
2126:
2122:
2118:
2114:
2110:
2106:
2102:
2097:
2095:
2090:
2086:
2082:
2078:
2074:
2065:
2061:
2056:
2052:
2050:
2045:
2041:
2037:
2027:
2025:
2021:
1421:
1419:
1410:
1406:
1404:
1400:
1395:
1391:
1387:
1383:
1375:
1374:
1345:
1343:
1339:
1331:
1327:
1323:
1320:
1317:
1313:
1309:
1308:
1303:
1300:
1297:
1296:
1291:
1287:
1284:
1280:
1276:
1272:
1269:
1268:
1264:
1263:
1241:
1233:
1230:
1226:
1221:
1219:
1214:
1212:
1208:
1204:
1200:
1196:
1185:
1182:
1174:
1164:
1160:
1154:
1153:
1148:This section
1146:
1142:
1137:
1136:
1128:
1125:
1123:
1117:
1115:
1109:
1107:
1103:
1098:
1096:
1092:
1087:
1083:
1079:
1075:
1071:
1067:
1059:
1058:
1035:
1020:
1016:
1015:rainbow table
1012:
1008:
1005:
1002:
1001:
996:
992:
988:
985:
982:
981:
977:
973:
970:
967:
966:
962:
958:
954:
951:
948:
947:
943:
939:
936:
933:
932:
929:
925:
922:
919:
918:
914:
911:
908:
907:
903:
899:
896:
893:
892:
888:
884:
881:
878:
877:
873:
869:
865:
862:
859:
858:
854:
850:
846:
843:
840:
839:
835:
831:
828:
825:
824:
820:
817:
815:
814:
810:
807:
804:
803:
799:
795:
791:
788:
786:
785:
781:
777:
774:
771:
770:
766:
763:
760:
759:
755:
752:
749:
747:
746:
742:
739:
737:
736:
732:
728:
725:
722:
719:
718:
714:
711:
708:
707:
703:
700:
697:
696:
692:
689:
686:
685:
681:
678:
675:
674:
670:
666:
663:
660:
659:
655:
652:
649:
648:
644:
641:
638:
637:
633:
630:
627:
626:
615:
611:
607:
602:
601:
600:
597:
595:
594:cryptanalysis
591:
587:
582:
580:
576:
572:
568:
563:
561:
558:has approved
557:
553:
549:
544:
534:
532:
528:
524:
520:
514:
509:
505:
500:
495:
490:
486:
483:
477:
475:
471:
467:
463:
459:
455:
451:
450:
439:
437:
433:
432:Edna Grossman
429:
425:
421:
417:
413:
412:Horst Feistel
409:
403:
401:
397:
392:
388:
384:
380:
375:
373:
369:
359:
357:
353:
348:
346:
342:
338:
334:
330:
326:
322:
317:
315:
314:cryptanalysis
311:
307:
303:
299:
296:
295:symmetric-key
292:
288:
283:
281:
277:
273:
269:
265:
261:
260:Horst Feistel
257:
252:
250:
246:
242:
236:
192:
188:
178:
174:
170:
166:
161:
158:
157:cryptanalysis
153:
149:
147:
143:
140:
136:
132:
128:
126:
122:
118:
116:
112:
109:Cipher detail
107:
104:
100:
96:
92:
88:
85:
81:
78:
75:
71:
67:
63:
60:
57:
53:
48:
39:
34:
19:
6283:Block cipher
6128:Key schedule
6118:Key exchange
6108:Kleptography
6071:Cryptosystem
6020:Cryptography
5870:Partitioning
5828:Side-channel
5806:
5773:Higher-order
5758:Differential
5639:Key schedule
5066:
4917:
4872:
4850:Levy, Steven
4831:Matt Robshaw
4777:
4773:
4706:
4622:cite journal
4597:
4591:
4562:
4548:
4536:
4523:
4506:
4493:
4480:
4467:
4454:
4441:
4421:
4403:"Double DES"
4397:
4377:
4371:
4346:
4338:
4311:
4305:
4278:
4272:
4237:
4233:
4223:
4196:
4190:
4163:
4157:
4130:
4124:
4097:
4093:
4087:
4078:
4036:
3969:
3951:
3947:
3933:
3915:
3895:
3888:
3876:. Retrieved
3863:
3835:
3829:
3815:
3807:
3802:
3793:
3787:
3776:. Retrieved
3772:the original
3762:
3751:. Retrieved
3741:
3727:
3713:
3703:
3692:. Retrieved
3682:
3653:
3644:
3633:. Retrieved
3623:
3616:
3604:
3595:
3571:. Retrieved
3567:
3557:
3549:
3532:
3526:
3516:– via
3511:. Retrieved
3486:
3476:– via
3471:. Retrieved
3446:
3435:. Retrieved
3428:the original
3410:
3393:
3389:
3383:
3374:
3368:
3359:
3353:
3344:
3338:
3327:. Retrieved
3323:the original
3312:
3300:. Retrieved
3296:the original
3267:
3263:
3253:
3241:. Retrieved
3234:the original
3223:
3211:
3202:
3196:
3172:
3153:
3130:the original
3112:(6): 74–84.
3109:
3105:
3054:
3016:
2996:
2984:Soviet Union
2948:block cipher
2941:
2926:
2917:
2906:Please help
2901:verification
2898:
2874:
2801:
2797:
2606:
2604:
2491:
2487:
2481:
2479:
2326:
2229:
2217:
2213:
2195:
2189:
2142:
2129:
2098:
2092:
2073:RSA Security
2069:
2047:replacement
2033:
2016:
1992:cipher_chunk
1980:cipher_chunk
1950:cipher_chunk
1875:substitution
1416:
1407:
1402:
1398:
1389:
1385:
1382:key schedule
1381:
1379:
1371:
1348:Key schedule
1335:
1329:
1321:
1316:lookup table
1311:
1305:
1302:Substitution
1301:
1295:key schedule
1293:
1289:
1285:
1278:
1274:
1270:
1260:
1239:
1228:
1225:exclusive-OR
1222:
1215:
1209:, which are
1206:
1202:
1194:
1192:
1177:
1168:
1157:Please help
1152:verification
1149:
1126:
1119:
1113:
1111:
1099:
1097:is 56 bits.
1066:block cipher
1063:
1055:
1018:
1013:utilizing a
927:
894:26 November
805:30 December
671:for comment
668:
598:
583:
564:
540:
516:
511:
507:
502:
497:
492:
488:
479:
447:
445:
404:
376:
365:
355:
351:
349:
318:
298:block cipher
284:
253:
249:cryptography
190:
186:
184:
155:Best public
73:Derived from
6271:Mathematics
6262:Mix network
5955:Utilization
5941:NSA Suite B
5926:AES process
5875:Rubber-hose
5813:Related-key
5721:Brute-force
5100:Less common
4644:Shamir, Adi
4600:(1): 3–72.
4588:Shamir, Adi
3390:Cryptologia
3270:(1): 1–29.
2121:Moore's law
2081:Matt Curtin
2040:brute force
1986:permutation
1896:permutation
1746:permutation
1650:permutation
1500:permutation
1326:permutation
1322:Permutation
1199:permutation
1171:August 2009
1028:Description
879:25 October
853:DES cracker
761:22 January
754:Videocipher
709:15 January
590:DES cracker
531:Steven Levy
125:Block sizes
6370:Categories
6222:Ciphertext
6192:Decryption
6187:Encryption
6148:Ransomware
5905:Chi-square
5823:Rotational
5763:Impossible
5684:Block size
5578:Spectr-H64
5402:Ladder-DES
5397:Kuznyechik
5342:Hierocrypt
5212:BassOmatic
5175:algorithms
5102:algorithms
5075:Triple DES
5050:algorithms
4764:. (1994).
4690:Biham, Eli
4676:Biham, Eli
4666:Biham, Eli
4640:Biham, Eli
4584:Biham, Eli
4576:References
3792:Schneier.
3778:2009-06-02
3753:2009-06-02
3694:2009-06-02
3635:2011-10-21
3573:2015-07-22
3513:2015-07-16
3473:2015-07-16
3437:2014-07-10
3396:(4): 371.
3343:Schneier.
3329:2009-11-08
3072:Triple DES
2999:Triple DES
2980:block size
2865:Triple DES
2496:involution
2168:Adi Shamir
2151:(LC), and
2107:, both in
1791:0xFFFFFFFF
1773:rightshift
1605:leftrotate
1590:leftrotate
1530:rightshift
1418:Pseudocode
1413:Pseudocode
1286:Key mixing
1277:, denoted
1229:F-function
1095:key length
1082:block size
1078:ciphertext
976:COPACOBANA
961:COPACOBANA
887:Triple DES
868:Deep Crack
866:Together,
687:September
650:27 August
621:Chronology
560:Triple DES
548:Triple DES
523:Adi Shamir
466:key length
337:Triple DES
291:key length
287:classified
245:encryption
87:Triple DES
83:Successors
6212:Plaintext
5880:Black-bag
5800:Boomerang
5789:Known-key
5768:Truncated
5593:Threefish
5588:SXAL/MBAL
5478:MultiSwap
5433:MacGuffin
5392:KN-Cipher
5332:Grand Cru
5287:CS-Cipher
5267:COCONUT98
4877:CiteSeerX
4741:cite book
4684:ASIACRYPT
4614:206783462
4256:0933-2790
4107:1003.4085
4013:cite book
3531:Konheim.
3302:28 August
3284:2190-8516
3243:21 August
3029:included
2483:weak keys
2340:¯
2310:¯
2294:¯
2280:¯
2267:⟺
2164:Eli Biham
2049:algorithm
1962:leftshift
1833:expansion
1626:leftshift
1608:KEY_shift
1593:KEY_shift
1557:0xFFFFFFF
1542:0xFFFFFFF
1271:Expansion
1201:, termed
1074:plaintext
1070:algorithm
698:November
661:17 March
519:Eli Biham
494:intended.
485:weakness.
456:pioneers
428:Roy Adler
137:Balanced
134:Structure
115:Key sizes
55:Designers
6351:Category
6257:Kademlia
6217:Codetext
6160:(CSPRNG)
5931:CRYPTREC
5895:Weak key
5848:Acoustic
5689:Key size
5533:Red Pike
5352:IDEA NXT
5232:Chiasmus
5227:CAST-256
5207:BaseKing
5192:Akelarre
5187:Adiantum
5154:Skipjack
5119:CAST-128
5114:Camellia
5062:Blowfish
4909:21157010
4856:, 2001,
4753:preprint
4733:27790868
4634:preprint
4430:Archived
4410:Archived
3997:27173465
3923:Archived
3878:March 6,
3672:Archived
3662:Archived
3615:92-1981)
3504:Archived
3464:Archived
3106:Computer
3049:See also
3023:Rijndael
2956:Blowfish
2944:software
2859:) under
2204:Biryukov
2135:online.
2034:For any
1443:multiple
1373:Figure 3
1262:Figure 2
1211:inverses
1057:Figure 1
920:26 July
860:January
400:IBM 3624
327:and the
302:backdoor
243:for the
6027:General
5972:Padding
5890:Rebound
5598:Treyfer
5548:SAVILLE
5508:PRESENT
5498:NOEKEON
5443:MAGENTA
5438:Madryga
5418:Lucifer
5282:CRYPTON
5091:Twofish
5081:Serpent
4768:at the
4531:. 2012.
4488:. 2009.
4475:. 2006.
4462:. 2010.
4436:. 2014.
4264:4070446
4112:Bibcode
4005:6361693
3552:, p. 55
3292:1706990
3126:2412454
3043:Twofish
3035:Serpent
2994:later.
2354:is the
2109:Germany
1725:message
1686:reverse
1680:decrypt
1434:message
1307:S-boxes
991:hashcat
983:August
934:19 May
909:26 May
731:Hellman
676:August
639:15 May
470:S-boxes
416:Lucifer
362:History
306:S-boxes
304:. The
293:of the
239:) is a
129:64 bits
119:56 bits
77:Lucifer
50:General
6138:Keygen
5936:NESSIE
5885:Davies
5833:Timing
5748:Linear
5708:Attack
5627:Design
5618:Zodiac
5583:Square
5558:SHACAL
5553:SC2000
5513:Prince
5493:Nimbus
5488:NewDES
5473:MULTI2
5463:MISTY1
5406:LOKI (
5382:KHAZAD
5377:KeeLoq
5372:KASUMI
5367:Kalyna
5252:CLEFIA
5237:CIKS-1
5197:Anubis
5048:Common
4932:
4907:
4897:
4879:
4860:
4809:
4731:
4721:
4658:
4650:
4612:
4385:
4359:
4326:
4293:
4262:
4254:
4211:
4178:
4145:
4053:
4003:
3995:
3985:
3903:
3852:
3613:INCITS
3550:Crypto
3548:Levy,
3290:
3282:
3184:
3124:
3041:, and
2992:Russia
2964:NewDES
2327:where
2147:(DC),
2036:cipher
1722:padded
1656:concat
1614:concat
1458:length
1394:parity
1328:, the
1290:subkey
1195:rounds
1106:INCITS
1091:parity
949:April
727:Diffie
634:Event
575:INCITS
571:INCITS
146:Rounds
99:LOKI89
6168:(PRN)
5818:Slide
5674:Round
5659:P-box
5654:S-box
5613:XXTEA
5573:Speck
5568:Simon
5563:SHARK
5543:SAFER
5528:REDOC
5453:Mercy
5412:89/91
5362:Iraqi
5327:G-DES
5317:FEA-M
5297:DES-X
5262:Cobra
5217:BATON
5202:Ascon
5182:3-Way
5173:Other
4963:(PDF)
4905:S2CID
4729:S2CID
4610:S2CID
4518:1996.
4413:(PDF)
4406:(PDF)
4260:S2CID
4102:arXiv
4100:(3).
4001:S2CID
3872:(PDF)
3708:2006.
3507:(PDF)
3496:(PDF)
3467:(PDF)
3456:(PDF)
3431:(PDF)
3420:(PDF)
3288:S2CID
3237:(PDF)
3220:(PDF)
3133:(PDF)
3122:S2CID
3102:(PDF)
3078:Notes
3008:DES-X
2972:CAST5
2968:SAFER
2804:group
2119:—see
2020:known
1977:// FP
1959:right
1920:right
1914:right
1902:right
1890:right
1881:right
1869:right
1857:right
1851:right
1839:right
1827:right
1821:right
1785:chunk
1779:right
1770:chunk
1752:chunk
1740:chunk
1737:// IP
1716:chunk
1638:right
1587:right
1581:right
1545:right
1485:right
1440:reach
1330:P-box
1310:, or
1282:side.
1102:bytes
1006:2017
1003:July
986:2016
971:2008
968:Nov.
952:2006
937:2005
923:2004
912:2002
897:2001
882:1999
863:1999
844:1998
841:July
829:1997
826:June
818:1994
808:1993
789:1992
775:1991
772:July
764:1988
750:1986
740:1983
723:1977
720:June
712:1977
701:1976
690:1976
679:1976
664:1975
653:1974
642:1973
631:Year
628:Date
95:DES-X
91:G-DES
5946:CNSA
5805:Mod
5731:MITM
5503:NUSH
5458:MESH
5448:MARS
5322:FROG
5312:FEAL
5292:DEAL
5272:Crab
5257:CMEA
5164:XTEA
5149:SEED
5129:IDEA
5124:GOST
5109:ARIA
4930:ISBN
4895:ISBN
4858:ISBN
4807:ISBN
4786:and
4747:link
4719:ISBN
4668:and
4656:ISBN
4648:ISBN
4642:and
4628:link
4586:and
4383:ISBN
4357:ISBN
4324:ISBN
4291:ISBN
4252:ISSN
4209:ISBN
4176:ISBN
4143:ISBN
4051:ISBN
4019:link
3993:OCLC
3983:ISBN
3901:ISBN
3880:2012
3850:ISBN
3659:HTML
3568:CNet
3304:2019
3280:ISSN
3245:2019
3182:ISBN
3039:MARS
3012:GDES
3003:FIPS
2986:the
2976:FEAL
2974:and
2960:IDEA
2449:and
2166:and
2105:Kiel
2103:and
2094:DES.
2058:The
1974:left
1929:left
1926:left
1887:// P
1863:keys
1800:from
1764:left
1704:each
1689:keys
1644:keys
1623:left
1602:left
1596:left
1566:from
1518:left
1479:left
1473:keys
1452:bits
1403:PC-2
1390:PC-1
1205:and
1068:—an
957:FPGA
955:The
900:The
870:and
847:The
832:The
729:and
579:TDEA
567:ANSI
556:NIST
543:FIPS
521:and
513:key.
508:and
460:and
185:The
5900:Tau
5860:XSL
5664:SPN
5608:xmx
5603:UES
5538:S-1
5523:RC2
5468:MMB
5347:ICE
5302:DFC
5159:TEA
5144:RC6
5139:RC5
5134:LEA
5086:SM4
5067:DES
5057:AES
4922:doi
4887:doi
4711:doi
4602:doi
4512:doi
4353:257
4316:doi
4283:doi
4242:doi
4201:doi
4168:doi
4135:doi
4041:doi
3975:doi
3840:doi
3669:PDF
3398:doi
3272:doi
3114:doi
3031:RC6
2952:RC5
2910:by
2498:):
2358:of
2060:EFF
2022:or
2007:for
2004:end
1947:var
1941:for
1938:end
1935:tmp
1923:xor
1860:xor
1815:tmp
1794:for
1788:and
1734:tmp
1731:var
1713:bit
1701:for
1692:end
1671:for
1668:end
1662:PC2
1611:var
1560:for
1554:and
1551:key
1539:and
1527:key
1512:PC1
1506:key
1494:key
1476:var
1470:var
1464:key
1461:var
1431:pad
1161:by
1114:KEY
1086:key
851:'s
849:EFF
588:'s
581:).
525:of
482:IBM
414:'s
408:IBM
396:IBM
391:PIN
358:).
352:DEA
256:IBM
191:DES
103:ICE
59:IBM
6372::
5428:M8
5423:M6
5410:,
5408:97
5307:E2
5073:,
4928:.
4903:.
4893:.
4885:.
4852:,
4829:,
4778:38
4776:,
4755:).
4743:}}
4739:{{
4727:.
4717:.
4698:,
4678:,
4654:,
4624:}}
4620:{{
4608:.
4596:.
4408:.
4355:.
4322:.
4289:.
4258:.
4250:.
4238:10
4236:.
4232:.
4207:.
4174:.
4141:.
4110:.
4096:.
4077:.
4065:^
4049:.
4027:^
4015:}}
4011:{{
3999:.
3991:.
3981:.
3959:^
3848:,
3592:,
3582:^
3566:.
3541:^
3502:.
3498:.
3462:.
3458:.
3422:.
3392:.
3286:.
3278:.
3266:.
3262:.
3228:.
3222:.
3176:.
3162:^
3152:.
3141:^
3120:.
3110:10
3108:.
3104:.
3085:^
3045:.
3037:,
3033:,
2970:,
2966:,
2962:,
2958:,
2954:,
2663::
1998:FP
1983::=
1971:or
1965:32
1953::=
1932::=
1917::=
1893::=
1872::=
1854::=
1830::=
1818::=
1812:do
1809:16
1806:to
1782::=
1776:32
1767::=
1758:IP
1743::=
1728:do
1719:of
1707:64
1695:if
1683:do
1677:if
1647::=
1635:or
1629:28
1617::=
1599::=
1584::=
1578:do
1575:16
1572:to
1548::=
1533:28
1521::=
1497::=
1455:in
1449:64
1446:of
1437:to
1207:FP
1203:IP
1009:A
944:)
800:.
438:.
430:,
422:,
347:.
316:.
251:.
211:iː
205:iː
150:16
101:,
97:,
93:,
89:,
6012:e
6005:t
5998:v
5807:n
5791:)
5787:(
5754:)
5750:(
5727:)
5723:(
5714:)
5710:(
5700:)
5696:(
5518:Q
5414:)
5077:)
5069:(
5042:)
5038:(
5028:e
5021:t
5014:v
4938:.
4924::
4911:.
4889::
4864:.
4813:.
4751:(
4749:)
4735:.
4713::
4662:.
4636:)
4632:(
4630:)
4616:.
4604::
4598:4
4543:.
4514::
4391:.
4365:.
4332:.
4318::
4299:.
4285::
4266:.
4244::
4217:.
4203::
4184:.
4170::
4151:.
4137::
4118:.
4114::
4104::
4098:2
4081:.
4059:.
4043::
4021:)
4007:.
3977::
3941:.
3909:.
3882:.
3842::
3823:.
3781:.
3756:.
3735:.
3721:.
3697:.
3638:.
3576:.
3440:.
3404:.
3400::
3394:2
3377:.
3332:.
3306:.
3274::
3268:6
3247:.
3190:.
3116::
2933:)
2927:(
2922:)
2918:(
2904:.
2847:K
2827:}
2822:K
2818:E
2814:{
2783:.
2776:1
2772:K
2767:D
2763:=
2756:2
2752:K
2747:E
2726:P
2723:=
2720:)
2717:)
2714:P
2711:(
2704:2
2700:K
2695:E
2691:(
2684:1
2680:K
2675:E
2649:2
2645:K
2622:1
2618:K
2590:.
2585:K
2581:D
2577:=
2572:K
2568:E
2547:P
2544:=
2541:)
2538:)
2535:P
2532:(
2527:K
2523:E
2519:(
2514:K
2510:E
2492:D
2488:E
2457:C
2437:P
2418:.
2415:K
2393:K
2389:E
2369:.
2366:x
2337:x
2307:C
2302:=
2299:)
2291:P
2286:(
2277:K
2272:E
2263:C
2260:=
2257:)
2254:P
2251:(
2246:K
2242:E
2001:)
1995:,
1989:(
1968:)
1956:(
1911:)
1908:P
1905:,
1899:(
1884:)
1878:(
1848:)
1845:E
1842:,
1836:(
1803:0
1797:i
1761:)
1755:,
1749:(
1710:-
1665:)
1659:,
1653:(
1632:)
1620:(
1569:0
1563:i
1536:)
1524:(
1515:)
1509:,
1503:(
1482:,
1401:(
1388:(
1279:E
1184:)
1178:(
1173:)
1169:(
1155:.
1036:.
546:"
354:(
235:/
232:z
229:ɛ
226:d
223:,
220:s
217:ɛ
214:ˈ
208:ˌ
202:d
199:ˌ
196:/
189:(
20:)
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.